| download: | index.html |
| Full analysis: | https://app.any.run/tasks/49711c15-1a49-483f-9348-b944b81a3115 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 08:13:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, CR, LF line terminators |
| MD5: | 39089842C2A4AE3B1C2193559F1B20E4 |
| SHA1: | F6E9FD7CD7B9DECAFDCB63FBE954B33DDEF752E0 |
| SHA256: | 00756F29304BF1734C16B2A328AB6E12D6E9F8C3722D25A8CCC504E81F2CE0E3 |
| SSDEEP: | 1536:PFfJoeC8KKL+JhOBl+Kw6z33XnPRhTz+1QepDR2e3uUQVV5rqa/I6vdlaTr:noeC1BOBc83HG1QO3uVrrqa/IQdlaTr |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks for external IP
- chrome.exe (PID: 3632)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3632)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2912)
Reads internet explorer settings
- iexplore.exe (PID: 1040)
- iexplore.exe (PID: 2316)
Creates files in the user directory
- iexplore.exe (PID: 2316)
- iexplore.exe (PID: 1040)
Application launched itself
- iexplore.exe (PID: 2912)
- chrome.exe (PID: 3632)
Manual execution by user
- chrome.exe (PID: 3632)
Reads settings of System Certificates
- iexplore.exe (PID: 2316)
Reads Internet Cache Settings
- iexplore.exe (PID: 2316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
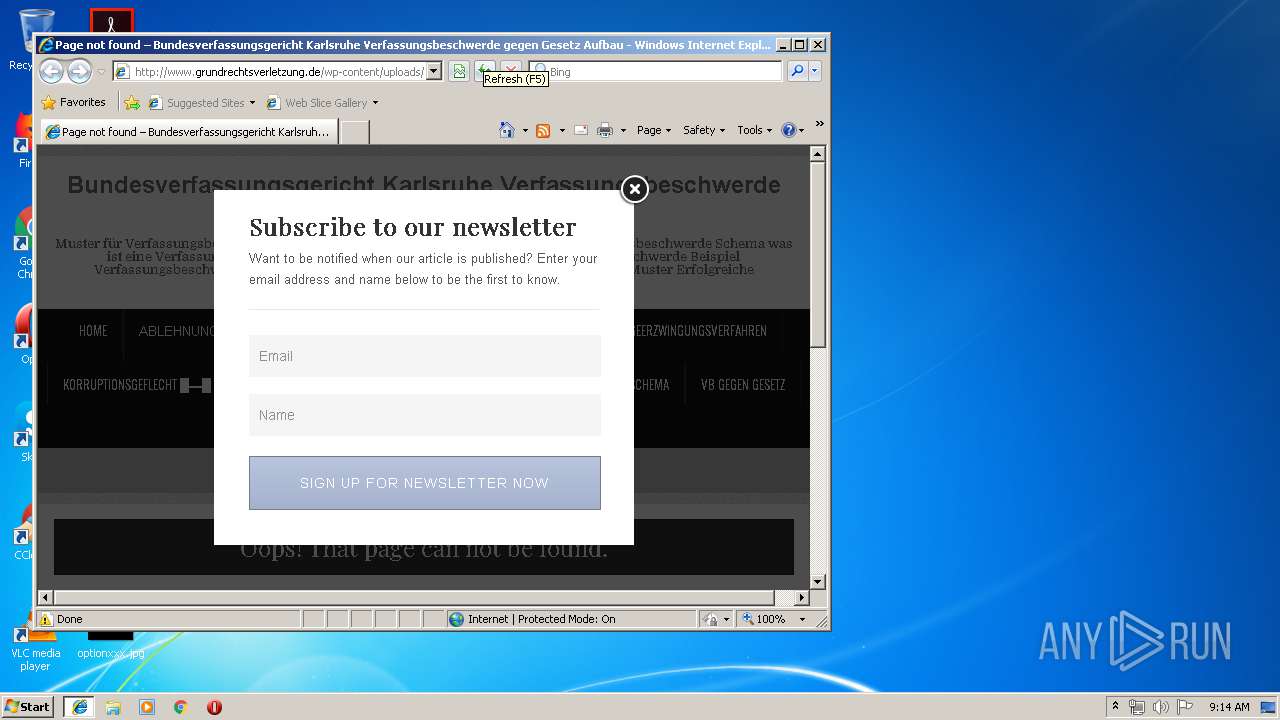
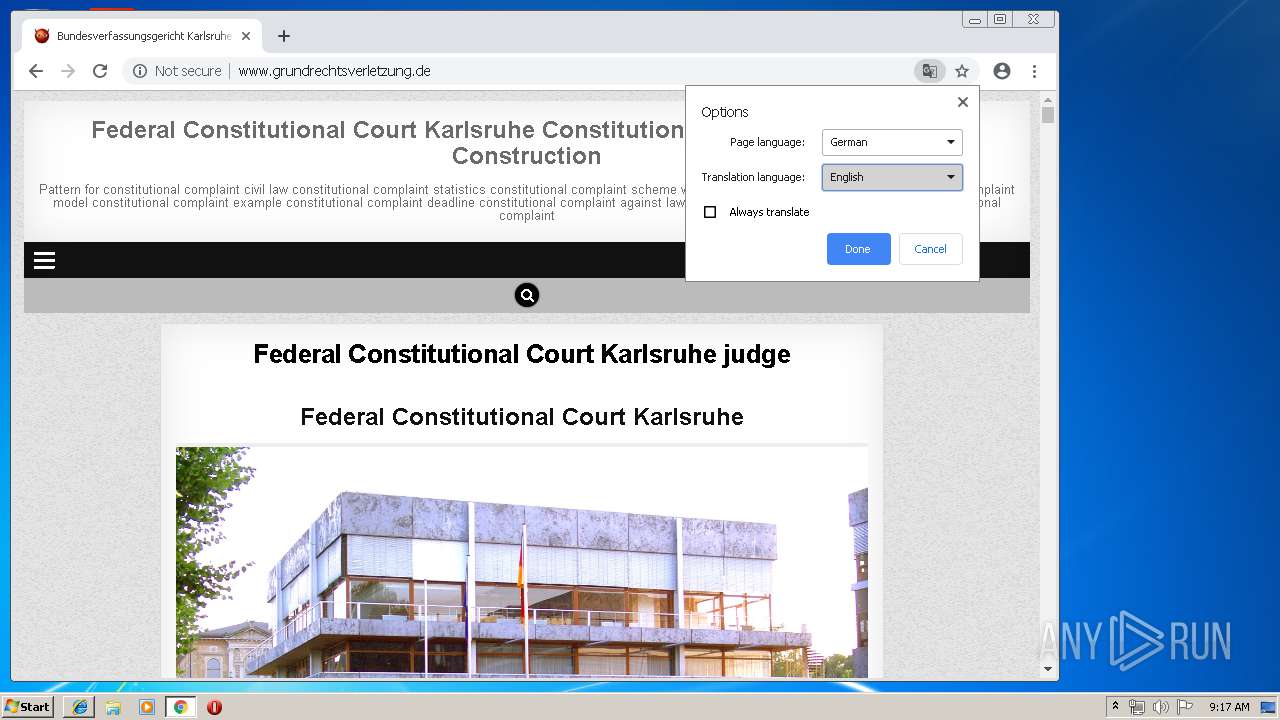
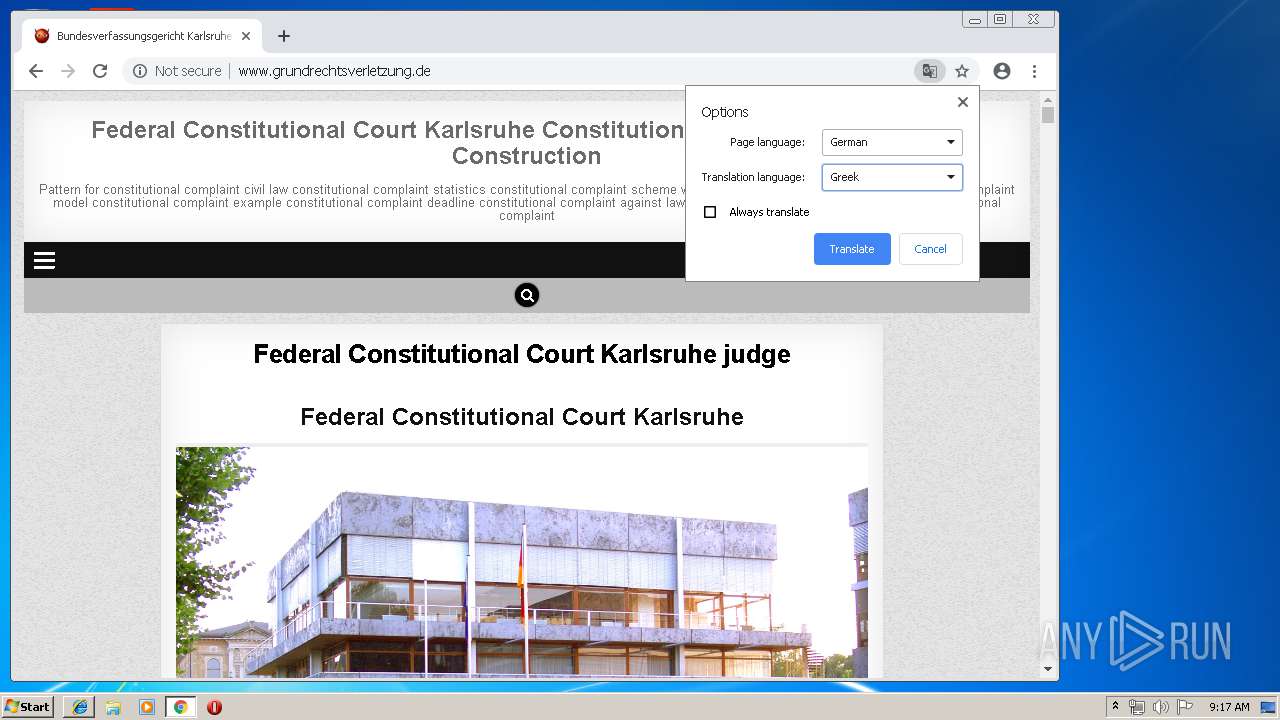
| viewport: | width=device-width, initial-scale=1, maximum-scale=1 |
|---|---|
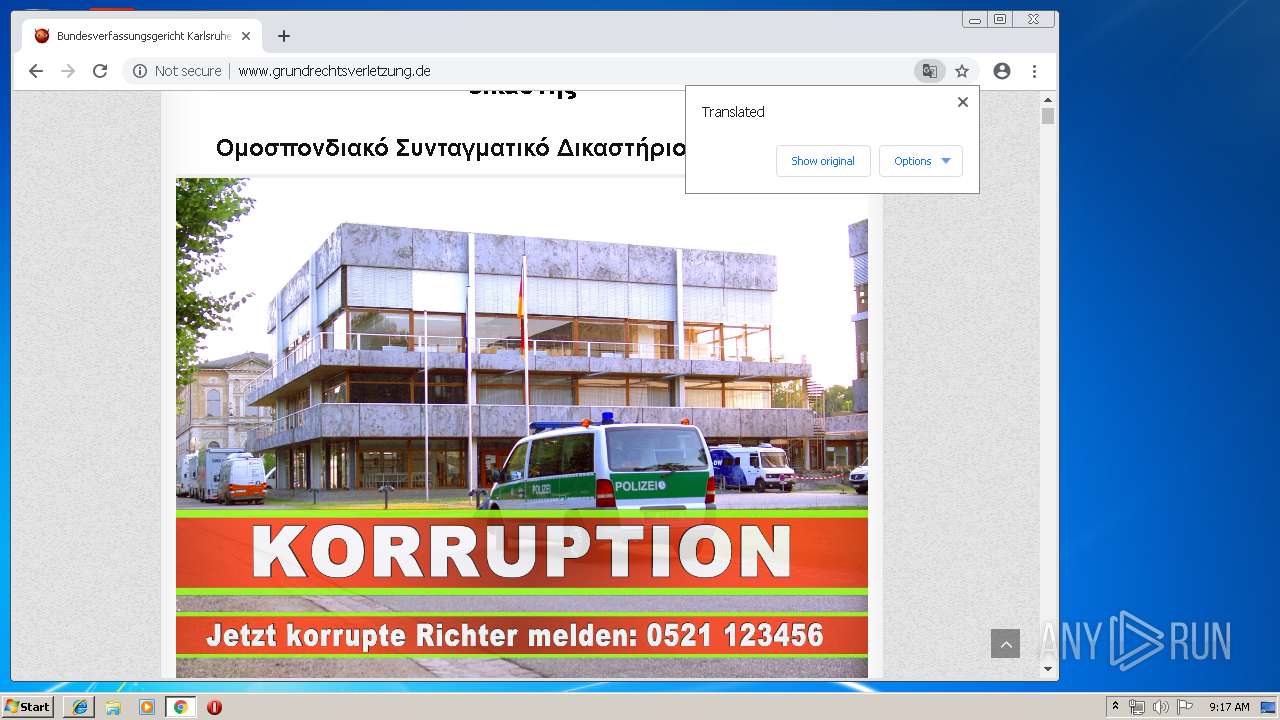
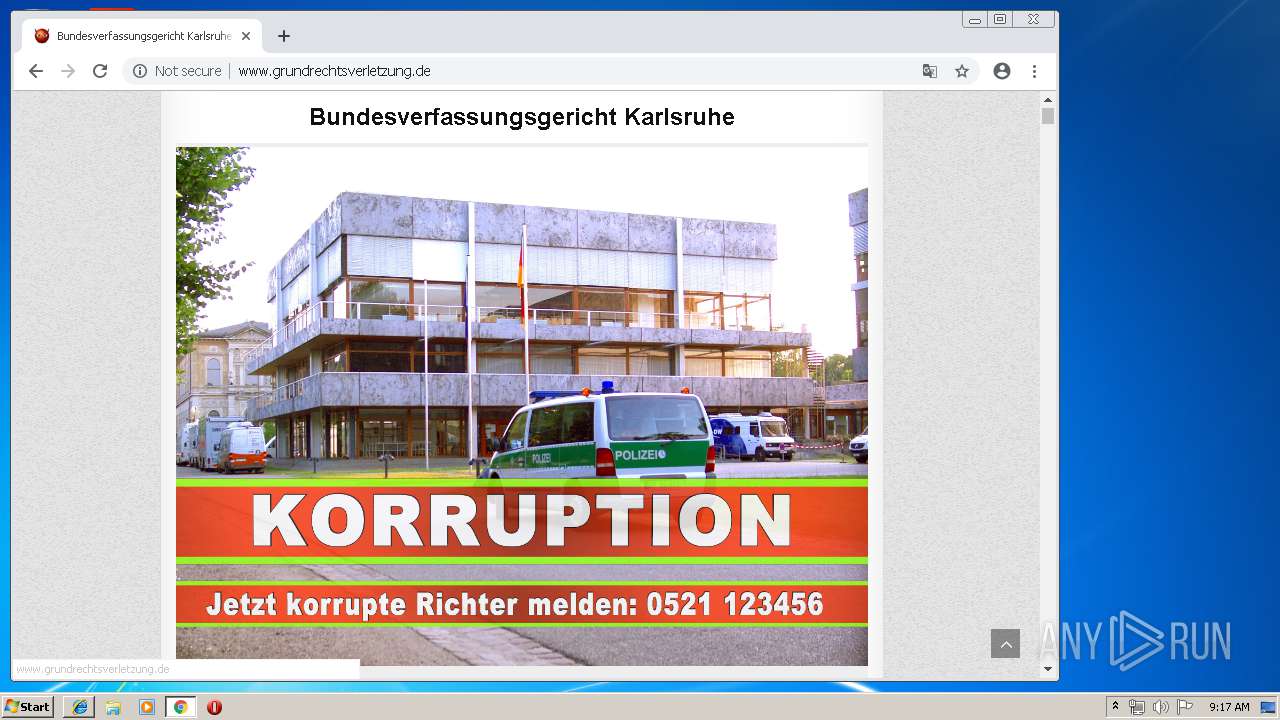
| Title: | Bundesverfassungsgericht Karlsruhe Verfassungsbeschwerde gegen Gesetz Aufbau – Muster für Verfassungsbeschwerde Zivilrecht Verfassungsbeschwerde Statistik Verfassungsbeschwerde Schema was ist eine Verfassungsbeschwerde Verfassungsbeschwerde mMuster Verfassungsbeschwerde Beispiel Verfassungsbeschwerde Frist Verfassungsbeschwerde gegen Gesetz Schema Aufbau Muster Erfolgreiche Verfassungsbeschwerde |
| Generator: | WordPress 5.1.1 |
Total processes
59
Monitored processes
27
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,15625573706286250378,16216844200742095384,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5369971910500867673 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5369971910500867673 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3652 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15625573706286250378,16216844200742095384,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10957146658064893950 --mojo-platform-channel-handle=3960 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,15625573706286250378,16216844200742095384,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7646771740164978166 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7646771740164978166 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15625573706286250378,16216844200742095384,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2402599998803442285 --mojo-platform-channel-handle=3788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2912 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,15625573706286250378,16216844200742095384,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7345786338664034966 --mojo-platform-channel-handle=968 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15625573706286250378,16216844200742095384,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9563874585862211386 --mojo-platform-channel-handle=2168 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3644 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15625573706286250378,16216844200742095384,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17107850296150376791 --mojo-platform-channel-handle=3616 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15625573706286250378,16216844200742095384,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7167992536962393570 --mojo-platform-channel-handle=3728 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 104
Read events
931
Write events
168
Delete events
5
Modification events
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {F396F5FD-8CE9-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307060003000C0008000D001A007403 | |||
Executable files
0
Suspicious files
111
Text files
381
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2912 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2912 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF79EC5BAD71DEBA62.TMP | — | |
MD5:— | SHA256:— | |||
| 2316 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PQDA1P20\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 2316 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\I5E8WIGV\wp-email-subscription-popup[1].css | text | |
MD5:— | SHA256:— | |||
| 2912 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{F396F5FE-8CE9-11E9-B63D-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 2316 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PQDA1P20\js[1] | text | |
MD5:— | SHA256:— | |||
| 2912 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 2316 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\T3HAOHAH\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2316 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\56QB8QNN\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
297
TCP/UDP connections
70
DNS requests
42
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
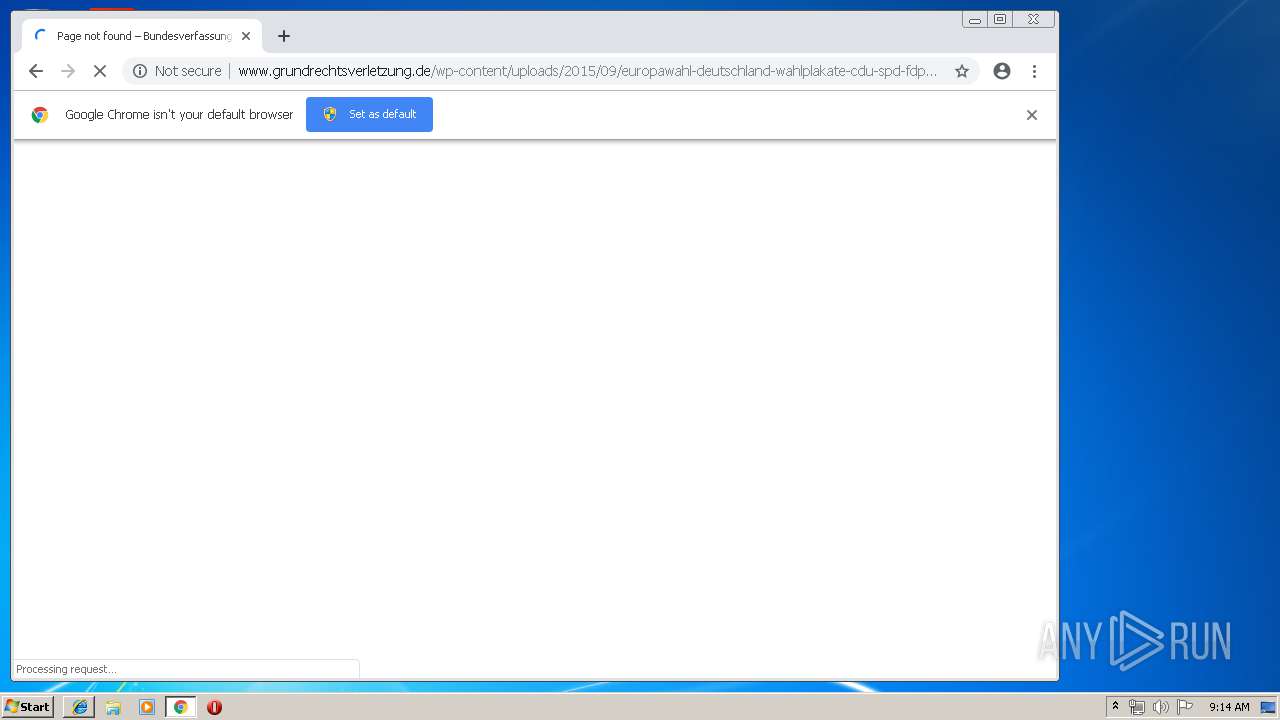
2316 | iexplore.exe | GET | 404 | 46.30.215.181:80 | http://www.grundrechtsverletzung.de/wp-content/uploads/2015/09/europawahl-deutschland-wahlplakate-cdu-spd-fdp-gr%C3%BCne-linke-afd-26-1024x768.jpg | DK | html | 28.1 Kb | suspicious |
2316 | iexplore.exe | GET | 200 | 46.30.215.181:80 | http://www.grundrechtsverletzung.de/wp-content/plugins/email-subscribe/css/wp-email-subscription-popup.css?ver=5.1.1 | DK | text | 1.76 Kb | suspicious |
2316 | iexplore.exe | GET | 200 | 172.217.22.106:80 | http://fonts.googleapis.com/css?family=Playfair+Display:400,400i,700,700i|Domine:400,700|Oswald:400,700|Poppins:400,400i,700,700i | US | text | 305 b | whitelisted |
2316 | iexplore.exe | GET | 200 | 46.30.215.181:80 | http://www.grundrechtsverletzung.de/wp-content/plugins/wysija-newsletters/css/validationEngine.jquery.css?ver=2.11 | DK | text | 1.14 Kb | suspicious |
2316 | iexplore.exe | GET | 200 | 46.30.215.181:80 | http://www.grundrechtsverletzung.de/wp-content/plugins/visitor-map/css/style.css?ver=5.1.1 | DK | text | 2.06 Kb | suspicious |
2316 | iexplore.exe | GET | 200 | 216.58.206.10:80 | http://maps.googleapis.com/maps/api/js?key=AIzaSyDgiem5bbeBic1L2fke9TiNU71piPtzI2o&v=3.exp&ver=5.1.1 | US | text | 32.0 Kb | whitelisted |
2316 | iexplore.exe | GET | 200 | 46.30.215.181:80 | http://www.grundrechtsverletzung.de/wp-content/plugins/wp-show-posts/css/wp-show-posts-min.css?ver=1.1.3 | DK | text | 1.04 Kb | suspicious |
2316 | iexplore.exe | GET | 200 | 46.30.215.181:80 | http://www.grundrechtsverletzung.de/wp-includes/js/jquery/jquery.js?ver=1.12.4 | DK | text | 32.9 Kb | suspicious |
2316 | iexplore.exe | GET | 200 | 46.30.215.181:80 | http://www.grundrechtsverletzung.de/wp-content/plugins/email-subscribe/css/subscribe-popup.css?ver=5.1.1 | DK | text | 1.58 Kb | suspicious |
2316 | iexplore.exe | GET | 200 | 46.30.215.181:80 | http://www.grundrechtsverletzung.de/wp-content/themes/wp-masonry-----/assets/css/font-awesome.min.css | DK | text | 6.89 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 209.197.3.15:445 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2912 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4 | System | 209.197.3.15:139 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
4 | System | 172.217.22.106:445 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2316 | iexplore.exe | 46.30.215.181:80 | www.grundrechtsverletzung.de | One.com A/S | DK | suspicious |
2316 | iexplore.exe | 172.217.22.106:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2316 | iexplore.exe | 209.197.3.15:80 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2316 | iexplore.exe | 172.217.21.227:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
netdna.bootstrapcdn.com |
| whitelisted |
www.grundrechtsverletzung.de |
| unknown |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
maps.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
s.w.org |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3632 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3632 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |