| File name: | Set-TessianRegistryKeys.ps1 |
| Full analysis: | https://app.any.run/tasks/ea0c04a7-d36b-41a6-9fd1-f5e550eea7b5 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2024, 08:05:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-c++ |
| File info: | C++ source, ASCII text |
| MD5: | C2B174A64BF10CEBBA69F2A8F452B027 |
| SHA1: | 0632E0A18946750BFE1763B2A2D5F98D2FC31267 |
| SHA256: | 005B02FD914E10E925D8F6272B6D3A759D5587DF2C0F3BAA09555156E72AFBD8 |
| SSDEEP: | 192:duyDy5L7VN6+9MM69vU12B2NjOyySWJATPq8T/SCyKFnpVW31zqJDSqyK1nc6NlU:2jcSjGiTKcAOtQu9TpByxEQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- powershell.exe (PID: 3952)
- powershell.exe (PID: 328)
- powershell.exe (PID: 1660)
- powershell.exe (PID: 1844)
- powershell_ise.exe (PID: 2468)
- cmd.exe (PID: 2376)
- powershell.exe (PID: 2776)
Creates file in the systems drive root
- powershell_ise.exe (PID: 2468)
Reads settings of System Certificates
- powershell_ise.exe (PID: 2468)
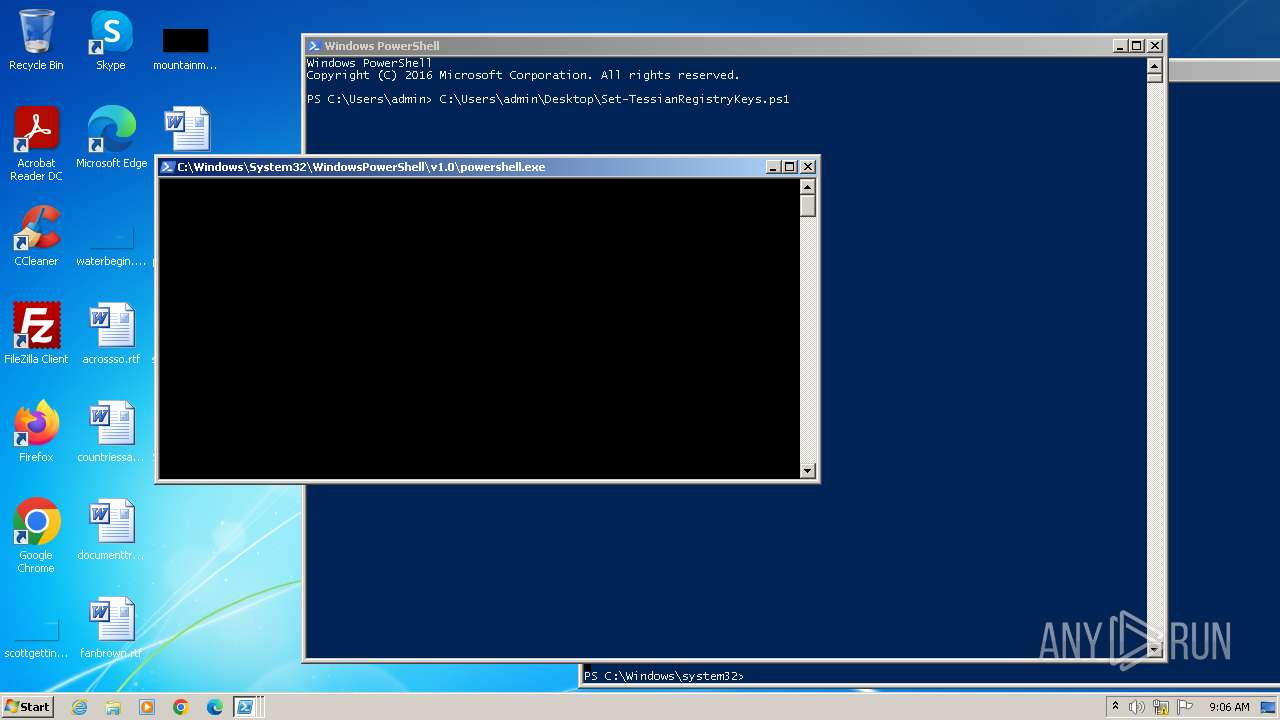
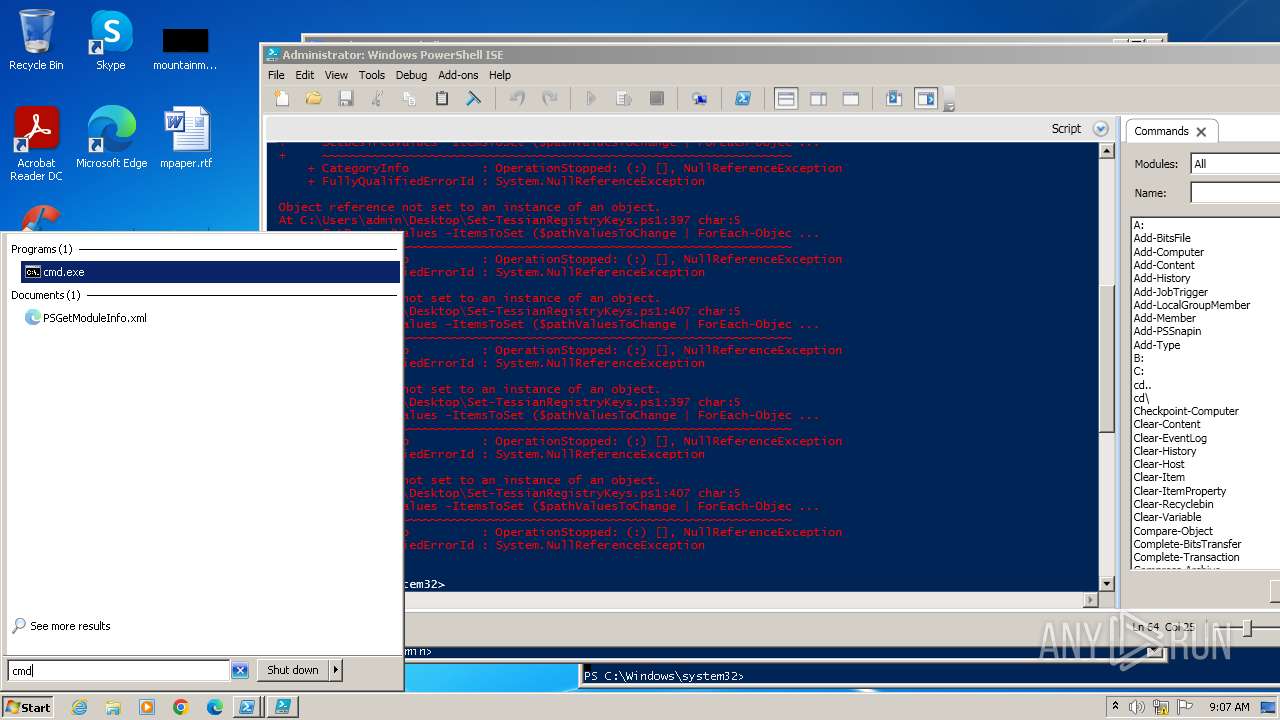
The process executes Powershell scripts
- cmd.exe (PID: 2376)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2376)
INFO
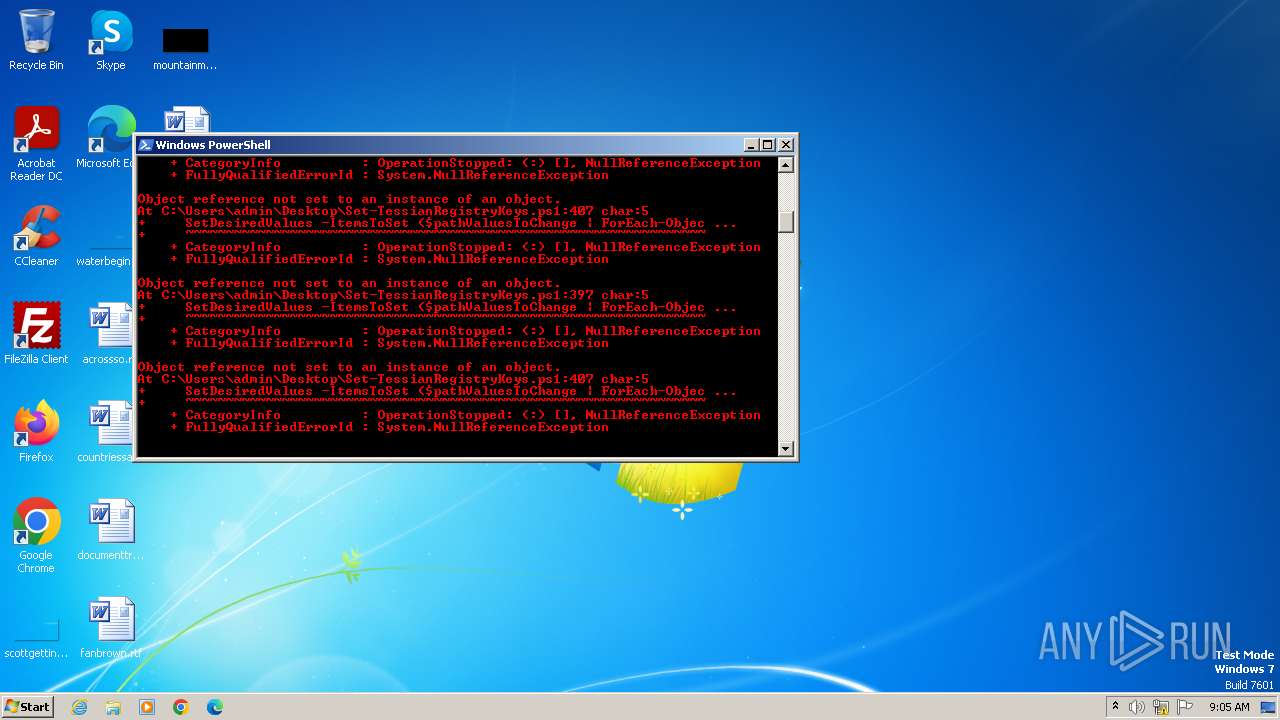
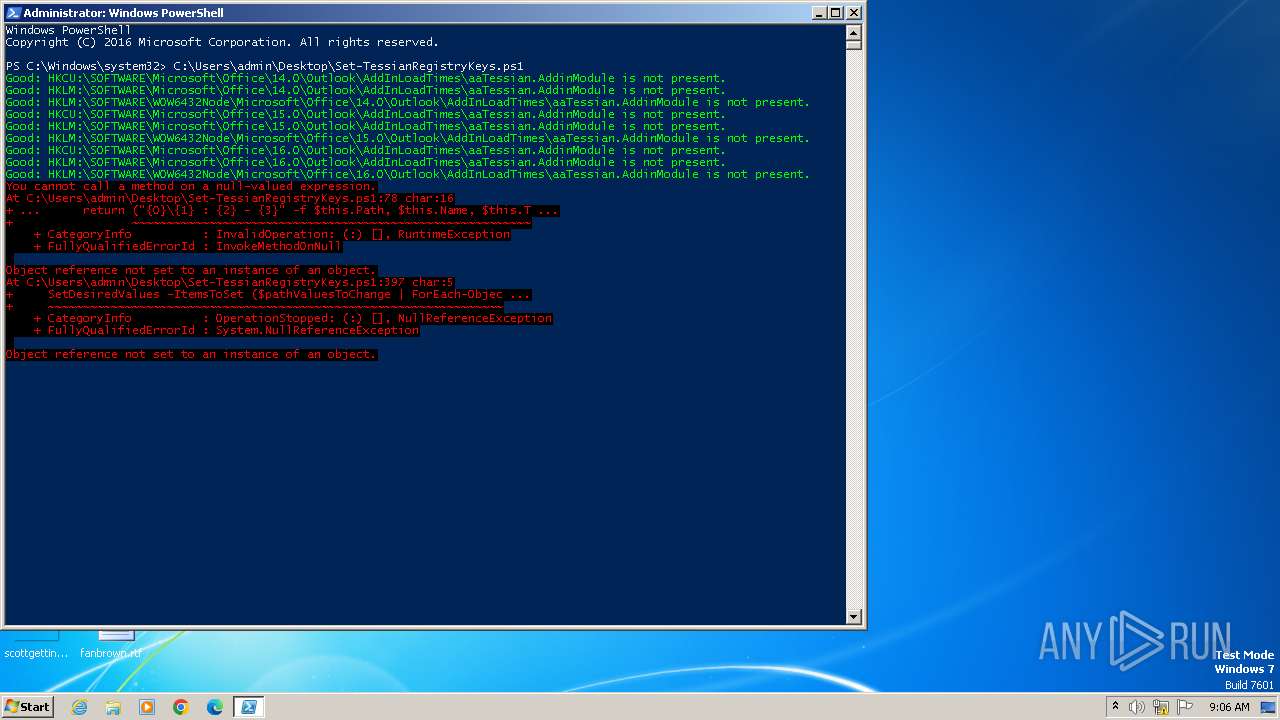
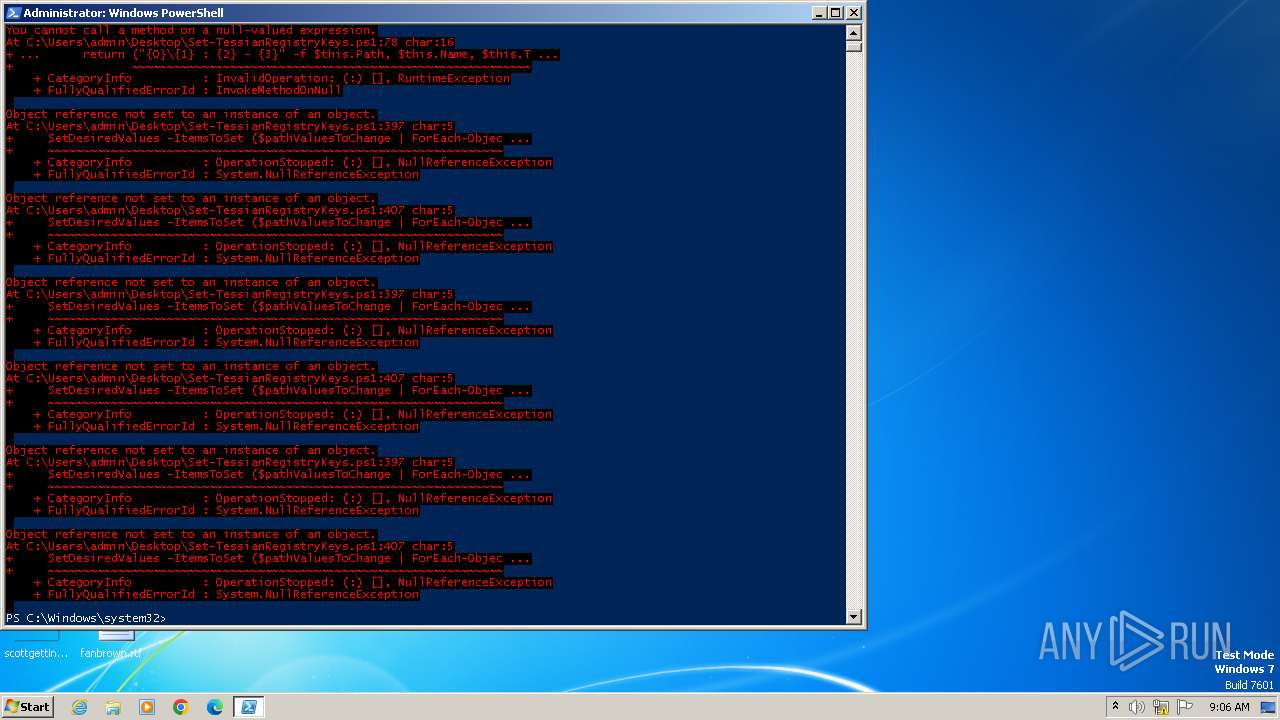
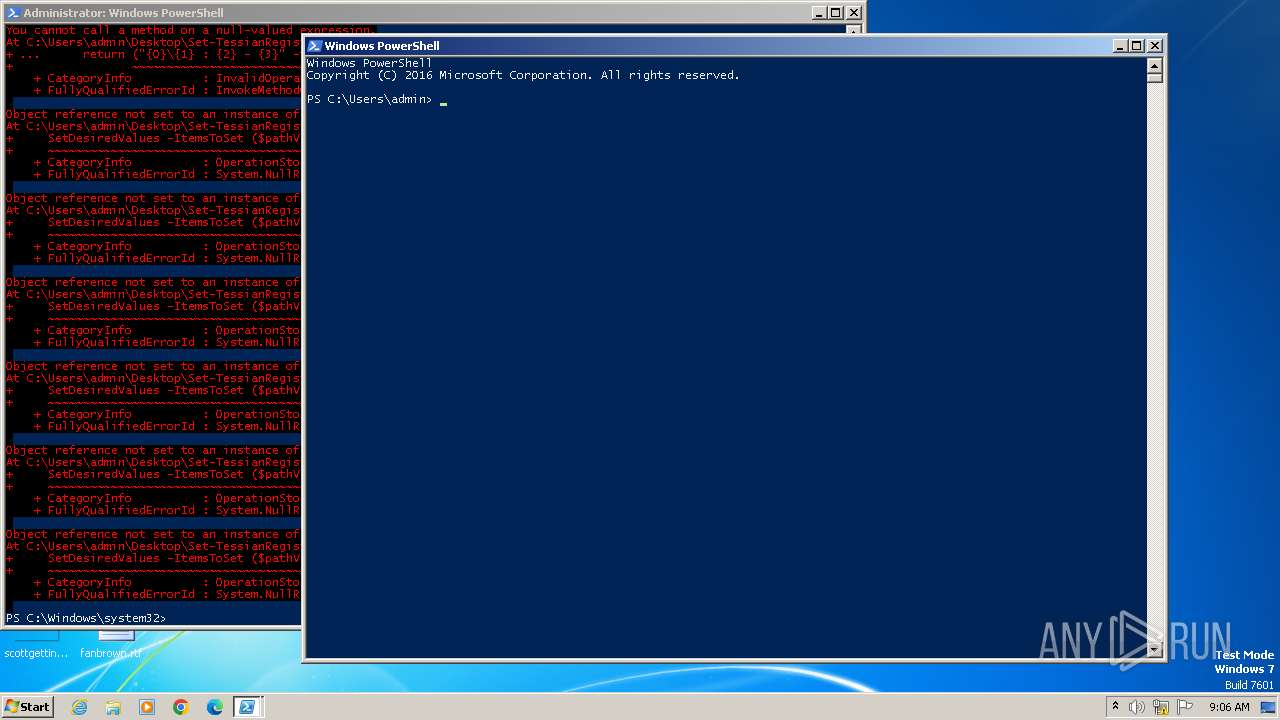
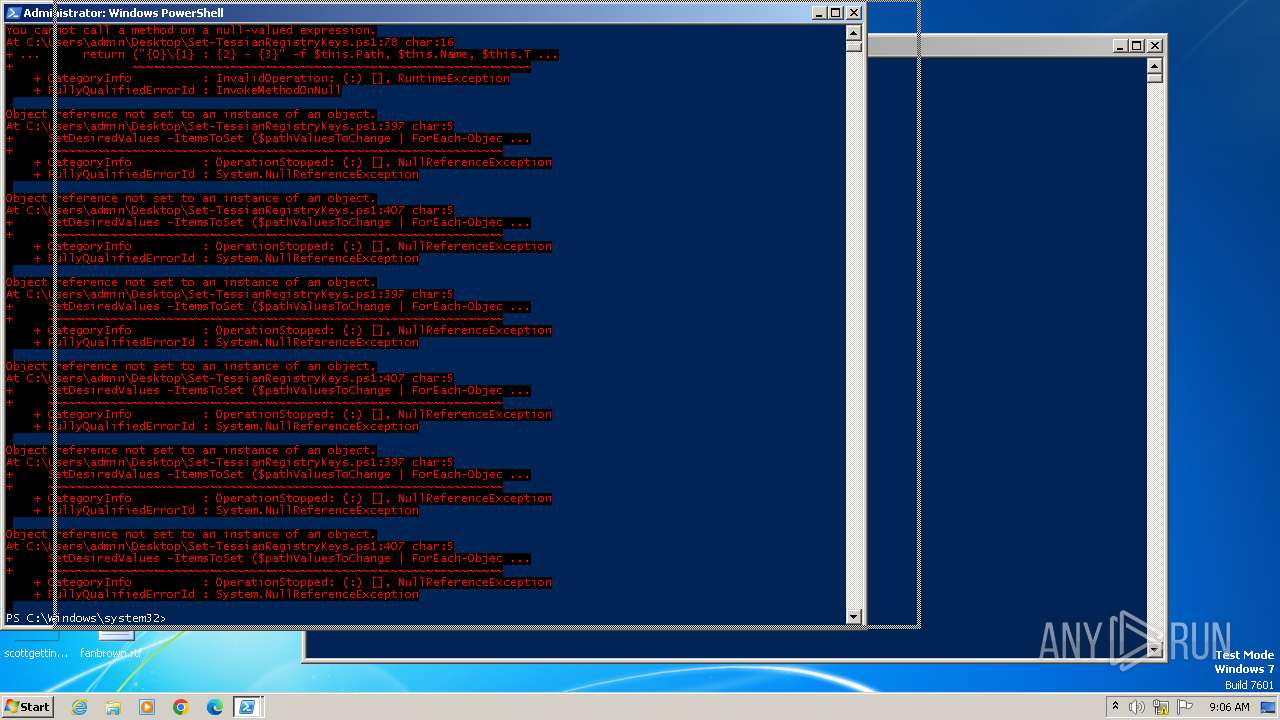
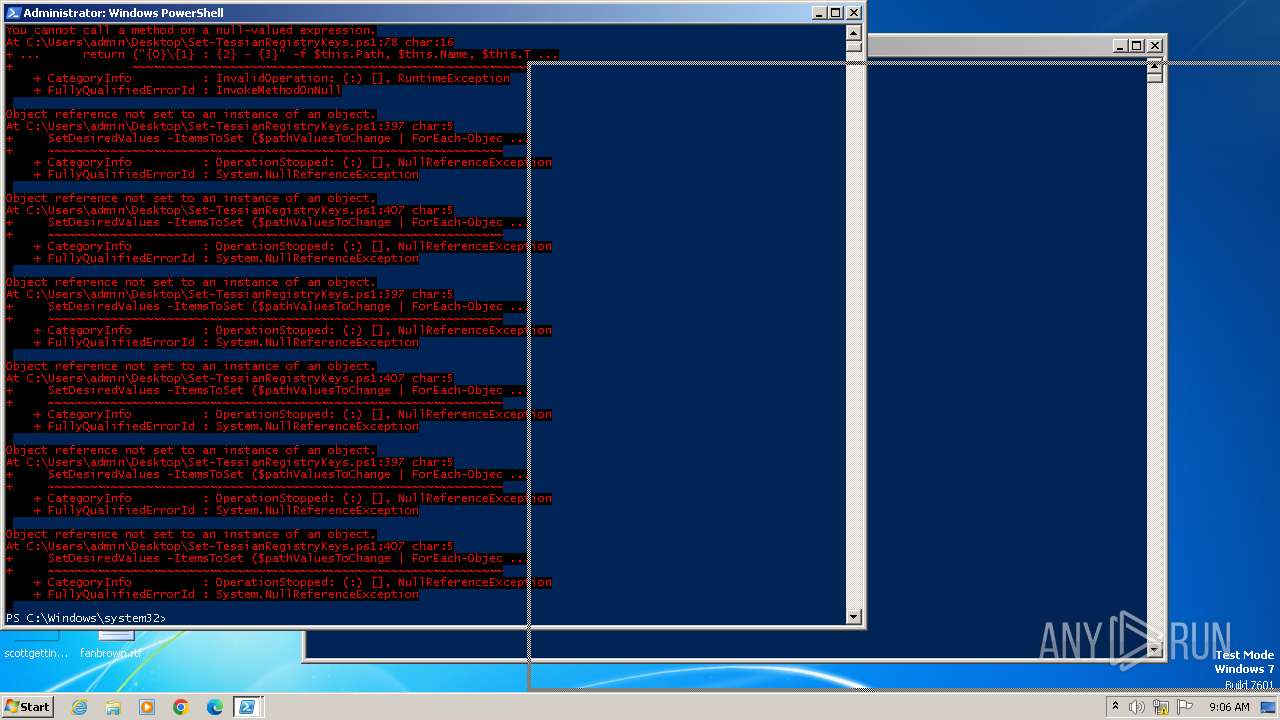
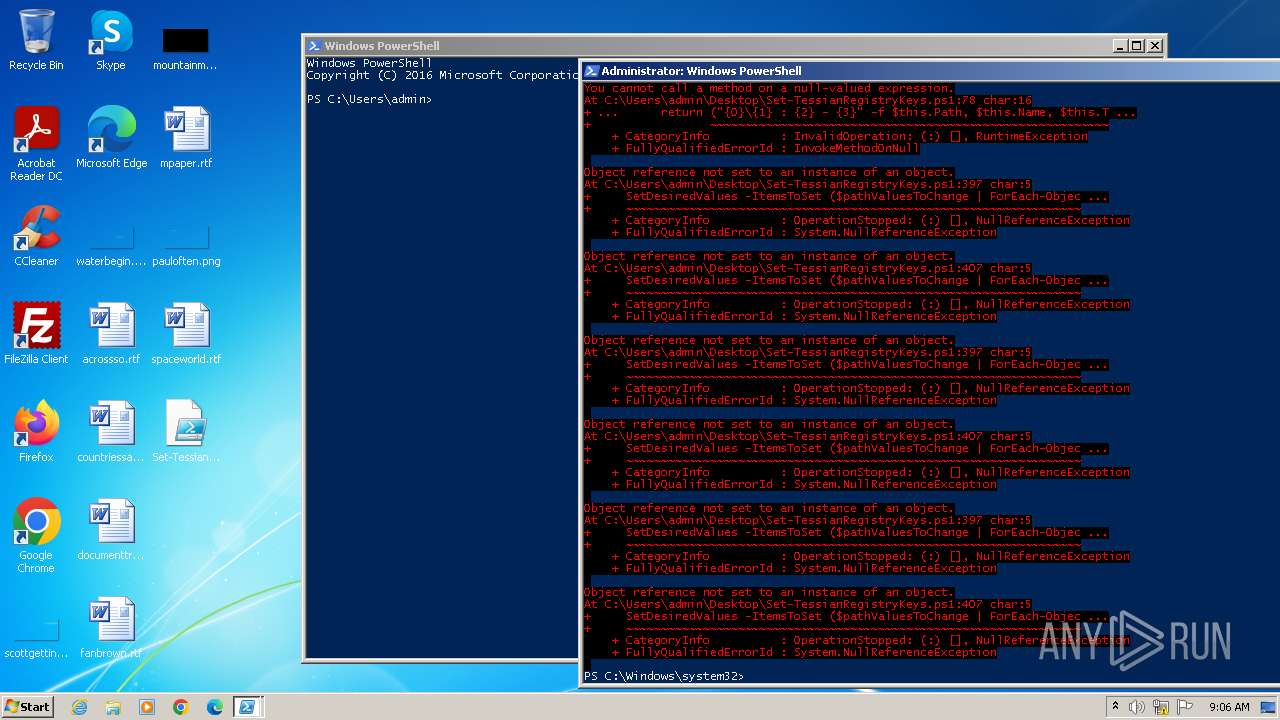
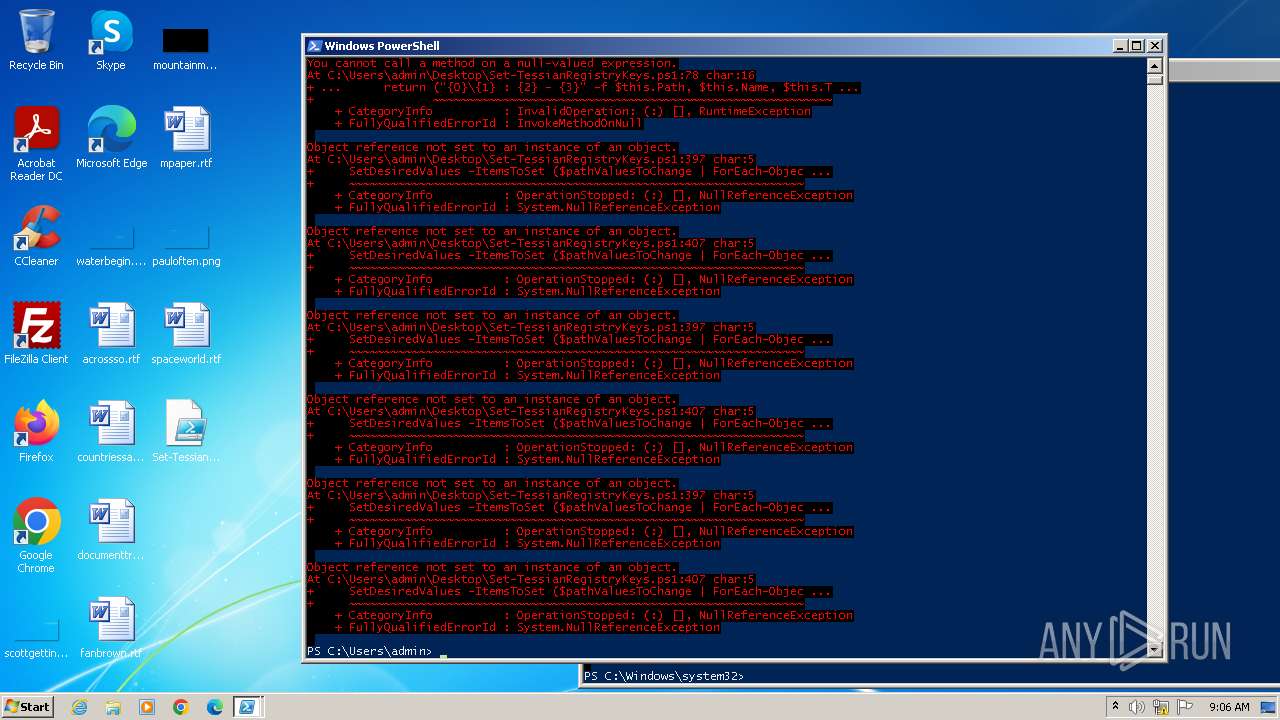
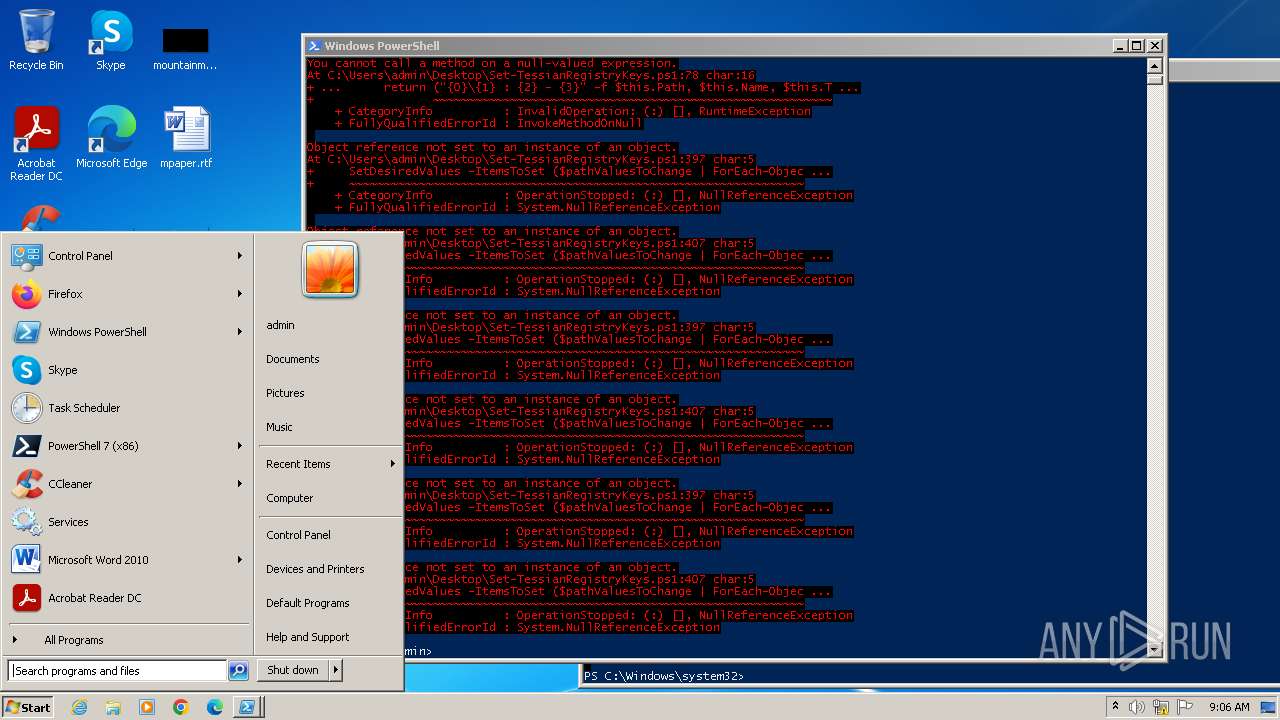
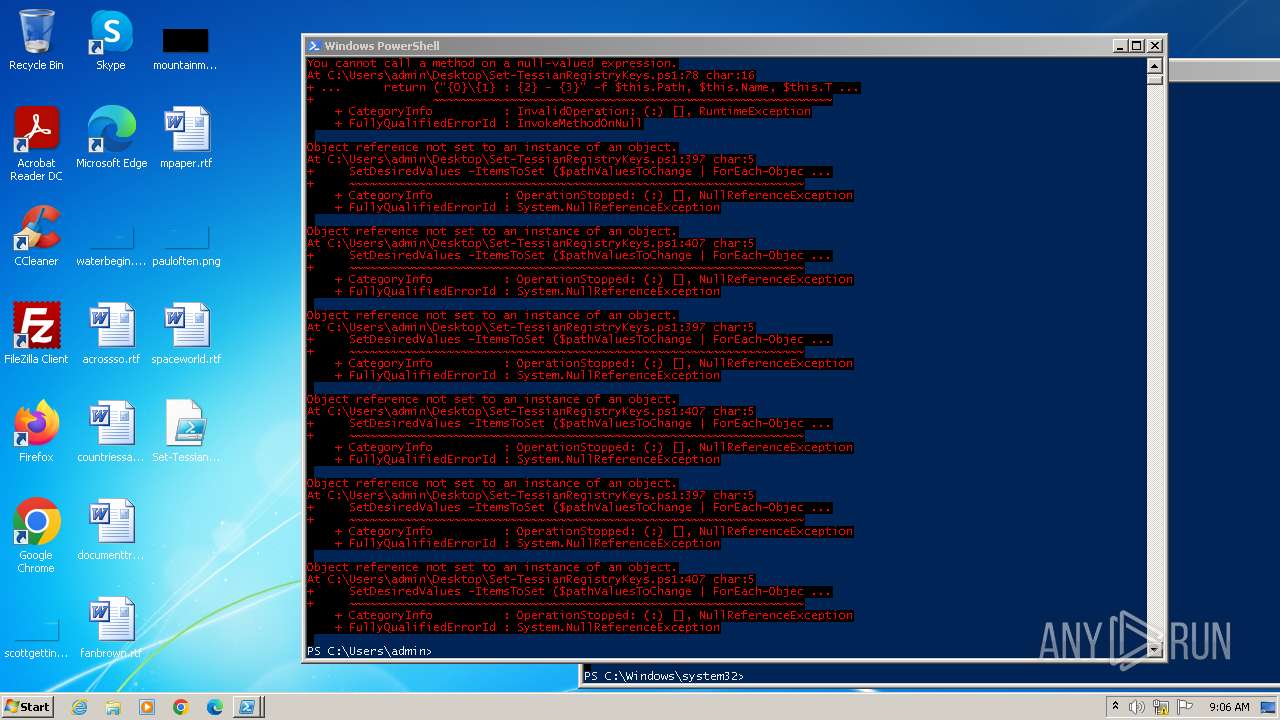
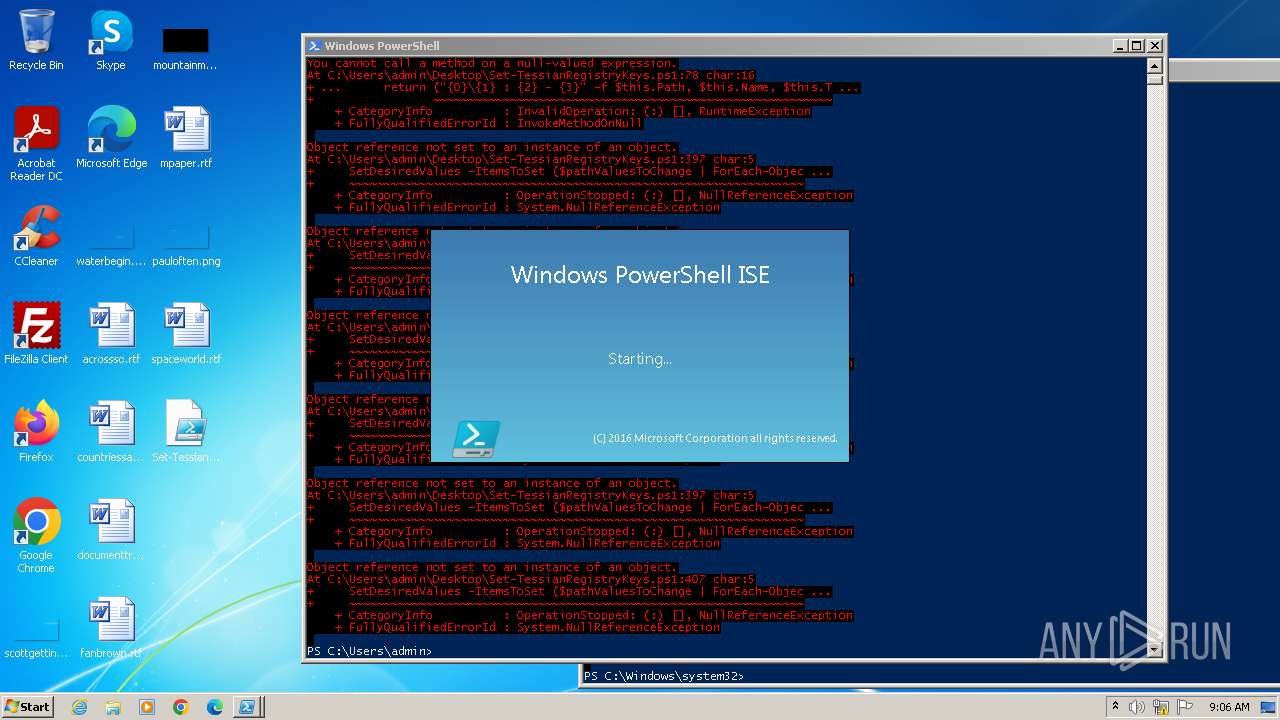
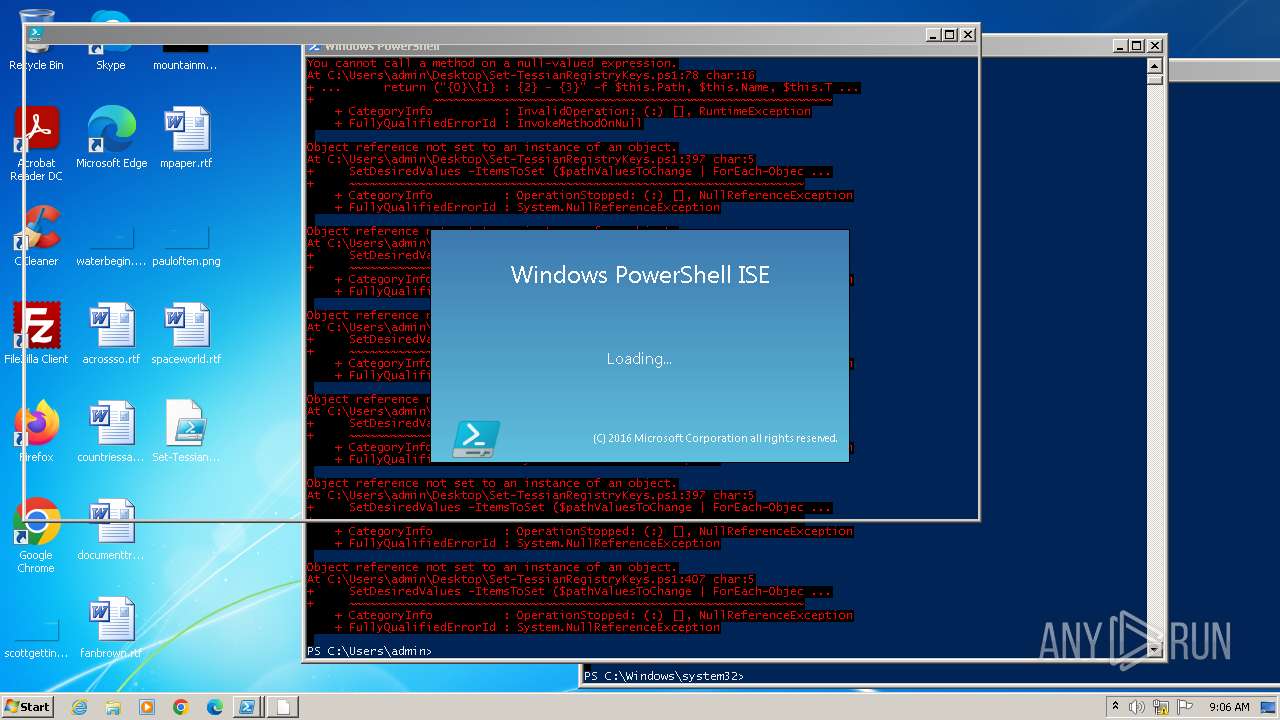
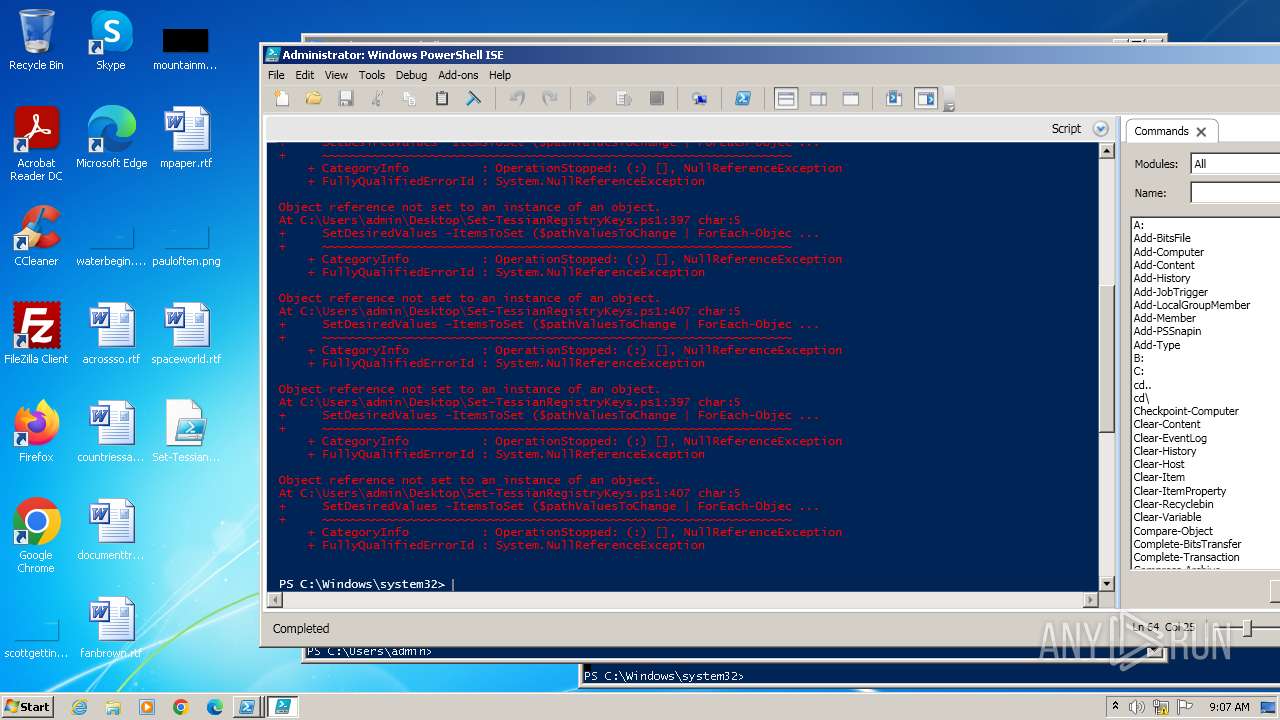
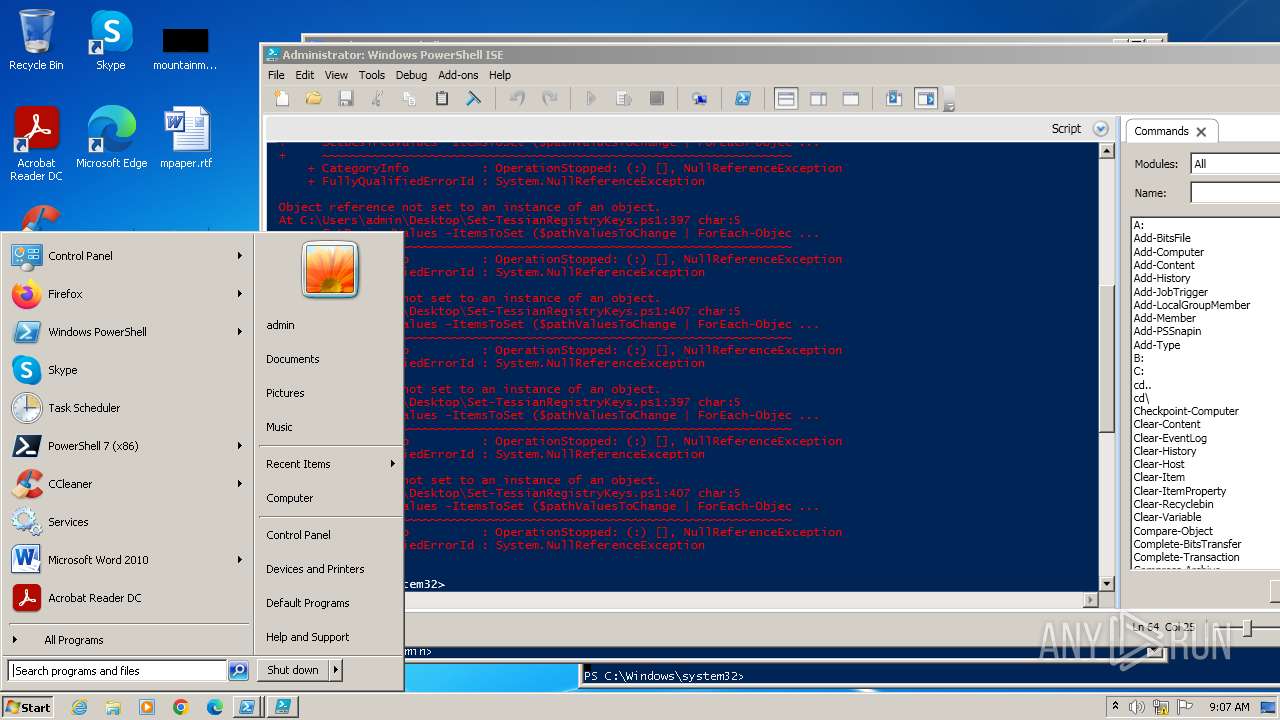
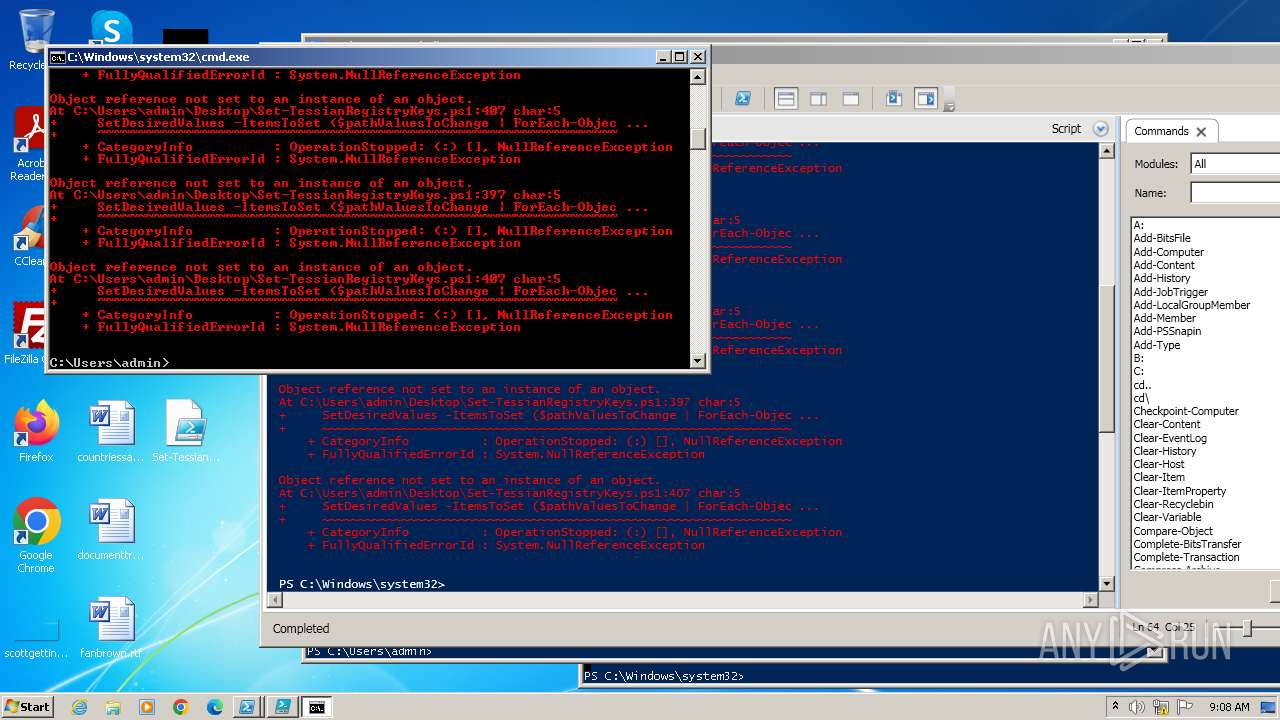
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3952)
- powershell.exe (PID: 328)
- powershell.exe (PID: 1844)
- powershell.exe (PID: 1660)
- powershell_ise.exe (PID: 2468)
- powershell.exe (PID: 2776)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 3952)
- powershell.exe (PID: 328)
- powershell.exe (PID: 1660)
- powershell.exe (PID: 1844)
- powershell_ise.exe (PID: 2468)
- powershell.exe (PID: 2776)
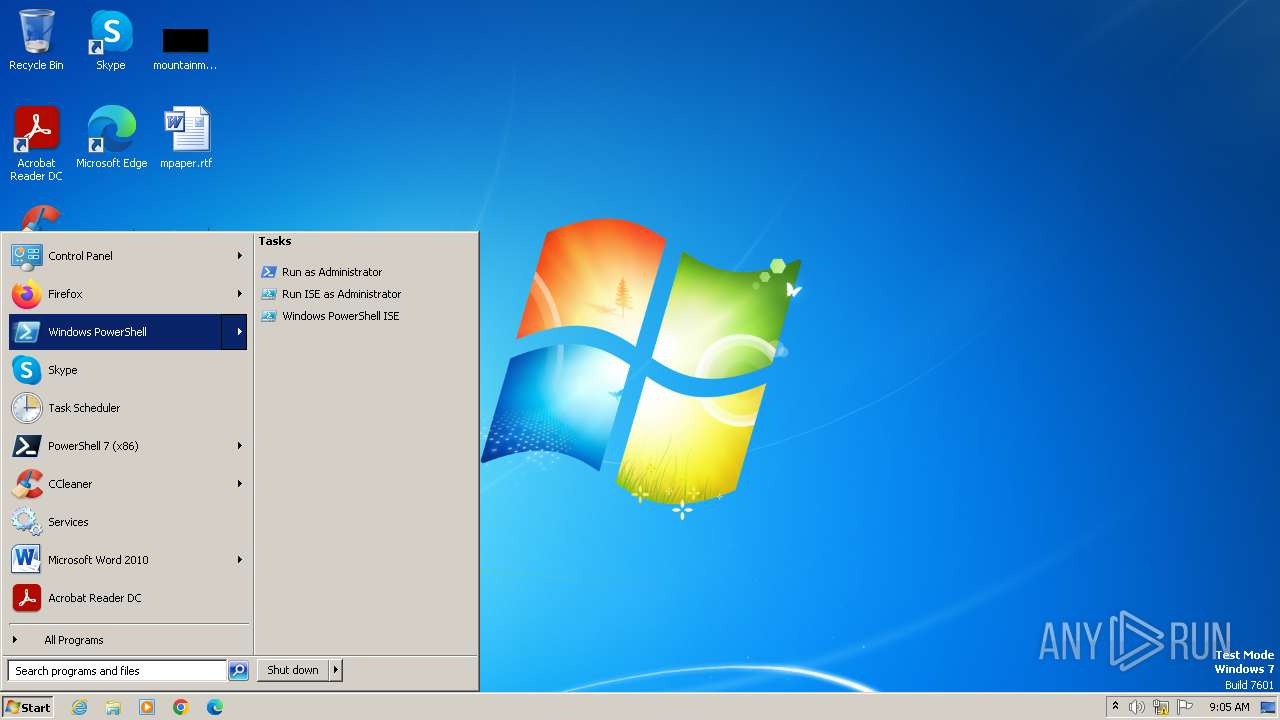
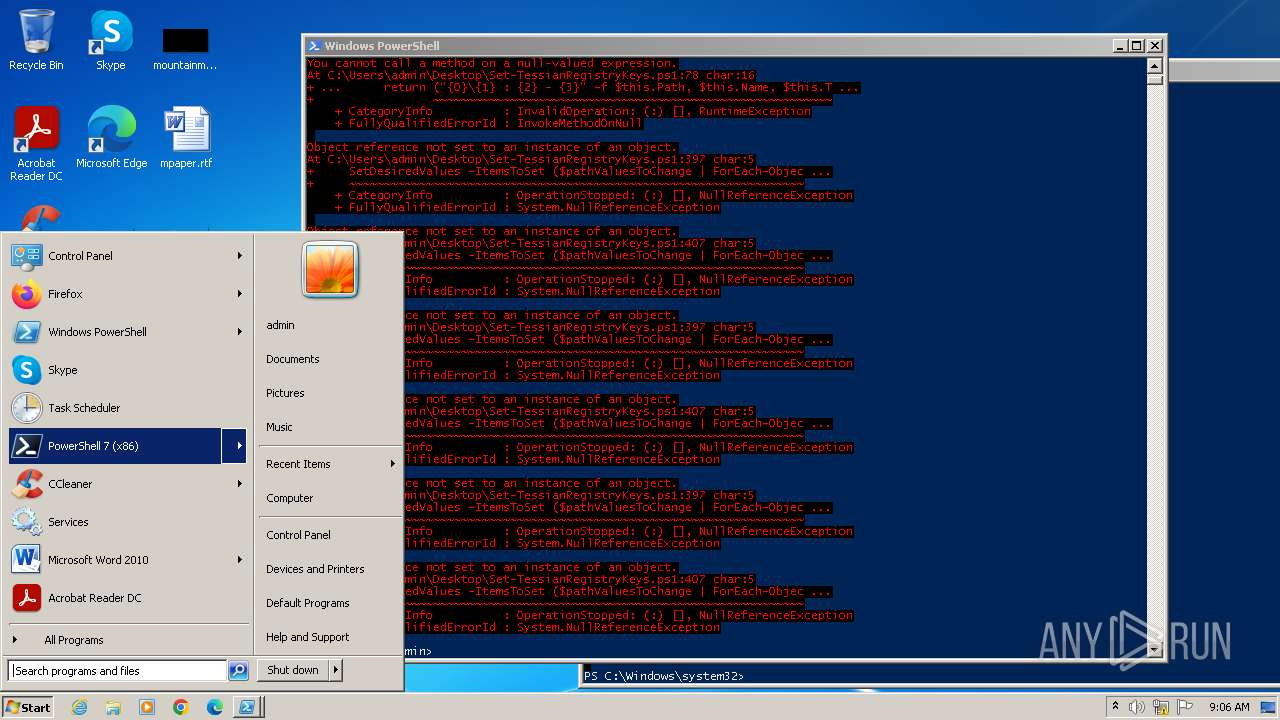
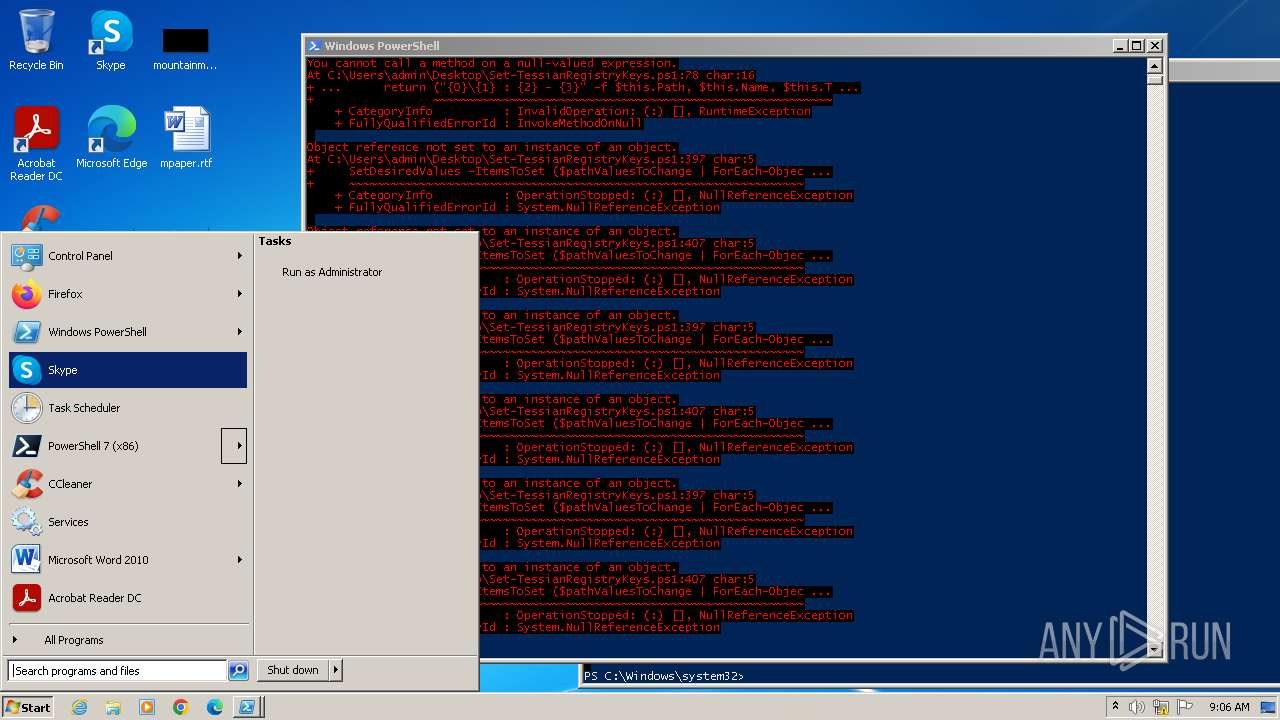
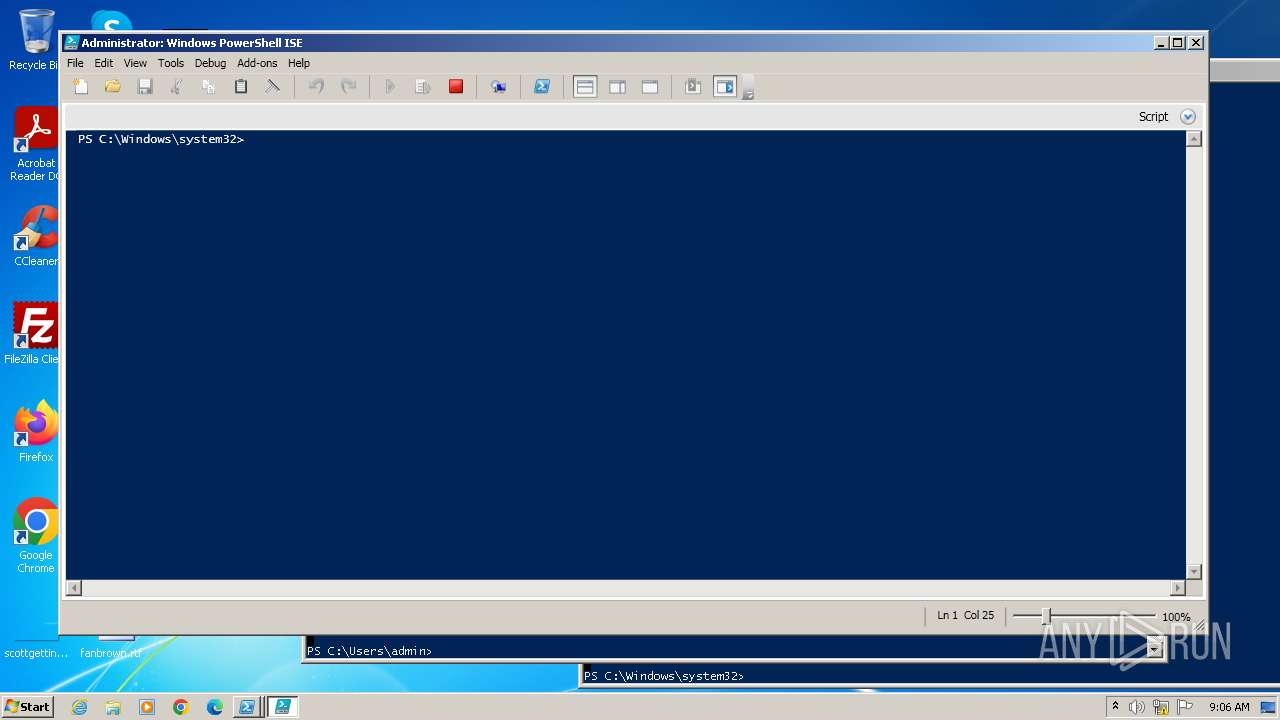
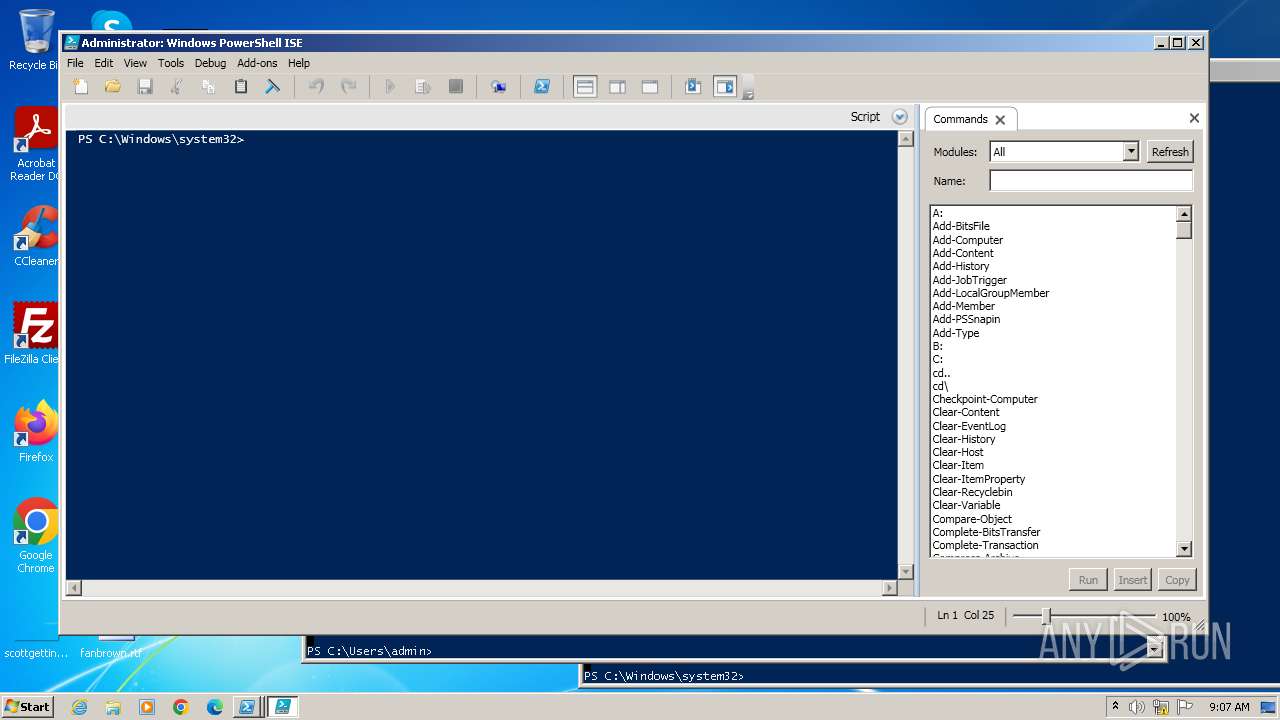
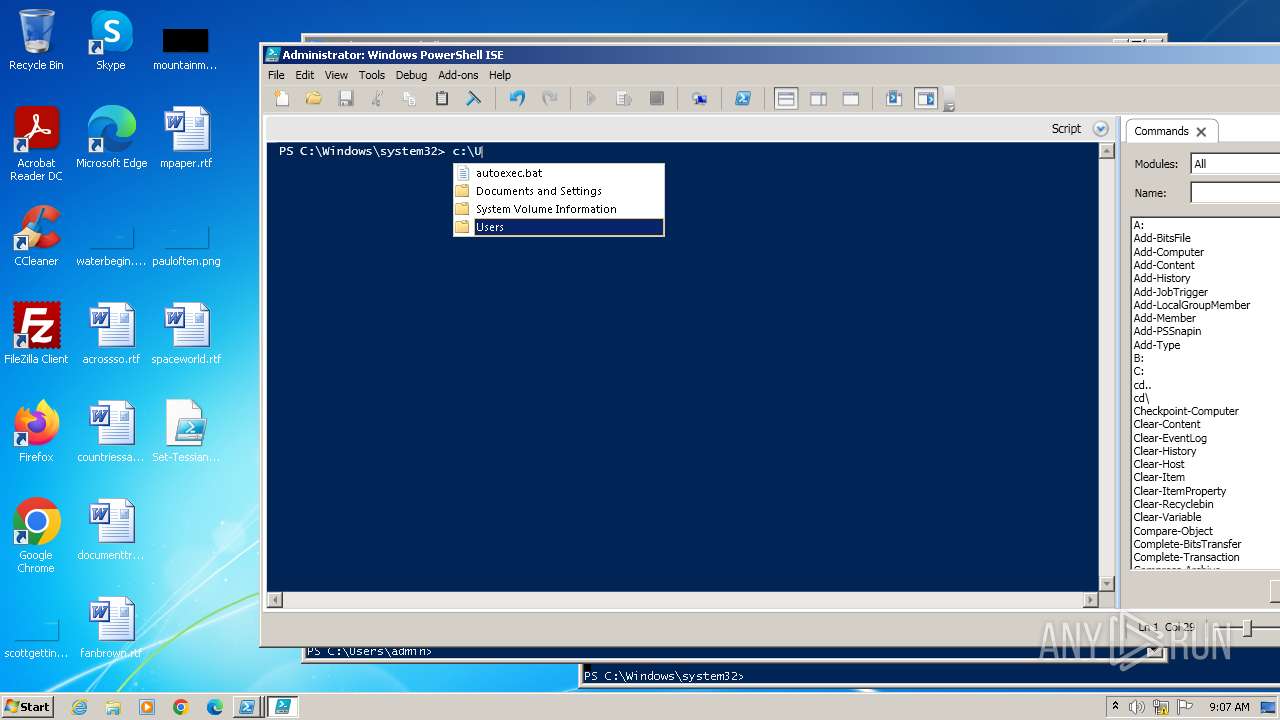
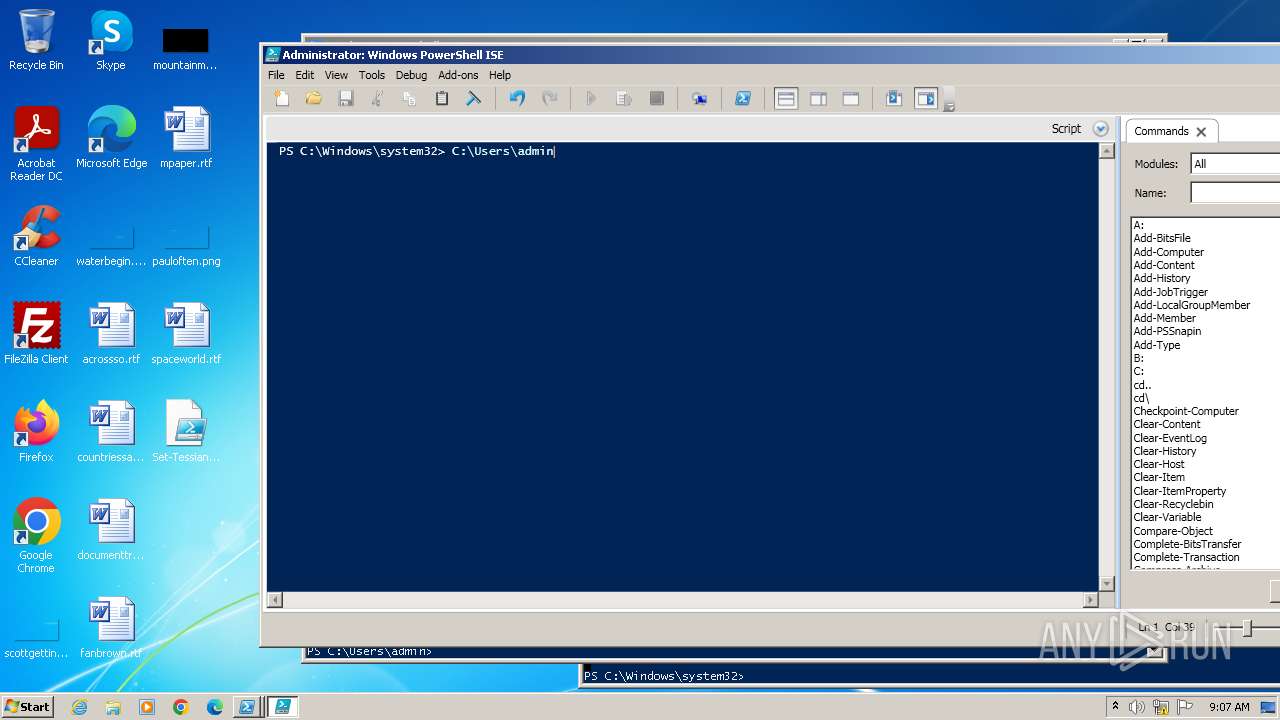
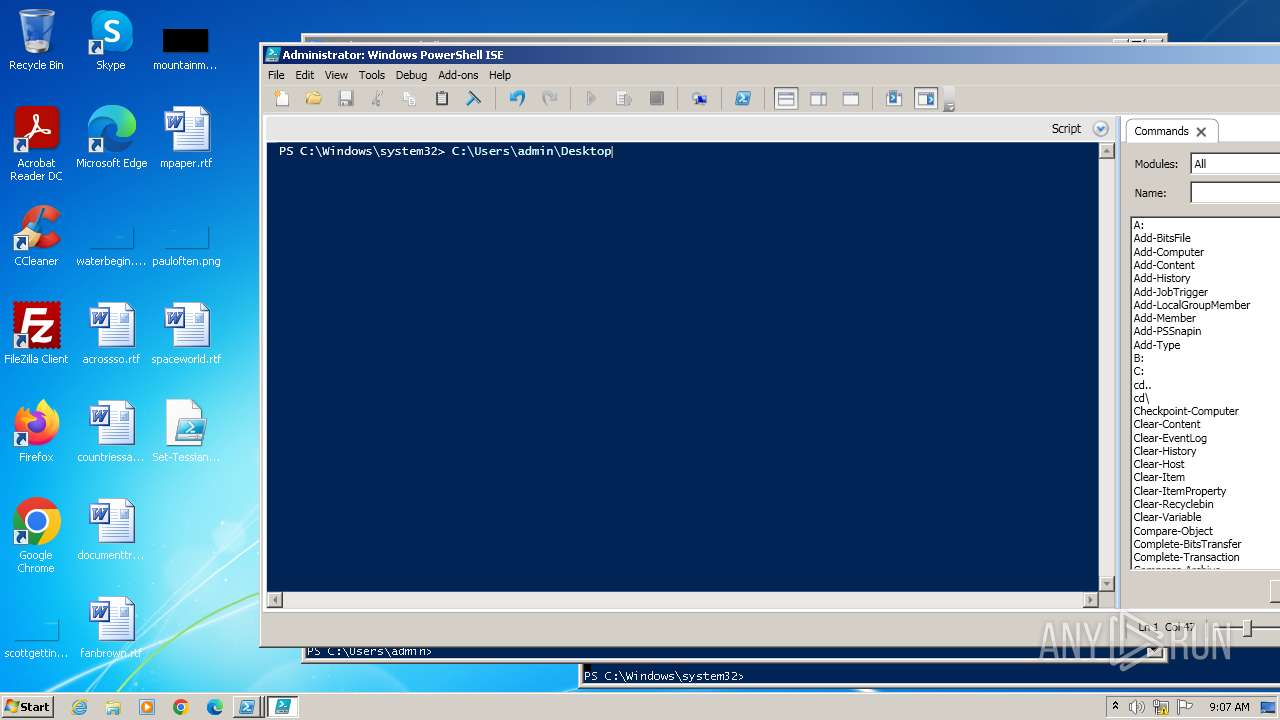
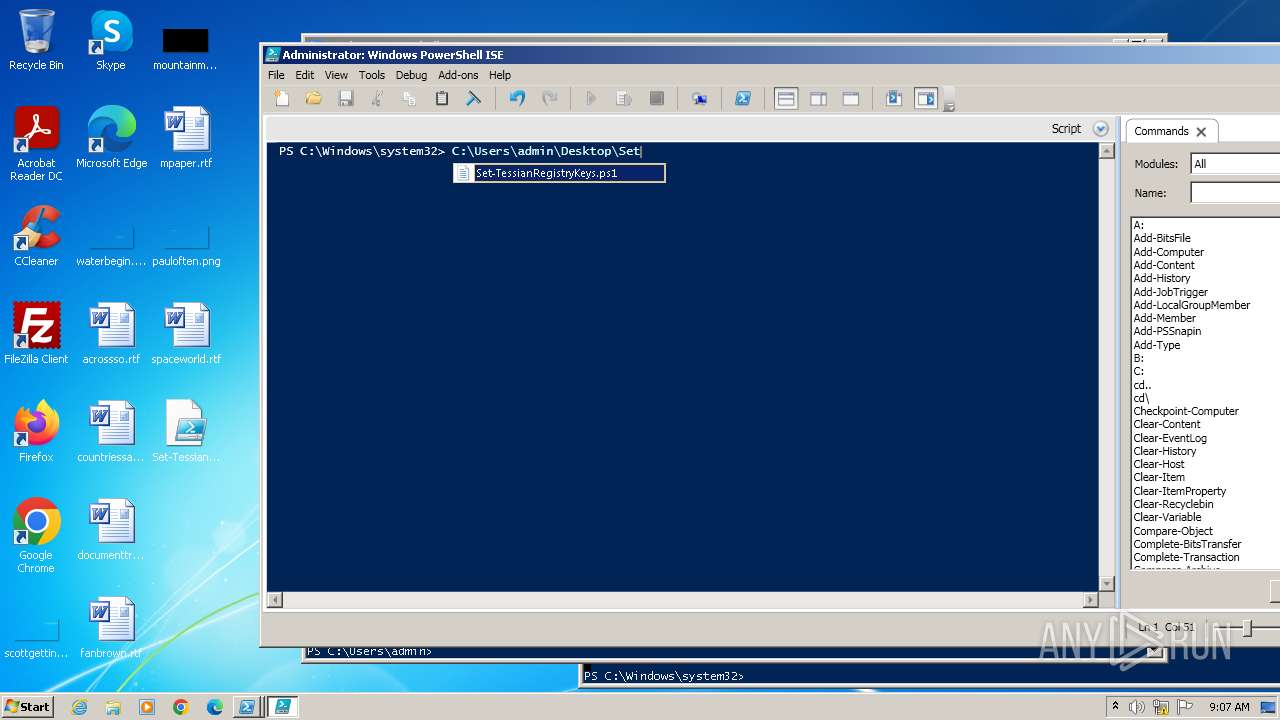
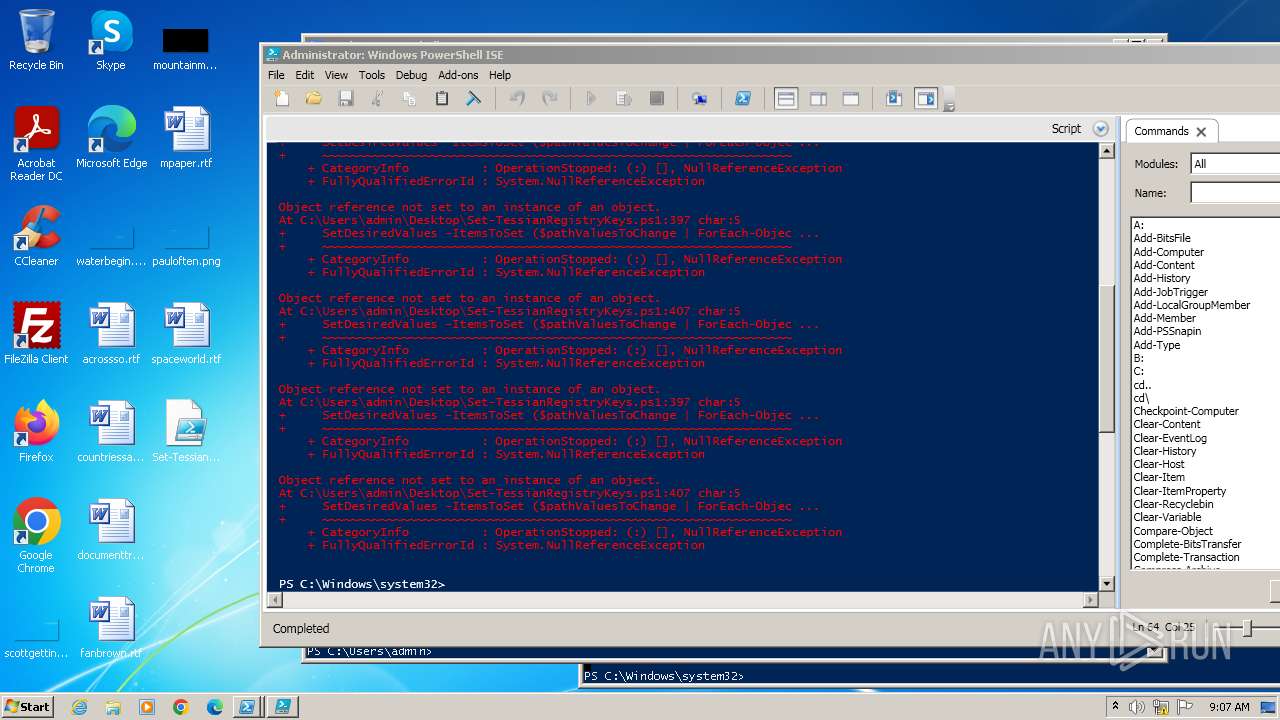
Manual execution by a user
- powershell.exe (PID: 328)
- powershell.exe (PID: 1660)
- powershell.exe (PID: 1844)
- powershell_ise.exe (PID: 2468)
- cmd.exe (PID: 2376)
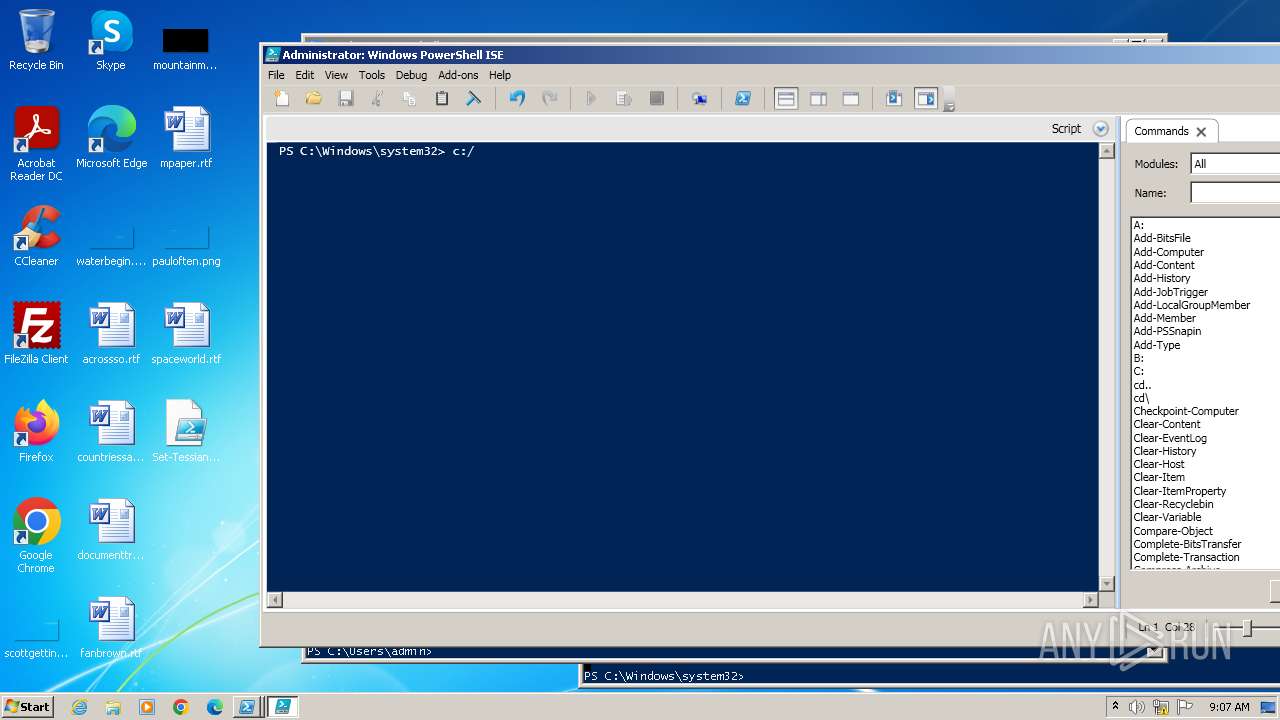
Checks current location (POWERSHELL)
- powershell.exe (PID: 328)
- powershell.exe (PID: 1660)
- powershell_ise.exe (PID: 2468)
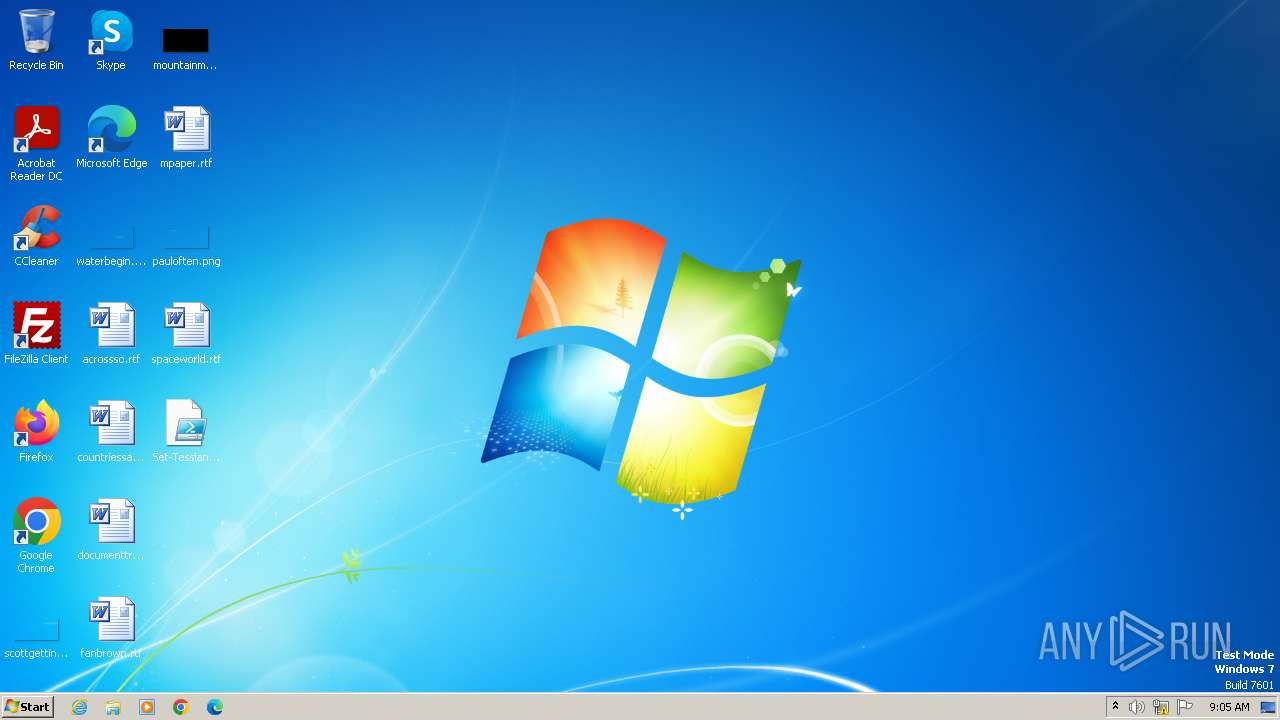
Creates files or folders in the user directory
- powershell_ise.exe (PID: 2468)
Reads security settings of Internet Explorer
- powershell_ise.exe (PID: 2468)
Create files in a temporary directory
- powershell_ise.exe (PID: 2468)
Reads the software policy settings
- powershell_ise.exe (PID: 2468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1660 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1844 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\Set-TessianRegistryKeys.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
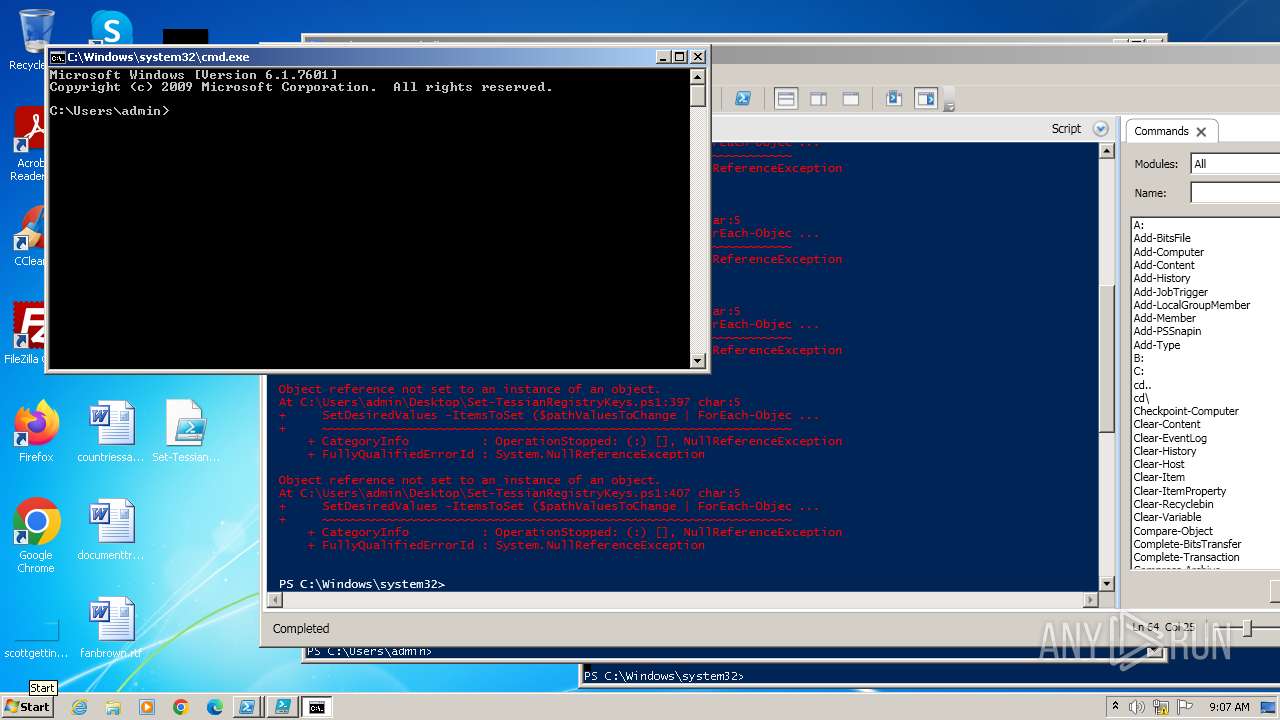
| 2376 | "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
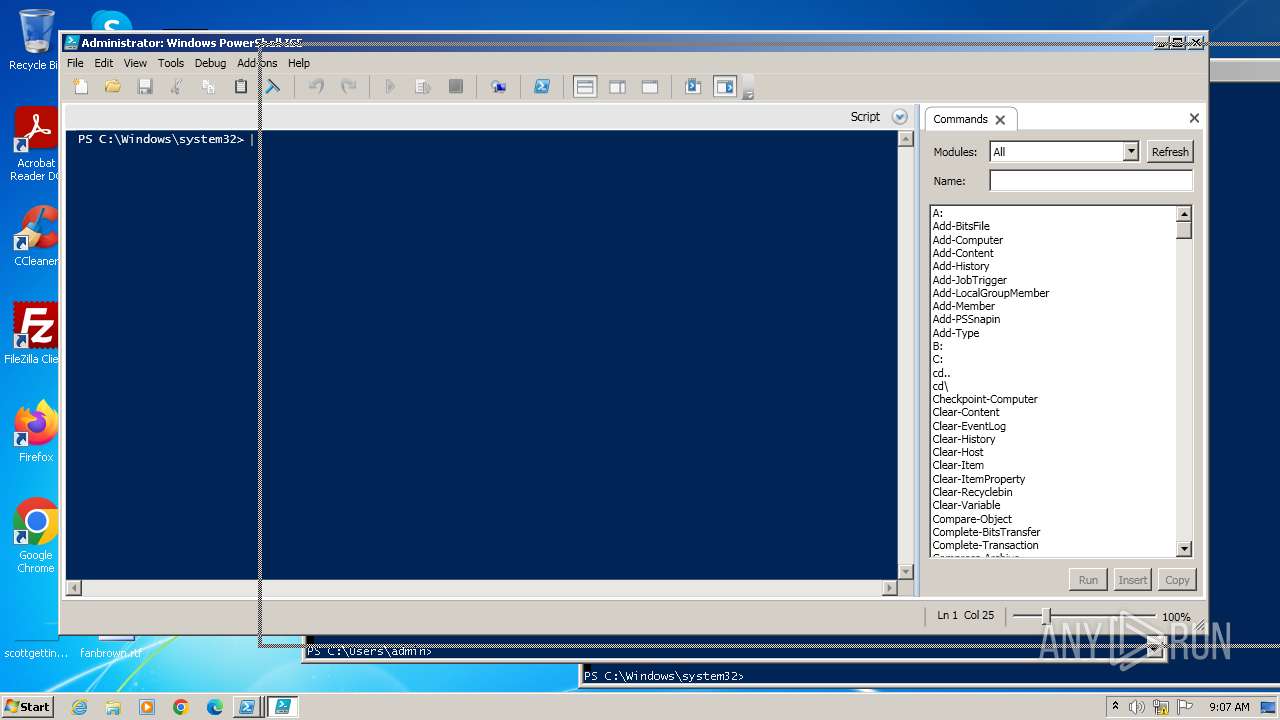
| 2468 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell ISE Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2776 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\Set-TessianRegistryKeys.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3952 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" C:\Users\admin\Desktop\Set-TessianRegistryKeys.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
26 103
Read events
25 760
Write events
340
Delete events
3
Modification events
| (PID) Process: | (3952) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3952) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3952) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3952) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3952) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (328) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (328) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (328) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (328) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (328) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
30
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1660 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\37227TXATTP4QUKUP5G7.temp | binary | |
MD5:DEA0DE52DFF2E328551A6BB67224CBDF | SHA256:5CF19C8374CF57F136F1E098E2FBC36D50B68B98FAE0A0D173BBA9634C77C9B7 | |||
| 1660 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:DEA0DE52DFF2E328551A6BB67224CBDF | SHA256:5CF19C8374CF57F136F1E098E2FBC36D50B68B98FAE0A0D173BBA9634C77C9B7 | |||
| 3952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5HJG4DL8WKS9VLMLYZII.temp | binary | |
MD5:7B9FC8EDA8DFC3E128623081DB20030C | SHA256:81FB596D7C5C7C9264E891A660D7B00455DD9AC326B9B53816B1F2FE38F4FAED | |||
| 328 | powershell.exe | C:\Users\admin\AppData\Local\Temp\bpdnx04t.x12.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3952 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 328 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:278981E2D5F46825DF4292301668E251 | SHA256:DC96784C93BBD68CB03E8C915572ACBE35098E241028164BB71B459D36D114AE | |||
| 3952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:7B9FC8EDA8DFC3E128623081DB20030C | SHA256:81FB596D7C5C7C9264E891A660D7B00455DD9AC326B9B53816B1F2FE38F4FAED | |||
| 328 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF107dbd.TMP | binary | |
MD5:7B9FC8EDA8DFC3E128623081DB20030C | SHA256:81FB596D7C5C7C9264E891A660D7B00455DD9AC326B9B53816B1F2FE38F4FAED | |||
| 328 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WVDMT0WWKCJ55JOQZ8BQ.temp | binary | |
MD5:278981E2D5F46825DF4292301668E251 | SHA256:DC96784C93BBD68CB03E8C915572ACBE35098E241028164BB71B459D36D114AE | |||
| 3952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF103ceb.TMP | binary | |
MD5:0268C3470C936E6FBAC2945B9E1C2099 | SHA256:DF2AF58E8879B48826D8A418ED3B02CC8D484BCFC231C5B7A11BD153ED3998E9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |