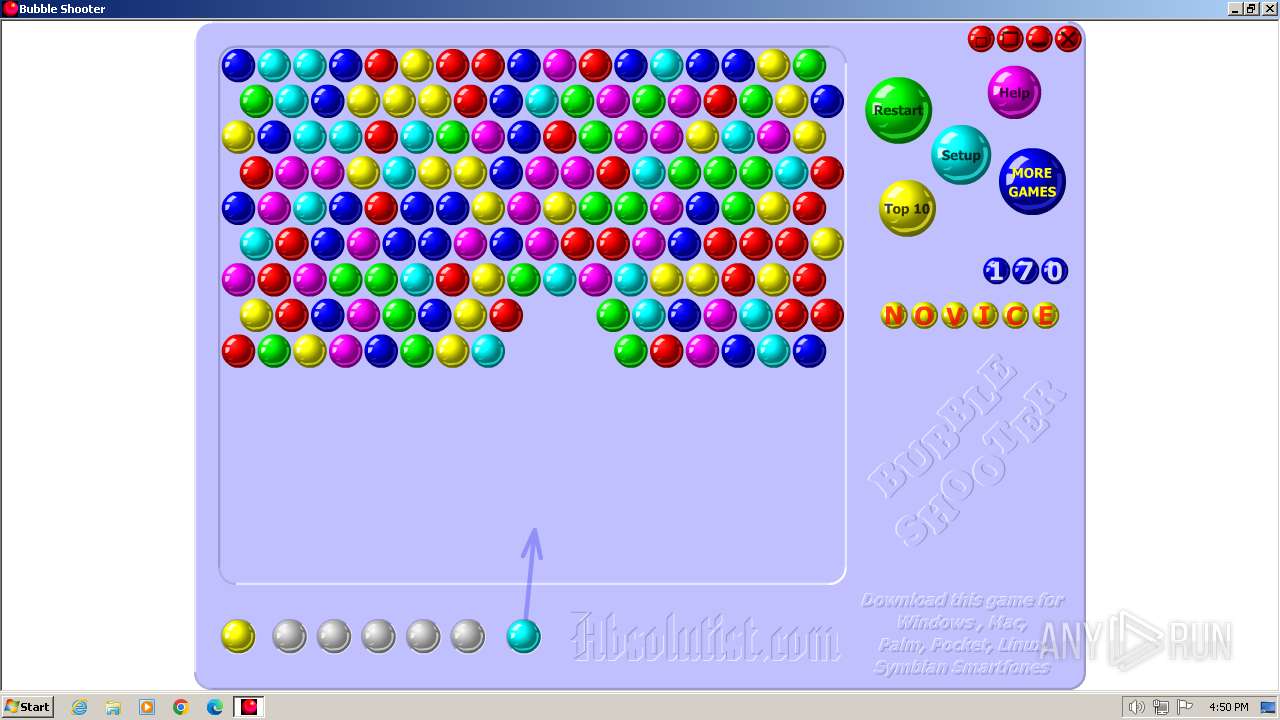
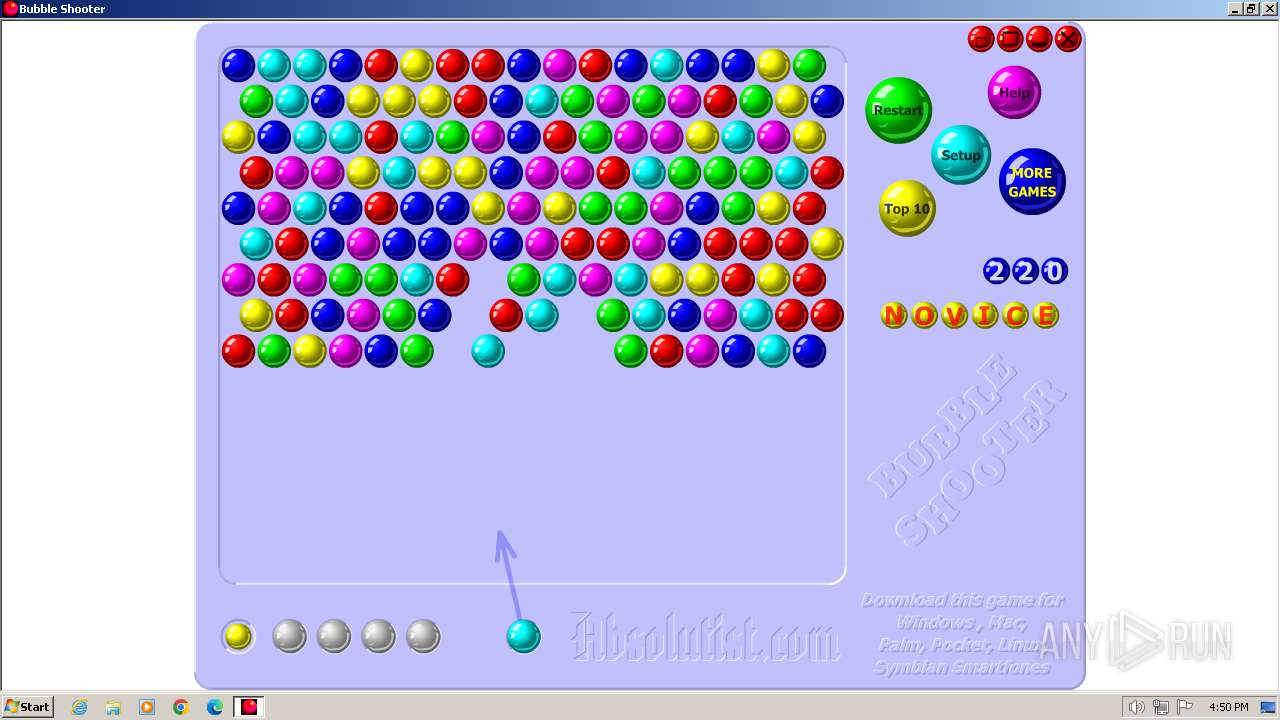
| File name: | Bubble Shooter.exe |
| Full analysis: | https://app.any.run/tasks/cdd92900-6284-4427-b328-034c43c62f1a |
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2024, 16:50:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6CF272E0C5378AA80AF6568C2153C1D6 |
| SHA1: | 3EC34E27DC4E86CB647CC720E3D6E2C50B214376 |
| SHA256: | 005D46CDCCDA33C55CDA8406840F643FFFE04FDD0574898F57292A2C4C3678D5 |
| SSDEEP: | 98304:AxrtwKlMDlj/TdIPyazrBaZMr3nSM7BZakY6gHKD4VwK8z/Cpzt1+jfCJdnNxHAj:/G |
MALICIOUS
Drops the executable file immediately after the start
- Bubble Shooter.exe (PID: 4052)
SUSPICIOUS
Executable content was dropped or overwritten
- Bubble Shooter.exe (PID: 4052)
Reads security settings of Internet Explorer
- Bubble Shooter.exe (PID: 4052)
Reads the Internet Settings
- Bubble Shooter.exe (PID: 4052)
INFO
Create files in a temporary directory
- Bubble Shooter.exe (PID: 4052)
Checks supported languages
- Bubble Shooter.exe (PID: 4052)
Reads the computer name
- Bubble Shooter.exe (PID: 4052)
Reads the machine GUID from the registry
- Bubble Shooter.exe (PID: 4052)
Reads CPU info
- Bubble Shooter.exe (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (38.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (28.2) |
| .exe | | | Win64 Executable (generic) (25) |
| .exe | | | Win32 Executable (generic) (4) |
| .exe | | | Generic Win/DOS Executable (1.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2005:09:28 10:51:56+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7 |
| CodeSize: | 1064960 |
| InitializedDataSize: | 1335296 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb62cb |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Game Time! |
| FileDescription: | - |
| FileVersion: | 1 |
| InternalName: | Untitled |
| LegalCopyright: | Copyright 2001-2002 |
| LegalTrademarks: | - |
| OriginalFileName: | Untitled.exe |
| PrivateBuild: | - |
| ProductName: | The Crazy Hacker |
| ProductVersion: | 1 |
| SpecialBuild: | - |
Total processes
36
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4052 | "C:\Users\admin\AppData\Local\Temp\Bubble Shooter.exe" | C:\Users\admin\AppData\Local\Temp\Bubble Shooter.exe | explorer.exe | ||||||||||||
User: admin Company: Game Time! Integrity Level: MEDIUM Exit code: 0 Version: 1.0 Modules
| |||||||||||||||
Total events
525
Read events
515
Write events
10
Delete events
0
Modification events
| (PID) Process: | (4052) Bubble Shooter.exe | Key: | HKEY_CURRENT_USER\Software\Game Time!\Untitled\V1.0\Settings |
| Operation: | write | Name: | crc |
Value: 39EDBCA0625EC2CBBADB0F3119CD270D | |||
| (PID) Process: | (4052) Bubble Shooter.exe | Key: | HKEY_CURRENT_USER\Software\Game Time!\Untitled\V1.0\Settings |
| Operation: | write | Name: | Options |
Value: 1100000054006800650020004300720061007A00790020004800610063006B006500720000000100000000000B000000470061006D0065002000540069006D006500210000001400000043006F007000790072006900670068007400200032003000300031002D00320030003000320000000100000000000100000000000400000031002E0030000000000000000001000011010000010000000100000000000F00000042007500620062006C0065002000530068006F006F007400650072000000020000000000000004000000000000000000000000000000000000000100000001000000000000000000000000000000030000006CC22424211ADF2BD7D6A81CEA8E76D47C4B3649D470D07C43167B4E9E43AC676F70A745C761EFD7E2779B0070CB00A4A8C88F9BA1400B9D010000000000000000000000000001000000000000000000120000005300570046004B006900740020006F006E002000740068006500200077006500620000001600000068007400740070003A002F002F007700770077002E007300770066006B00690074002E0063006F006D0000000B00000043006F006E00740061006300740020007500730000001300000073007500700070006F007200740040007300770066006B00690074002E0063006F006D0000000000FF000000FF00F5FFFFFF0000000000000000000000009001000000000000010201220E0000004D0053002000530061006E0073002000530065007200690066000000F5FFFFFF0000000000000000000000009001000000000000010201220E0000004D0053002000530061006E0073002000530065007200690066000000010000000000000001000000000000000000010000000000000000000000000000000000D60706000500170011000E00310022020000000001000000000050000000 | |||
| (PID) Process: | (4052) Bubble Shooter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4052) Bubble Shooter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4052) Bubble Shooter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4052) Bubble Shooter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4052 | Bubble Shooter.exe | C:\Users\admin\AppData\Local\Temp\17F77F0.tmp | executable | |
MD5:900373C059C2B51CA91BF110DBDECB33 | SHA256:31453FD8F743C19E27F8FA04EE88DFEBE95A7884CDFBC15AB0EB8994829AAD61 | |||
| 4052 | Bubble Shooter.exe | C:\Users\admin\AppData\Local\Temp\{9D153322-5488-4D36-931F-79F36E6C643D}\1985.swf | binary | |
MD5:5F4A4E028AFC3F909867FE6BCFF4BCC2 | SHA256:7591BAD20714075C287EE59113EE524CA1CA3E779DC06077347E34CDB9EA4DEA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |