| File name: | 2-HPN-2019-G18436.js |
| Full analysis: | https://app.any.run/tasks/9ffd5bf6-2984-4420-8e85-df8231bd09bf |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 24, 2019, 19:32:35 |
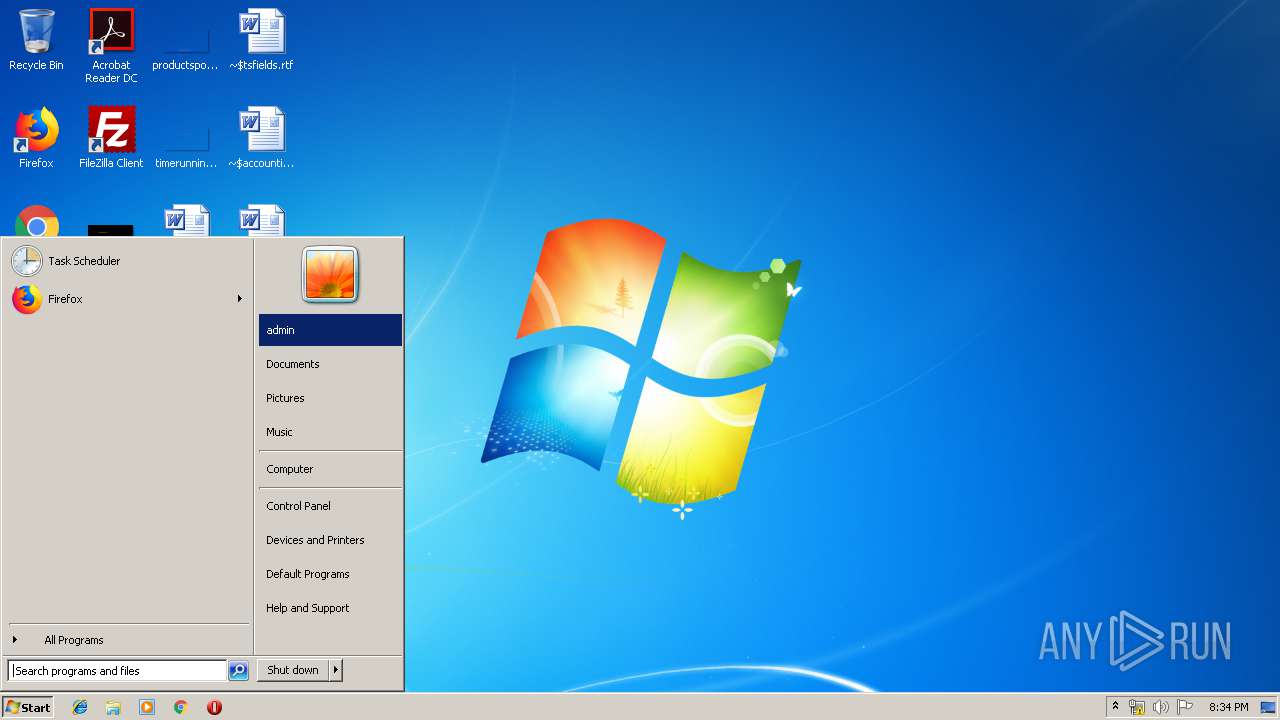
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
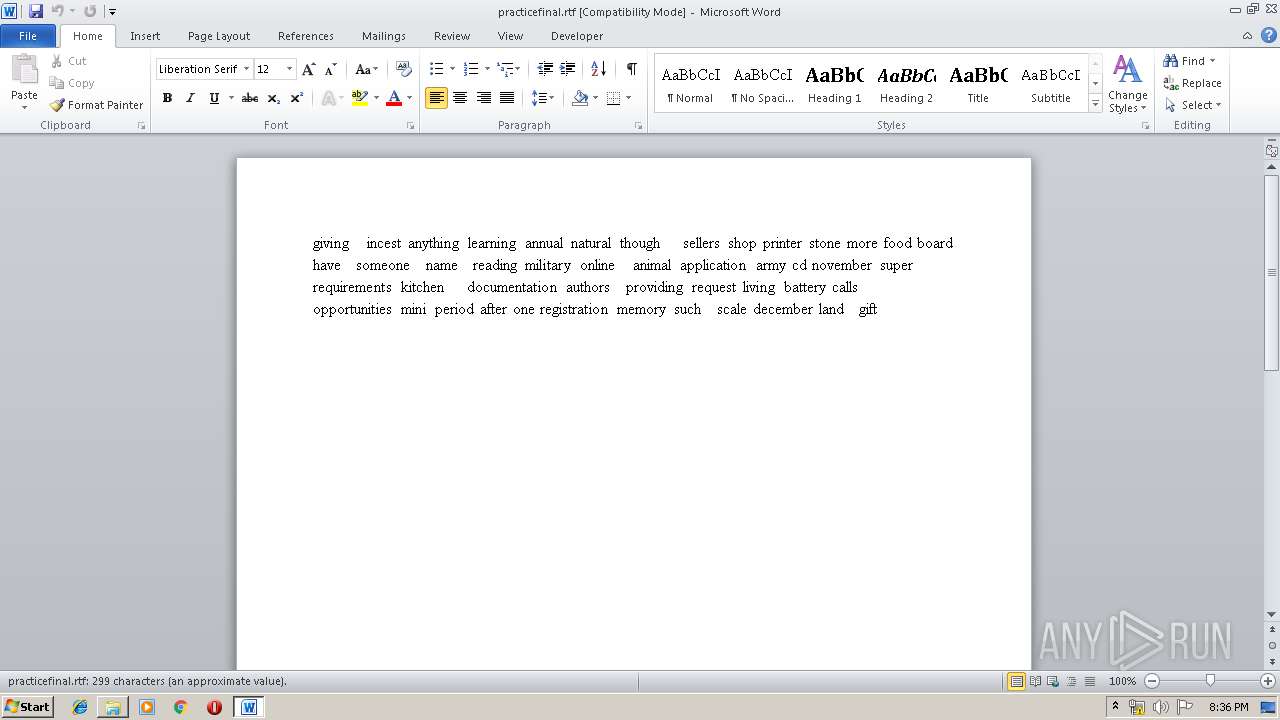
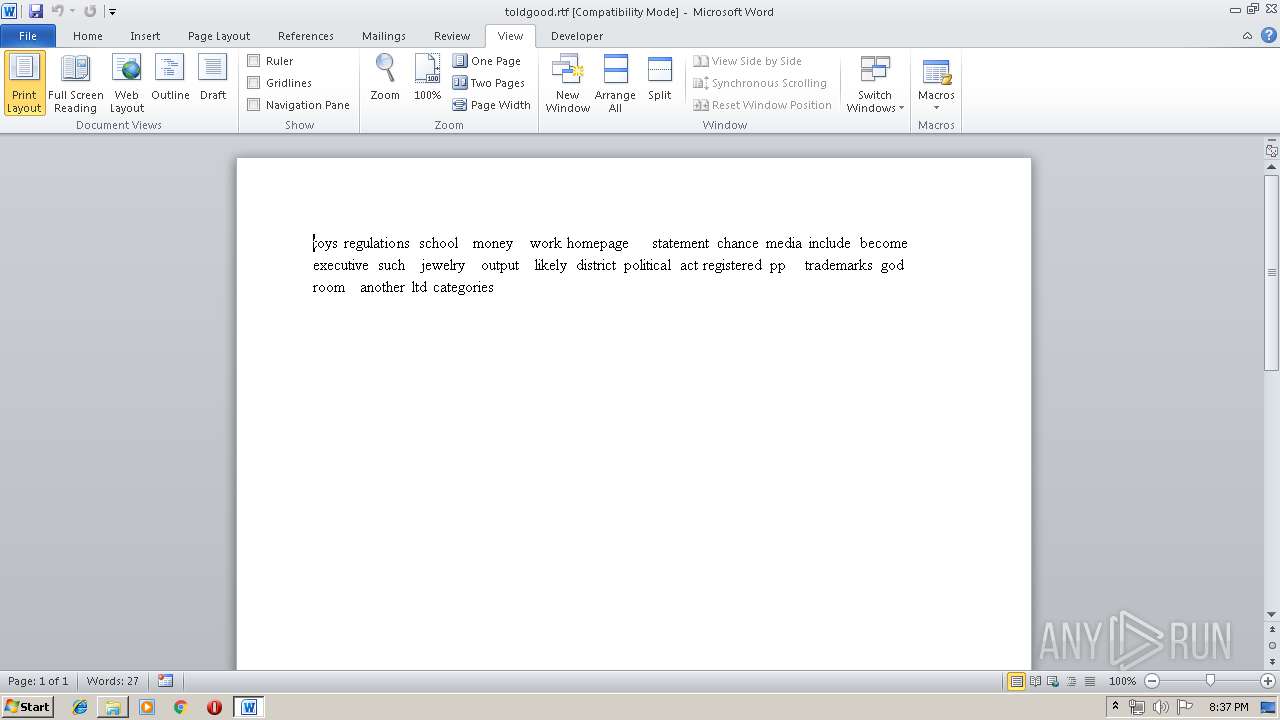
| MIME: | text/plain |
| File info: | ASCII text, with very long lines |
| MD5: | C3B85967B800F9F28D040F8C91A8F9AD |
| SHA1: | 552E9792700824E9ECBF0A065ED522868637158E |
| SHA256: | 0088ADB4E86956B8B15A3CB45156F74A95644C88CE5572EC601E10DE5BA1BADD |
| SSDEEP: | 3072:4DqwRZ04gpIaGgZIpTRDNRNHfA6wkG1TEd93dnJ+cEmw4K:vp4K |
MALICIOUS
Downloads executable files from the Internet
- WScript.exe (PID: 1812)
Application was dropped or rewritten from another process
- zdvtodvh1.exe (PID: 2940)
- zdvtodvh1.exe (PID: 2424)
- soundser.exe (PID: 3700)
- soundser.exe (PID: 4024)
- SSDGB43XiH.exe (PID: 2456)
- SSDGB43XiH.exe (PID: 2652)
- soundser.exe (PID: 4048)
- soundser.exe (PID: 4036)
Connects to CnC server
- soundser.exe (PID: 4024)
- soundser.exe (PID: 4036)
EMOTET was detected
- soundser.exe (PID: 4024)
- soundser.exe (PID: 4036)
Emotet process was detected
- soundser.exe (PID: 3700)
- soundser.exe (PID: 4048)
Changes the autorun value in the registry
- soundser.exe (PID: 4024)
- soundser.exe (PID: 4036)
SUSPICIOUS
Executable content was dropped or overwritten
- WScript.exe (PID: 1812)
- zdvtodvh1.exe (PID: 2424)
- soundser.exe (PID: 4024)
- SSDGB43XiH.exe (PID: 2652)
Creates files in the user directory
- WScript.exe (PID: 1812)
Application launched itself
- zdvtodvh1.exe (PID: 2940)
- soundser.exe (PID: 3700)
- SSDGB43XiH.exe (PID: 2456)
- soundser.exe (PID: 4048)
Starts itself from another location
- zdvtodvh1.exe (PID: 2424)
- SSDGB43XiH.exe (PID: 2652)
Connects to server without host name
- soundser.exe (PID: 4024)
INFO
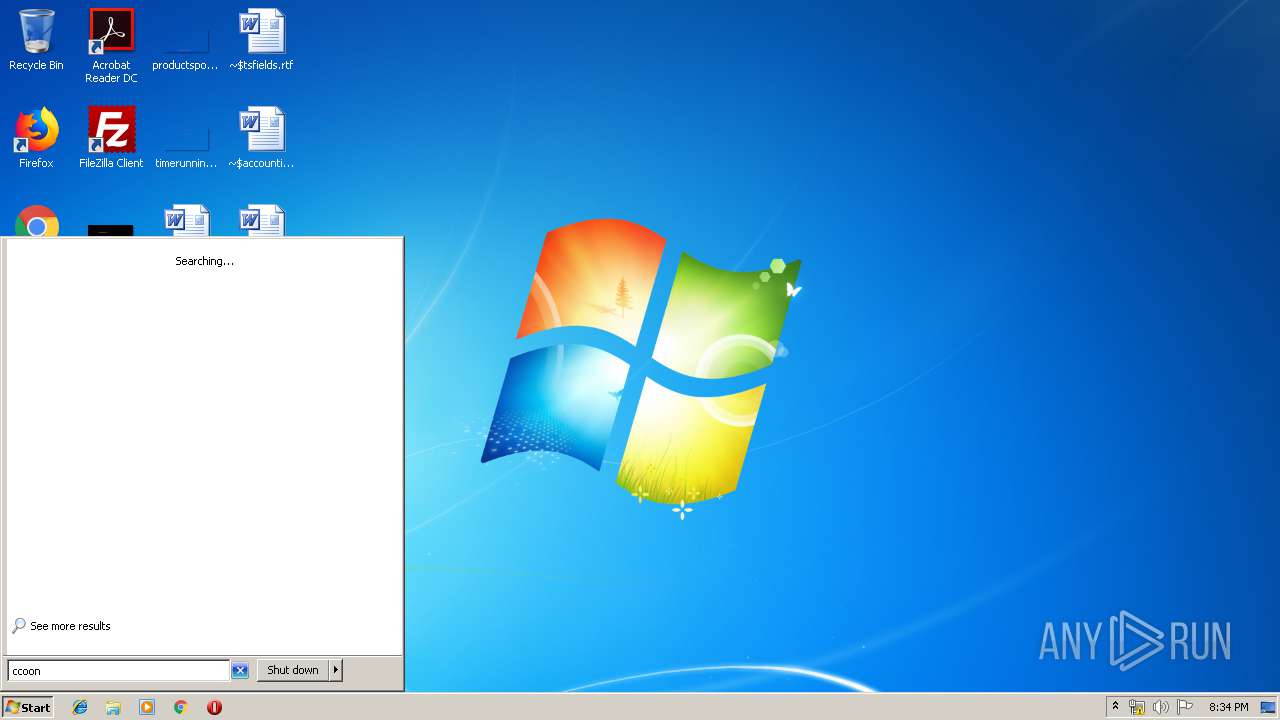
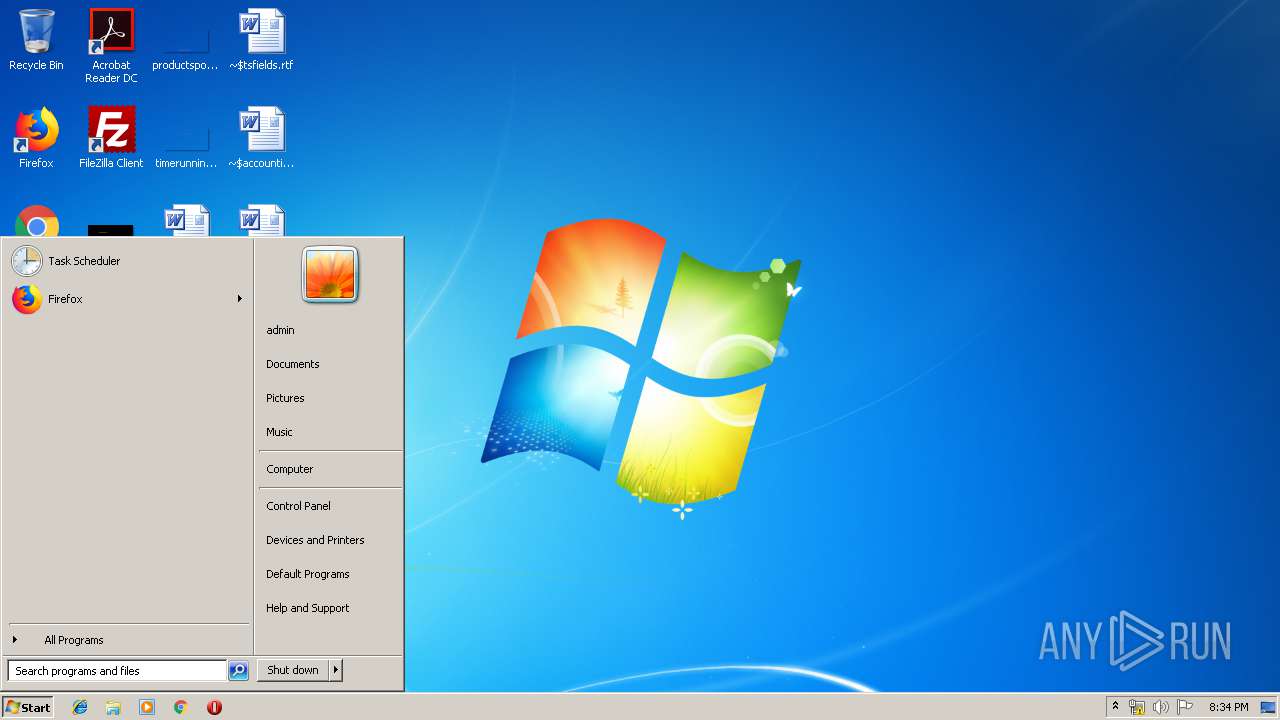
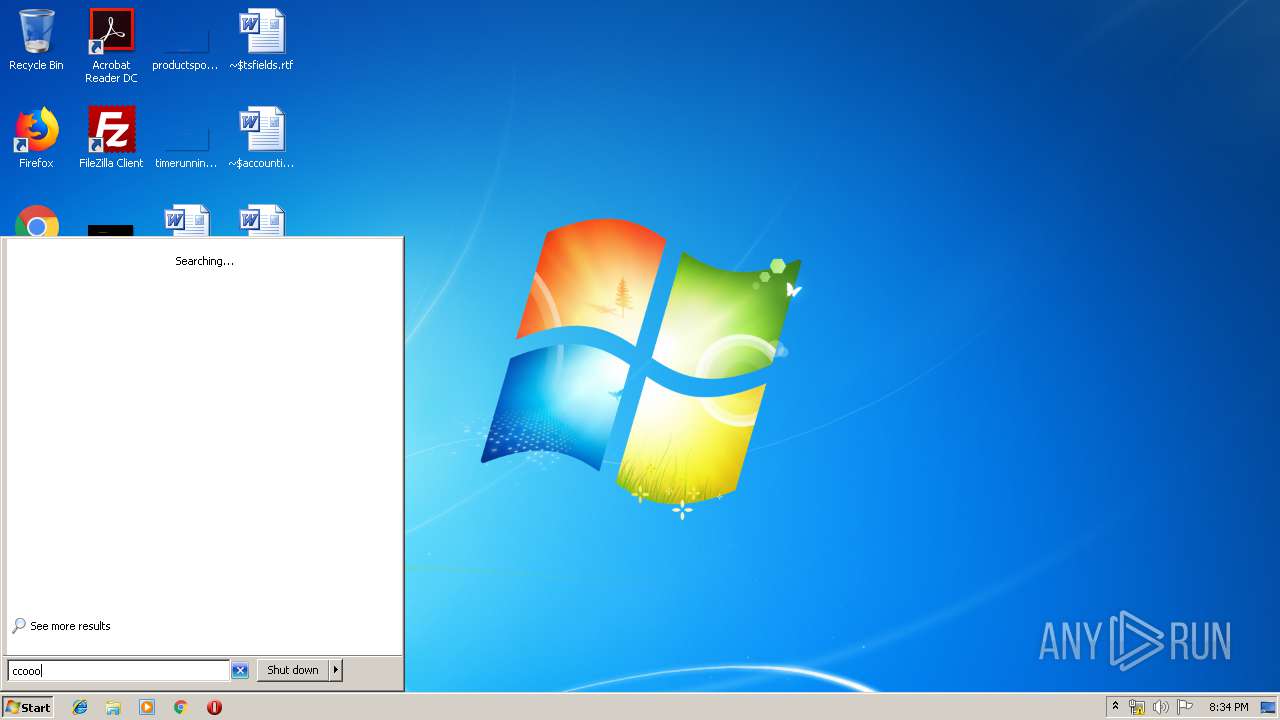
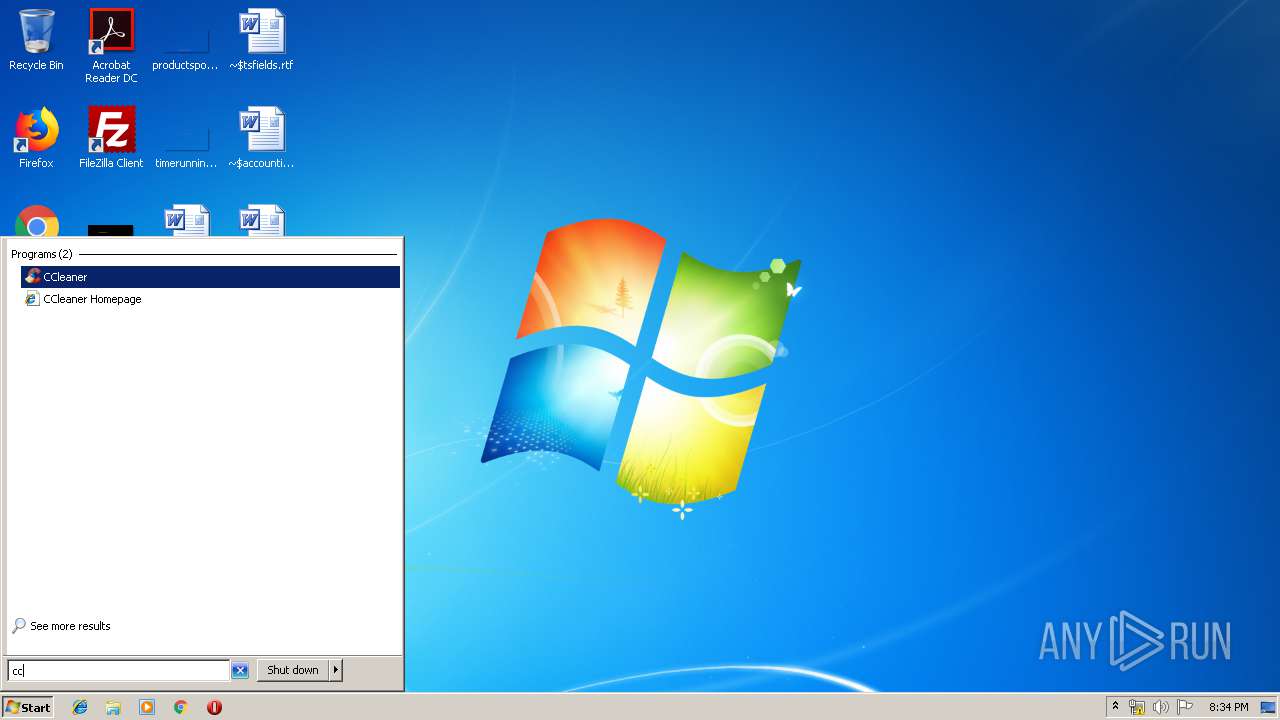
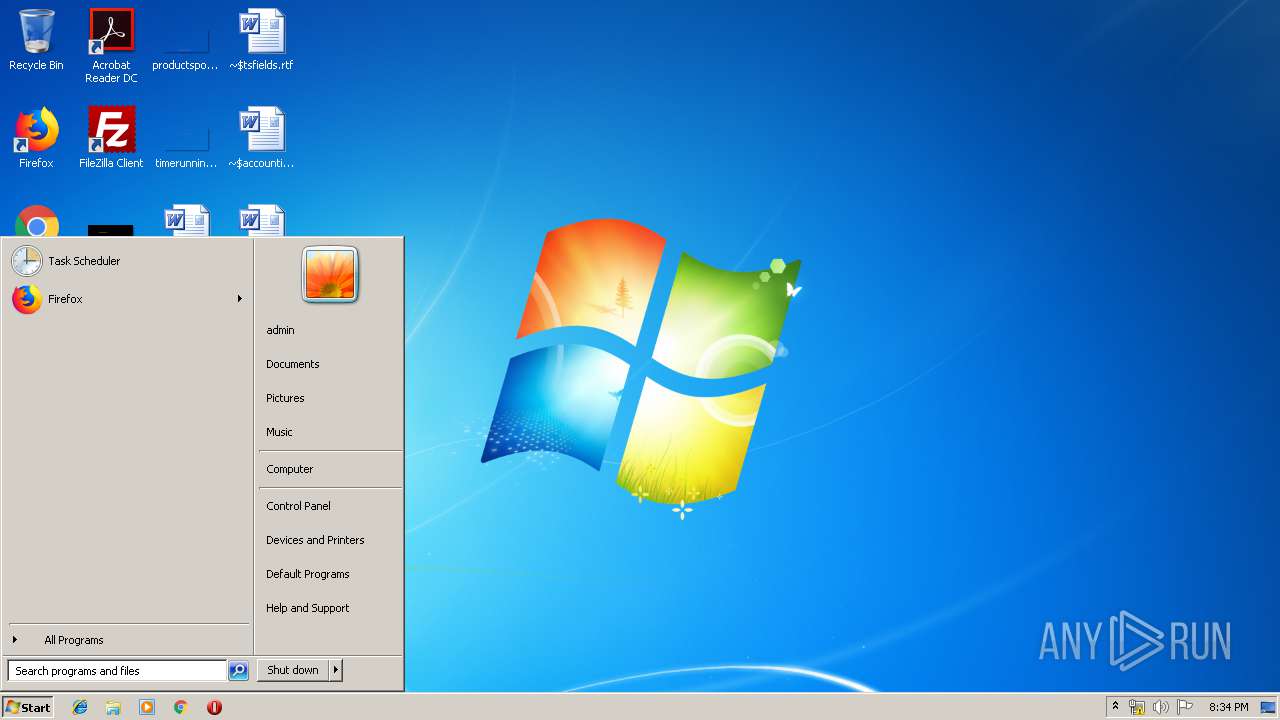
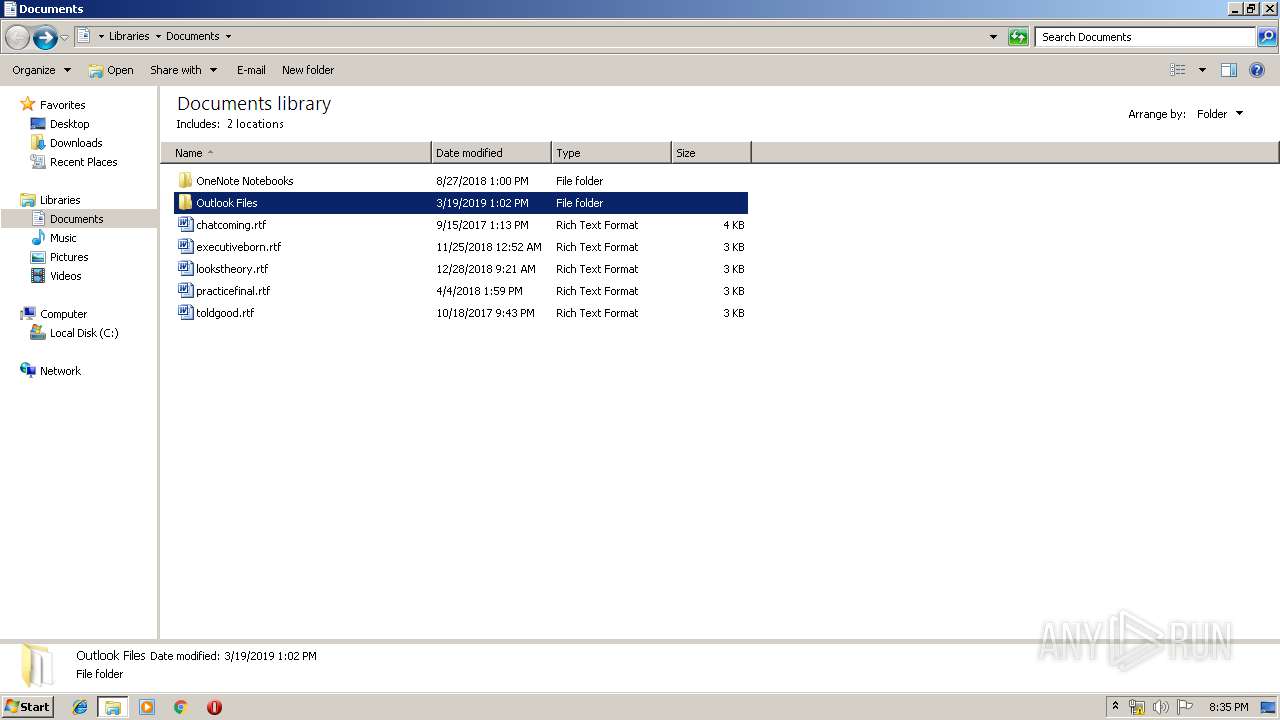
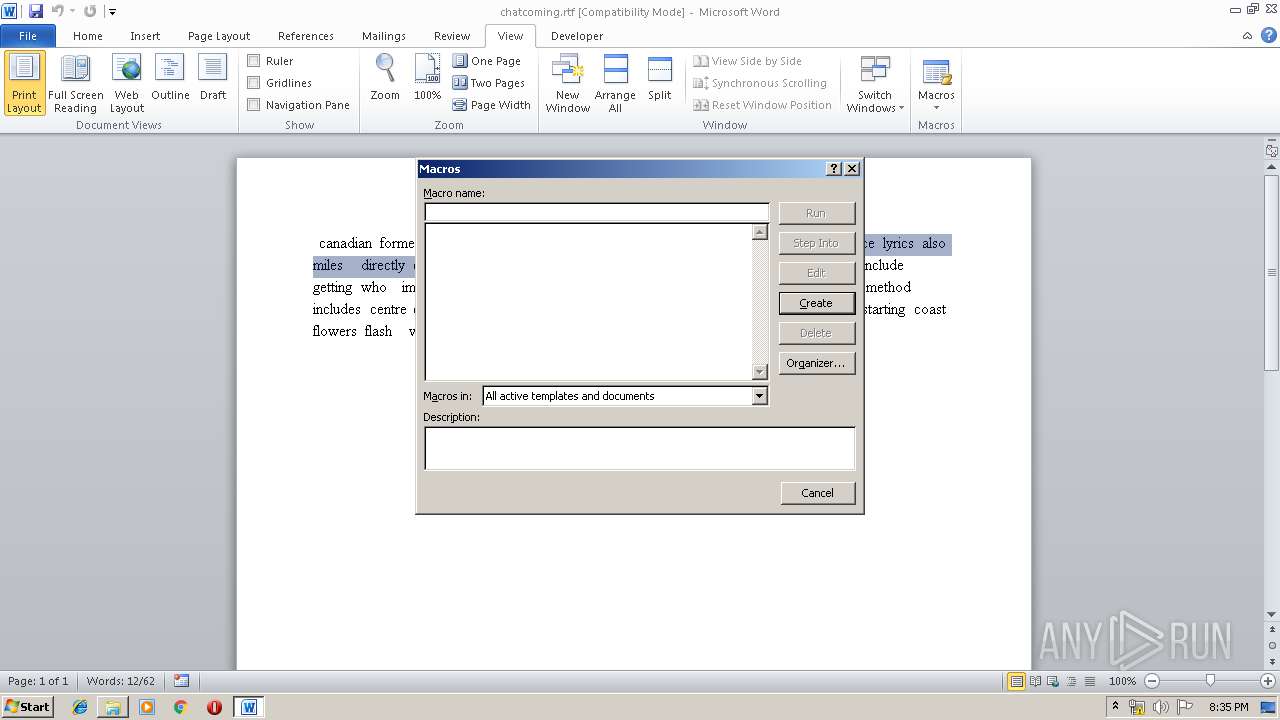
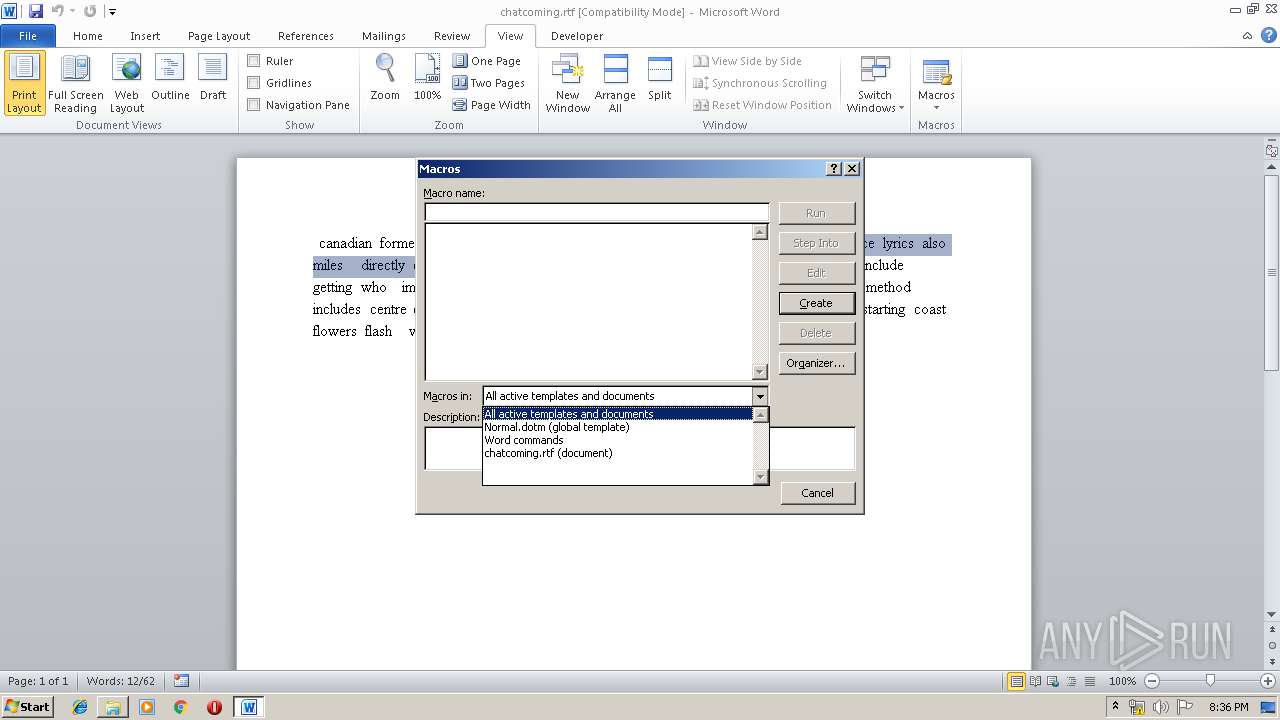
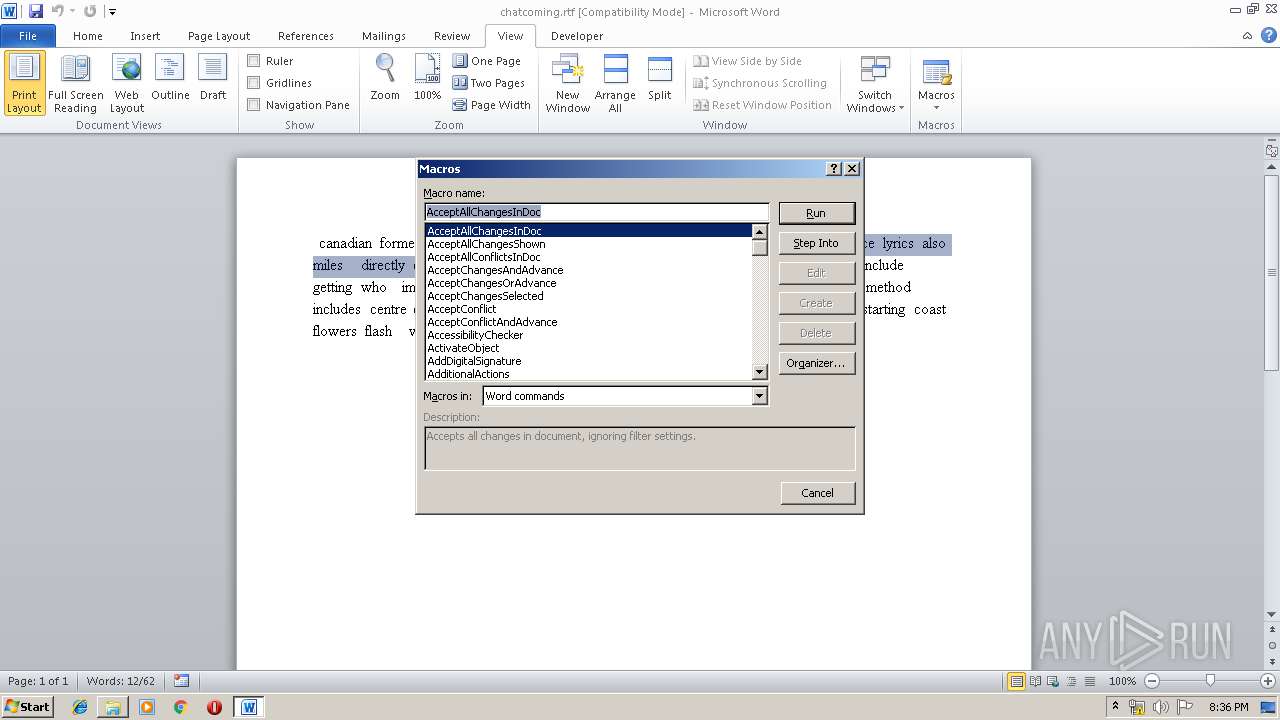
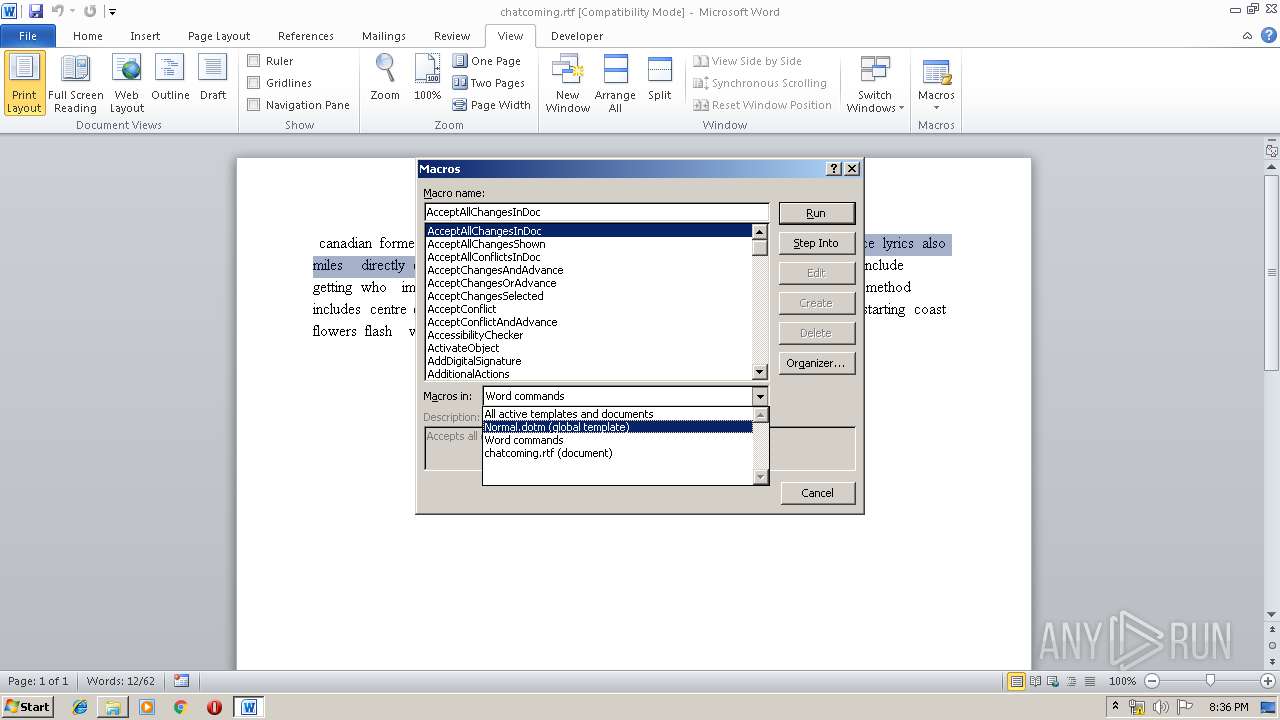
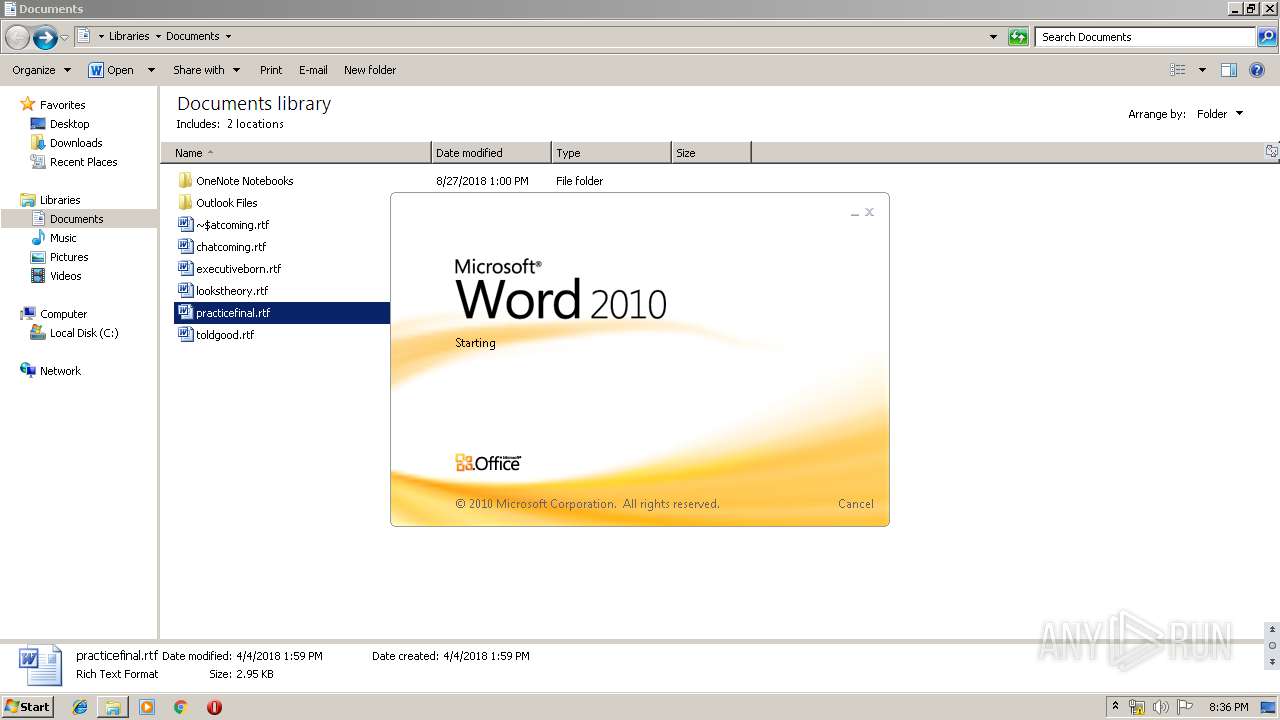
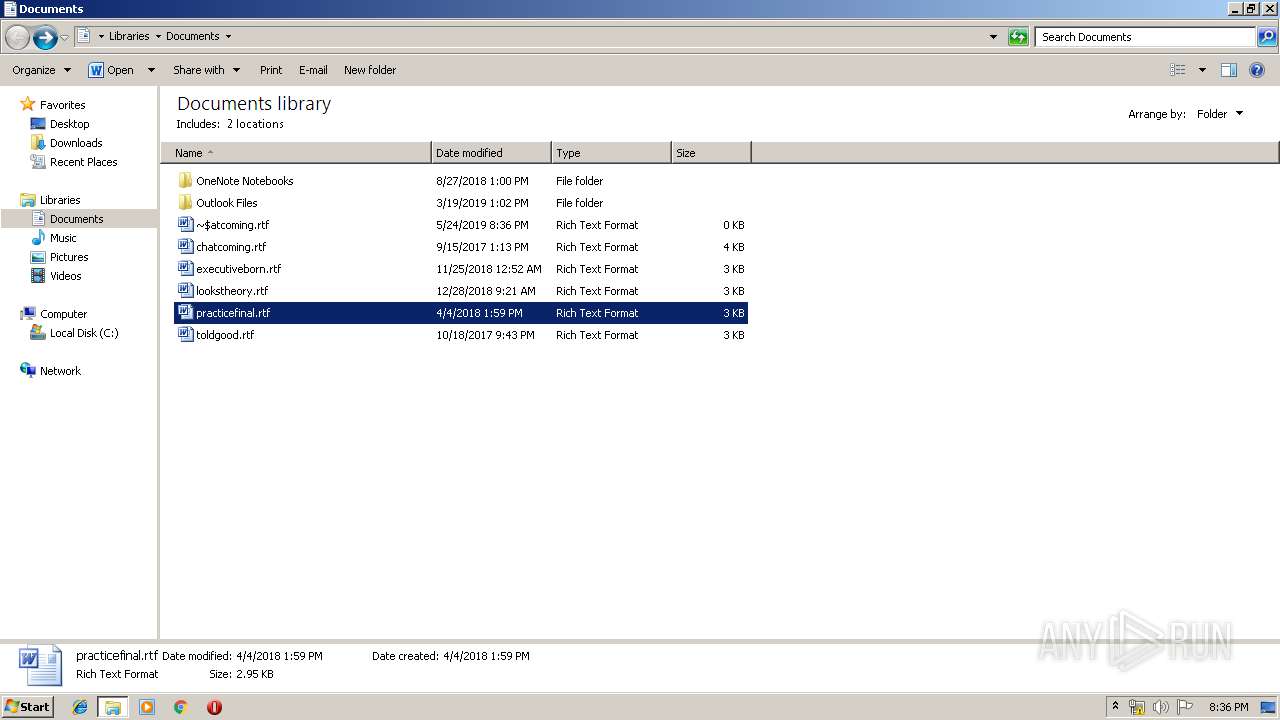
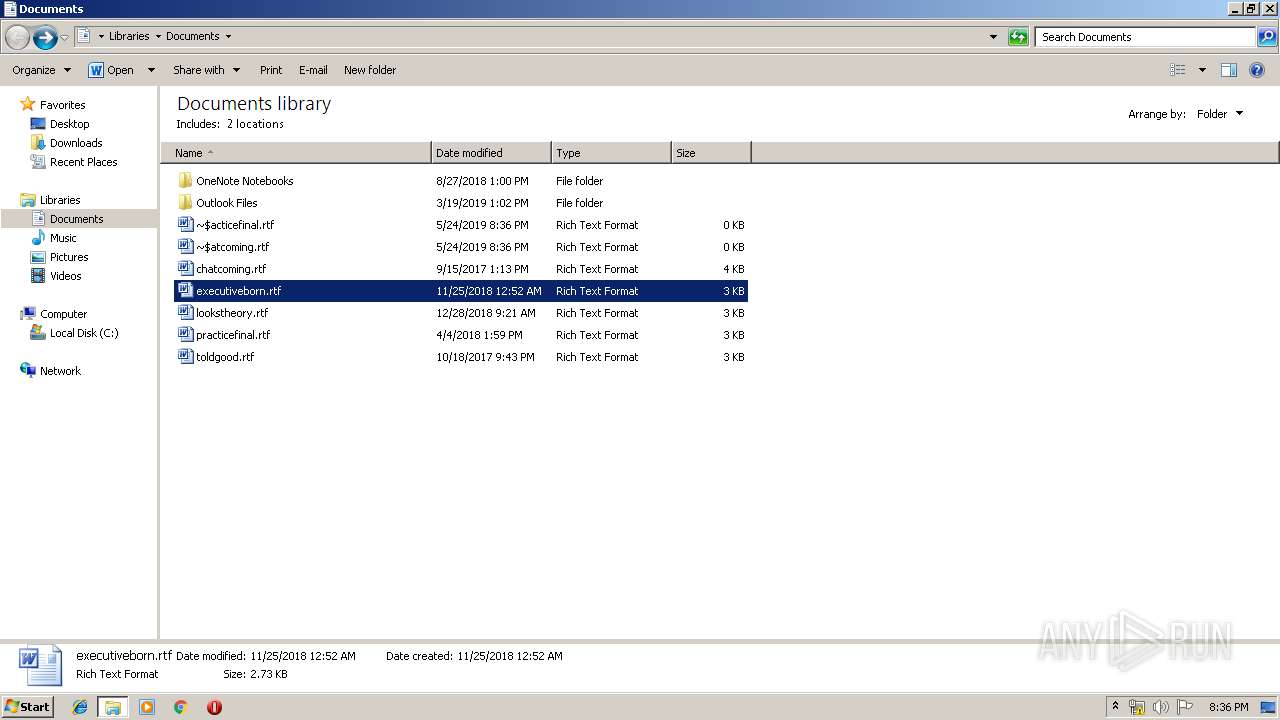
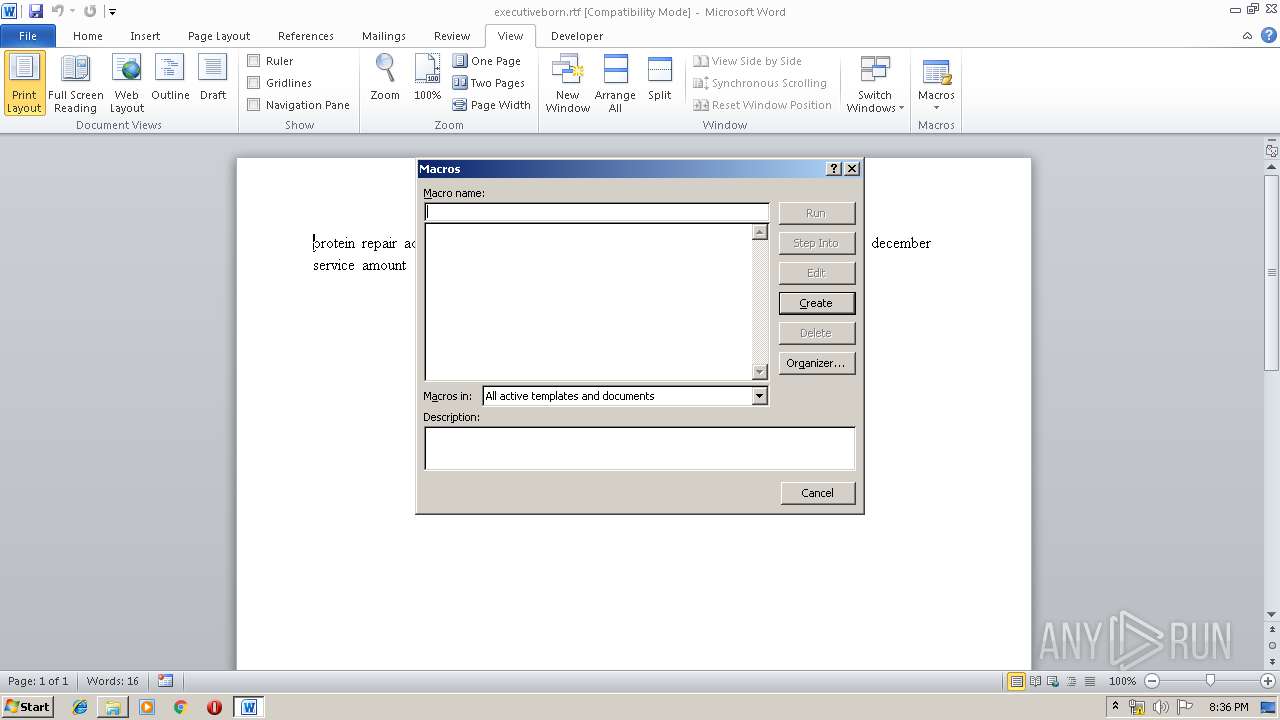
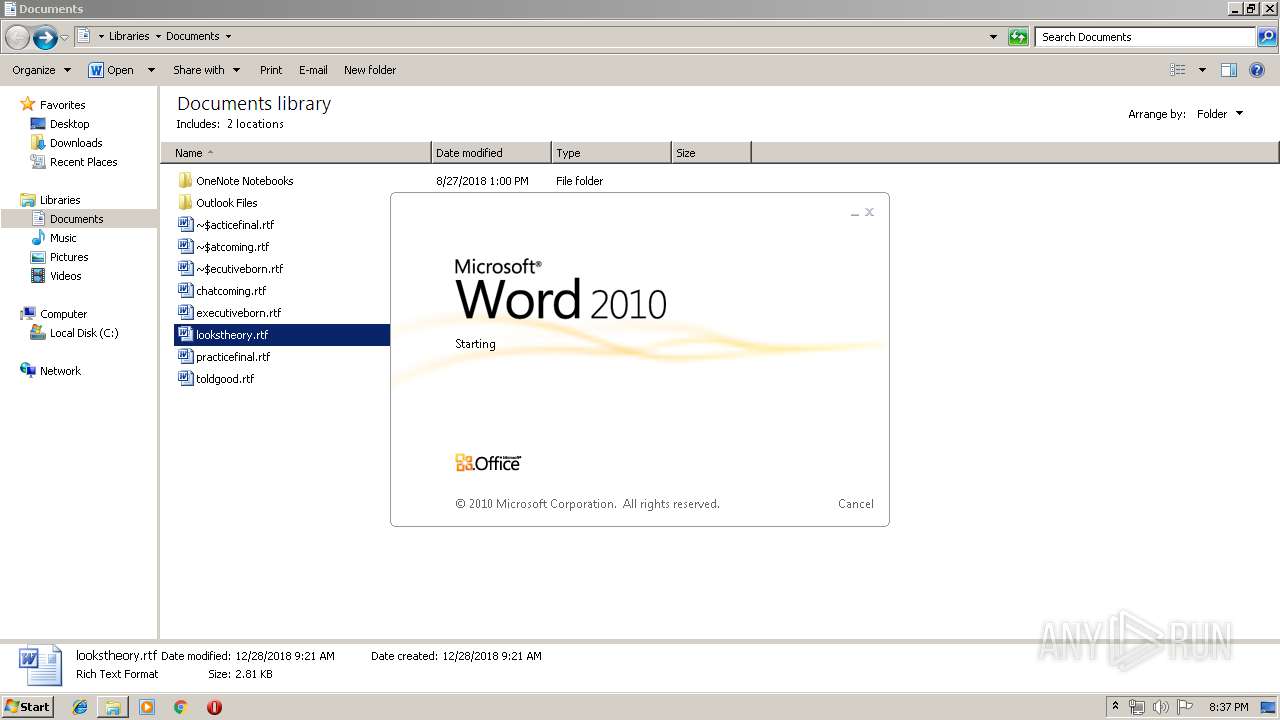
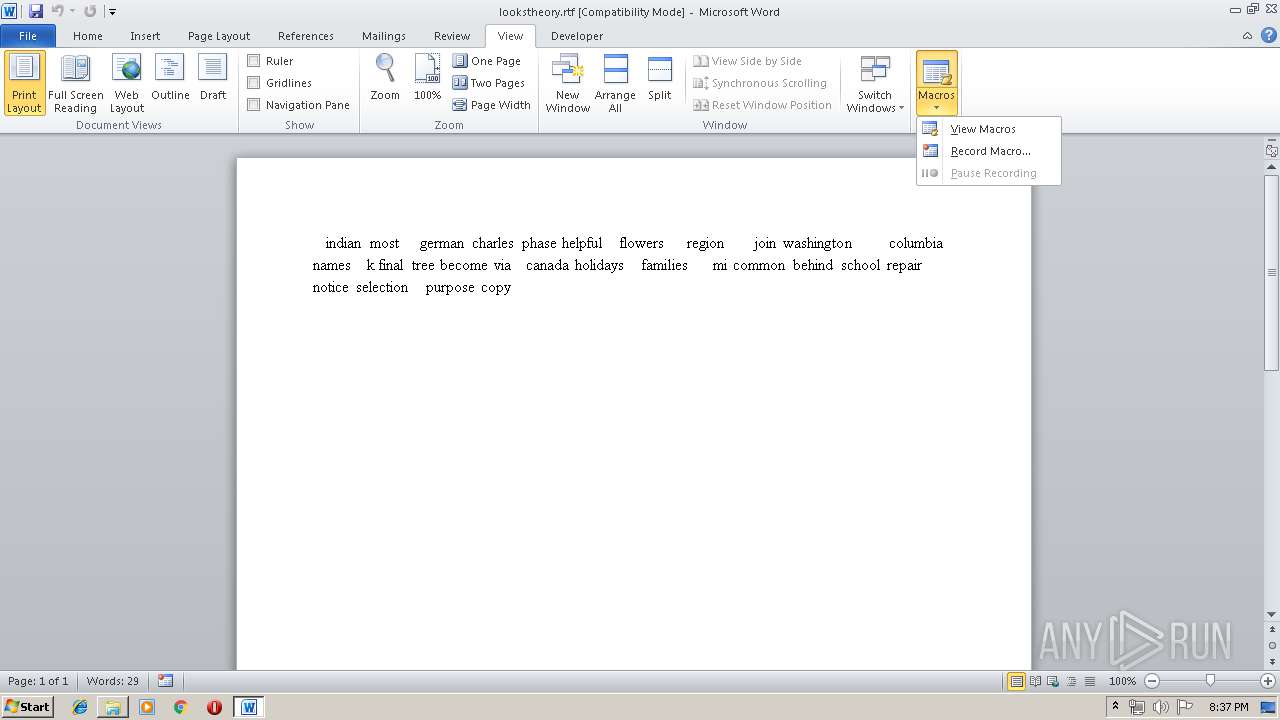
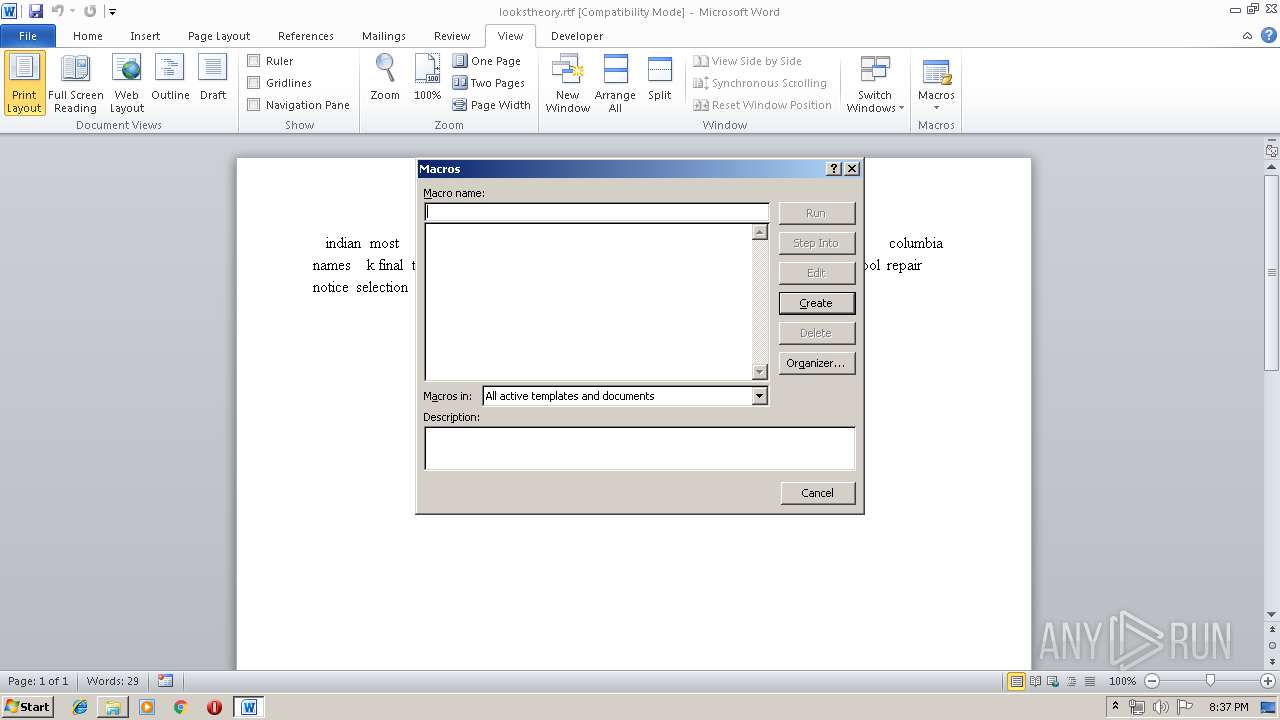
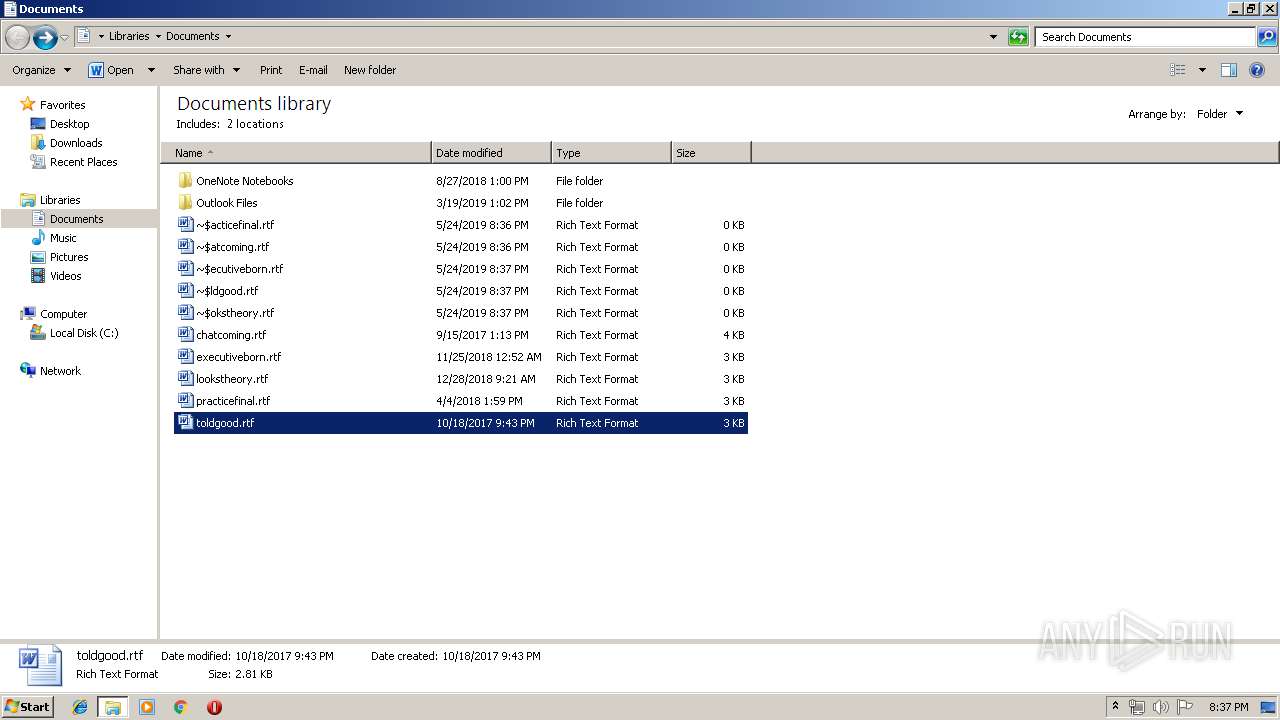
Manual execution by user
- WINWORD.EXE (PID: 2804)
- WINWORD.EXE (PID: 772)
- WINWORD.EXE (PID: 3004)
- WINWORD.EXE (PID: 1012)
- WINWORD.EXE (PID: 580)
- WINWORD.EXE (PID: 2744)
- WINWORD.EXE (PID: 2892)
- WINWORD.EXE (PID: 2676)
- WINWORD.EXE (PID: 2972)
- WINWORD.EXE (PID: 392)
- WINWORD.EXE (PID: 1828)
- WINWORD.EXE (PID: 2772)
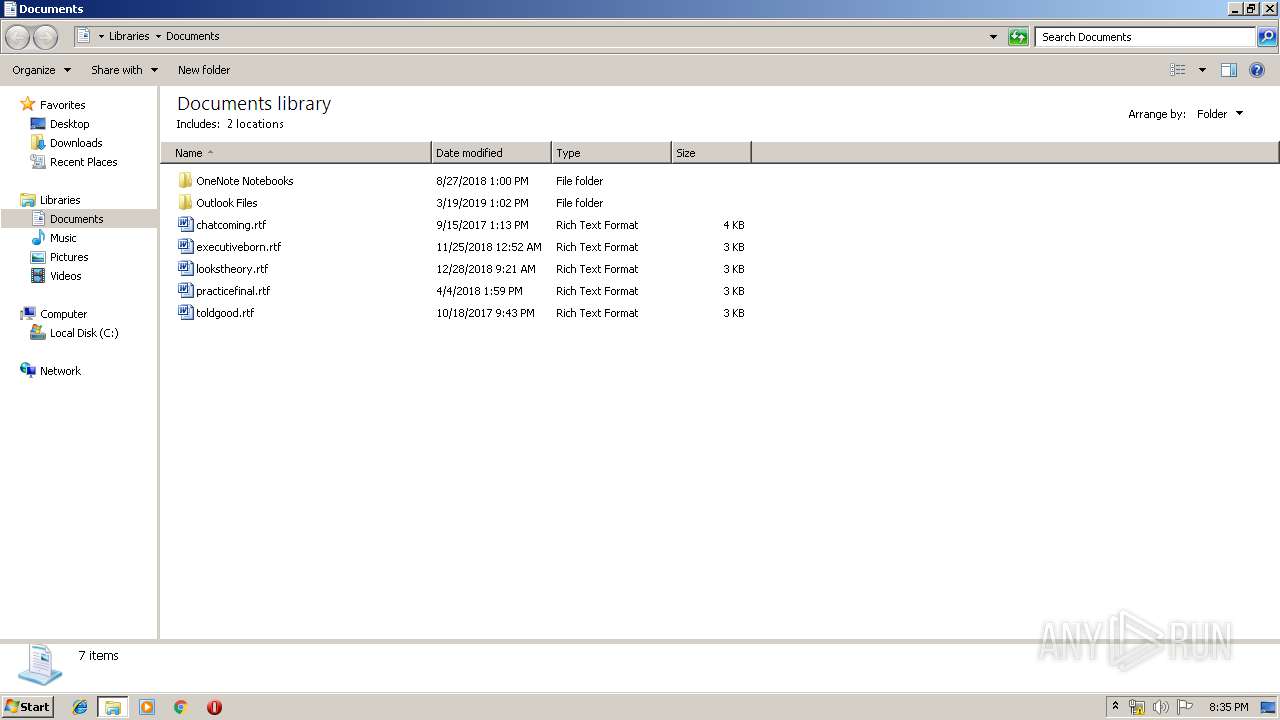
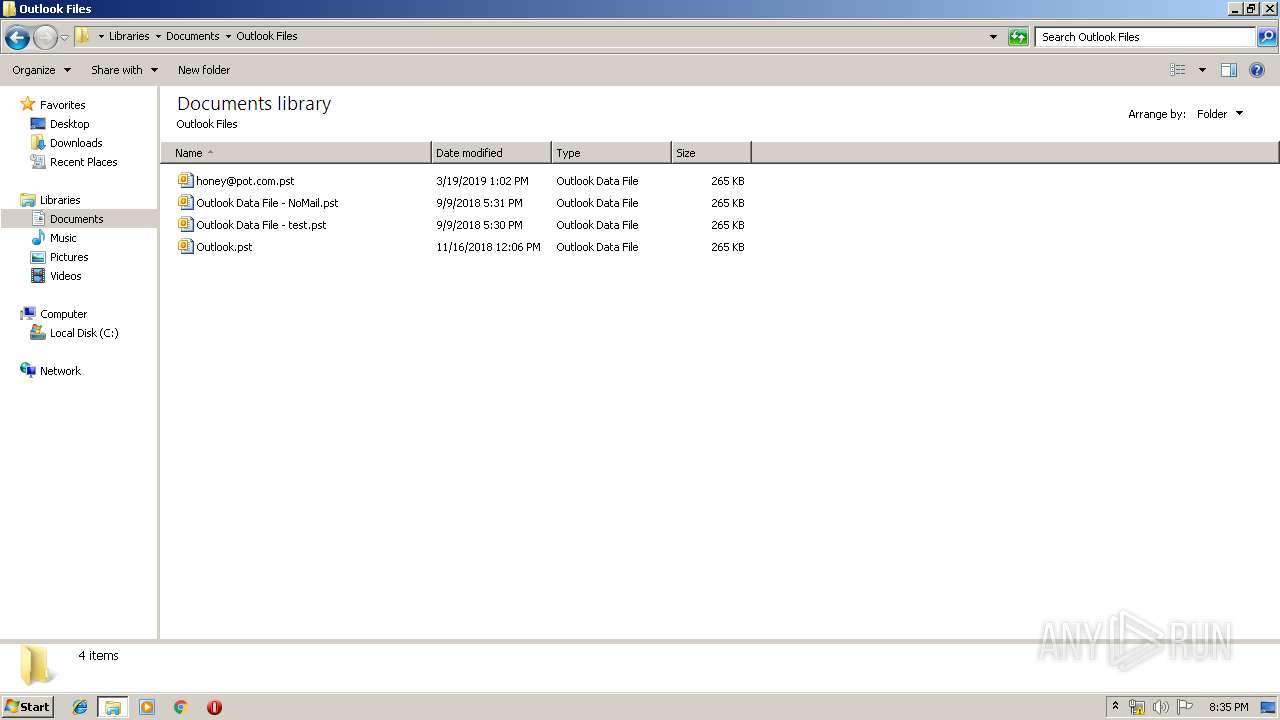
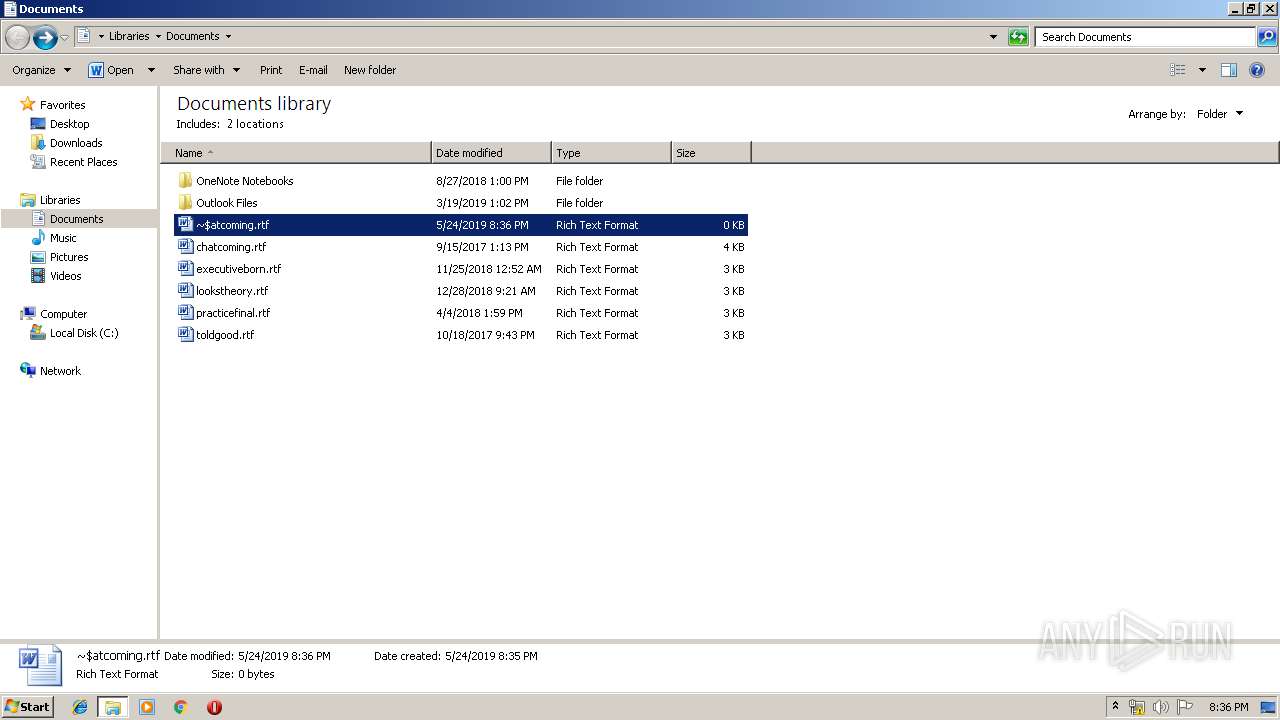
Creates files in the user directory
- WINWORD.EXE (PID: 2804)
- WINWORD.EXE (PID: 772)
- WINWORD.EXE (PID: 1828)
- WINWORD.EXE (PID: 580)
- WINWORD.EXE (PID: 1012)
- WINWORD.EXE (PID: 2772)
- WINWORD.EXE (PID: 2892)
- WINWORD.EXE (PID: 2676)
- WINWORD.EXE (PID: 2972)
- WINWORD.EXE (PID: 2744)
- WINWORD.EXE (PID: 392)
- WINWORD.EXE (PID: 3004)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 772)
- WINWORD.EXE (PID: 2804)
- WINWORD.EXE (PID: 3004)
- WINWORD.EXE (PID: 580)
- WINWORD.EXE (PID: 1012)
- WINWORD.EXE (PID: 1828)
- WINWORD.EXE (PID: 2744)
- WINWORD.EXE (PID: 2892)
- WINWORD.EXE (PID: 2972)
- WINWORD.EXE (PID: 2676)
- WINWORD.EXE (PID: 392)
- WINWORD.EXE (PID: 2772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
21
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
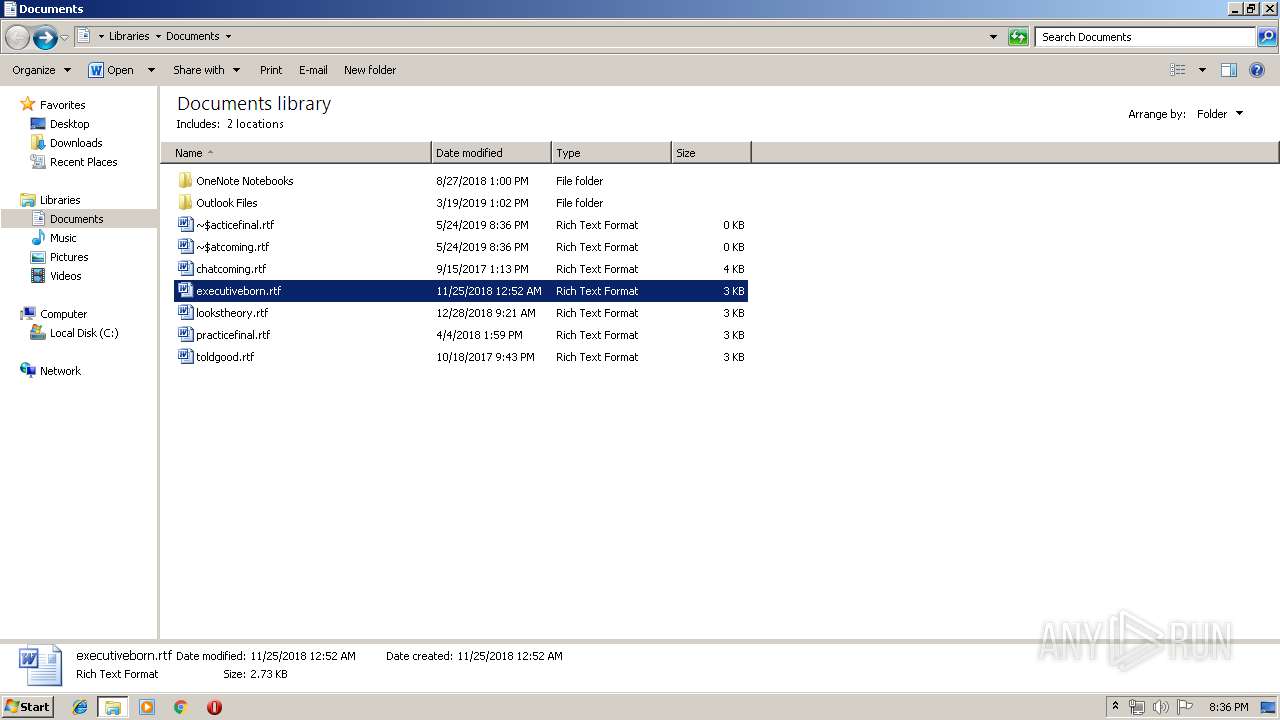
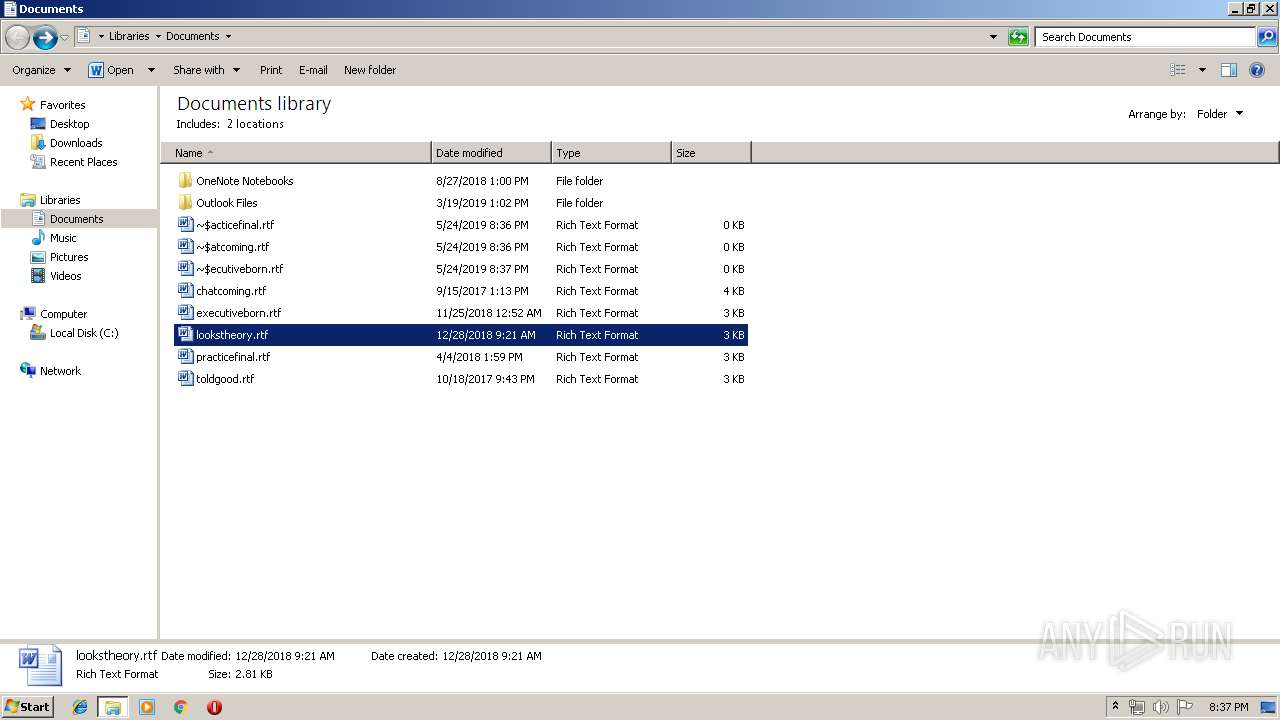
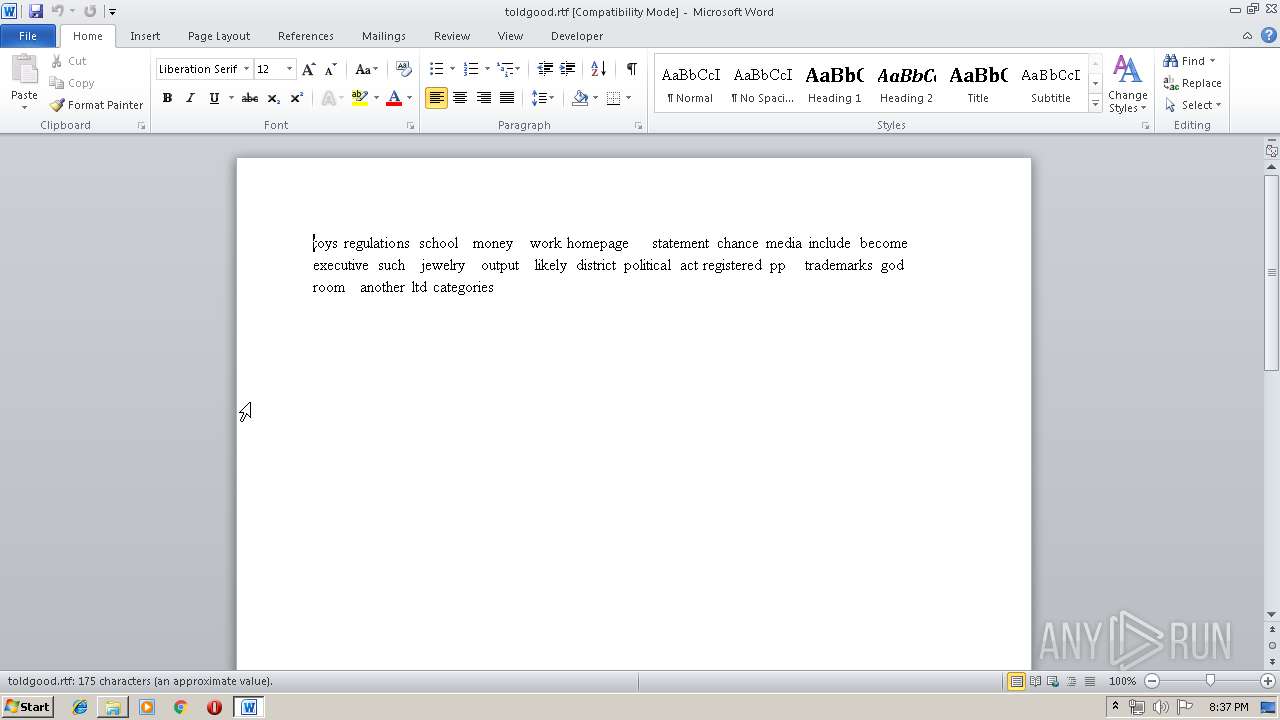
| 392 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Documents\toldgood.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\ncaccounting.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\~$rveyonly.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
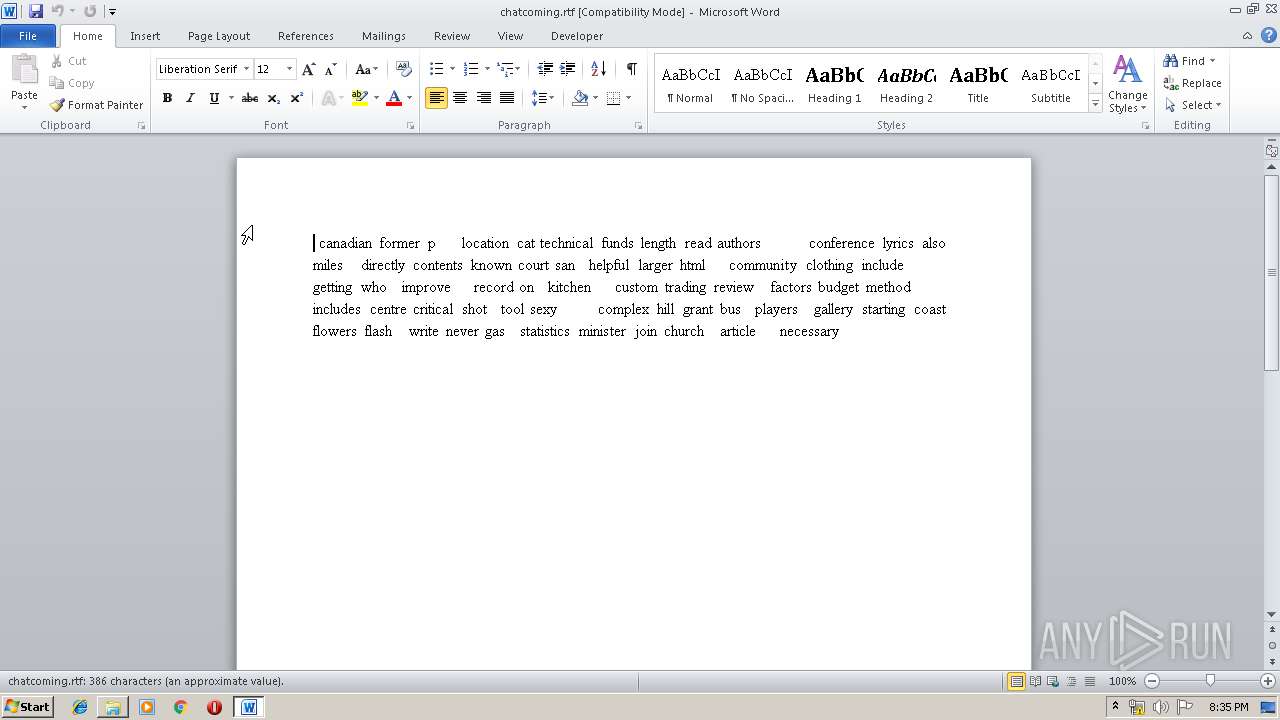
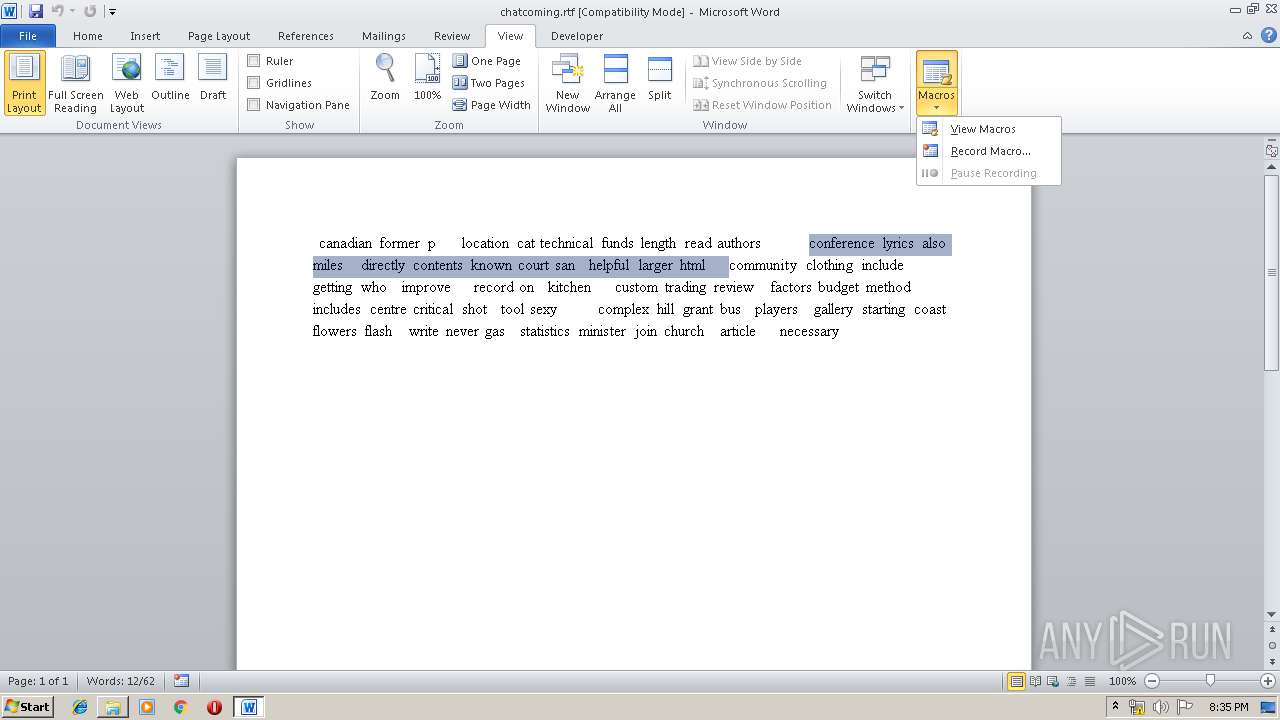
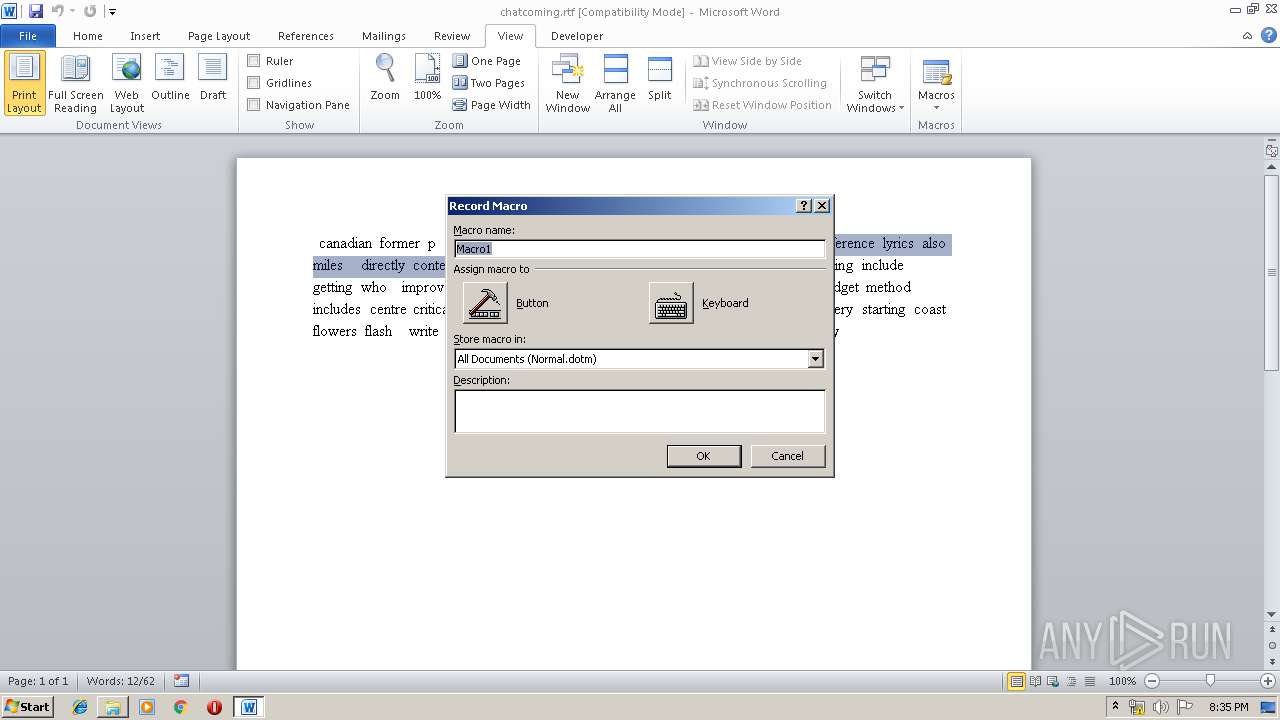
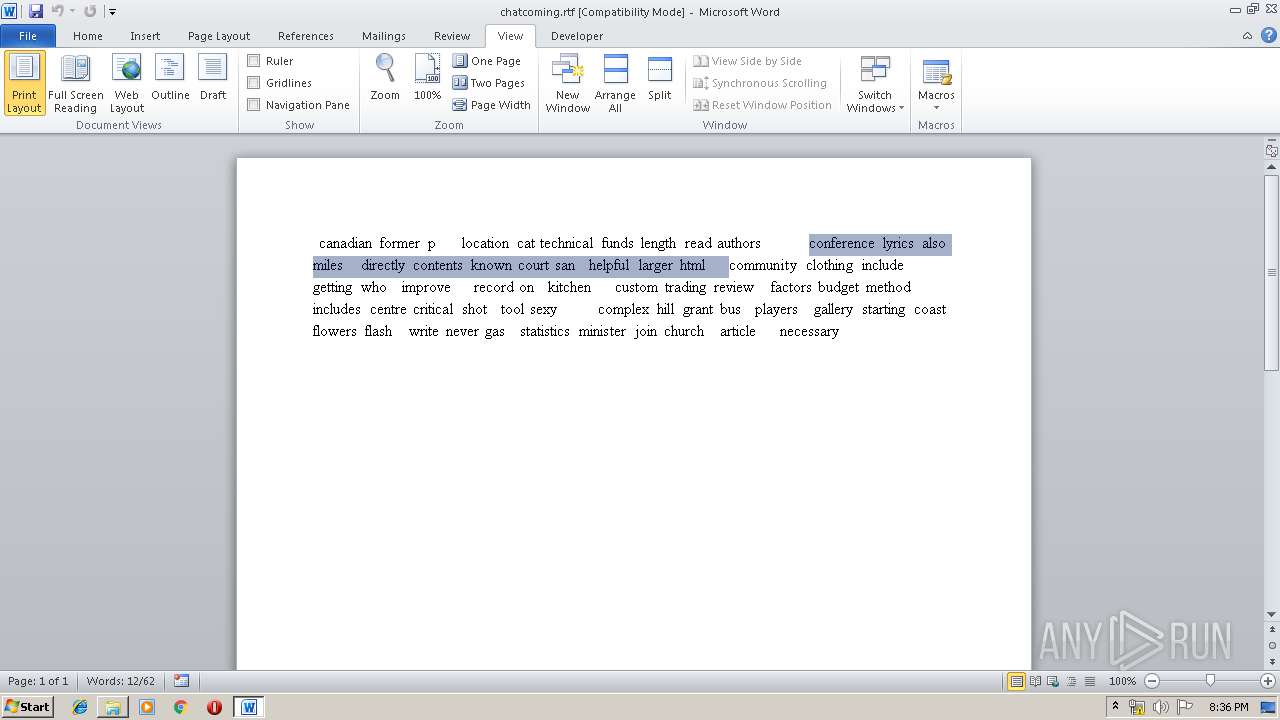
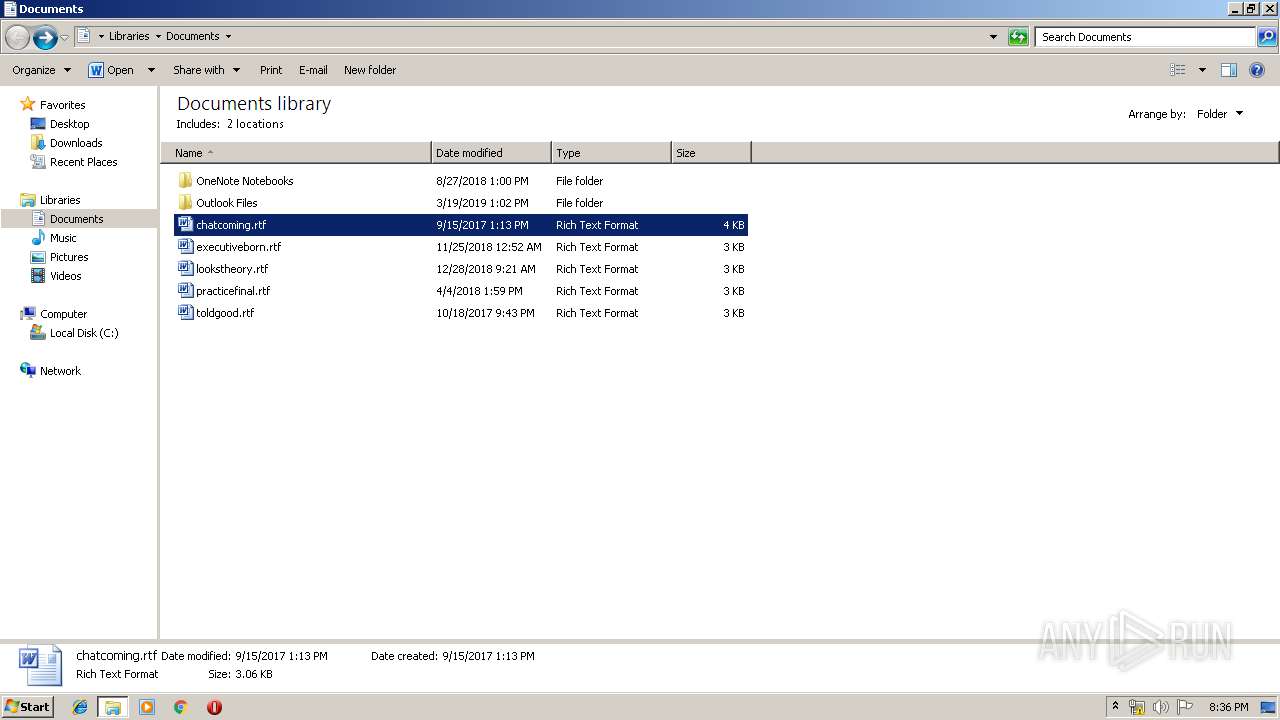
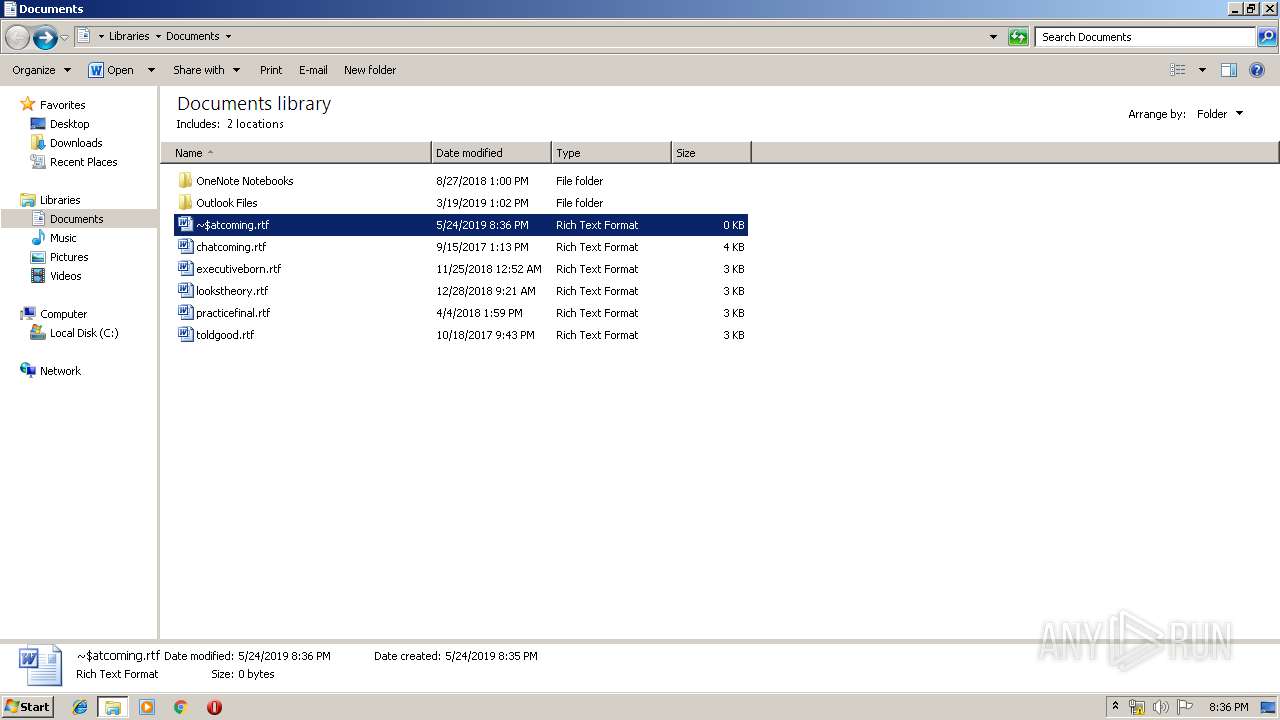
| 1012 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Documents\chatcoming.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1812 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\2-HPN-2019-G18436.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\capacitysub.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2424 | --be3ccf46 | C:\Users\admin\AppData\Local\Temp\zdvtodvh1.exe | zdvtodvh1.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: 2007 Microsoft Office component Exit code: 0 Version: 12.0.6500.5000 Modules
| |||||||||||||||
| 2456 | "C:\Users\admin\AppData\Local\soundser\SSDGB43XiH.exe" | C:\Users\admin\AppData\Local\soundser\SSDGB43XiH.exe | — | soundser.exe | |||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware Resolution Set Exit code: 0 Version: 9.6.2.31837 Modules
| |||||||||||||||
| 2652 | --9142af60 | C:\Users\admin\AppData\Local\soundser\SSDGB43XiH.exe | SSDGB43XiH.exe | ||||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware Resolution Set Exit code: 0 Version: 9.6.2.31837 Modules
| |||||||||||||||
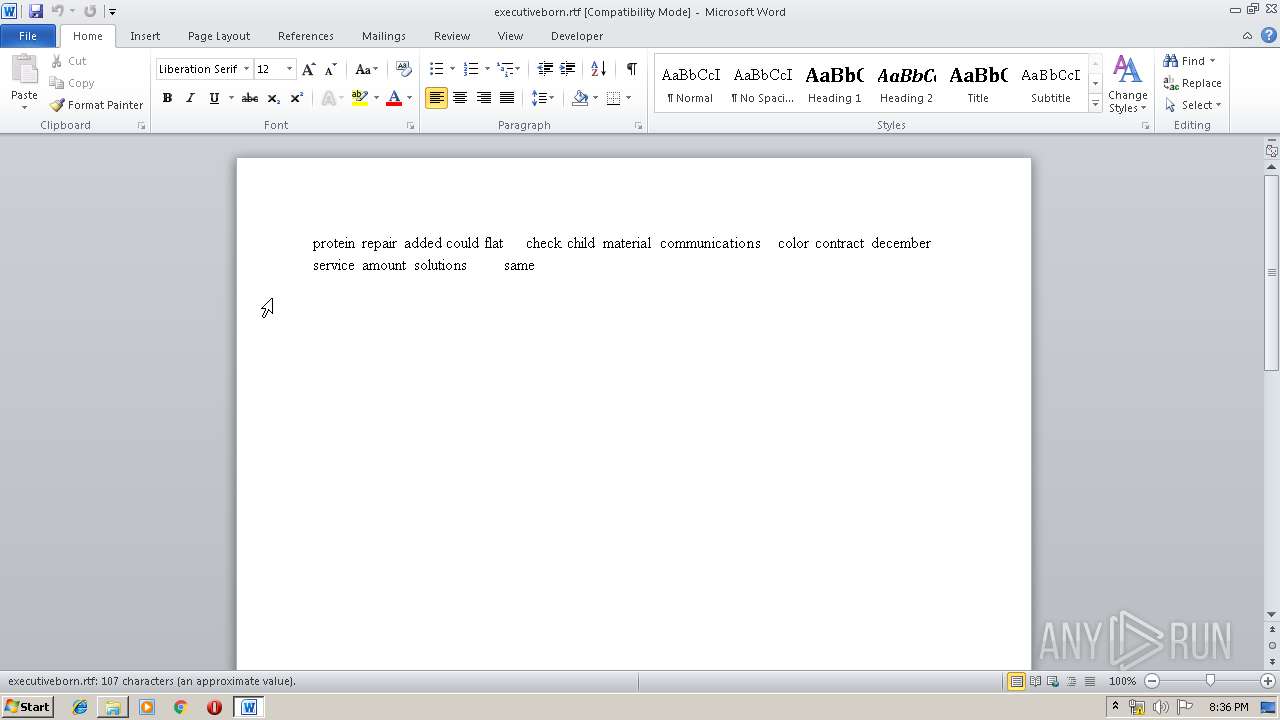
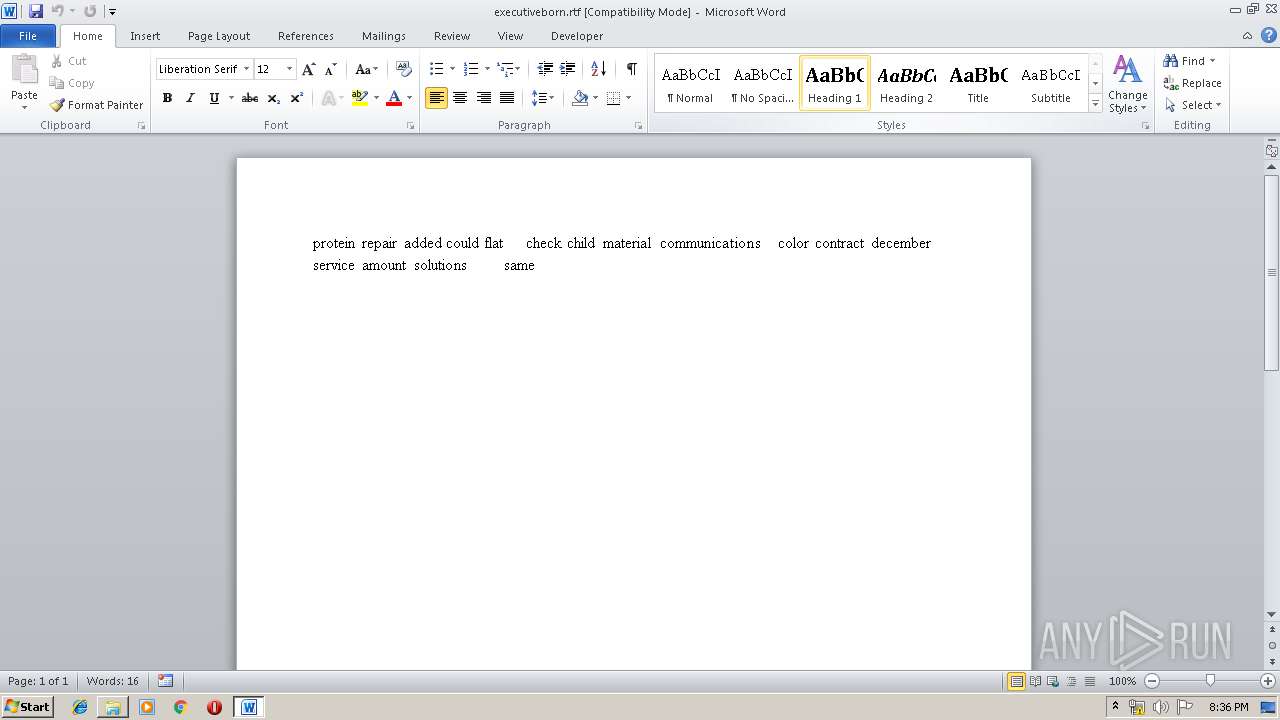
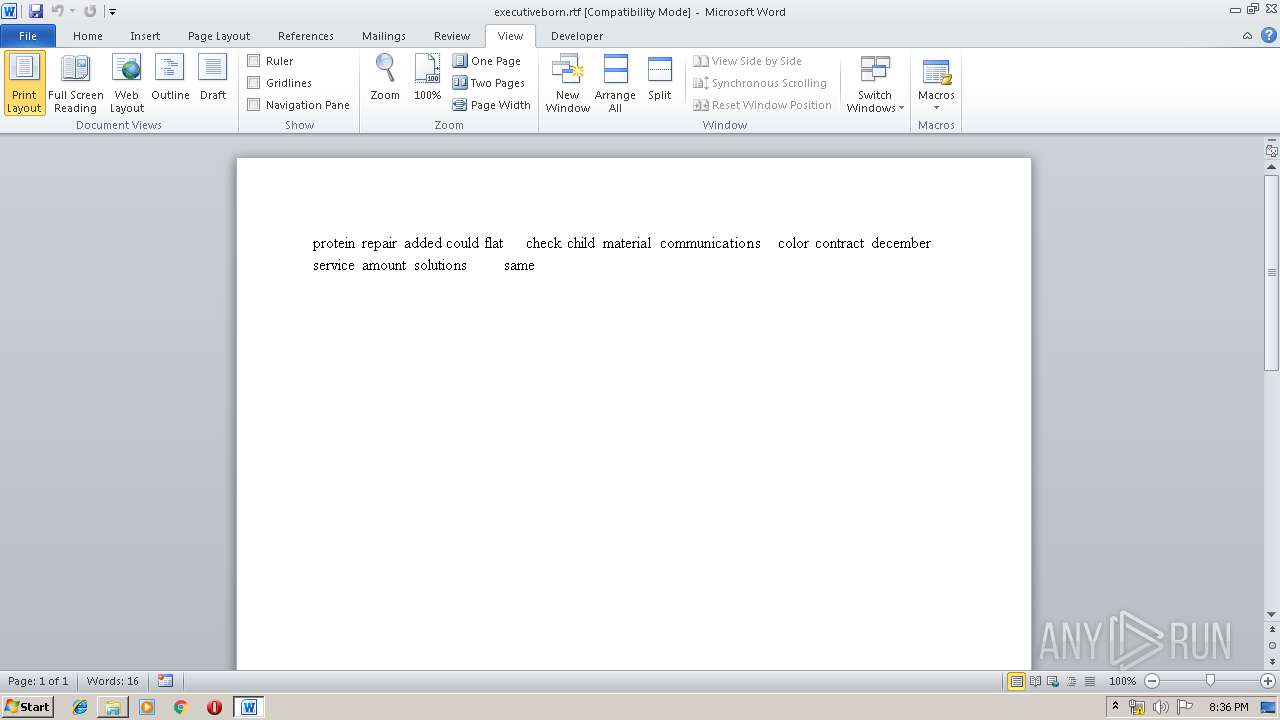
| 2676 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Documents\executiveborn.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
10 104
Read events
9 109
Write events
693
Delete events
302
Modification events
| (PID) Process: | (1812) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1812) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1812) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1812) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1812) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1812) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1812) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1812) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1812) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1812) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
4
Suspicious files
0
Text files
25
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1812 | WScript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\iskhgo7poeevzj2[1].exe | — | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5924.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{D855A6DE-4211-4FF1-8FAB-1638C78264FA}.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{F5E603C8-1F7D-4973-B0AD-A8BD9DC694DB}.tmp | — | |
MD5:— | SHA256:— | |||
| 772 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8739.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 772 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{5DA1B531-068E-49BB-9F86-7AAEBF30E29A}.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAFA1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{711070AA-E2C8-4A3B-B399-CD3F80FC4284}.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{C65DD13F-7FE9-4F93-9BCC-F3D895CBFA7D}.tmp | — | |
MD5:— | SHA256:— | |||
| 2772 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD24C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
16
DNS requests
3
Threats
49
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1812 | WScript.exe | GET | 302 | 103.117.212.217:80 | http://thepngbusiness.com/wp-content/5ecnu9155/ | unknown | — | — | suspicious |
1812 | WScript.exe | GET | 200 | 45.119.213.95:80 | http://mitsubishi-3s.com/wp-content/languages/ly28/ | VN | executable | 76.6 Kb | suspicious |
4024 | soundser.exe | POST | — | 181.16.127.226:443 | http://181.16.127.226:443/odbc/ | AR | — | — | malicious |
4024 | soundser.exe | POST | — | 201.217.67.3:80 | http://201.217.67.3/stubs/jit/ringin/merge/ | EC | — | — | malicious |
4024 | soundser.exe | POST | — | 181.39.134.122:80 | http://181.39.134.122/odbc/ban/ | EC | — | — | malicious |
4024 | soundser.exe | POST | — | 186.150.97.69:8080 | http://186.150.97.69:8080/sess/devices/ringin/merge/ | DO | — | — | malicious |
4024 | soundser.exe | POST | — | 38.143.223.215:8080 | http://38.143.223.215:8080/prep/ | US | — | — | malicious |
4036 | soundser.exe | POST | 200 | 159.65.241.220:8080 | http://159.65.241.220:8080/nsip/srvc/ringin/ | US | binary | 148 b | malicious |
4036 | soundser.exe | GET | 200 | 216.98.148.157:8080 | http://216.98.148.157:8080/whoami.php | US | text | 13 b | malicious |
4036 | soundser.exe | POST | 200 | 198.50.170.27:8080 | http://198.50.170.27:8080/schema/health/ringin/merge/ | CA | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.224.138.173:443 | seethalekshmiconstructions.com | — | — | malicious |
1812 | WScript.exe | 103.117.212.217:80 | thepngbusiness.com | — | — | suspicious |
4024 | soundser.exe | 181.110.239.26:80 | — | Telecom Argentina S.A. | AR | malicious |
4024 | soundser.exe | 38.143.223.215:8080 | — | Cogent Communications | US | malicious |
4024 | soundser.exe | 186.150.97.69:8080 | — | TRICOM | DO | malicious |
4024 | soundser.exe | 181.39.134.122:80 | — | Telconet S.A | EC | malicious |
— | — | 181.16.127.226:443 | — | Ver Tv S.A. | AR | malicious |
4024 | soundser.exe | 201.217.67.3:80 | — | Satnet | EC | malicious |
4036 | soundser.exe | 66.228.32.31:7080 | — | Linode, LLC | US | malicious |
4036 | soundser.exe | 216.98.148.157:8080 | — | CariNet, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
seethalekshmiconstructions.com |
| malicious |
thepngbusiness.com |
| suspicious |
mitsubishi-3s.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1812 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
1812 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
1812 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1812 | WScript.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
1812 | WScript.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
4024 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 6 |
4024 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 14 |
4024 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4024 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4024 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
26 ETPRO signatures available at the full report