| File name: | 1.rsp.dat |
| Full analysis: | https://app.any.run/tasks/76bbc177-cdb0-4010-92aa-56e0a7a8fe86 |
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 06:51:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 47870FF98164155F088062C95C448783 |
| SHA1: | 15E710A107830B193124A6D2BBC785B9383262A9 |
| SHA256: | 009406C1C7C0B289A25D44DFAA8364633D9B71DF5F3C7A65DEEC1EF00A8C2EBB |
| SSDEEP: | 98304:LBOy82SvWaN6o/8Ne0iK6pPij+UP7/t8Wp5WhzI/FqeNaZsdS4zaAwZuaQixlJoH:FOUARl/pPAP7mWp5WRIqsAI4jQiLg |
MALICIOUS
Drops executable file immediately after starts
- 1.rsp.dat.exe (PID: 956)
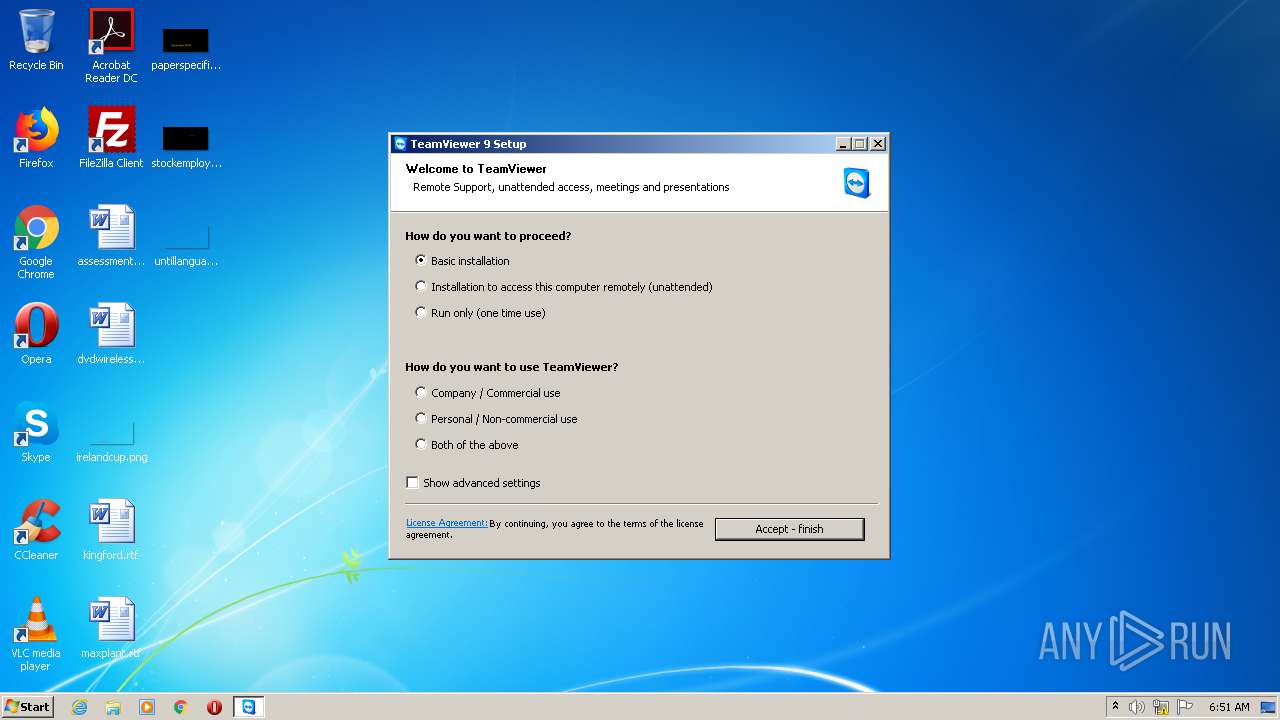
- TeamViewer_Setup_ru.exe (PID: 1980)
Application was dropped or rewritten from another process
- TeamViewer_Setup_ru.exe (PID: 1980)
- TeamViewer_.exe (PID: 3136)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2588)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 444)
Loads dropped or rewritten executable
- TeamViewer_.exe (PID: 3136)
- TeamViewer_Setup_ru.exe (PID: 1980)
SUSPICIOUS
Executable content was dropped or overwritten
- 1.rsp.dat.exe (PID: 956)
- TeamViewer_Setup_ru.exe (PID: 1980)
- TeamViewer_.exe (PID: 3136)
Starts CMD.EXE for commands execution
- 1.rsp.dat.exe (PID: 956)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:10 14:05:01+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 5889024 |
| InitializedDataSize: | 25088 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x59fa2e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | topinambour.exe |
| LegalCopyright: | |
| OriginalFileName: | topinambour.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Sep-2018 12:05:01 |
| FileDescription: | - |
| FileVersion: | 0.0.0.0 |
| InternalName: | topinambour.exe |
| LegalCopyright: | - |
| OriginalFilename: | topinambour.exe |
| ProductVersion: | 0.0.0.0 |
| Assembly Version: | 0.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-Sep-2018 12:05:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0059DA34 | 0x0059DC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.98877 |
.rsrc | 0x005A0000 | 0x00005E38 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0988 |
.reloc | 0x005A6000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.25522 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.84324 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.21926 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.69111 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.79162 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.1771 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.74745 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
39
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "cmd" /c schtasks /create /SC MINUTE /MO 30 /TR %localappdata%\VirtualStore\certcheck.exe /TN VerifiedPublisherCertCheck /F | C:\Windows\system32\cmd.exe | — | 1.rsp.dat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 956 | "C:\Users\admin\AppData\Local\Temp\1.rsp.dat.exe" | C:\Users\admin\AppData\Local\Temp\1.rsp.dat.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1980 | "C:\Users\admin\AppData\Local\Temp\TeamViewer_Setup_ru.exe" | C:\Users\admin\AppData\Local\Temp\TeamViewer_Setup_ru.exe | 1.rsp.dat.exe | ||||||||||||
User: admin Company: TeamViewer GmbH Integrity Level: MEDIUM Exit code: 0 Version: 9.0.25942.0 Modules
| |||||||||||||||
| 2588 | schtasks /create /SC MINUTE /MO 30 /TR C:\Users\admin\AppData\Local\VirtualStore\certcheck.exe /TN VerifiedPublisherCertCheck /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3136 | "C:\Users\admin\AppData\Local\Temp\TeamViewer\Version9\TeamViewer_.exe" | C:\Users\admin\AppData\Local\Temp\TeamViewer\Version9\TeamViewer_.exe | TeamViewer_Setup_ru.exe | ||||||||||||
User: admin Company: TeamViewer Integrity Level: MEDIUM Description: TeamViewer Remote Control Application Installer Exit code: 0 Version: 9.0.25942.0 Modules
| |||||||||||||||
Total events
1 033
Read events
1 029
Write events
4
Delete events
0
Modification events
| (PID) Process: | (956) 1.rsp.dat.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (956) 1.rsp.dat.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
9
Suspicious files
0
Text files
59
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1980 | TeamViewer_Setup_ru.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\Version9\tvinfo.ini | text | |
MD5:— | SHA256:— | |||
| 3136 | TeamViewer_.exe | C:\Users\admin\AppData\Local\Temp\nsmDC44.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3136 | TeamViewer_.exe | C:\Users\admin\AppData\Local\Temp\nsmDC44.tmp\start_unicode.ini | text | |
MD5:— | SHA256:— | |||
| 3136 | TeamViewer_.exe | C:\Users\admin\AppData\Local\Temp\nsmDC44.tmp\environment_unicode.ini | text | |
MD5:— | SHA256:— | |||
| 3136 | TeamViewer_.exe | C:\Users\admin\AppData\Local\Temp\nsmDC44.tmp\vpn_unicode.ini | text | |
MD5:— | SHA256:— | |||
| 3136 | TeamViewer_.exe | C:\Users\admin\AppData\Local\Temp\nsmDC44.tmp\host_unicode.ini | text | |
MD5:— | SHA256:— | |||
| 3136 | TeamViewer_.exe | C:\Users\admin\AppData\Local\Temp\nsmDC44.tmp\advanced_unicode.ini | text | |
MD5:— | SHA256:— | |||
| 1980 | TeamViewer_Setup_ru.exe | C:\Users\admin\AppData\Local\Temp\TeamViewer\Version9\TeamViewer_.exe | executable | |
MD5:— | SHA256:— | |||
| 3136 | TeamViewer_.exe | C:\Users\admin\AppData\Local\Temp\nsmDC44.tmp\Lizenz_TeamViewer_EN_unicode.txt | text | |
MD5:8D69AA2DC0CF6E66CAF4946547A23287 | SHA256:6344C1162B89B7236A1FEE925366C1BDAB1634C4737214DB61E94B0667F8FC41 | |||
| 3136 | TeamViewer_.exe | C:\Users\admin\AppData\Local\Temp\nsmDC44.tmp\System.dll | executable | |
MD5:BF712F32249029466FA86756F5546950 | SHA256:7851CB12FA4131F1FEE5DE390D650EF65CAC561279F1CFE70AD16CC9780210AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report