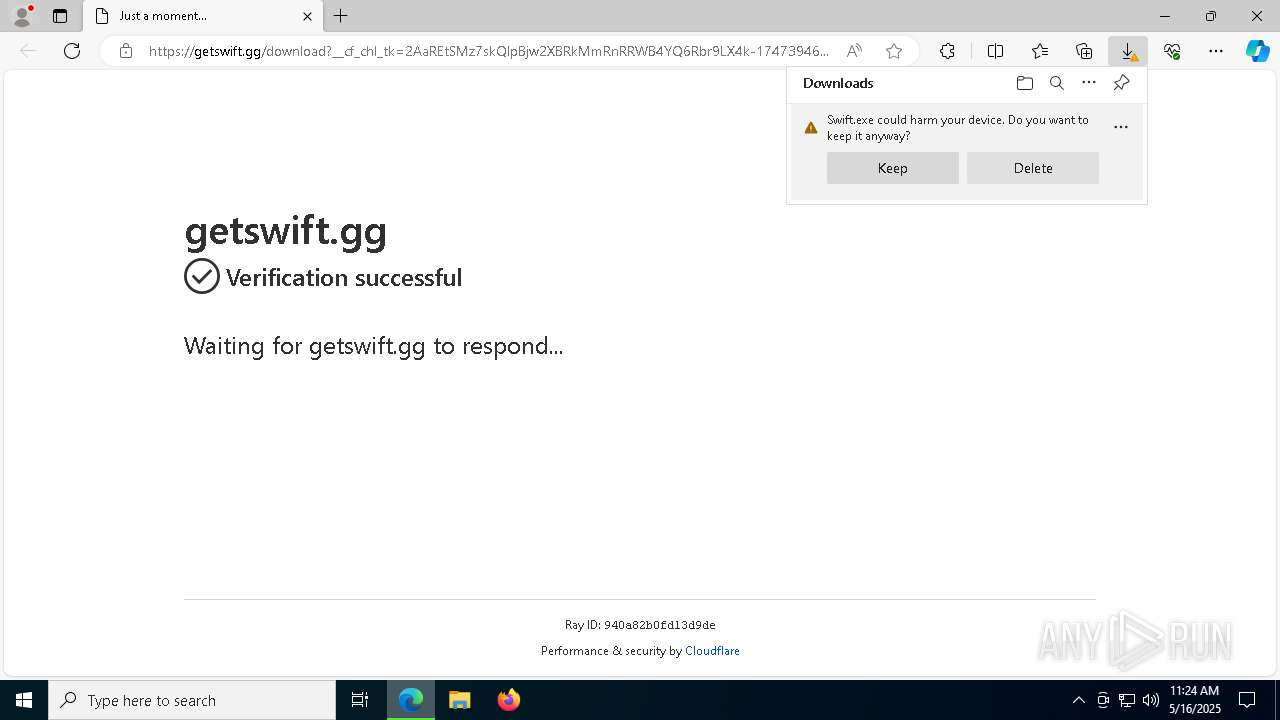
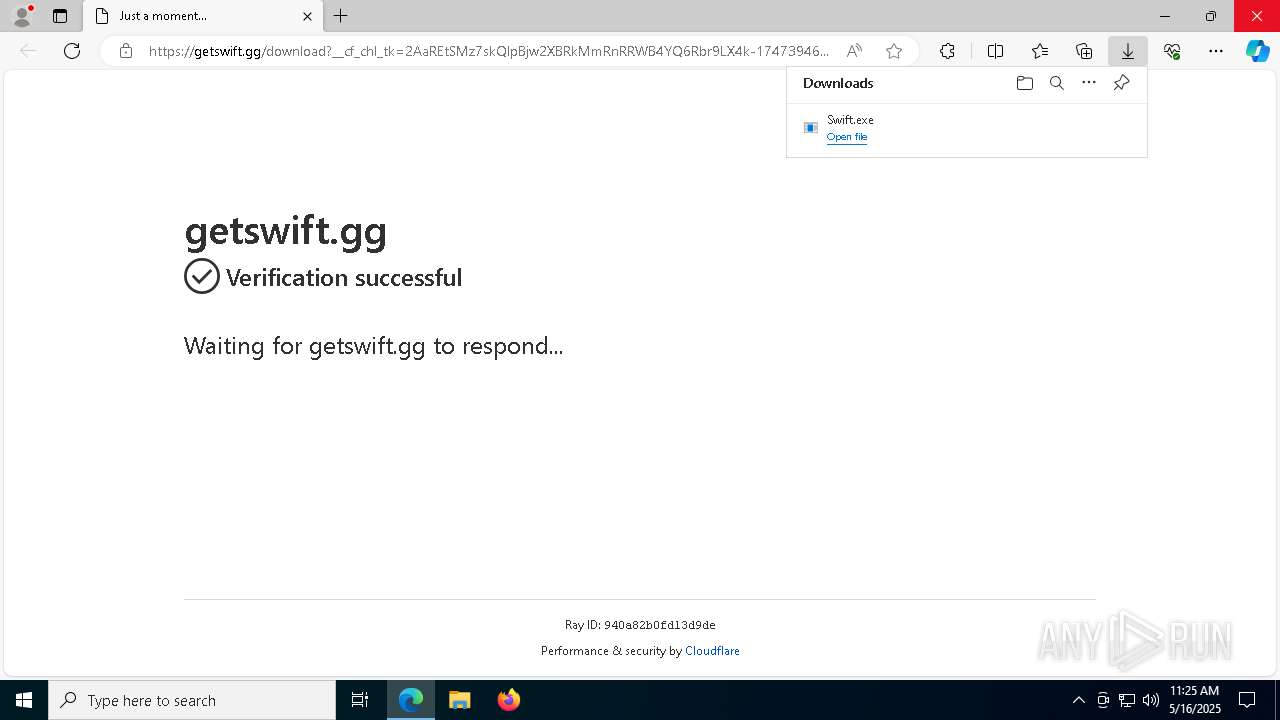
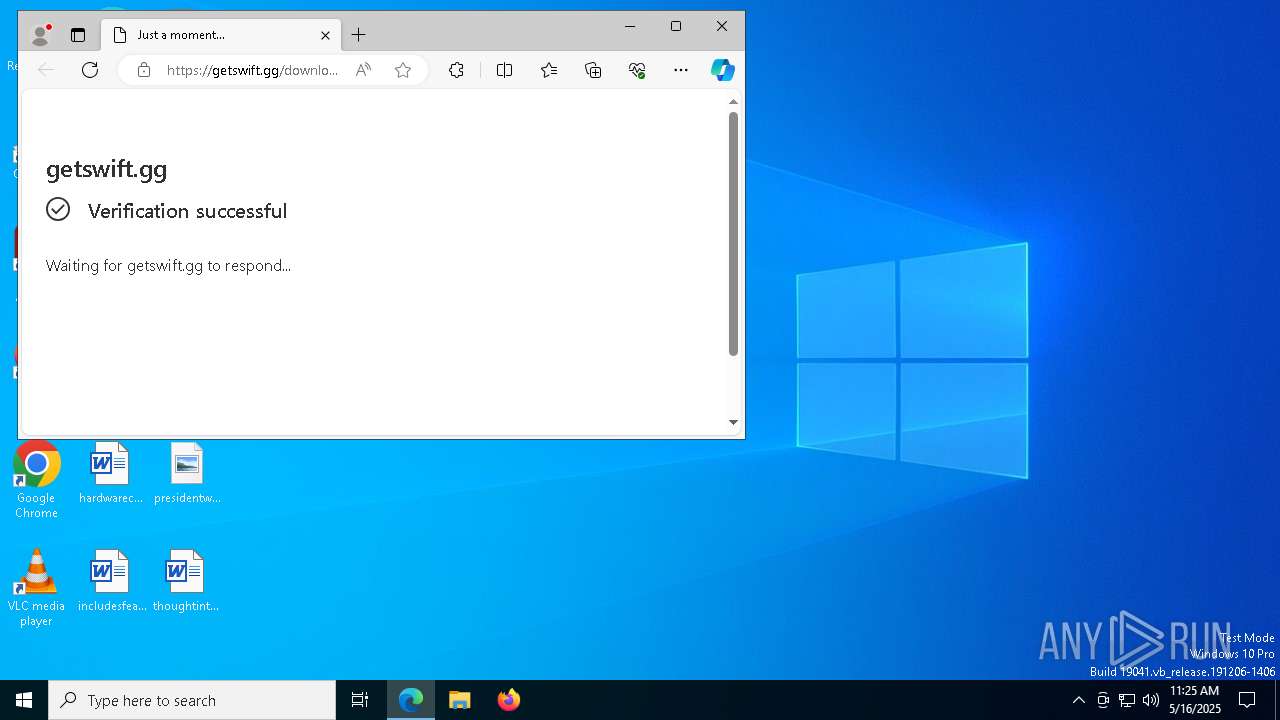
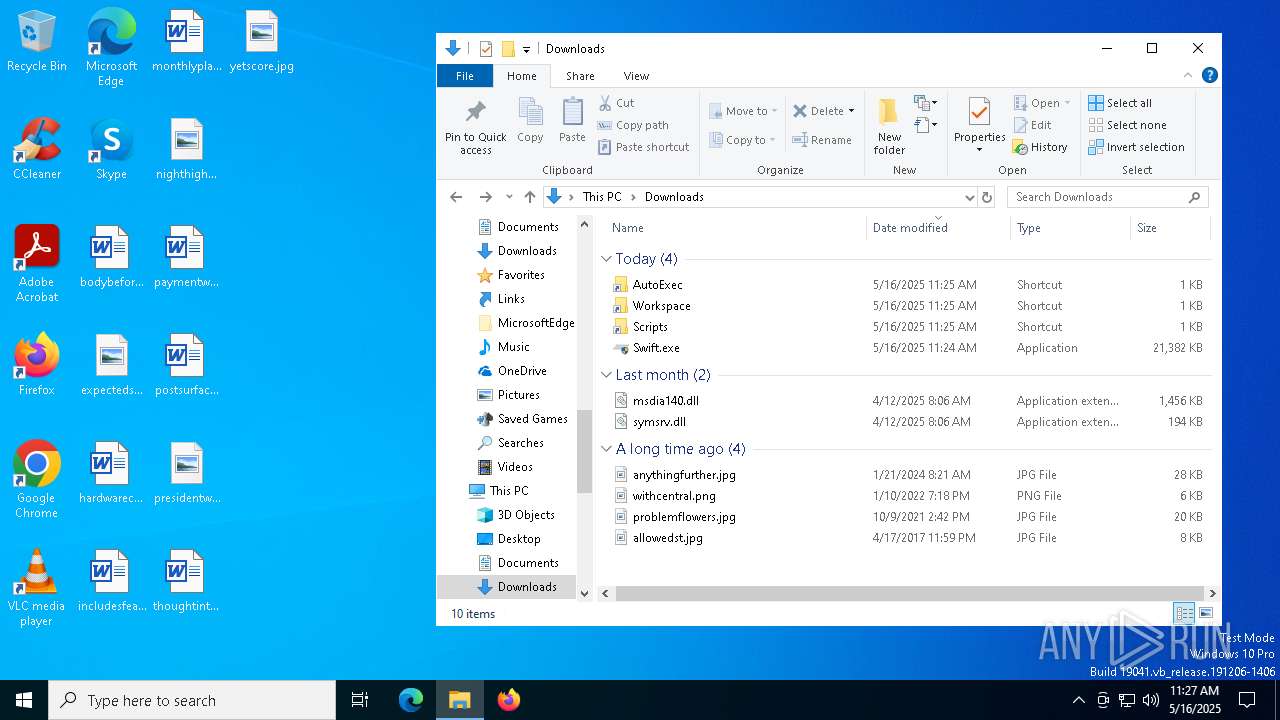
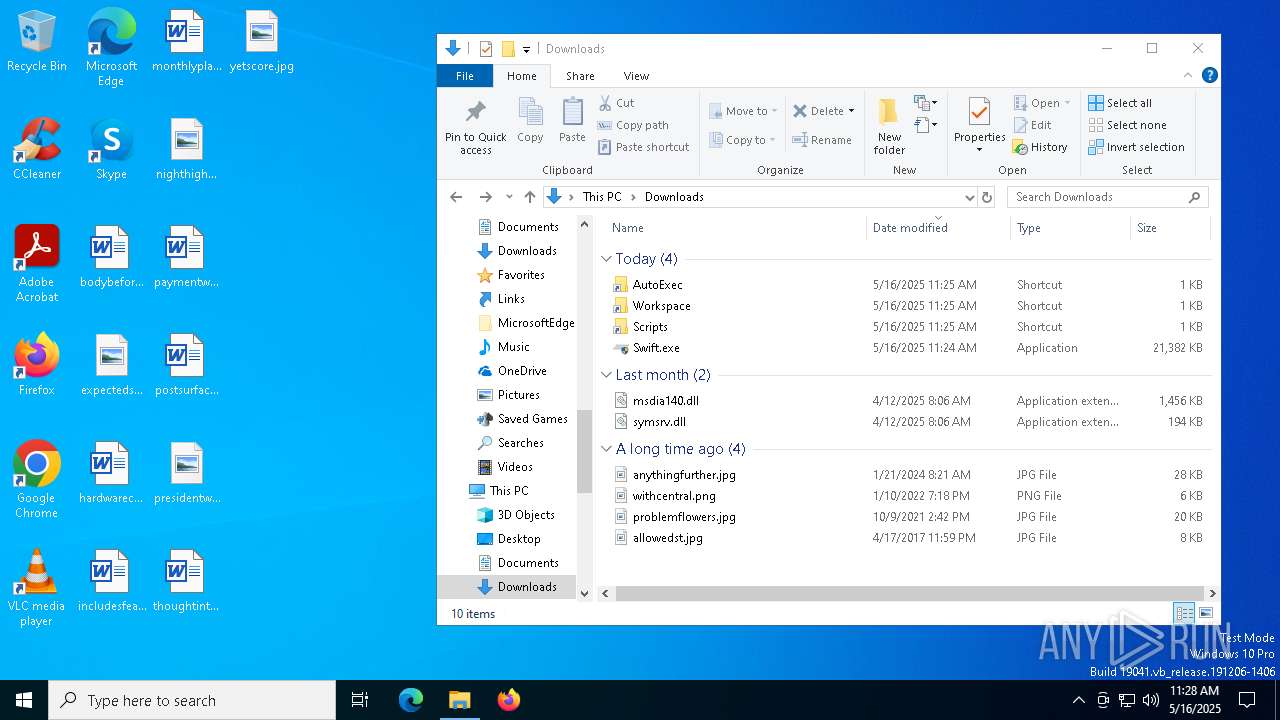
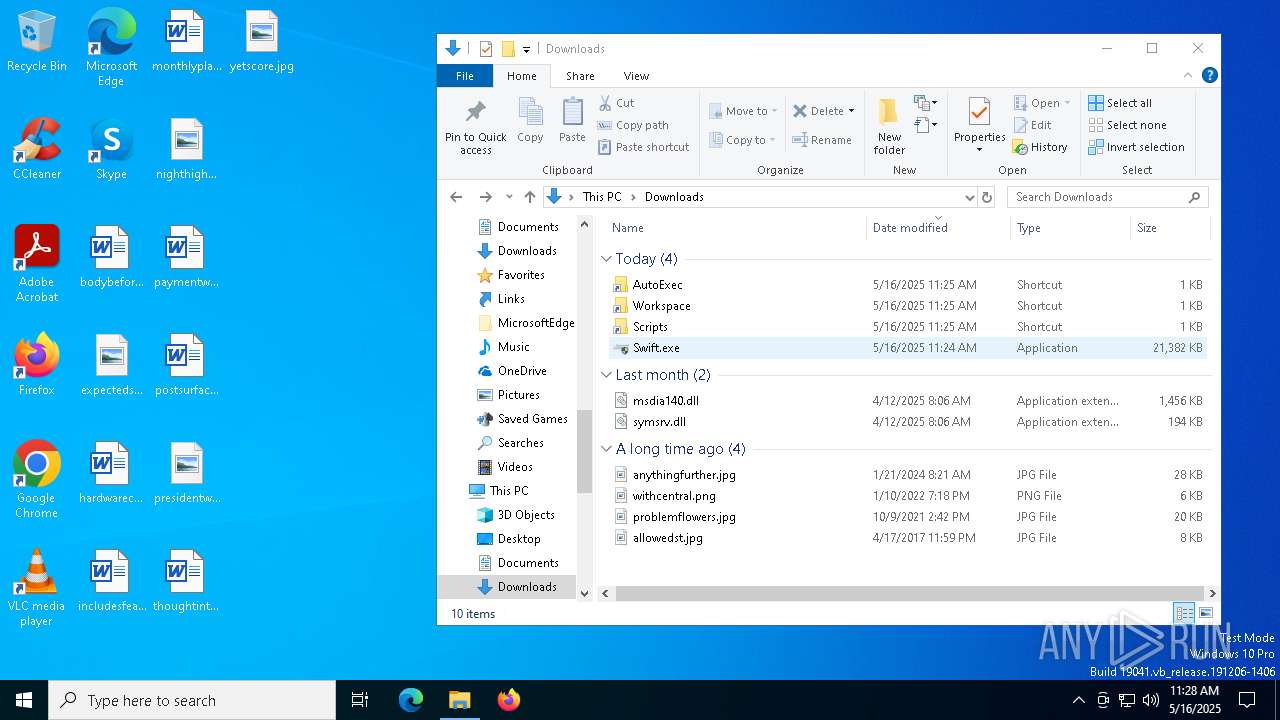
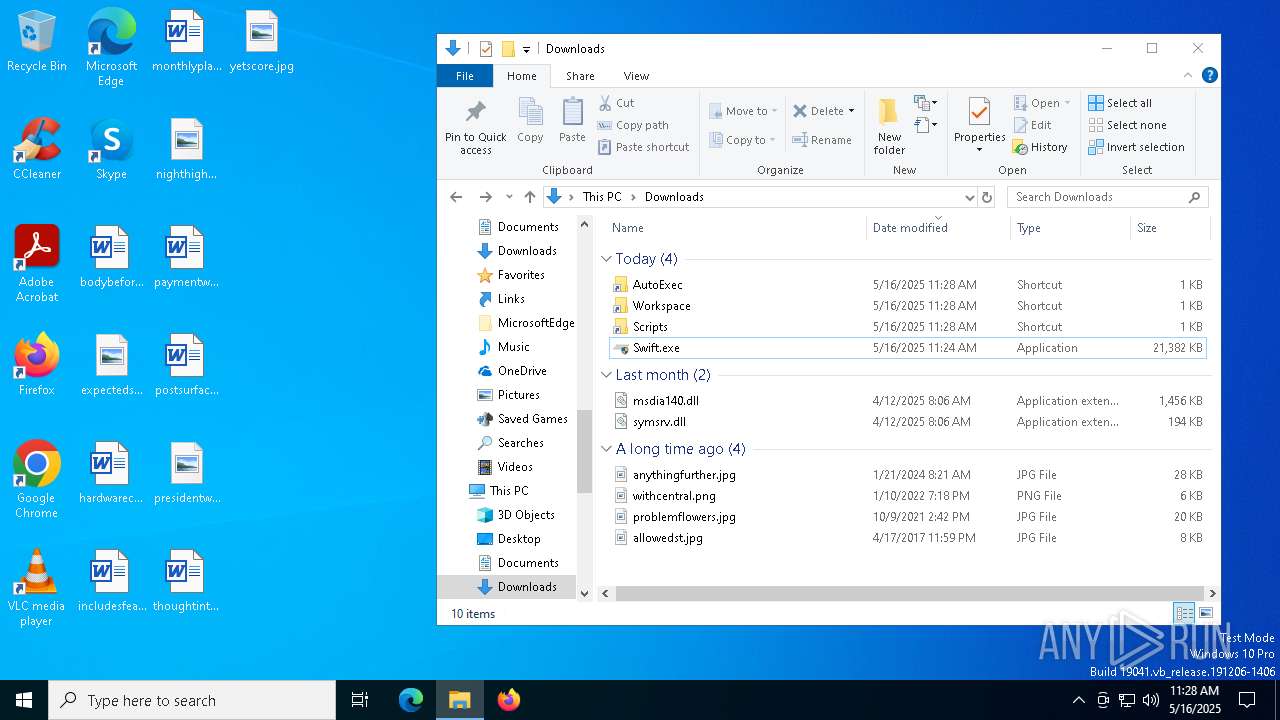
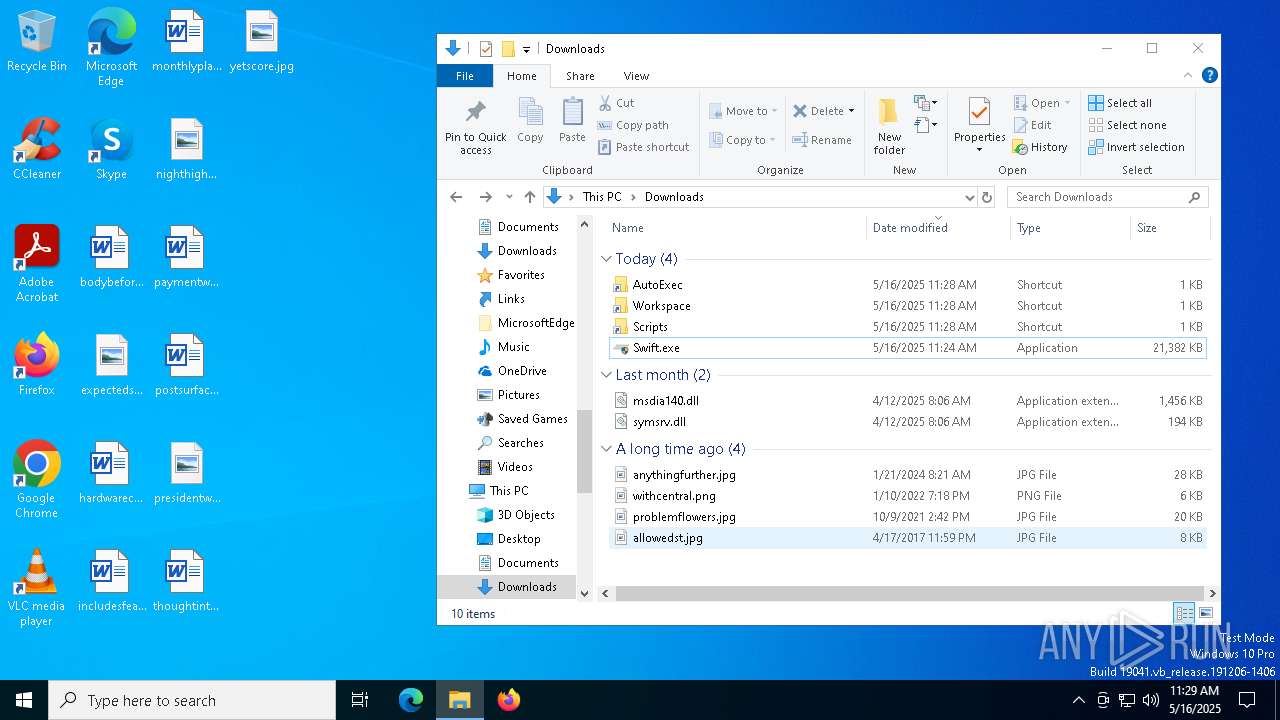
| URL: | https://getswift.gg/download |
| Full analysis: | https://app.any.run/tasks/f5342b87-a45f-4b71-8238-e3264a86430a |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 11:24:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 15C8A70ACE4620150747BA330BB16DBB |
| SHA1: | FDF85984AF719270715D887A8C852A6523E6EB24 |
| SHA256: | 0085362EF4EC55B3F58835FBB71984465A2EFD368ACC3201F72F5A1D81555DD6 |
| SSDEEP: | 3:N8hnMDtCySLz:2GDy |
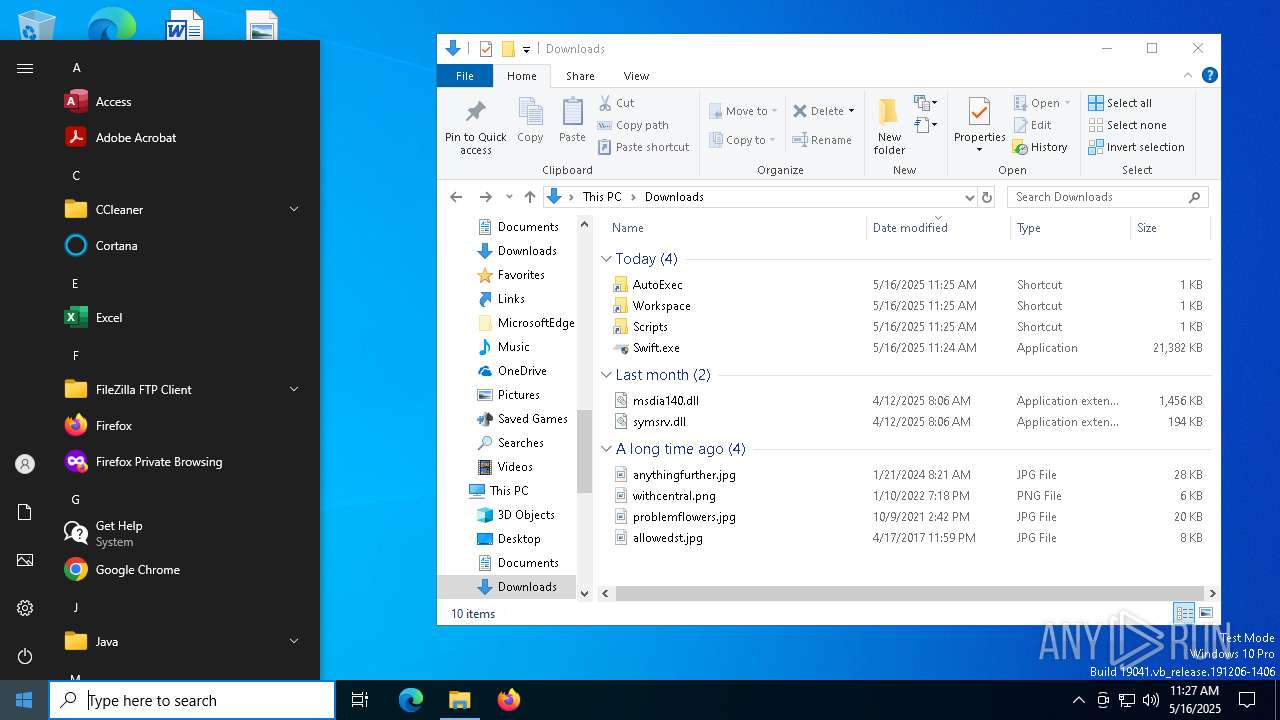
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 4000)
- powershell.exe (PID: 2392)
- powershell.exe (PID: 4932)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 4464)
- powershell.exe (PID: 2320)
- powershell.exe (PID: 7884)
- powershell.exe (PID: 2284)
- powershell.exe (PID: 7816)
- powershell.exe (PID: 660)
- powershell.exe (PID: 5608)
- powershell.exe (PID: 5812)
SUSPICIOUS
Reads the BIOS version
- Swift.exe (PID: 4608)
- Swift.exe (PID: 3900)
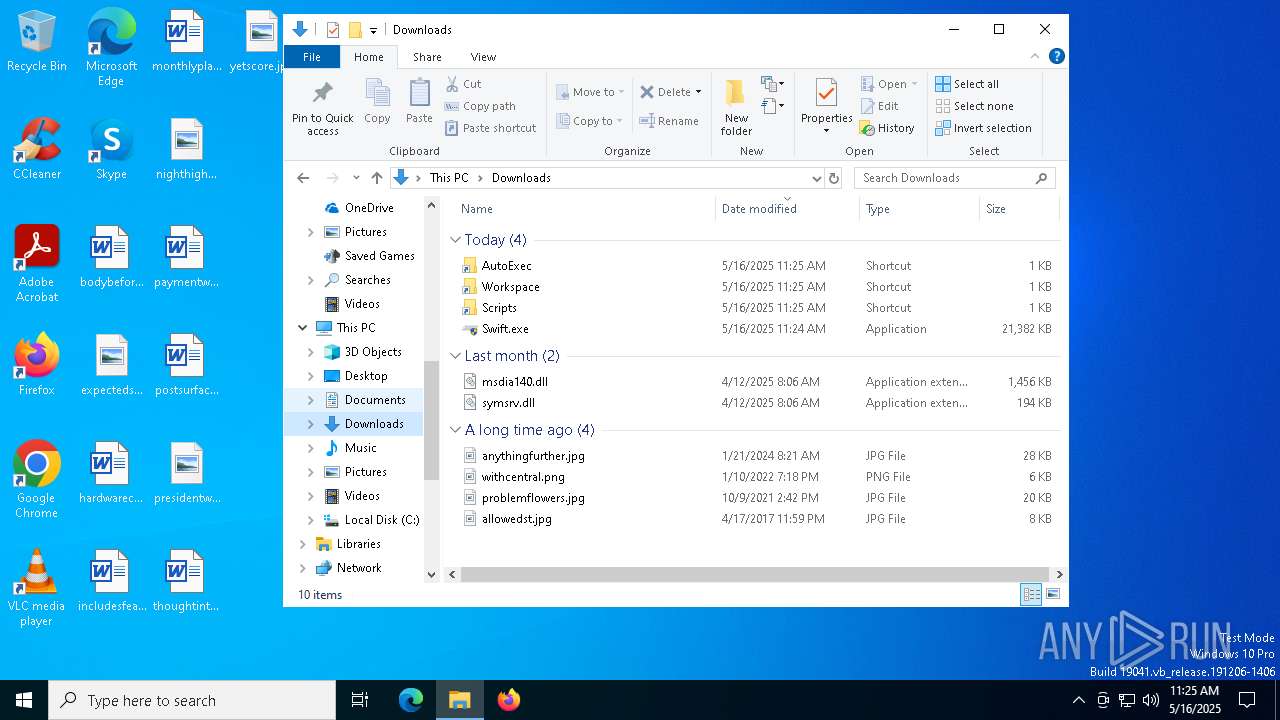
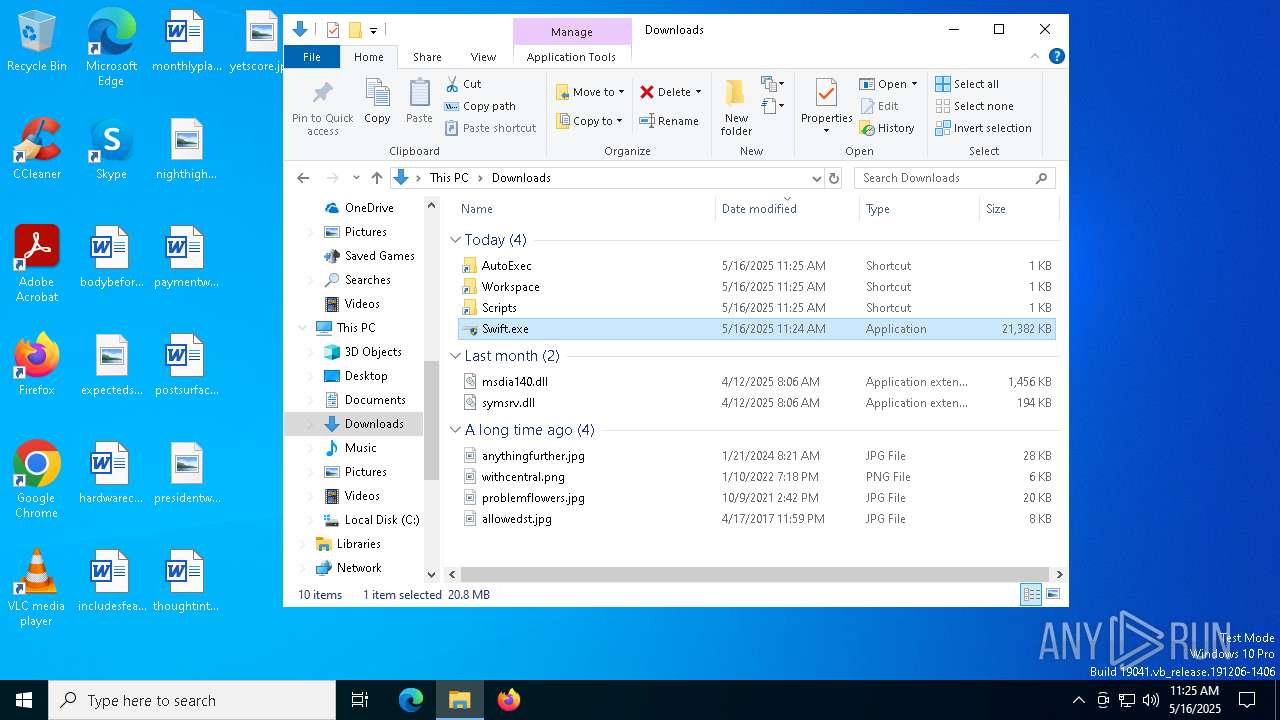
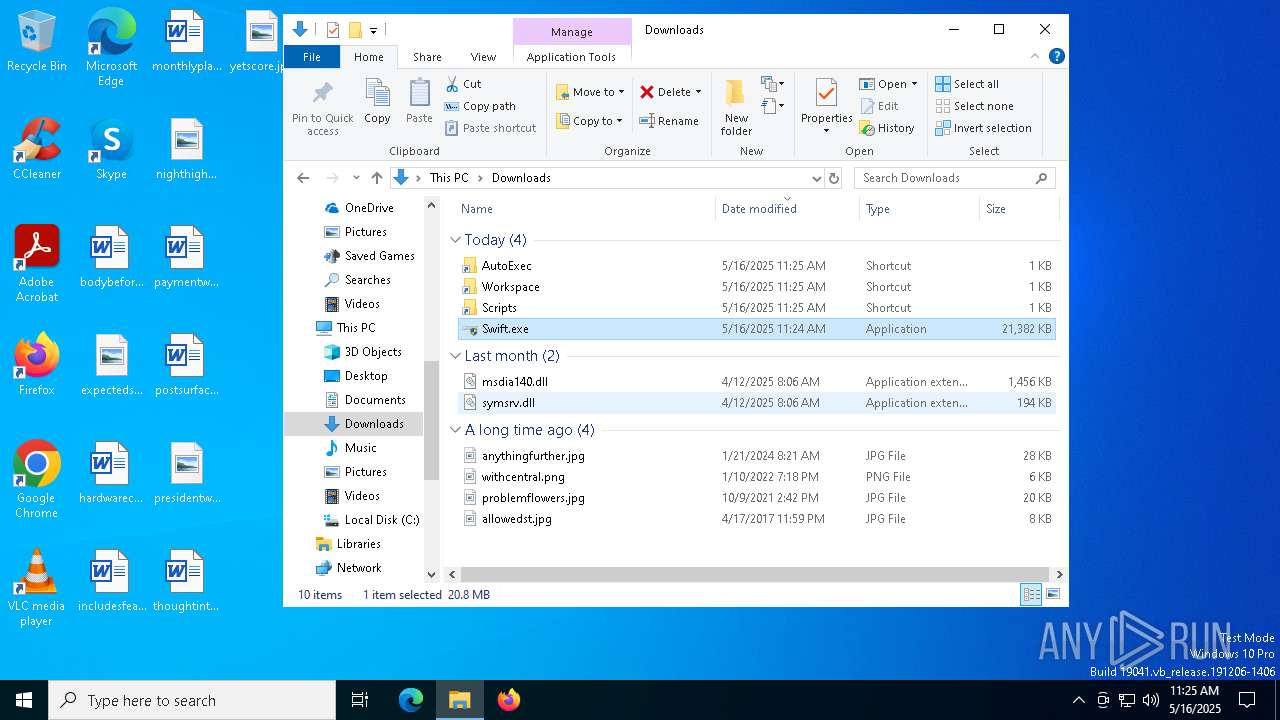
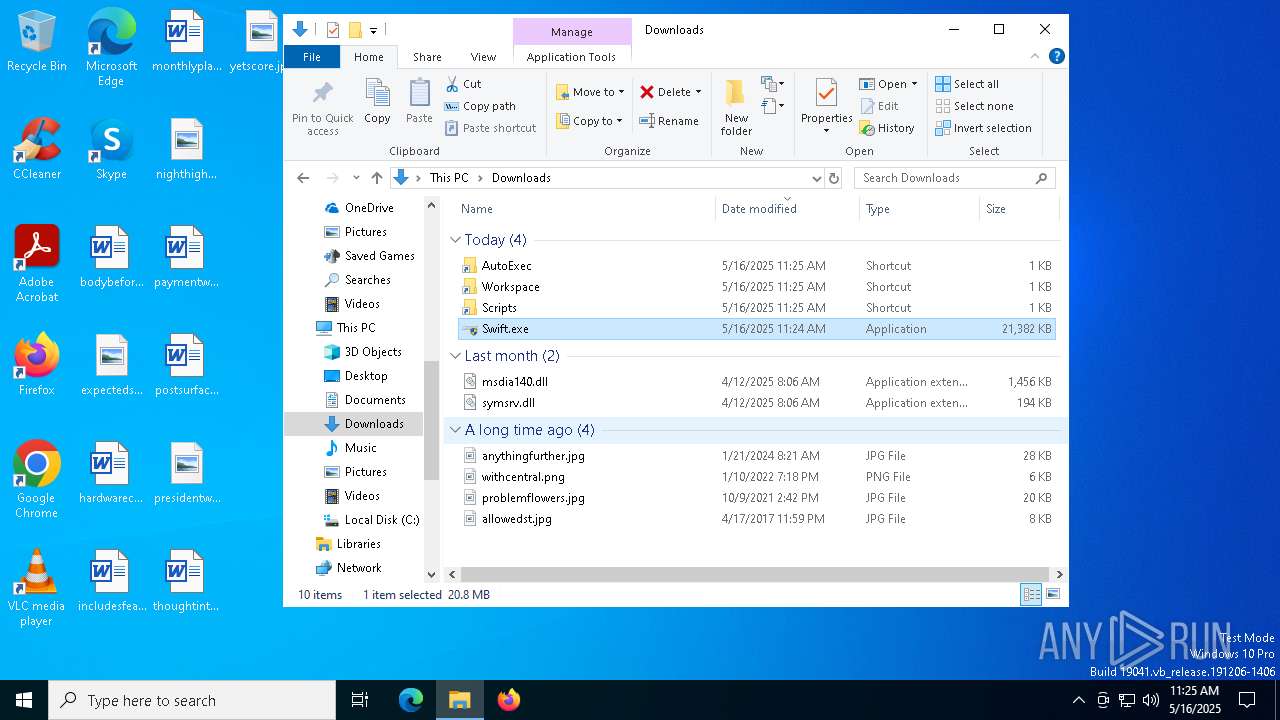
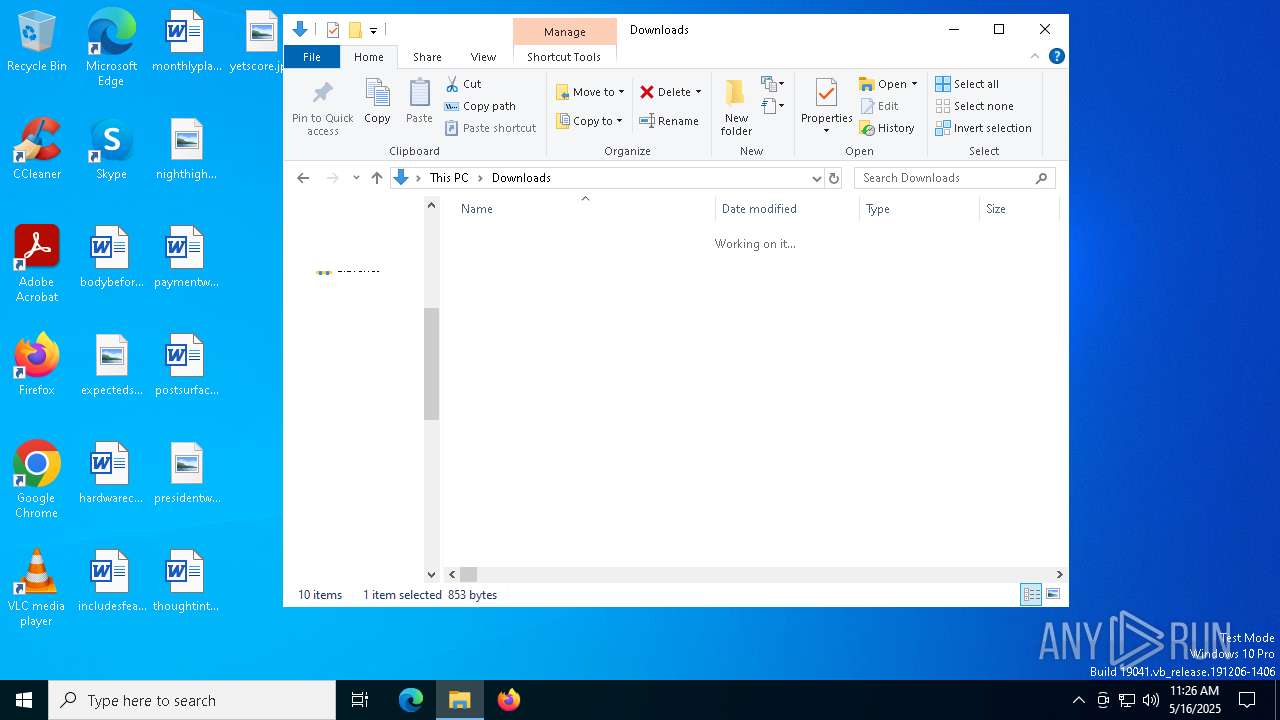
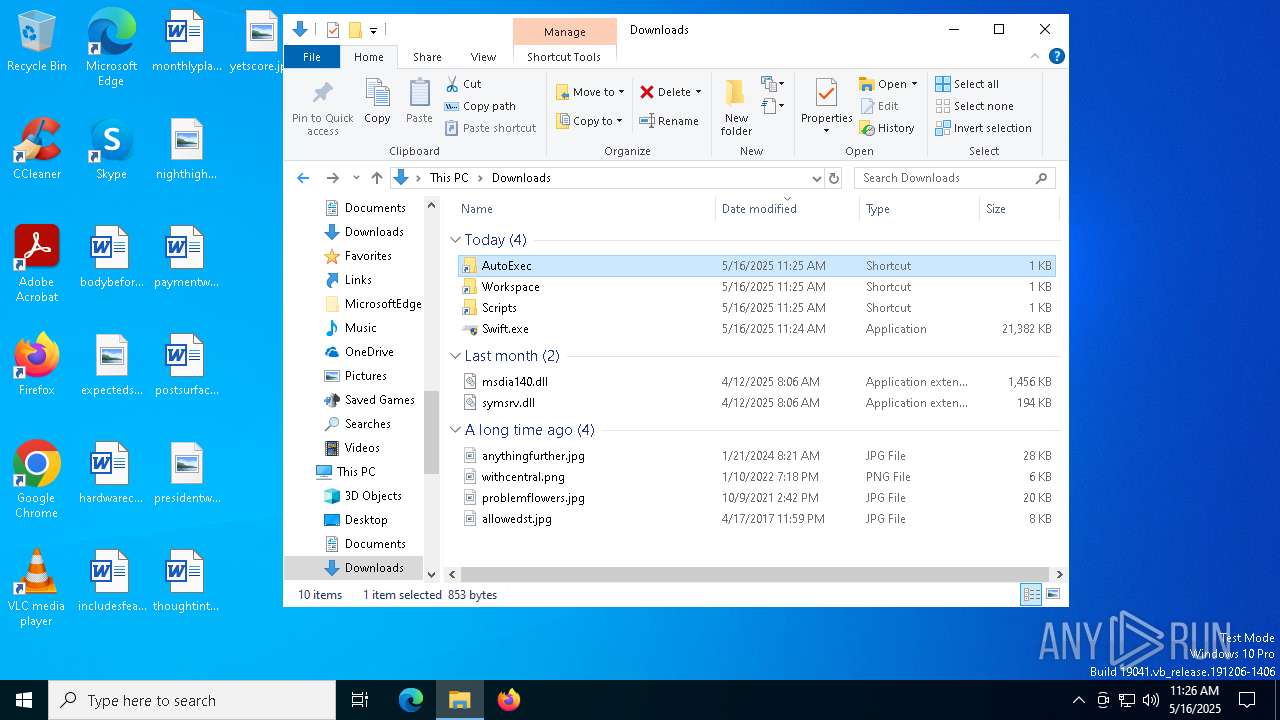
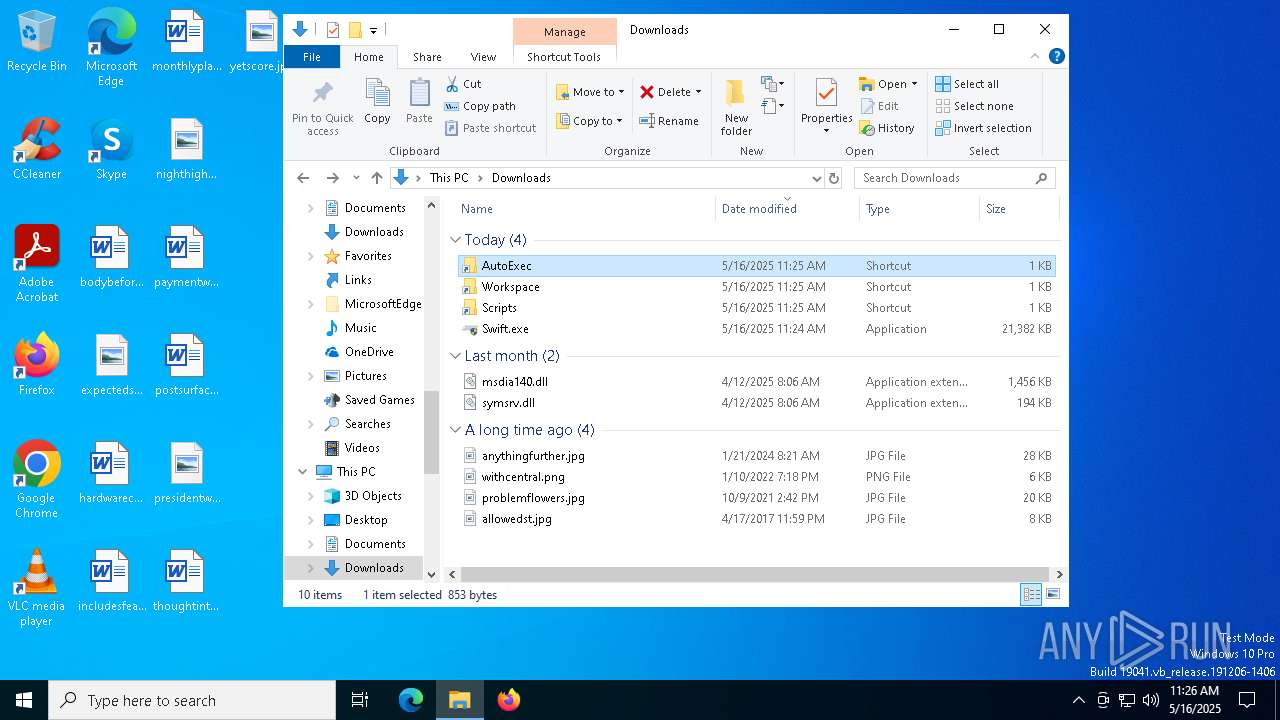
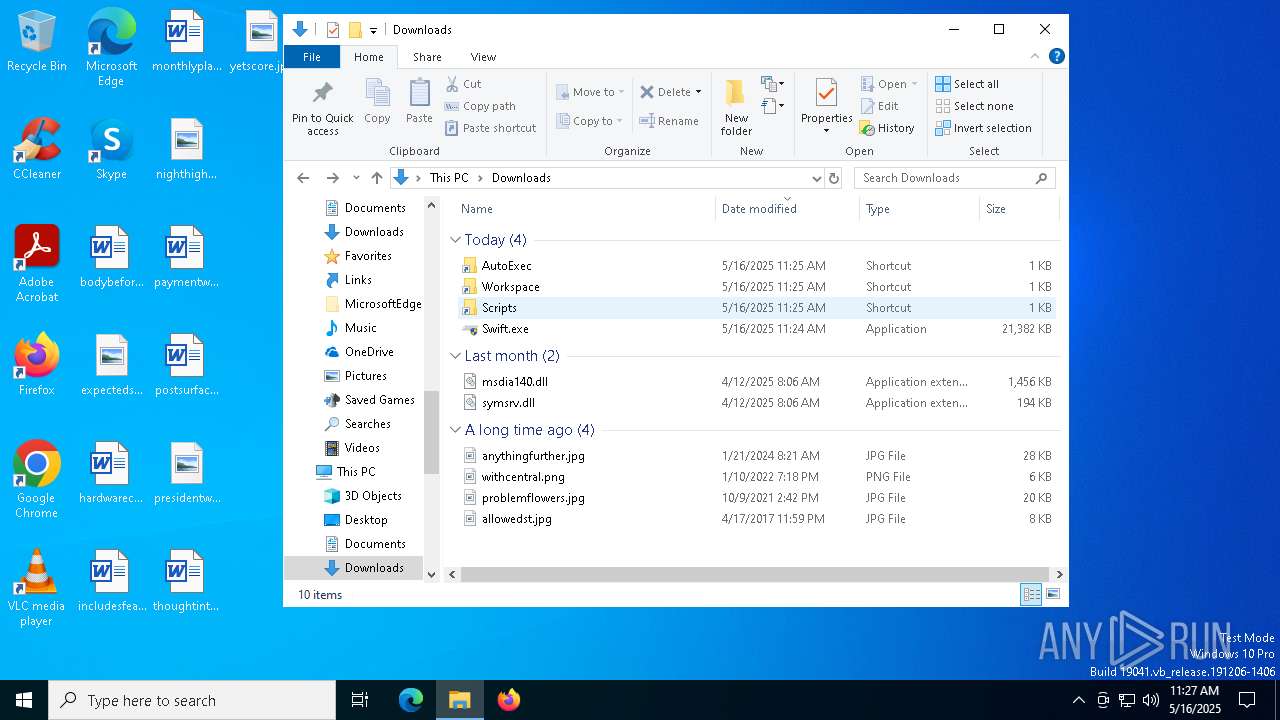
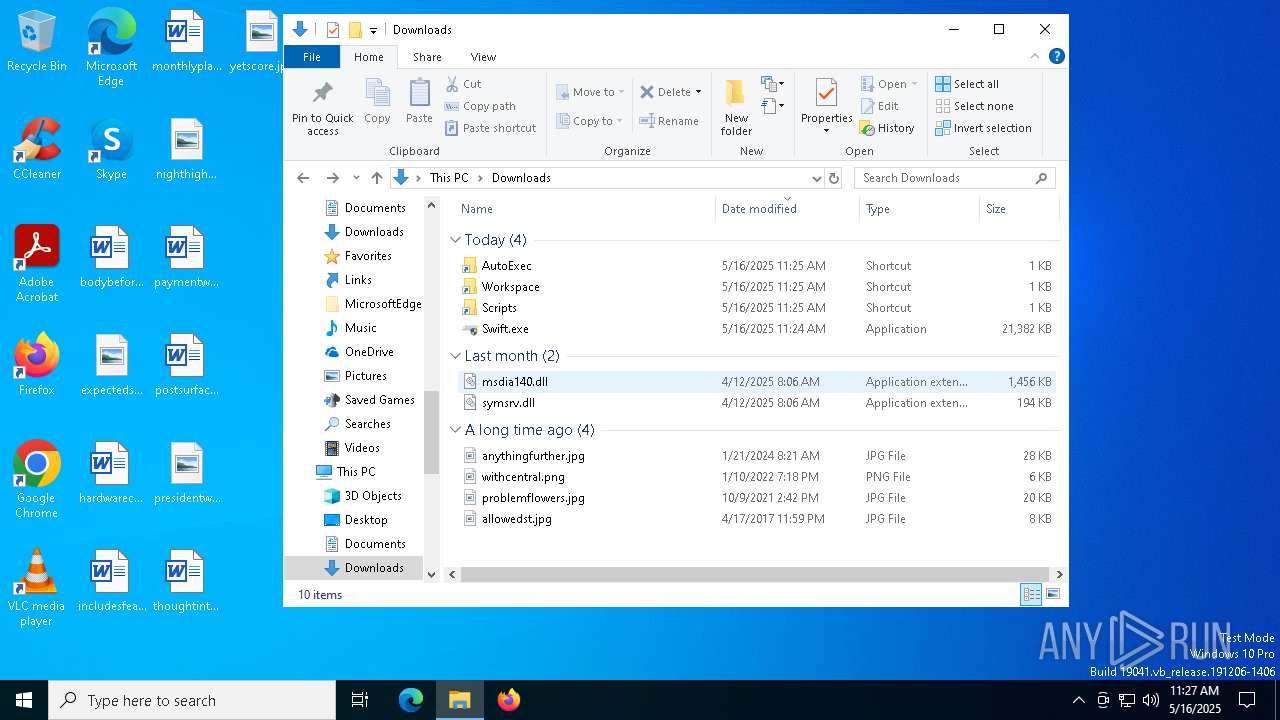
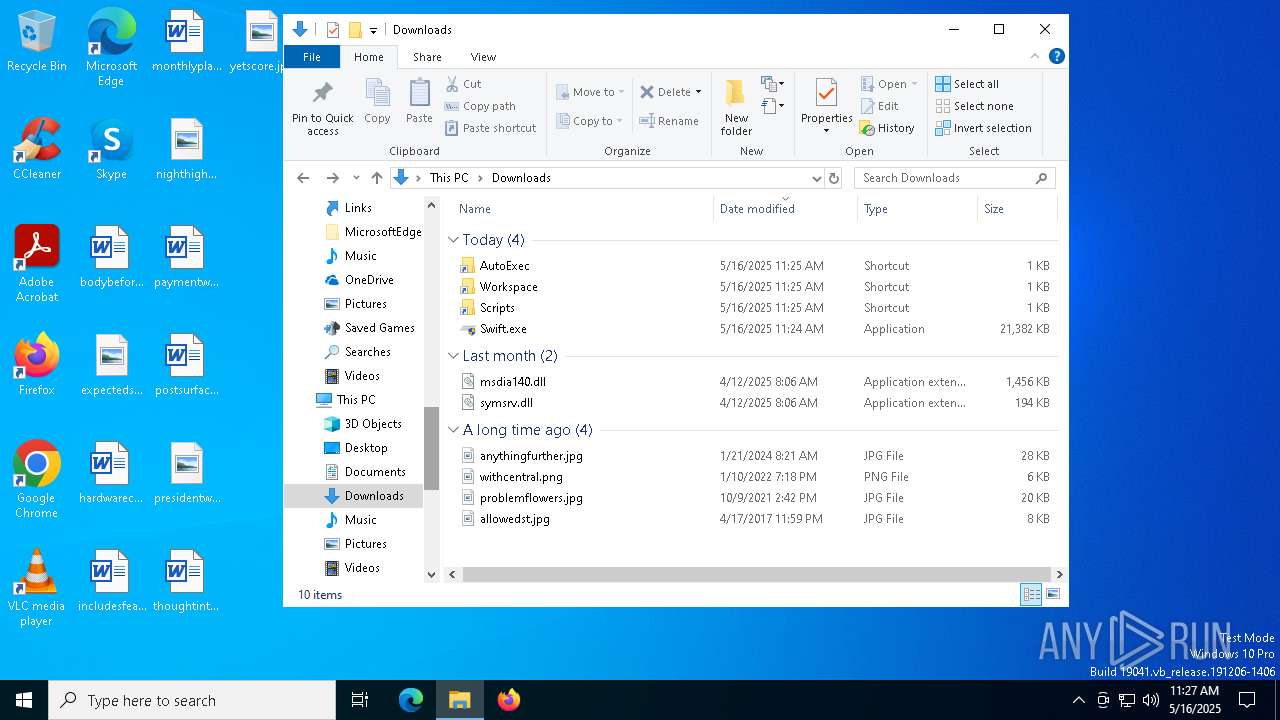
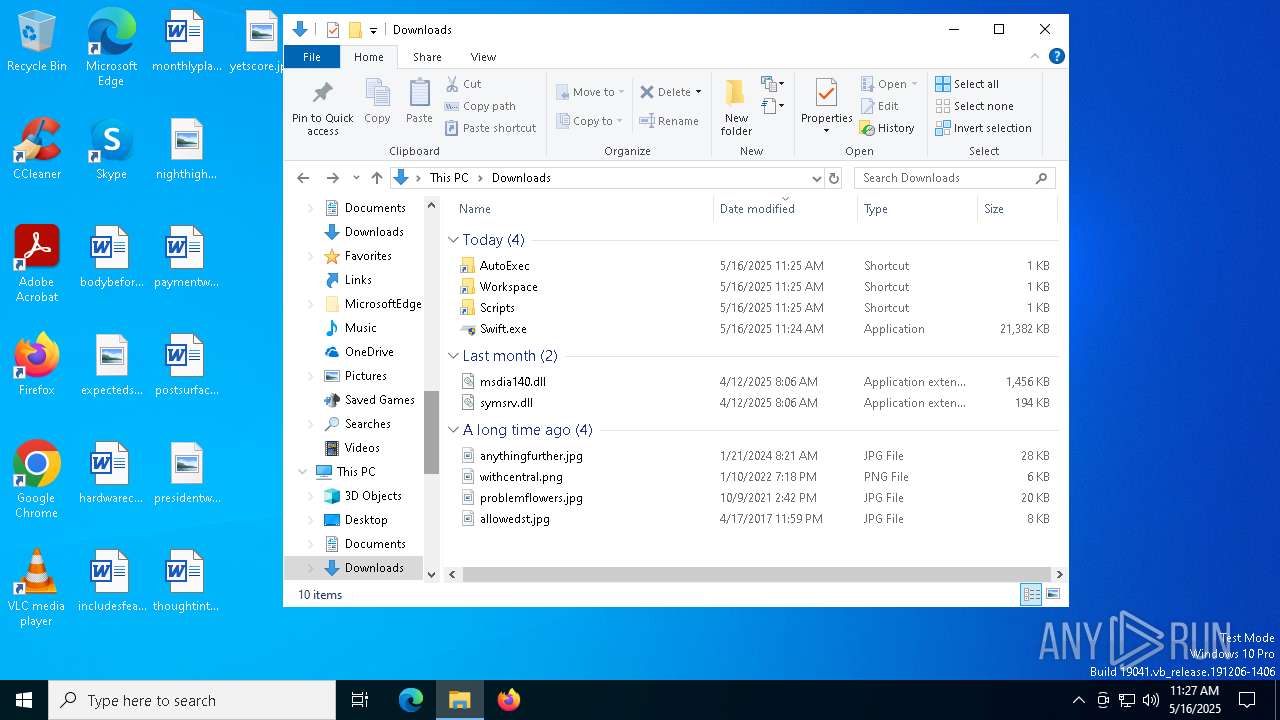
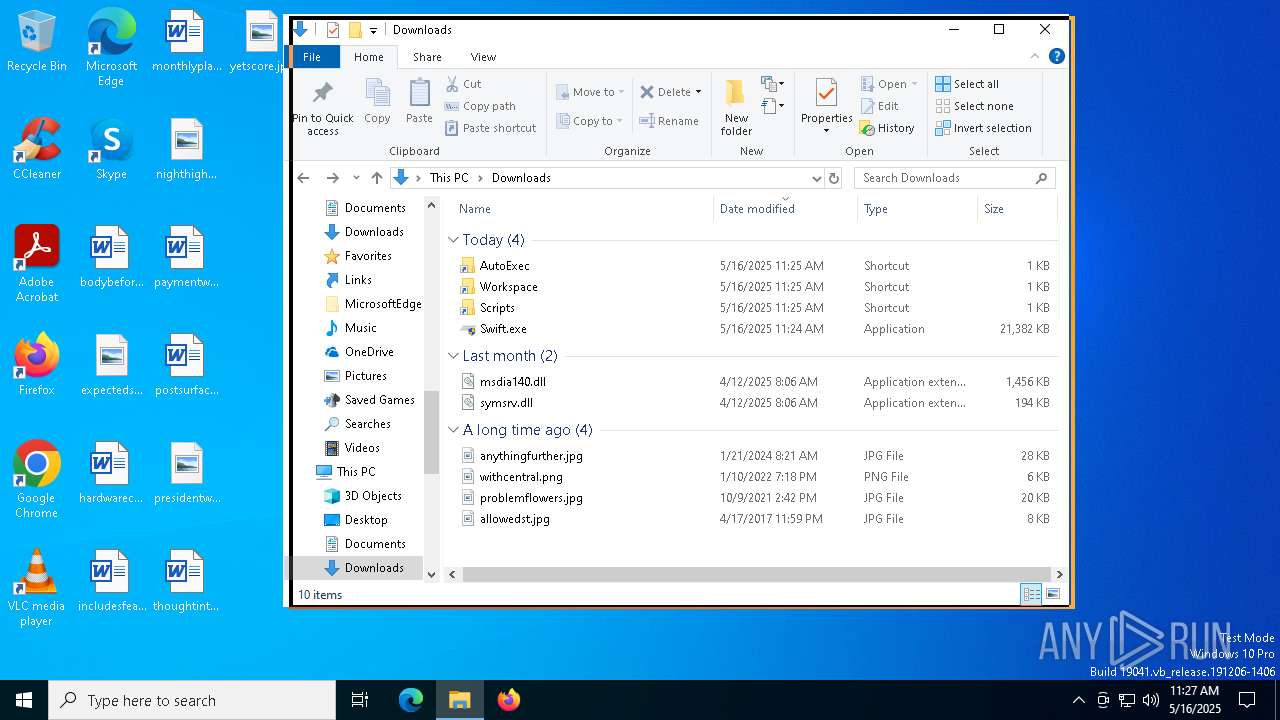
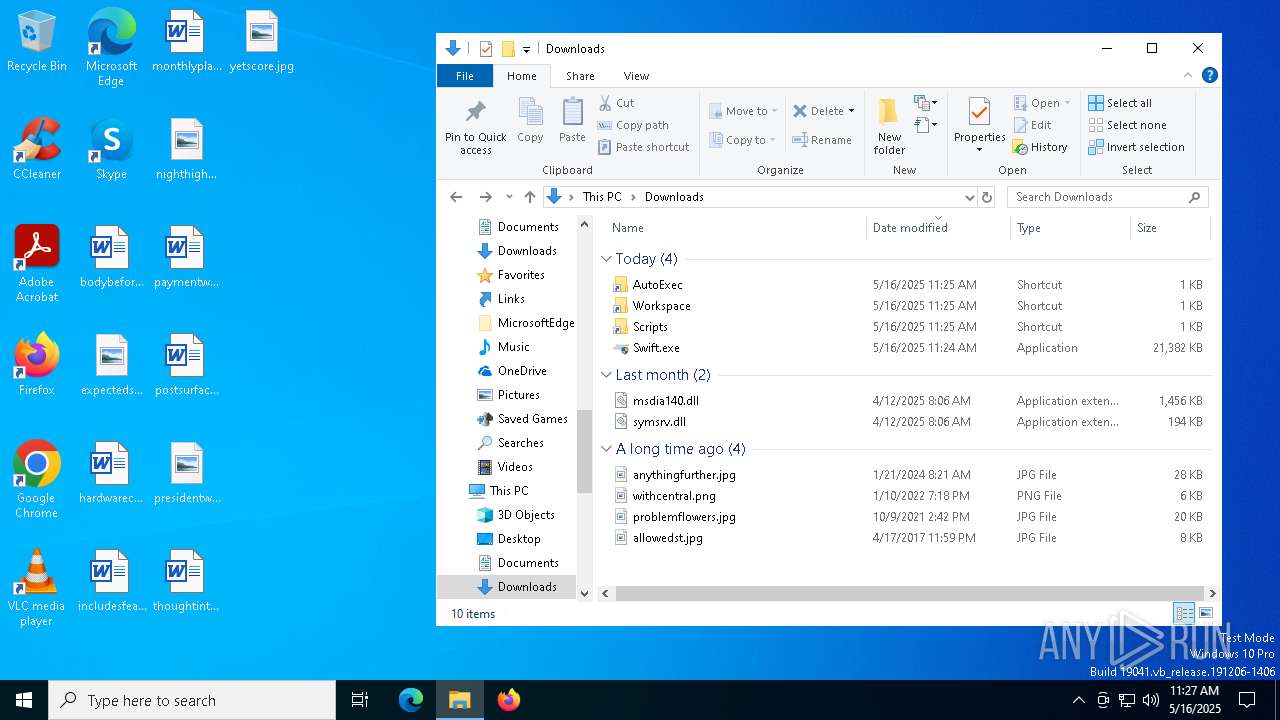
Executable content was dropped or overwritten
- Swift.exe (PID: 4608)
Process drops legitimate windows executable
- Swift.exe (PID: 4608)
Starts POWERSHELL.EXE for commands execution
- Swift.exe (PID: 3900)
- Swift.exe (PID: 4608)
- Swift.exe (PID: 2776)
- Swift.exe (PID: 6392)
The process hide an interactive prompt from the user
- Swift.exe (PID: 3900)
- Swift.exe (PID: 4608)
- Swift.exe (PID: 6392)
- Swift.exe (PID: 2776)
The process bypasses the loading of PowerShell profile settings
- Swift.exe (PID: 4608)
- Swift.exe (PID: 3900)
- Swift.exe (PID: 2776)
- Swift.exe (PID: 6392)
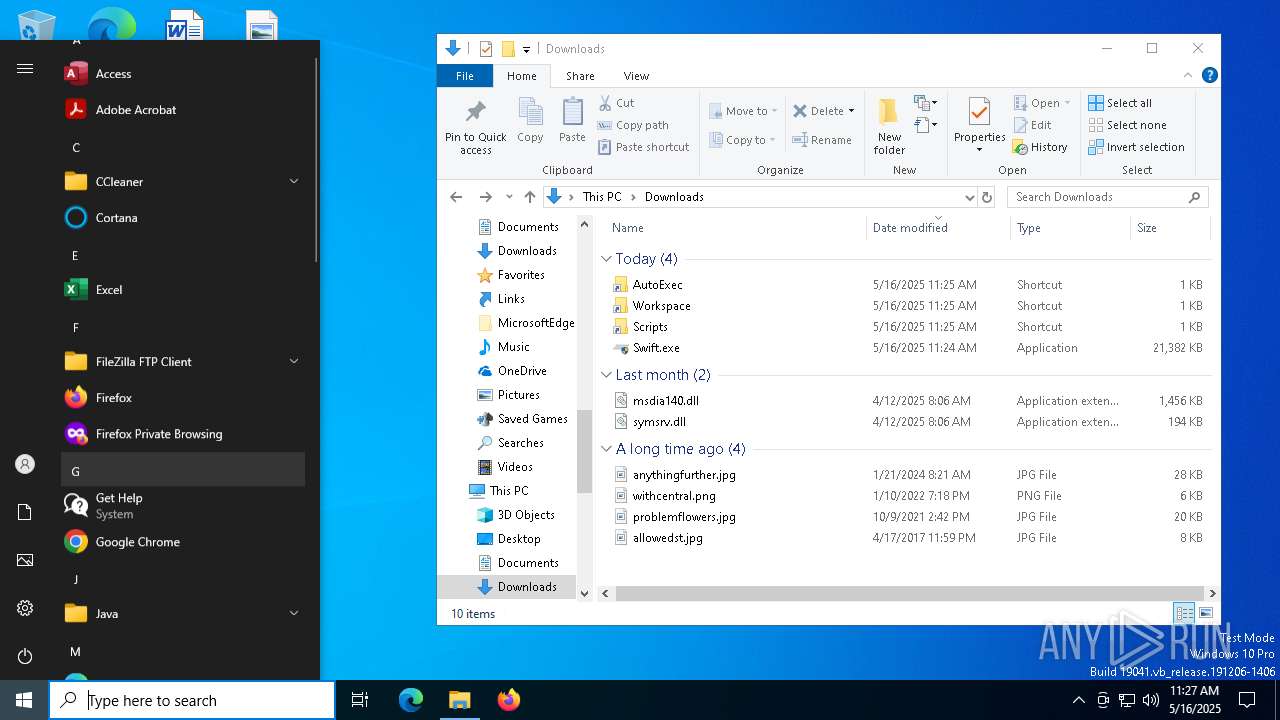
INFO
Application launched itself
- msedge.exe (PID: 7468)
- msedge.exe (PID: 6344)
Process checks whether UAC notifications are on
- Swift.exe (PID: 4608)
- Swift.exe (PID: 3900)
Checks supported languages
- identity_helper.exe (PID: 2096)
- Swift.exe (PID: 4608)
- Swift.exe (PID: 3900)
Executable content was dropped or overwritten
- msedge.exe (PID: 7468)
- msedge.exe (PID: 6436)
Reads the computer name
- identity_helper.exe (PID: 2096)
- Swift.exe (PID: 4608)
- Swift.exe (PID: 3900)
Reads Environment values
- identity_helper.exe (PID: 2096)
The sample compiled with english language support
- Swift.exe (PID: 4608)
- msedge.exe (PID: 6436)
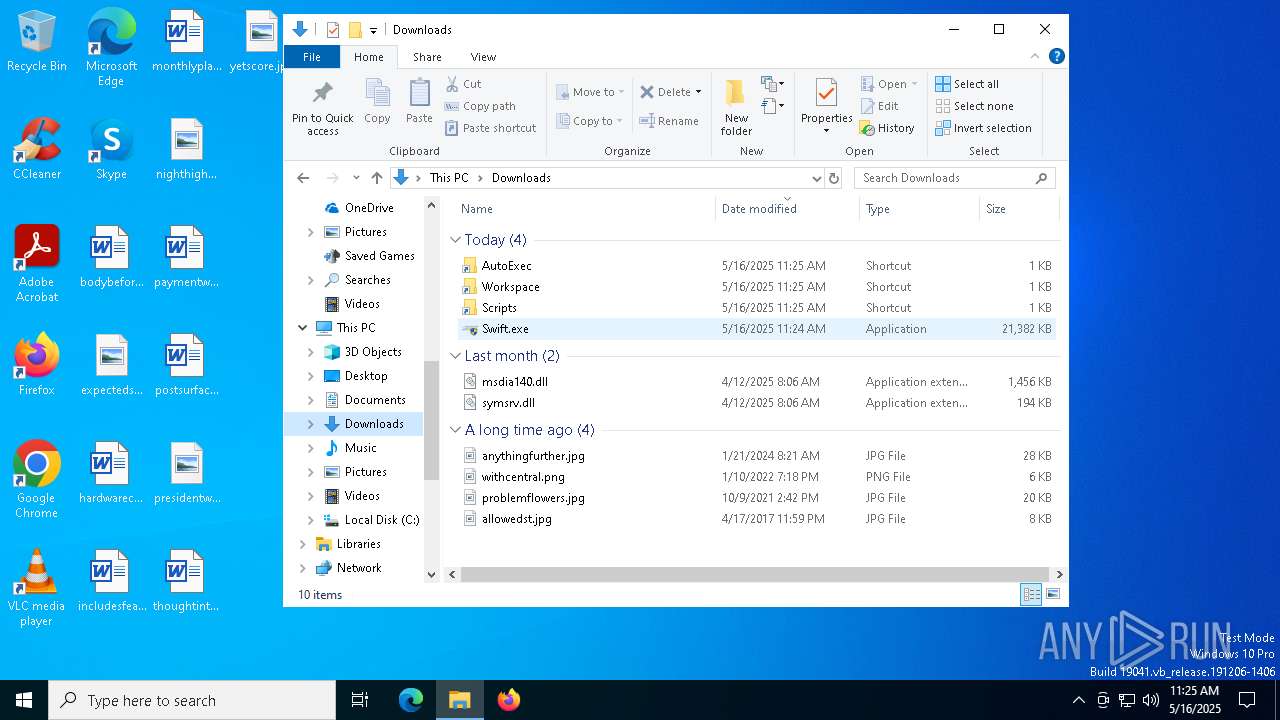
Manual execution by a user
- Swift.exe (PID: 3796)
- Swift.exe (PID: 2776)
- Swift.exe (PID: 456)
- Swift.exe (PID: 6392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
242
Monitored processes
102
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
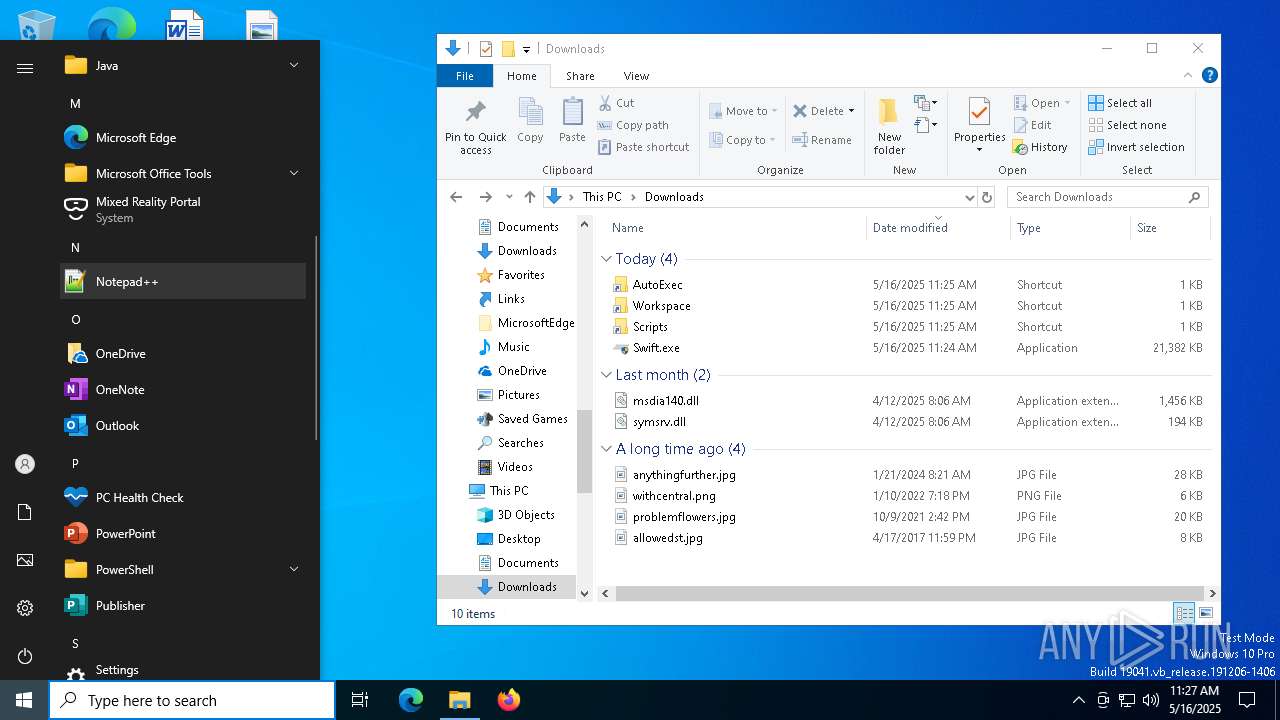
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | "C:\Users\admin\Downloads\Swift.exe" | C:\Users\admin\Downloads\Swift.exe | — | explorer.exe | |||||||||||
User: admin Company: swift Integrity Level: MEDIUM Description: swift-new Exit code: 3221226540 Version: 0.1.0 Modules
| |||||||||||||||
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6740 --field-trial-handle=2288,i,13409527160810120157,6341147292731910223,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
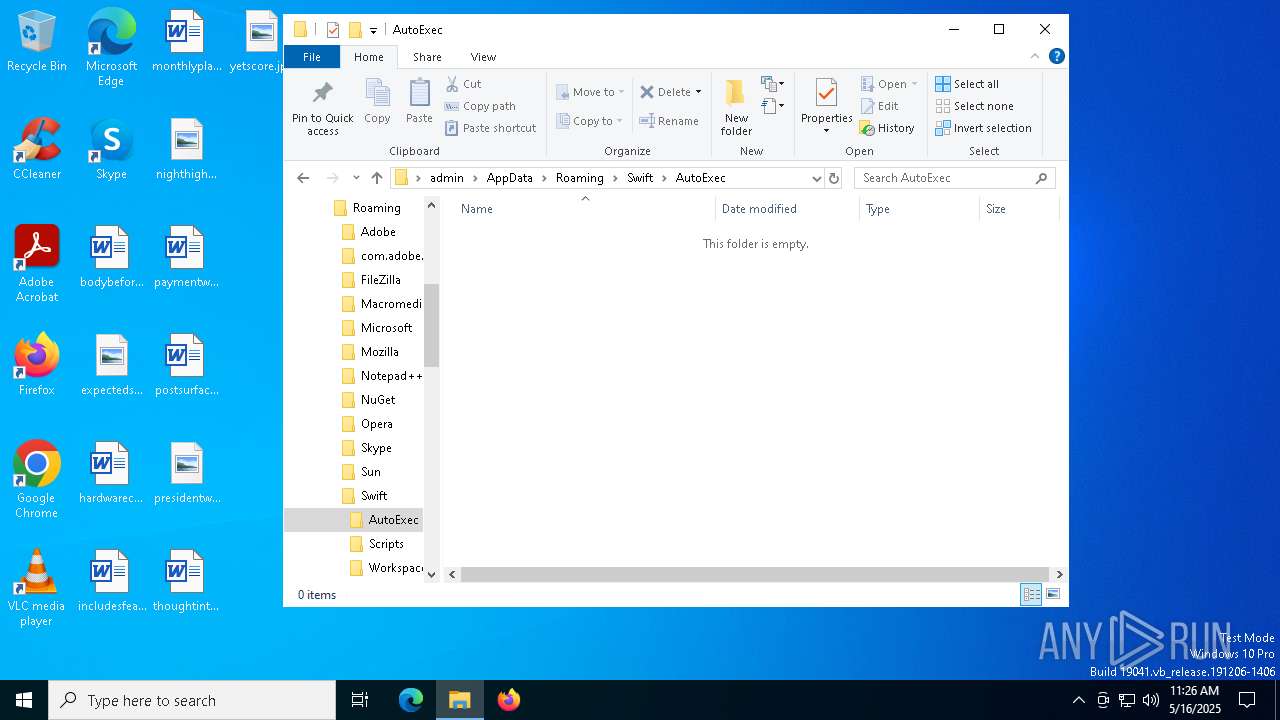
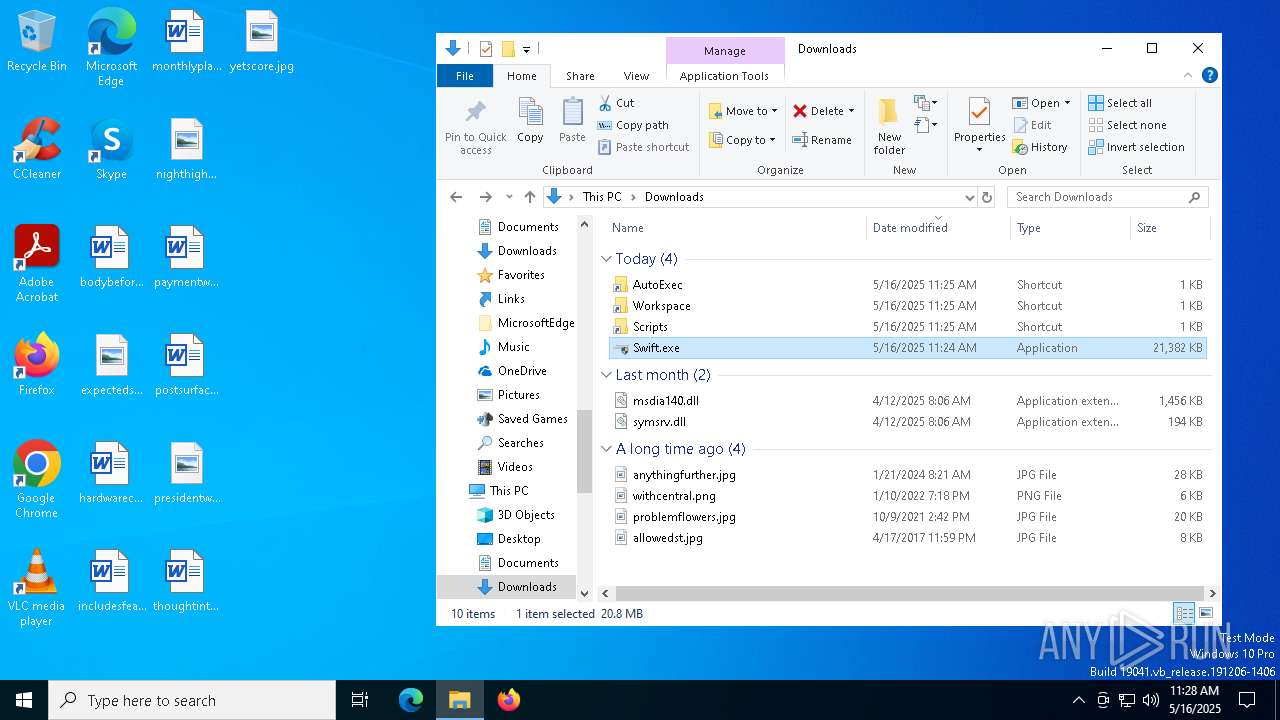
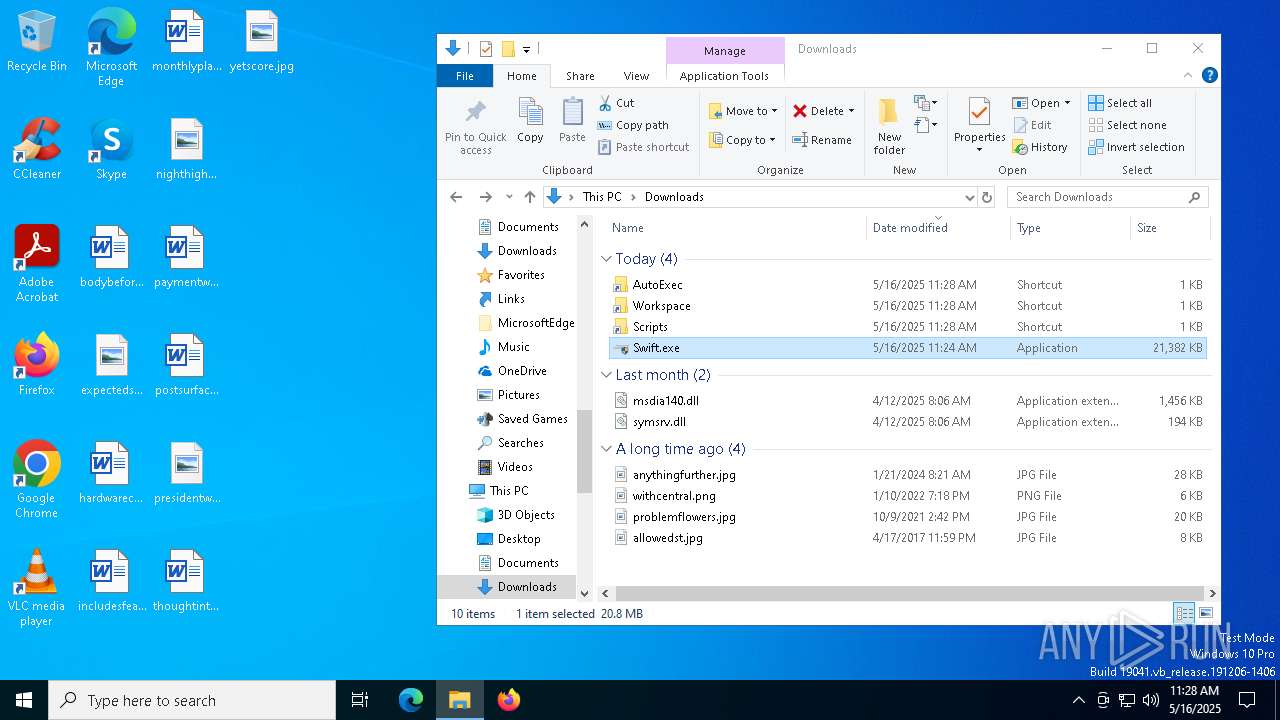
| 660 | "powershell" -WindowStyle Hidden -NoProfile -NonInteractive -Command "$WshShell = New-Object -comObject WScript.Shell; $Shortcut = $WshShell.CreateShortcut('C:\Users\admin\Downloads\Scripts.lnk'); $Shortcut.TargetPath = 'C:\Users\admin\AppData\Roaming\Swift\Scripts'; $Shortcut.Save()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Swift.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1500 --field-trial-handle=2248,i,11073292321753543169,5872903813578359563,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7232 --field-trial-handle=2288,i,13409527160810120157,6341147292731910223,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=6328 --field-trial-handle=2288,i,13409527160810120157,6341147292731910223,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
63 272
Read events
63 242
Write events
30
Delete events
0
Modification events
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2DCBFE4FD5932F00 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F0AA0650D5932F00 | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197218 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4B709FE1-9AA5-451B-968D-E05064F30952} | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197218 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9107E918-4529-46D1-8C77-E0F77C87BD0B} | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197218 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1B42B4B3-1038-4EFD-A41E-05B2D2F5C3B7} | |||
| (PID) Process: | (7468) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197218 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6A656B2B-128D-4607-AA2A-4EE40AF73074} | |||
Executable files
18
Suspicious files
438
Text files
136
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bd28.TMP | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bd28.TMP | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bd28.TMP | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bd28.TMP | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bd28.TMP | — | |
MD5:— | SHA256:— | |||
| 7468 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
66
DNS requests
75
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.38:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6252 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747803014&P2=404&P3=2&P4=YkZIw47stKGdAcx3Y%2bfDJb5lbicK%2b3VZDXri4UmeZGnPeJP%2fX55b42hn3iwqmiyLF%2b7Psi8DQB414uQyIx2%2bOg%3d%3d | unknown | — | — | whitelisted |
5544 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5544 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6252 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747803014&P2=404&P3=2&P4=YkZIw47stKGdAcx3Y%2bfDJb5lbicK%2b3VZDXri4UmeZGnPeJP%2fX55b42hn3iwqmiyLF%2b7Psi8DQB414uQyIx2%2bOg%3d%3d | unknown | — | — | whitelisted |
6252 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747803014&P2=404&P3=2&P4=YkZIw47stKGdAcx3Y%2bfDJb5lbicK%2b3VZDXri4UmeZGnPeJP%2fX55b42hn3iwqmiyLF%2b7Psi8DQB414uQyIx2%2bOg%3d%3d | unknown | — | — | whitelisted |
6252 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1747803016&P2=404&P3=2&P4=DmNH4Q5ekFanbx1oS5oOgapLCMgN6SVFrj2niZjz%2bzJkL7nWQDNJe%2bzD116ifpYBE4l9vLvg3ZGk2aTEPi%2fODQ%3d%3d | unknown | — | — | whitelisted |
6252 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1747803016&P2=404&P3=2&P4=DmNH4Q5ekFanbx1oS5oOgapLCMgN6SVFrj2niZjz%2bzJkL7nWQDNJe%2bzD116ifpYBE4l9vLvg3ZGk2aTEPi%2fODQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.38:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7756 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7756 | msedge.exe | 104.26.5.120:443 | getswift.gg | — | — | unknown |
7468 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7756 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
getswift.gg |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
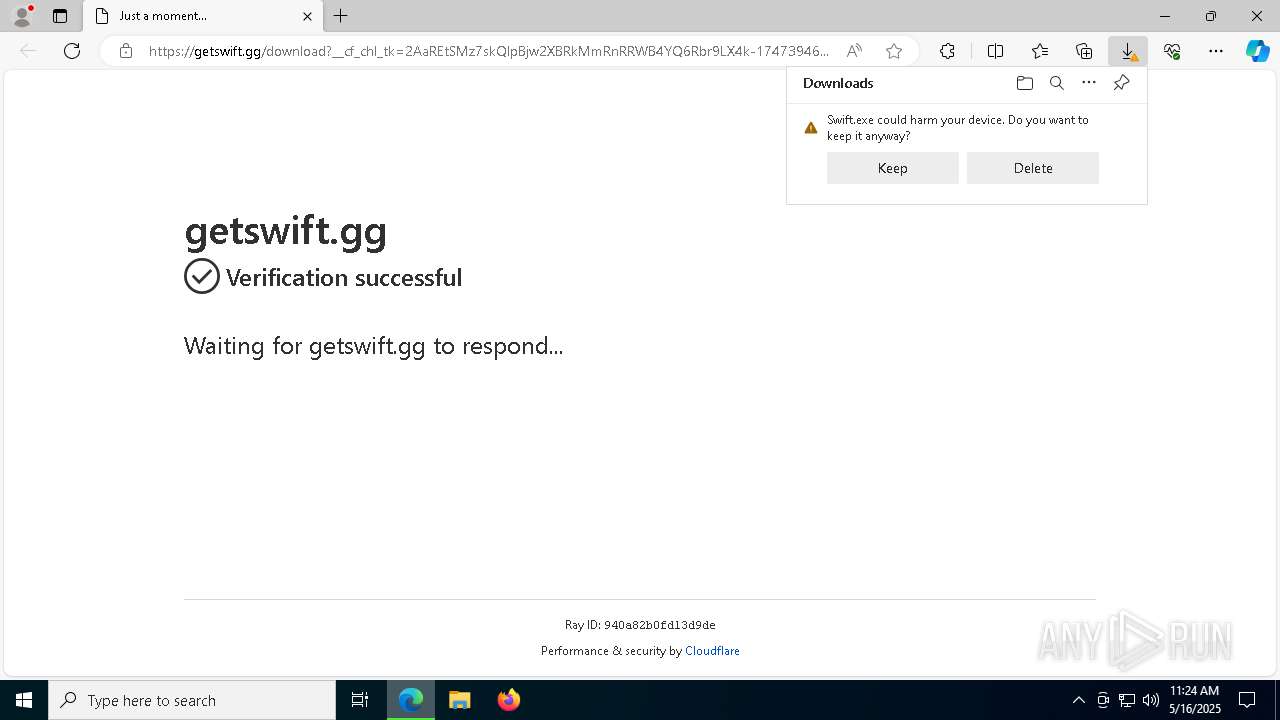
7756 | msedge.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (getswift .gg) |
7756 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7756 | msedge.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (getswift .gg) |
7756 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7756 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7756 | msedge.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (getswift .gg) |
7756 | msedge.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (getswift .gg) |
7756 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |