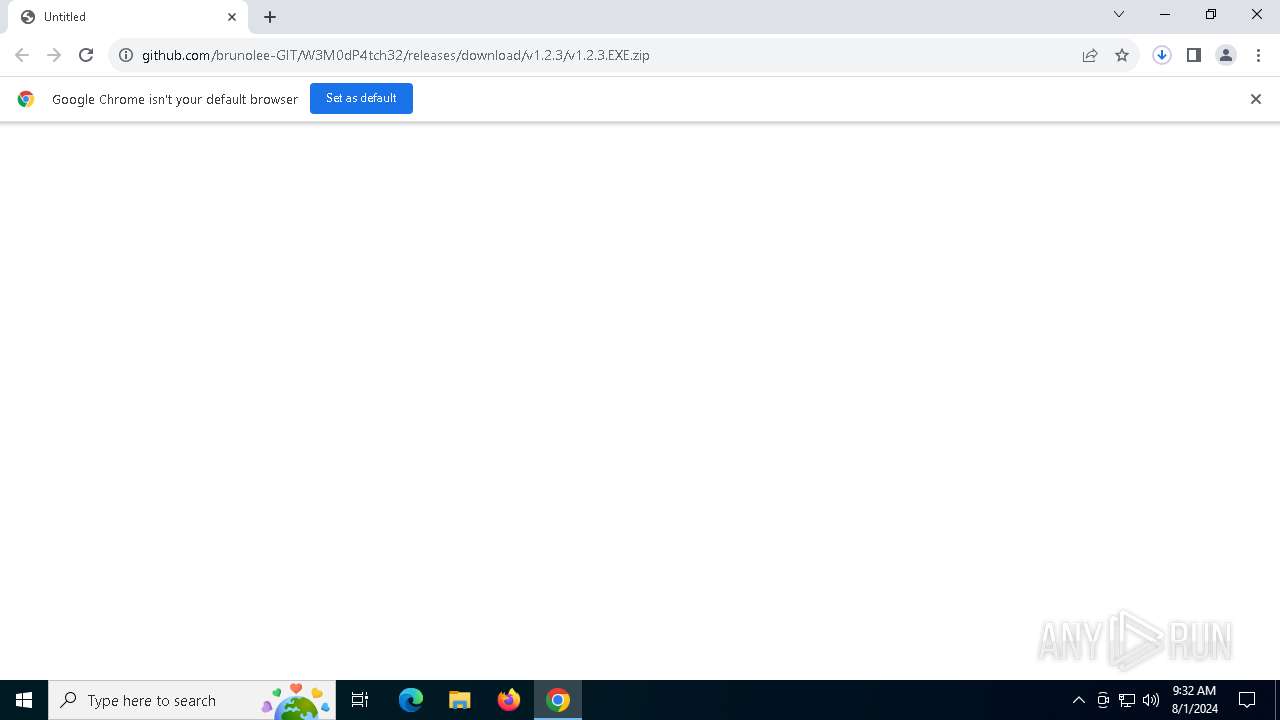
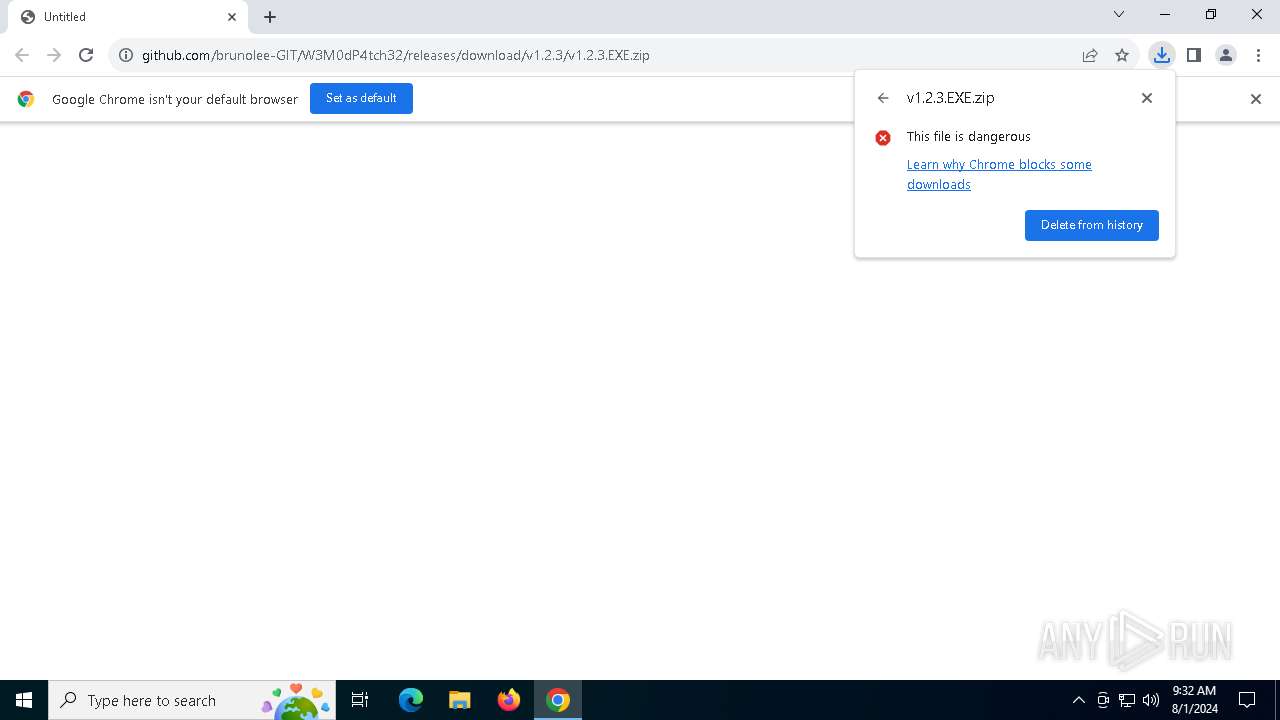
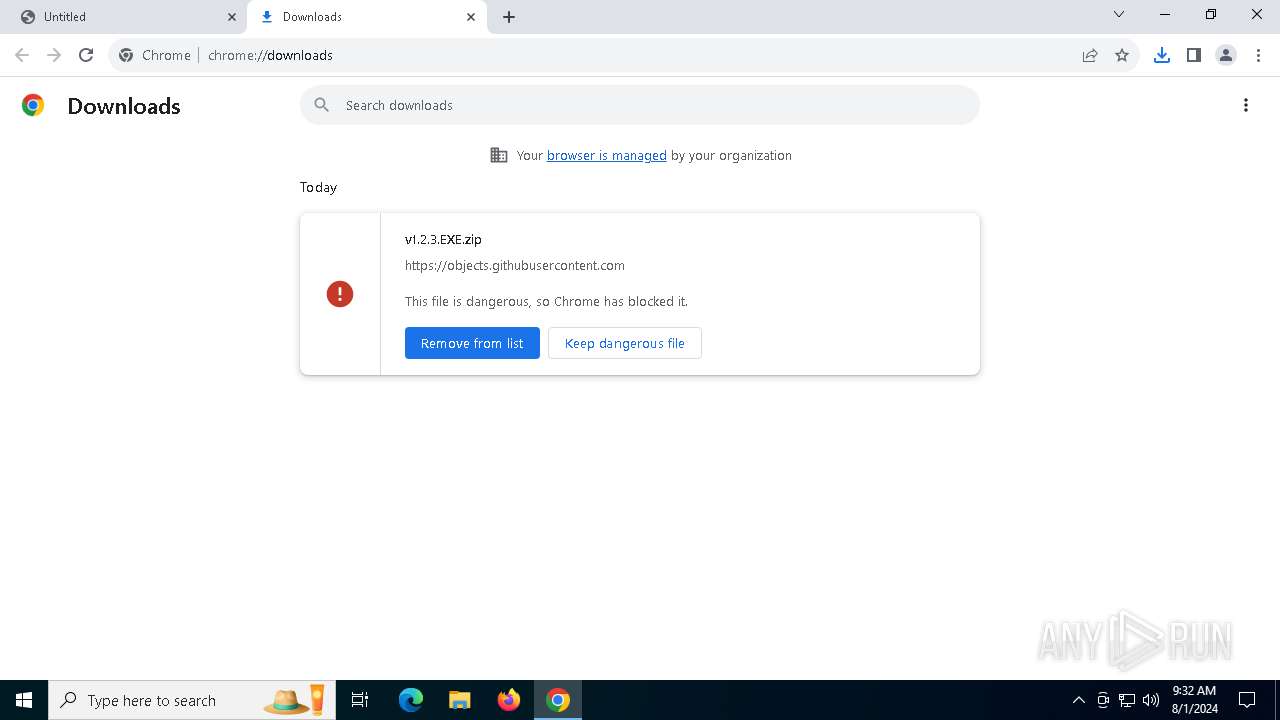
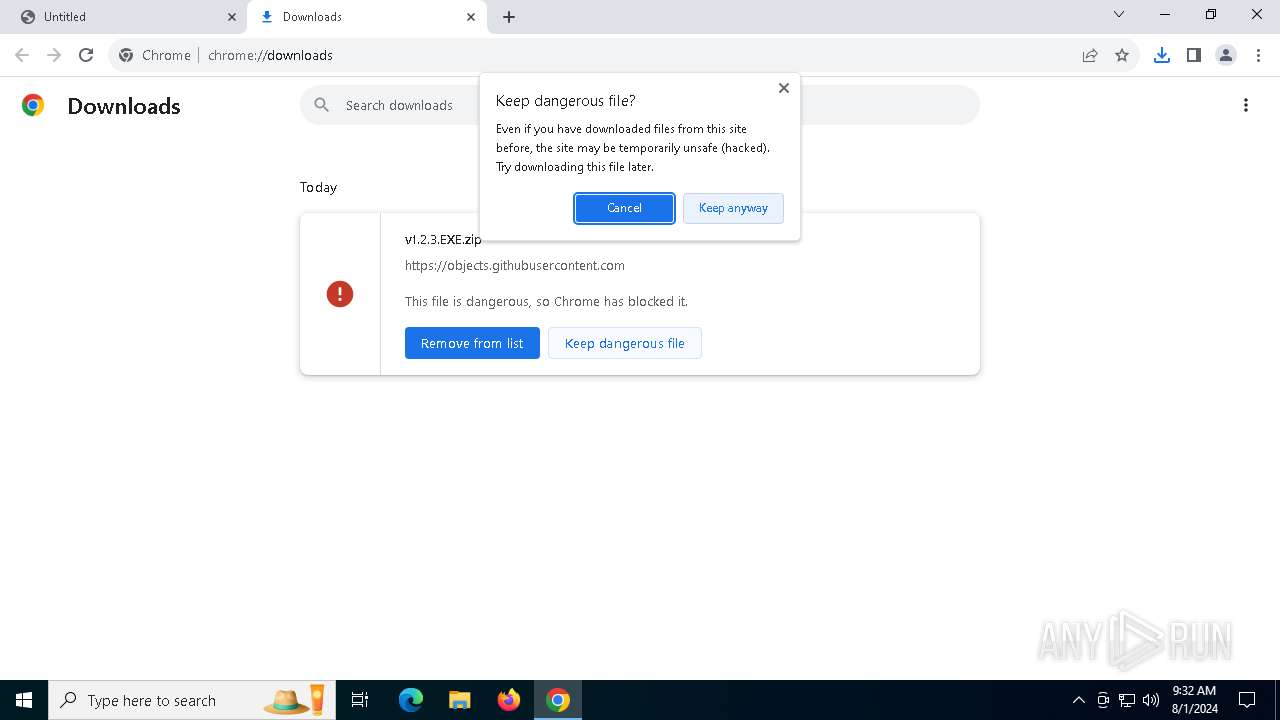
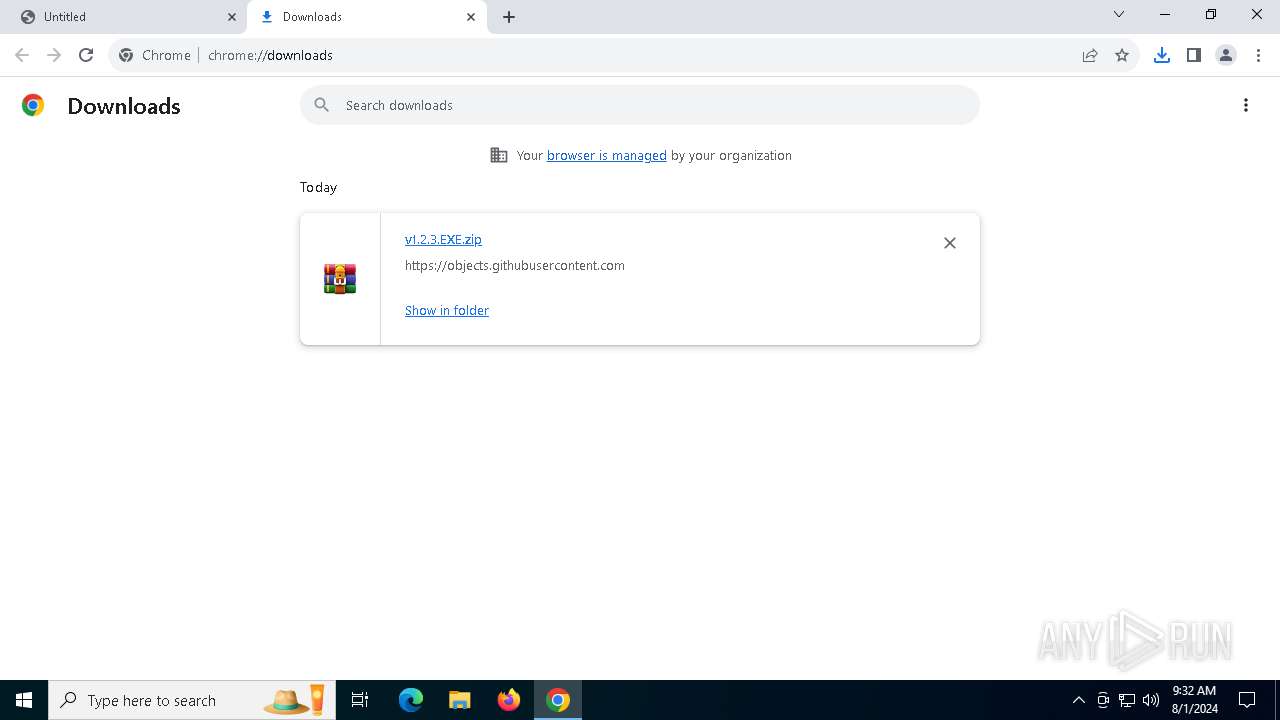
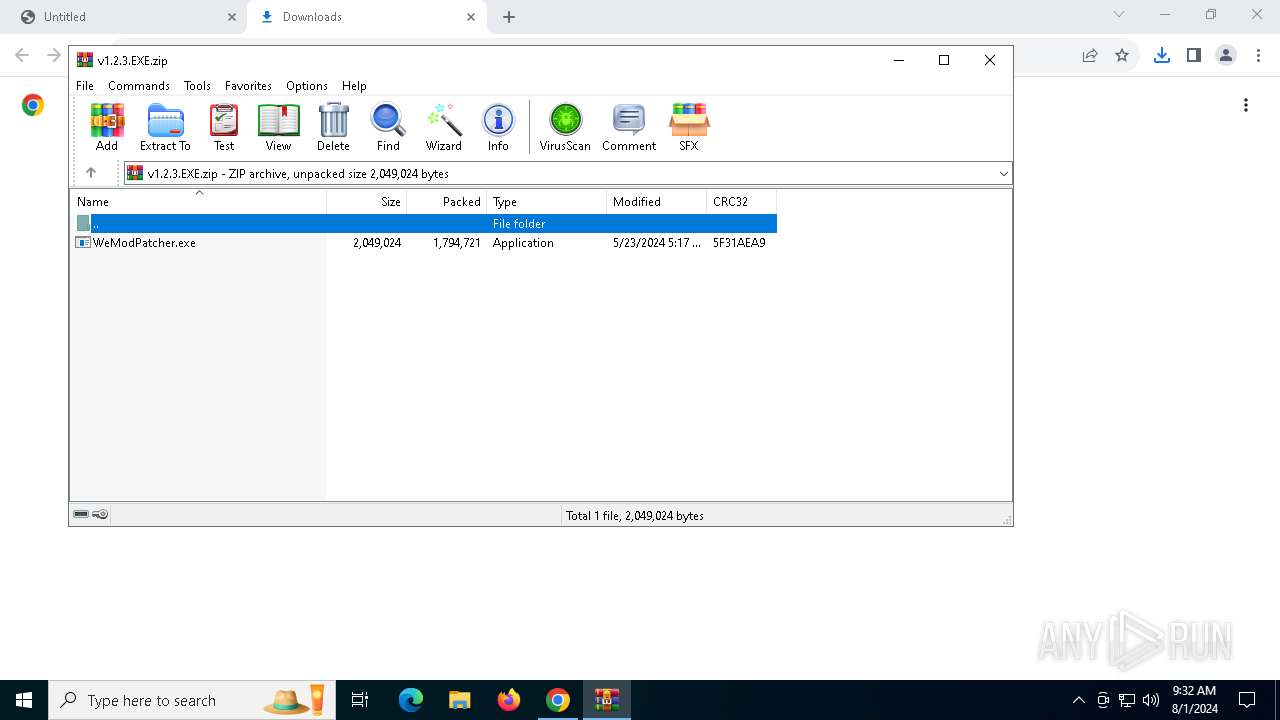
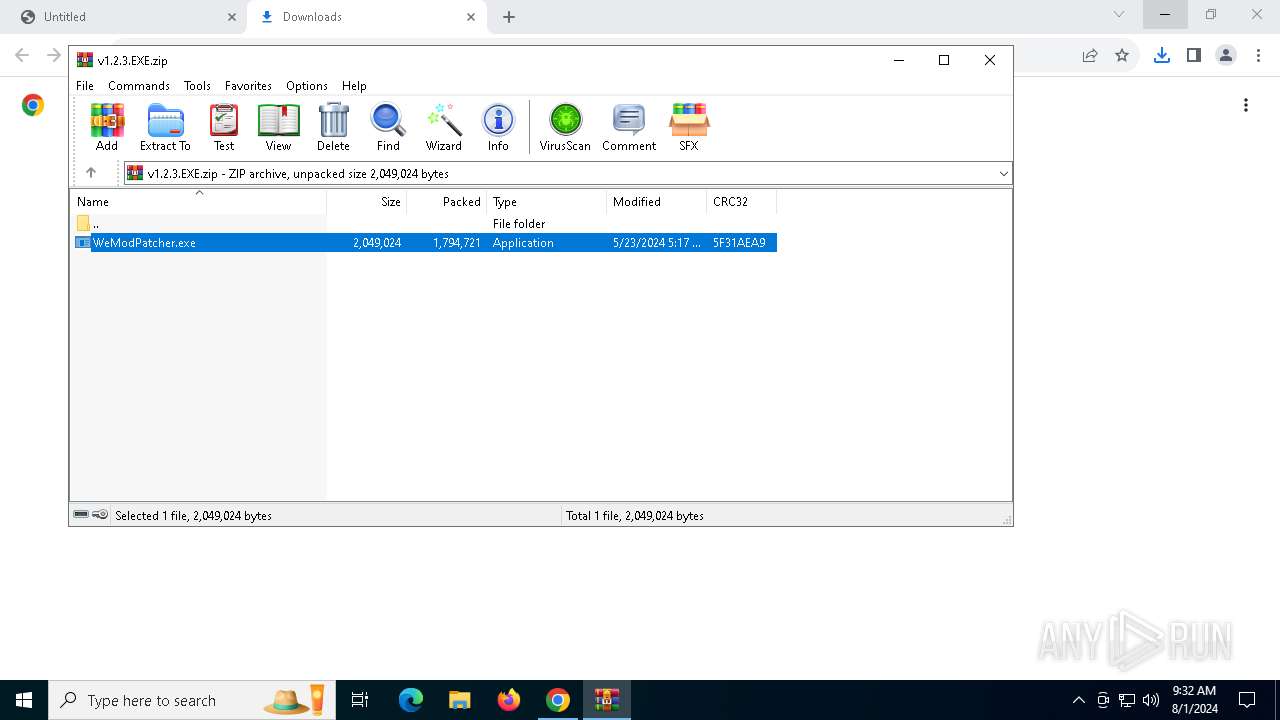
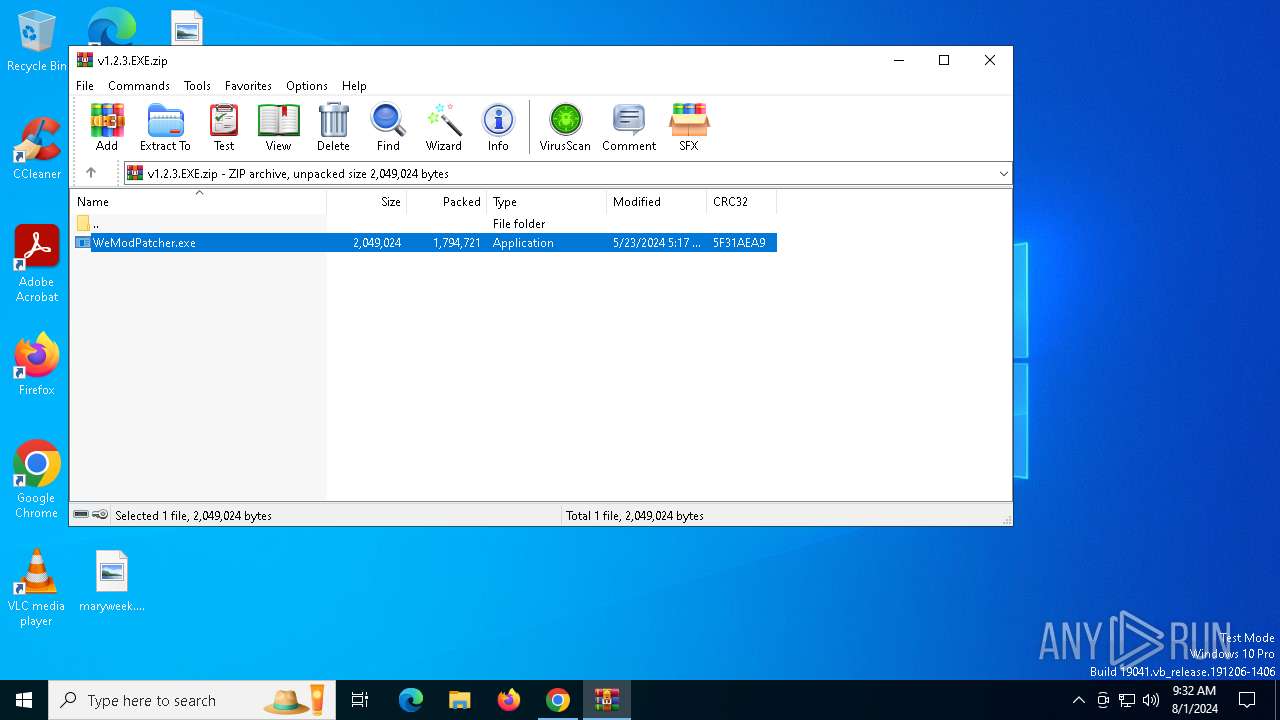
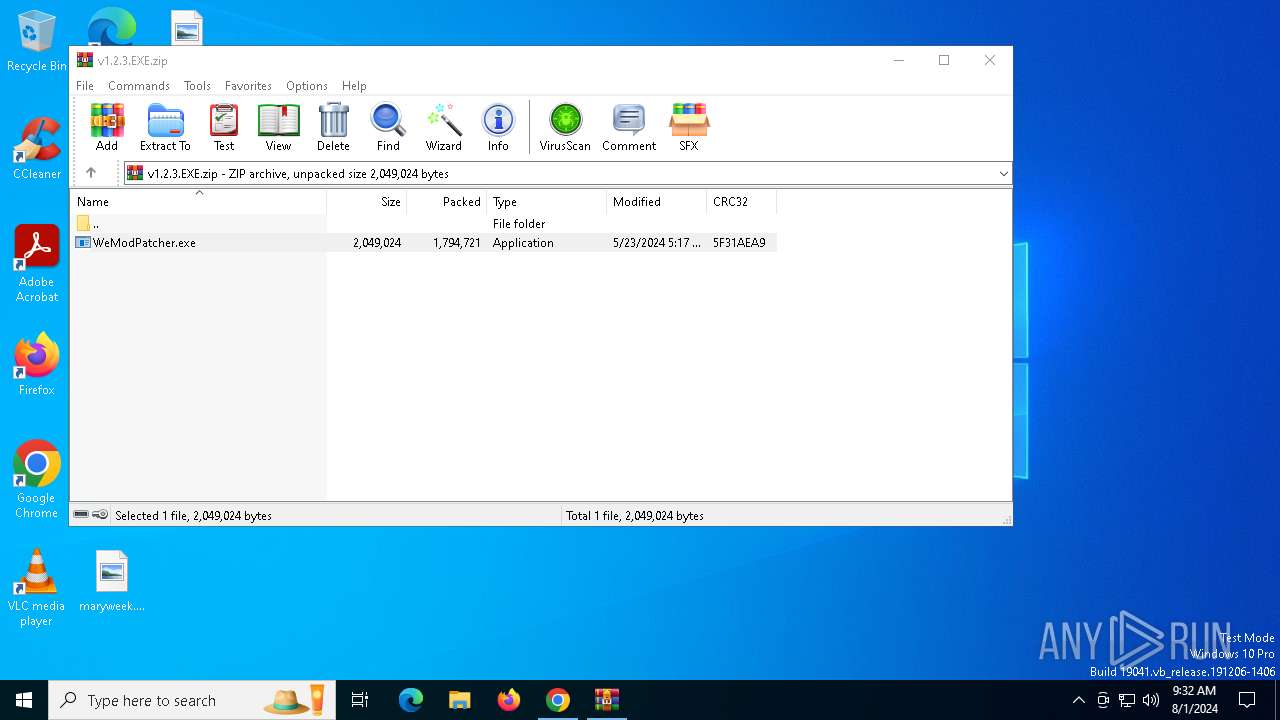
| URL: | https://github.com/brunolee-GIT/W3M0dP4tch32/releases/download/v1.2.3/v1.2.3.EXE.zip |
| Full analysis: | https://app.any.run/tasks/f1bb3c86-1140-4105-9fa5-444f7a6aefa4 |
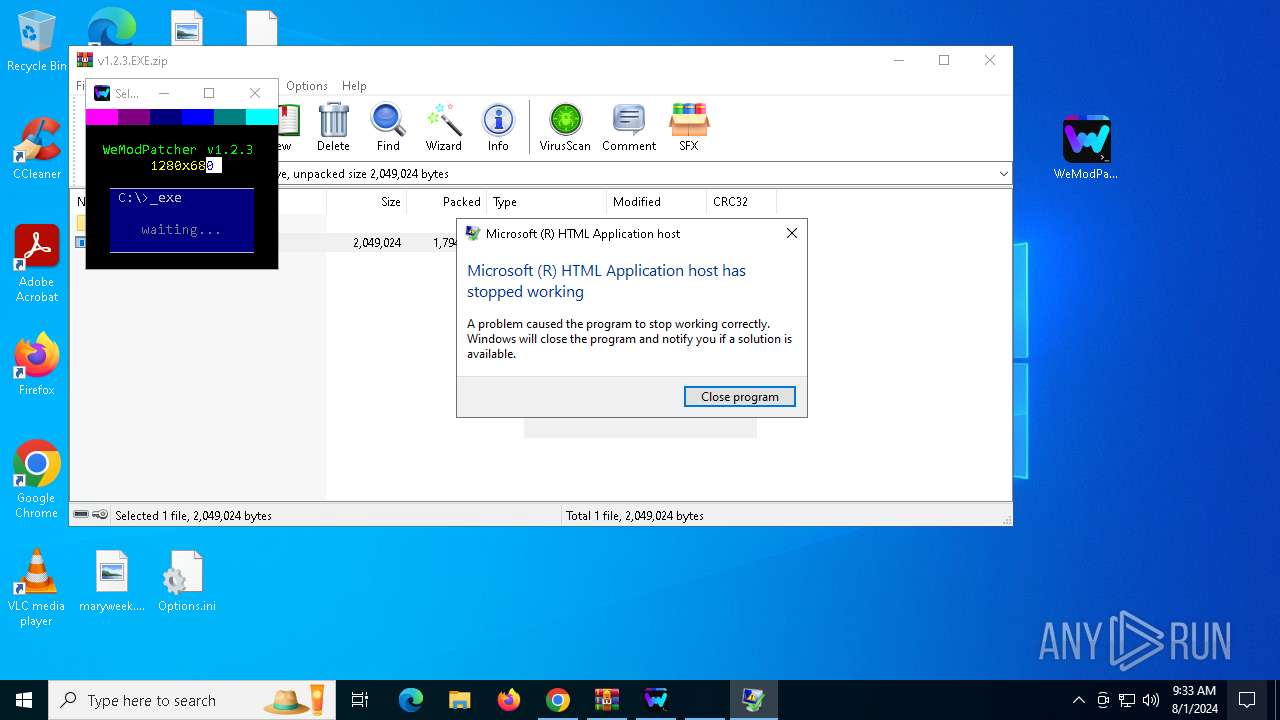
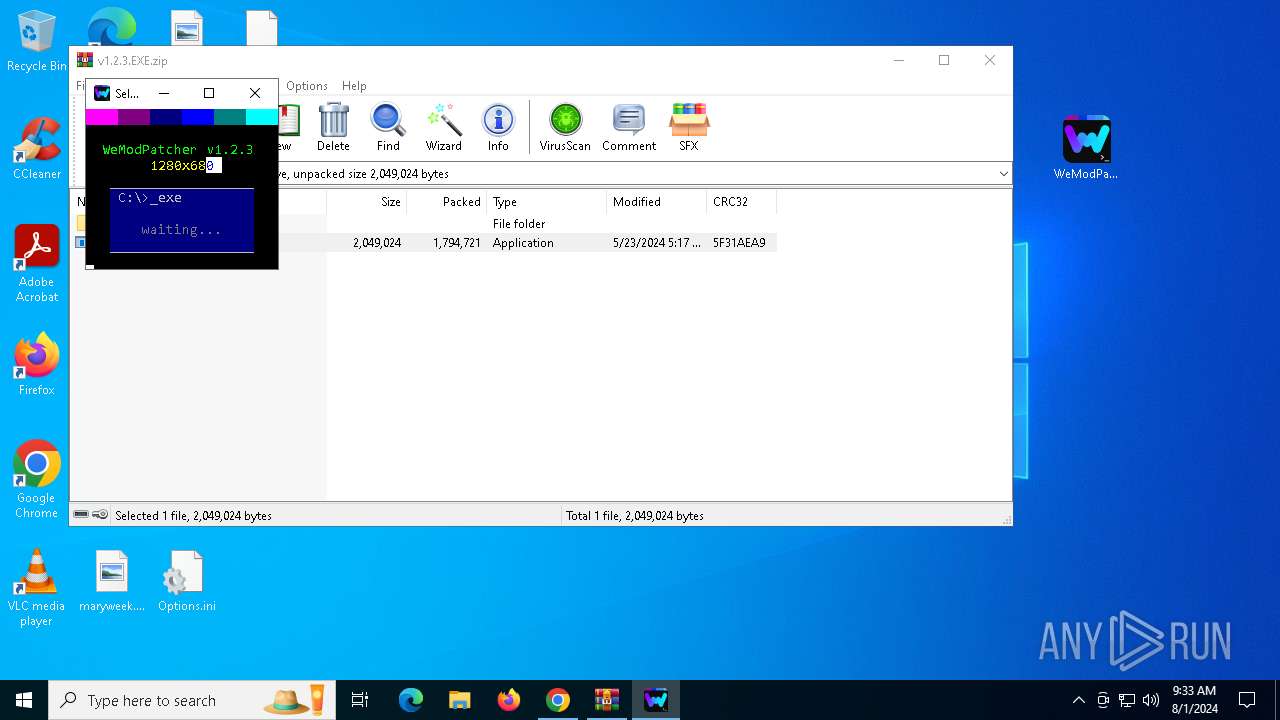
| Verdict: | Malicious activity |
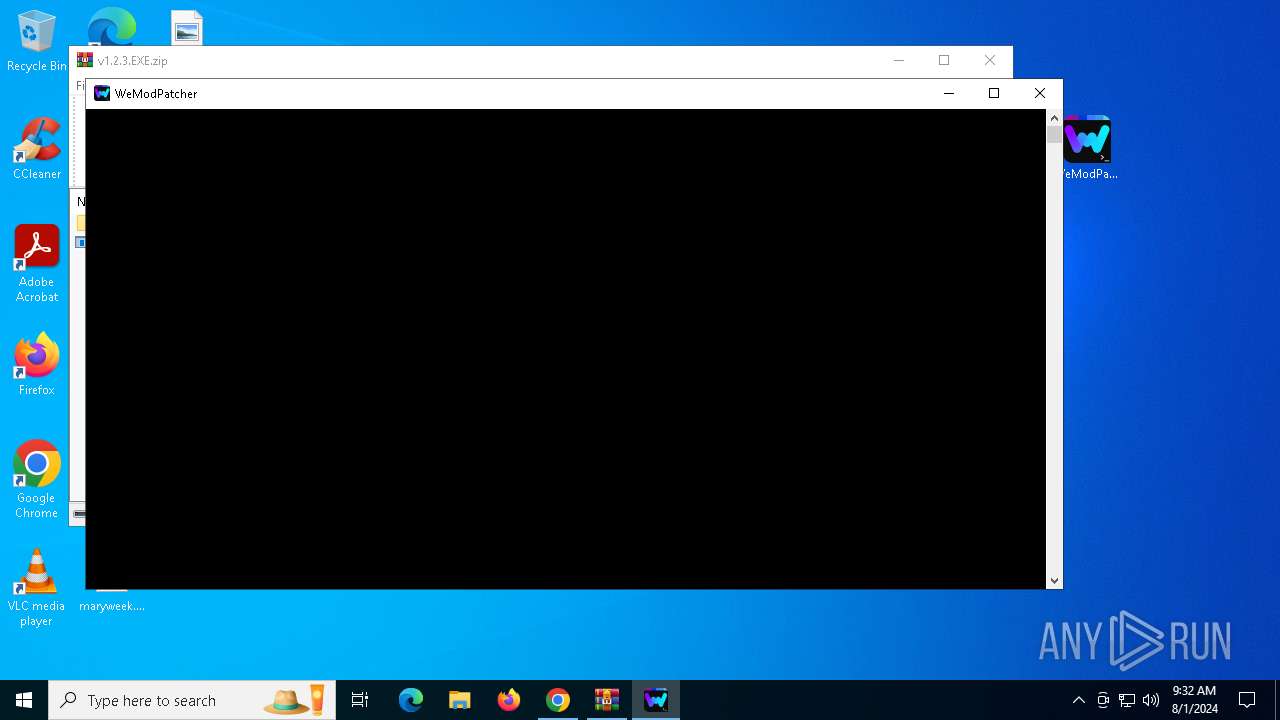
| Analysis date: | August 01, 2024, 09:32:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
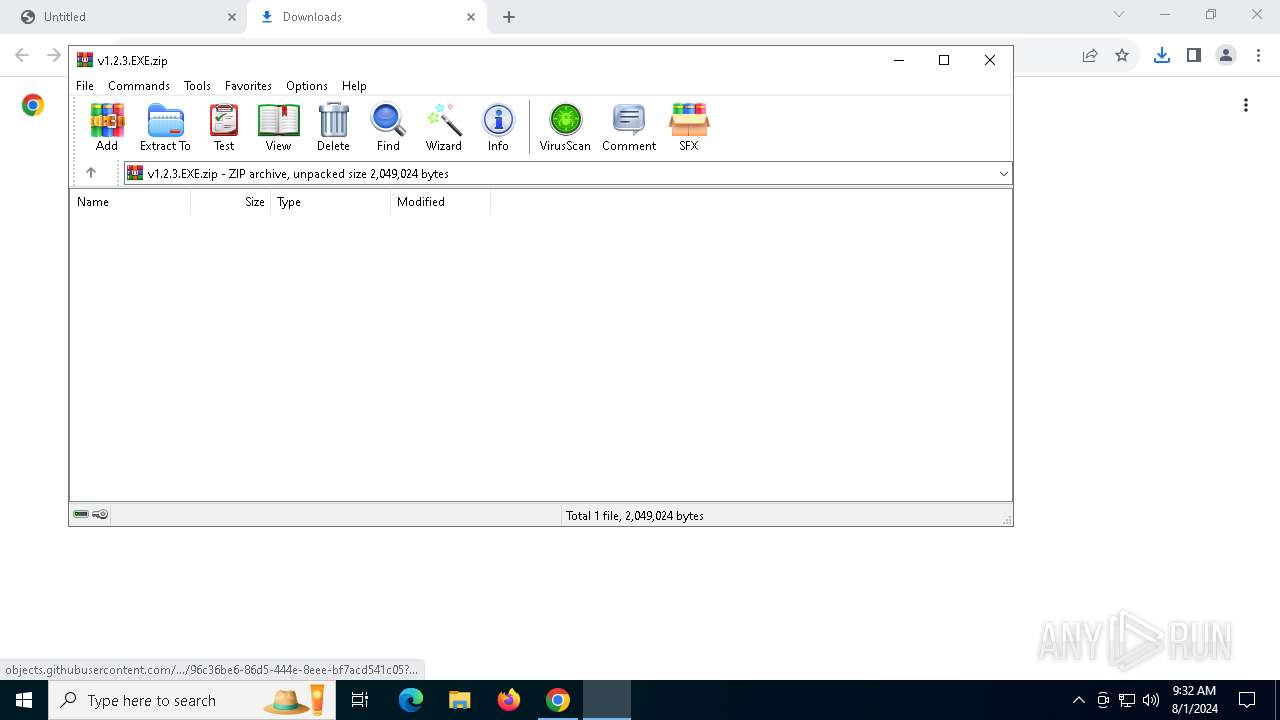
| MD5: | 416DE77CCEB2EBE16098F02C80938B87 |
| SHA1: | 681658815F9FFC940BF3B490672D54FF8E3039AF |
| SHA256: | 005422586AB82DC195E507F6E8D1ED6710B239DEDD126EDBD4C79B0F1B460520 |
| SSDEEP: | 3:N8tEd3FJlyWkRRG+0kCmmLb0YV:2uxYRGXspYV |
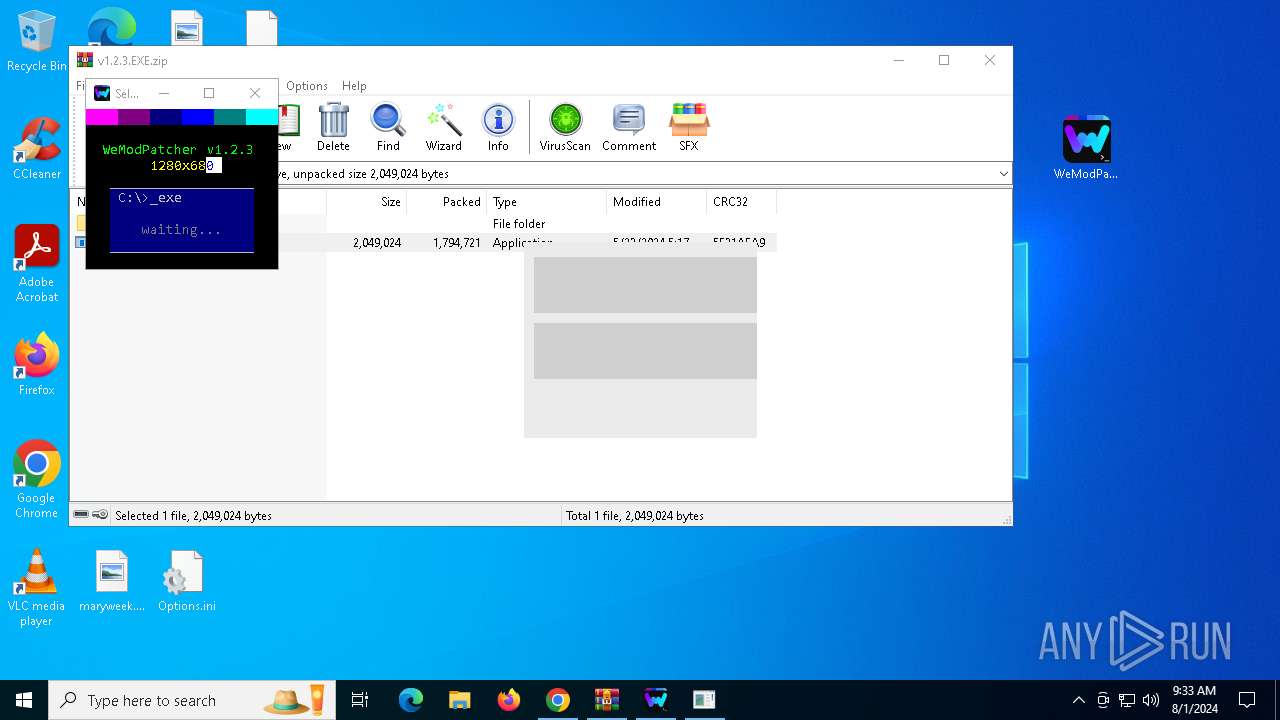
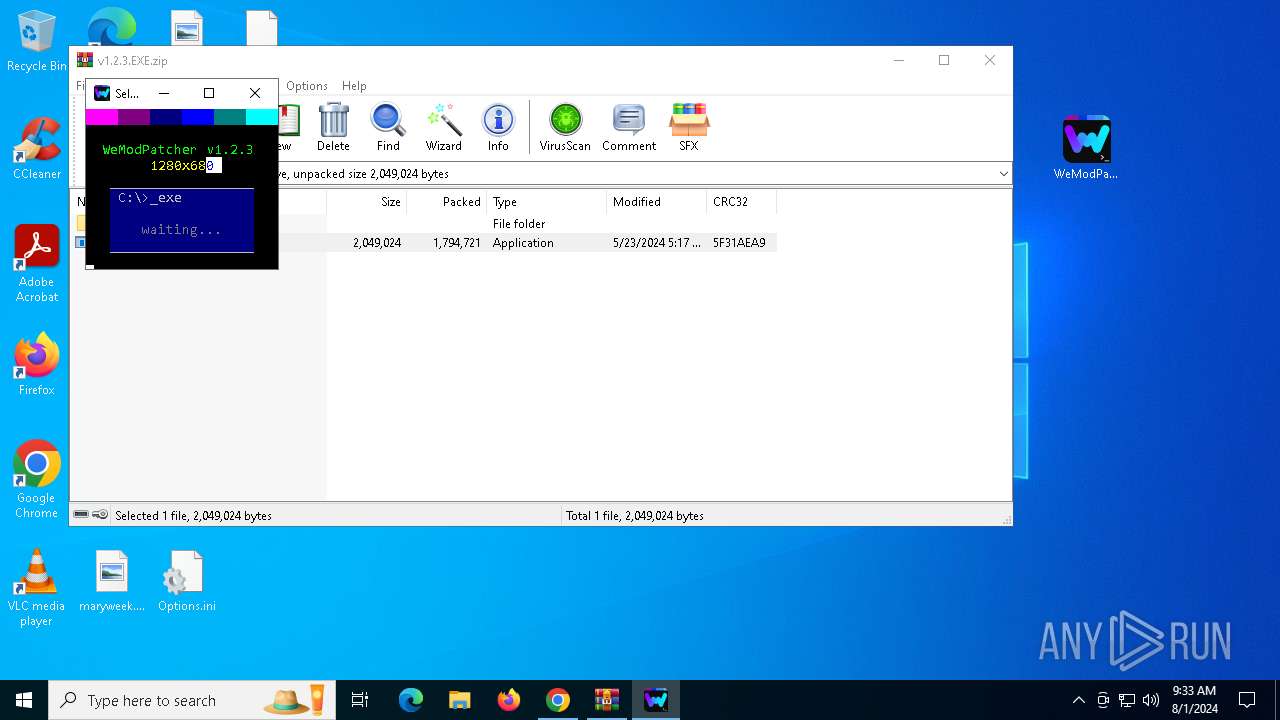
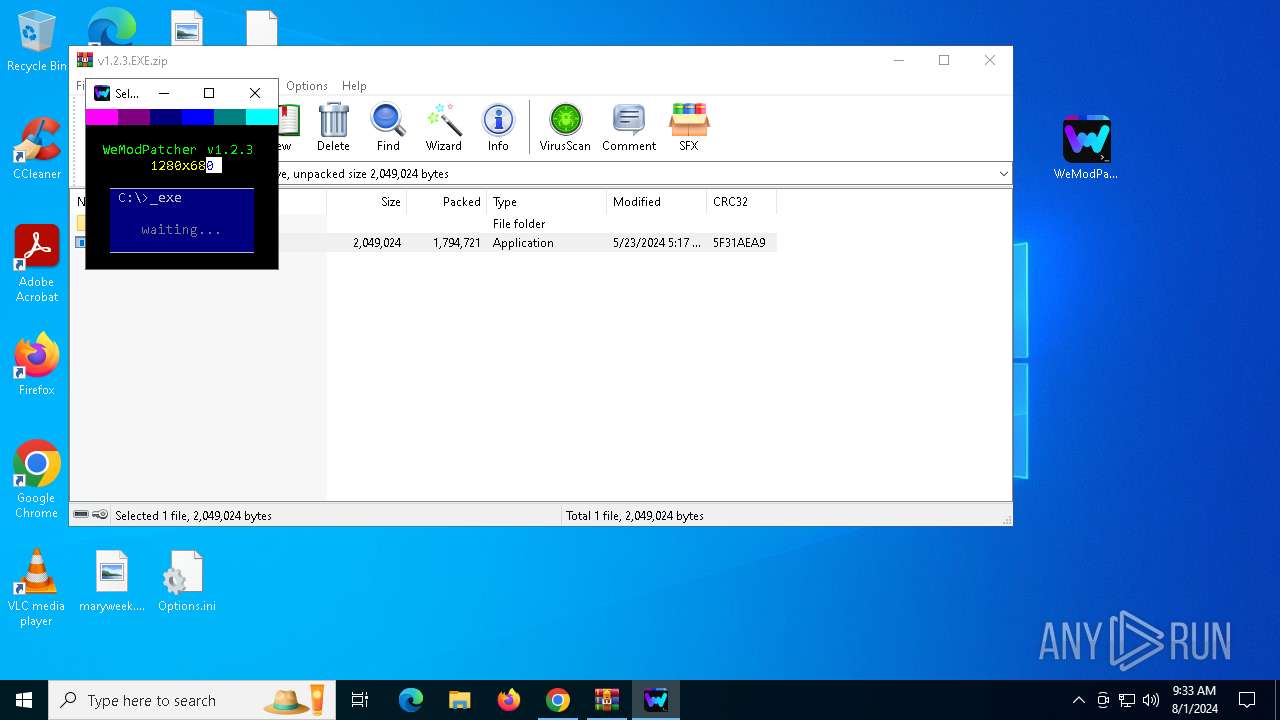
MALICIOUS
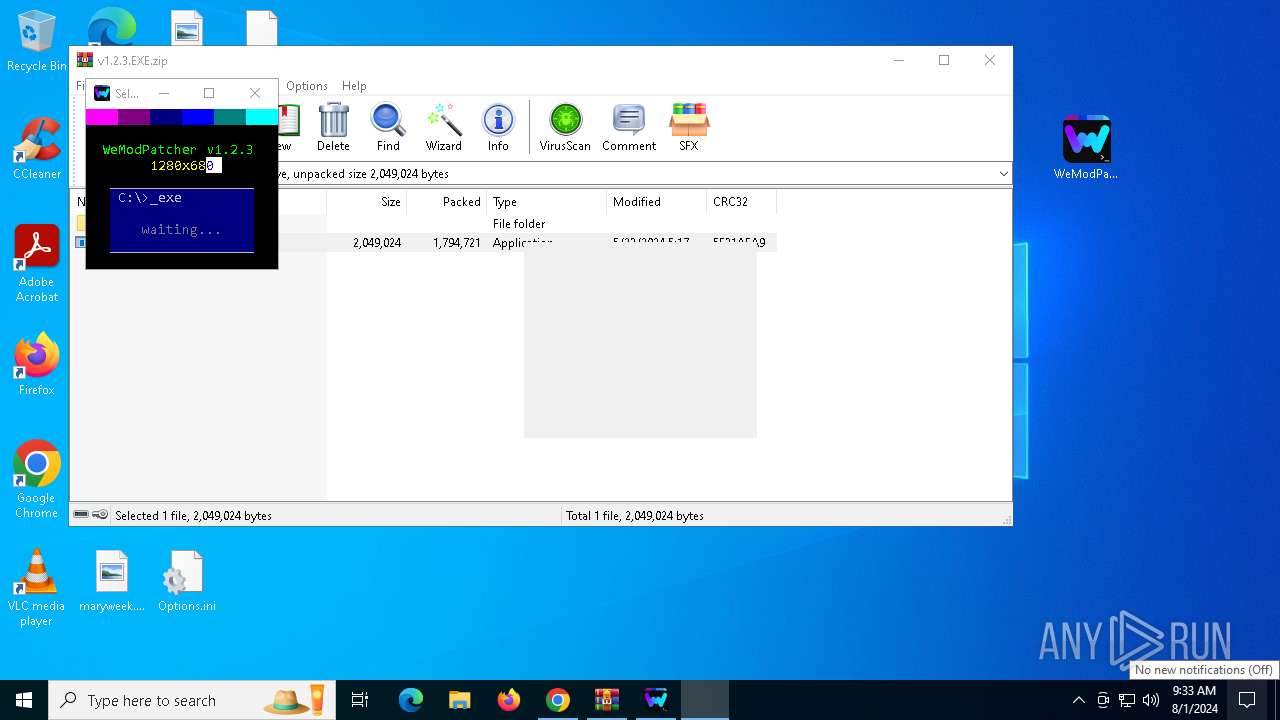
Drops the executable file immediately after the start
- WeModPatcher.exe (PID: 8088)
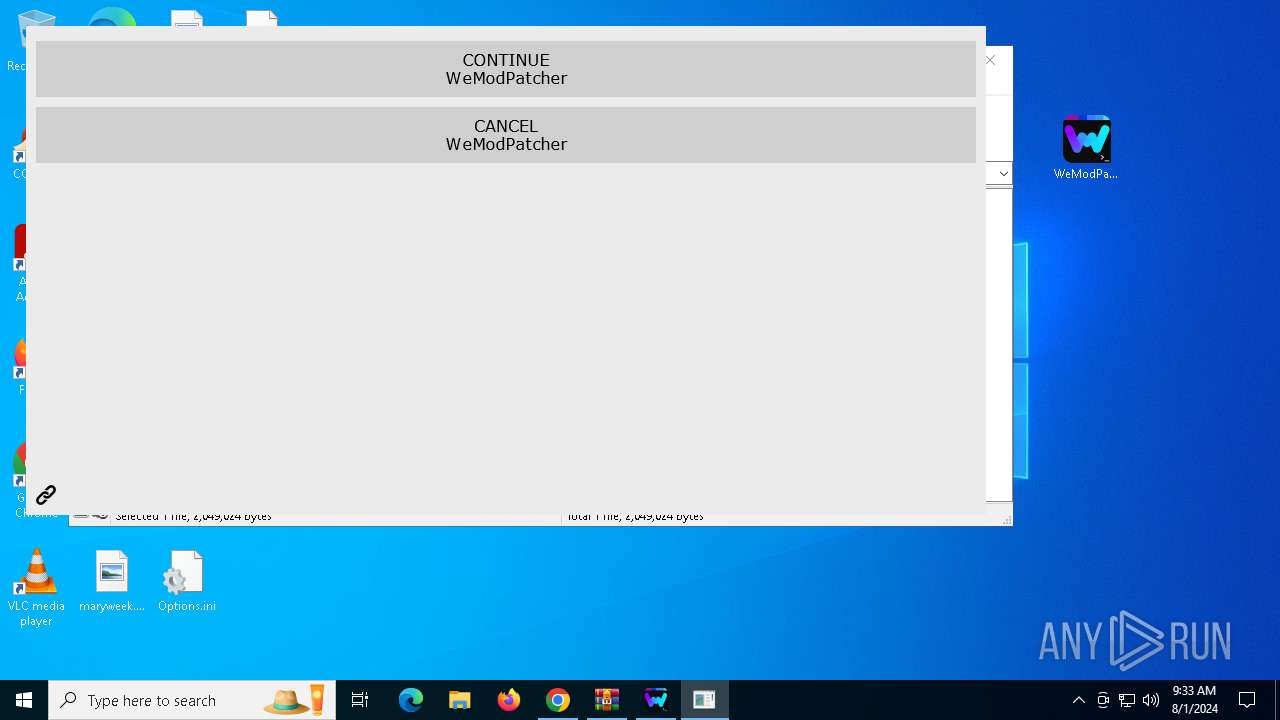
SUSPICIOUS
Executing commands from a ".bat" file
- WeModPatcher.exe (PID: 8088)
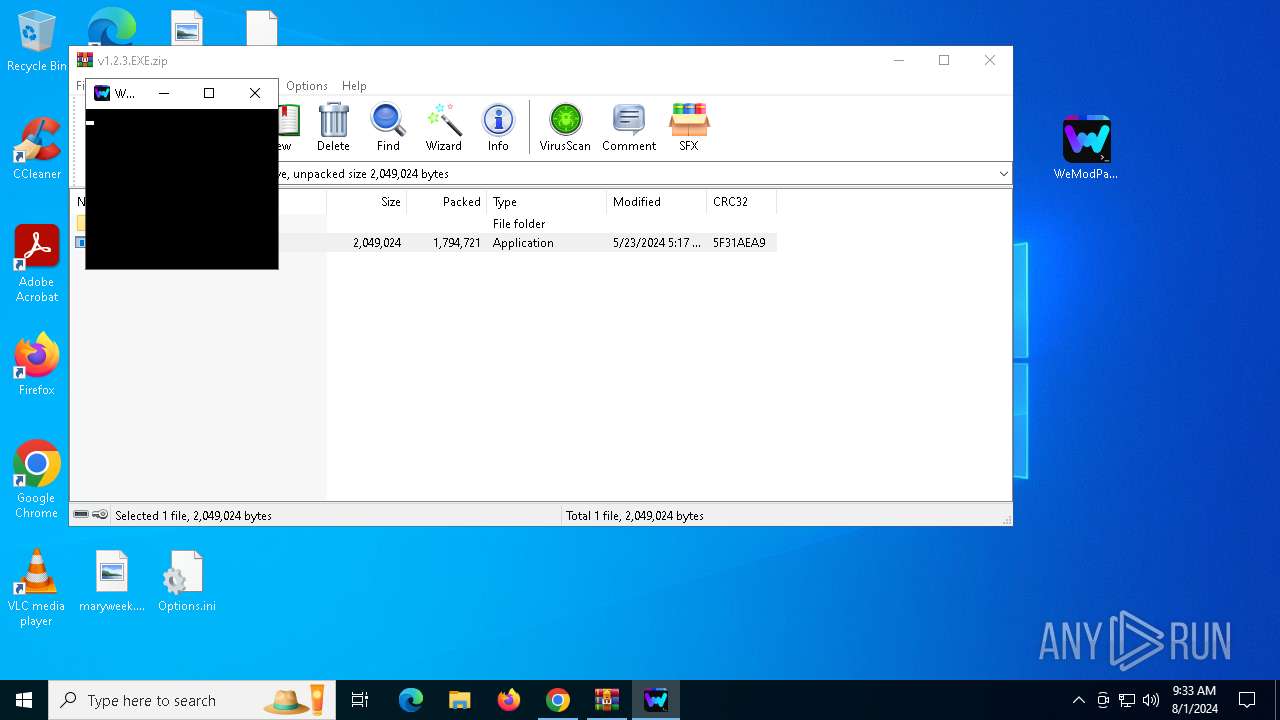
Drops 7-zip archiver for unpacking
- WeModPatcher.exe (PID: 8088)
Starts CMD.EXE for commands execution
- WeModPatcher.exe (PID: 8088)
- cmd.exe (PID: 8156)
Application launched itself
- cmd.exe (PID: 8156)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7596)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 7816)
- cmd.exe (PID: 7220)
- cmd.exe (PID: 6012)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 5976)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 5144)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 1132)
Get information on the list of running processes
- cmd.exe (PID: 8156)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 7816)
- cmd.exe (PID: 4236)
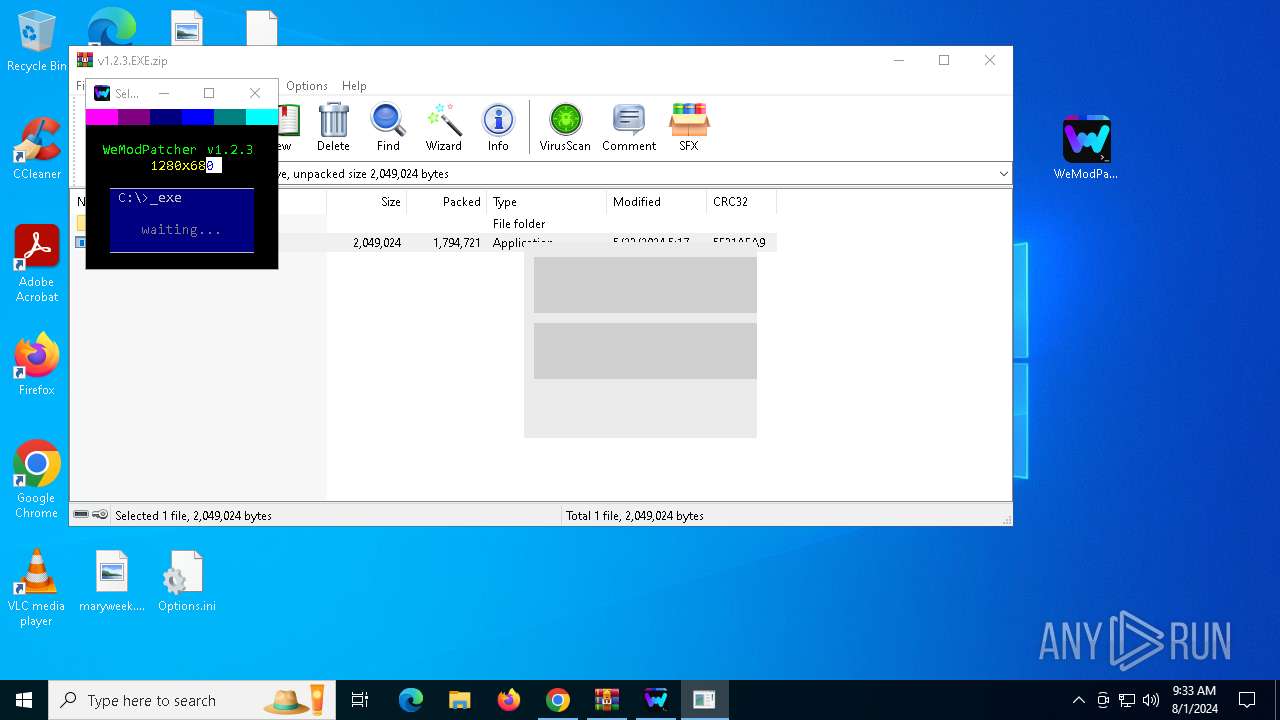
Starts application with an unusual extension
- cmd.exe (PID: 8156)
- cmd.exe (PID: 7964)
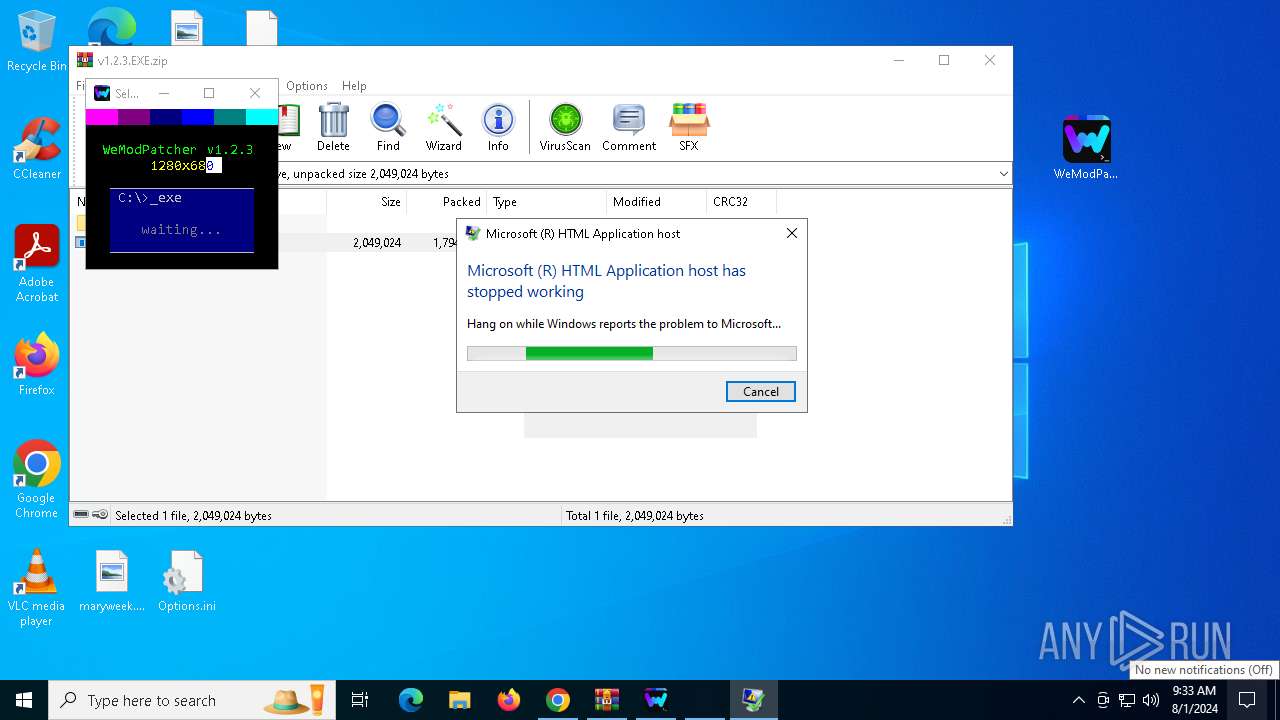
Creates FileSystem object to access computer's file system (SCRIPT)
- mshta.exe (PID: 7748)
- mshta.exe (PID: 6328)
- mshta.exe (PID: 1536)
- mshta.exe (PID: 6300)
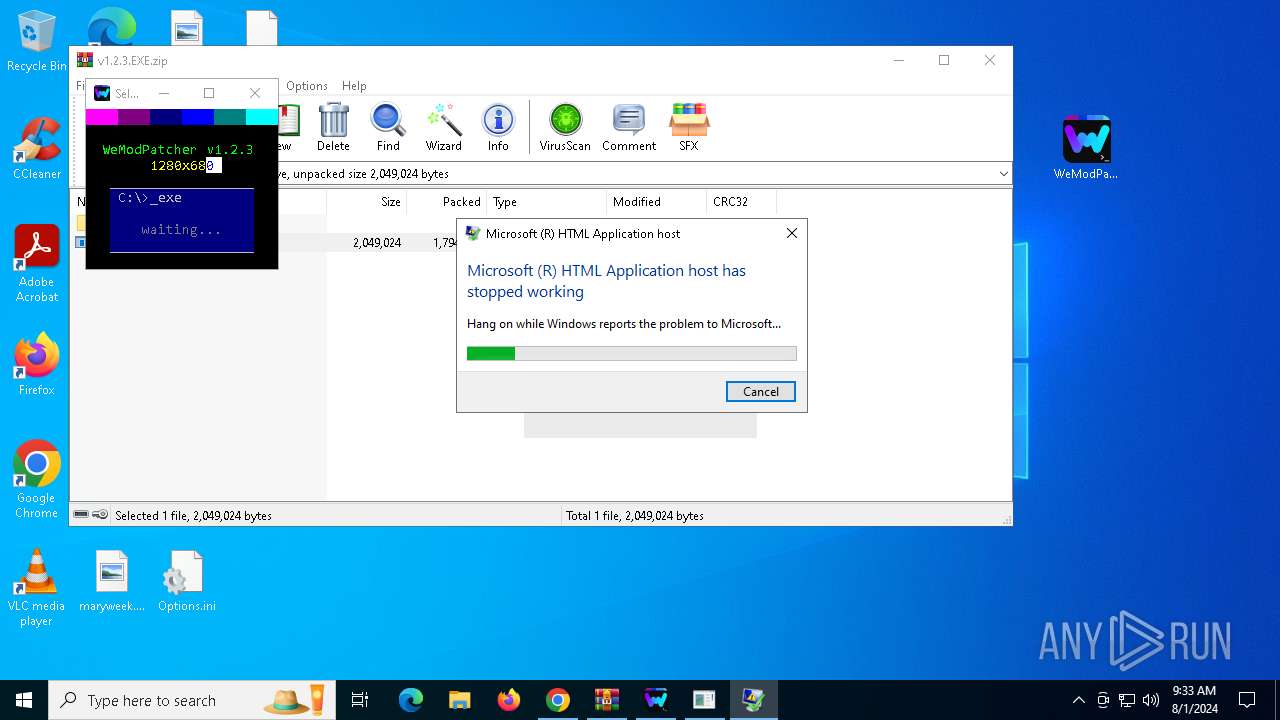
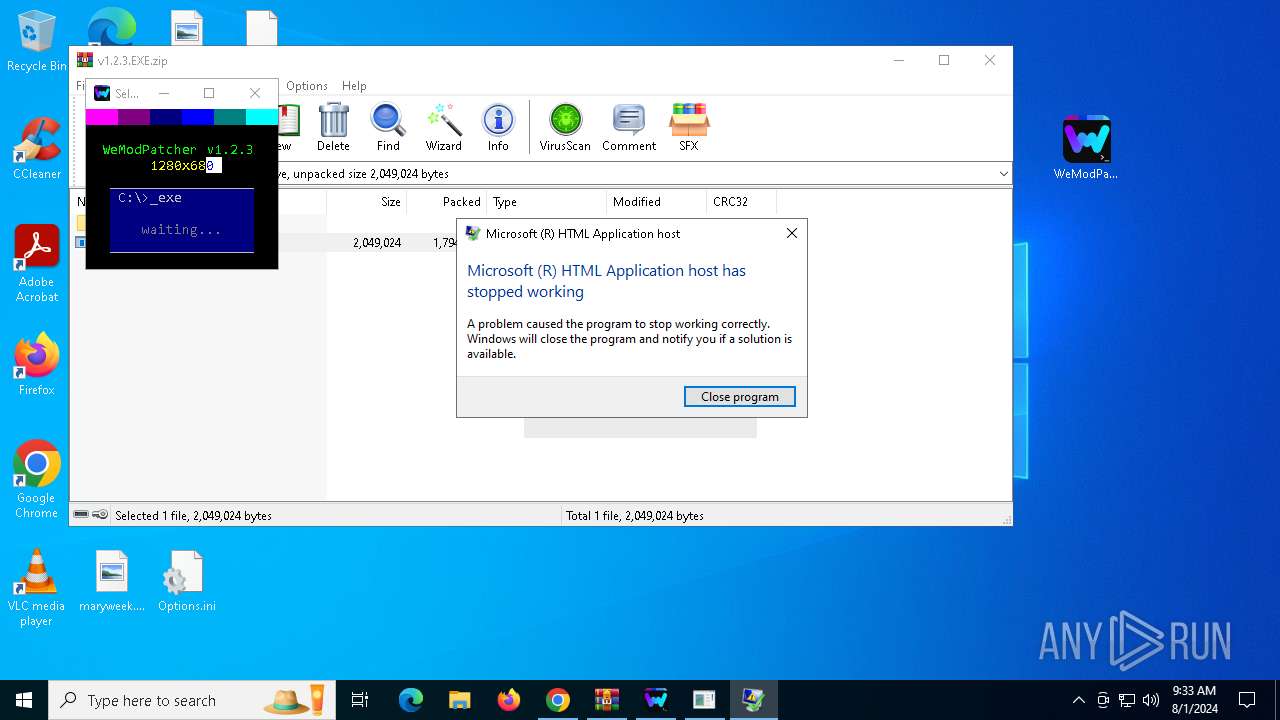
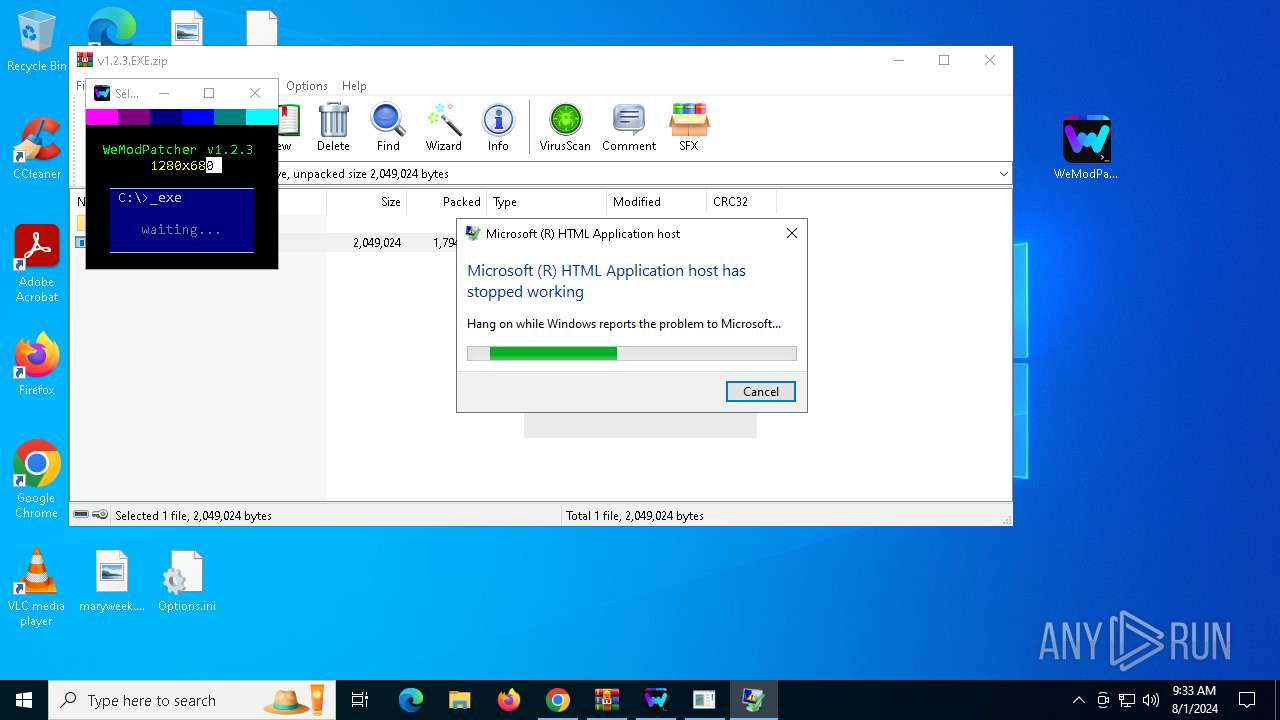
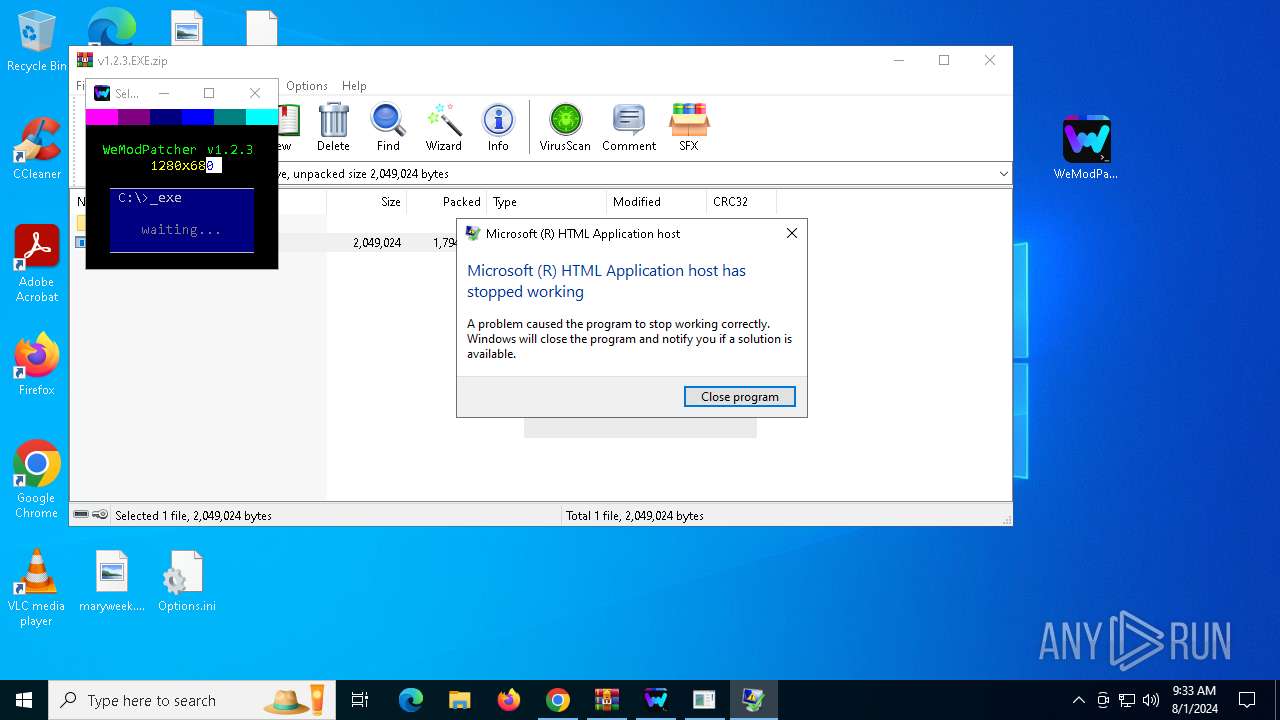
The process creates files with name similar to system file names
- WerFault.exe (PID: 1716)
- WerFault.exe (PID: 1164)
- WerFault.exe (PID: 4704)
- WerFault.exe (PID: 1344)
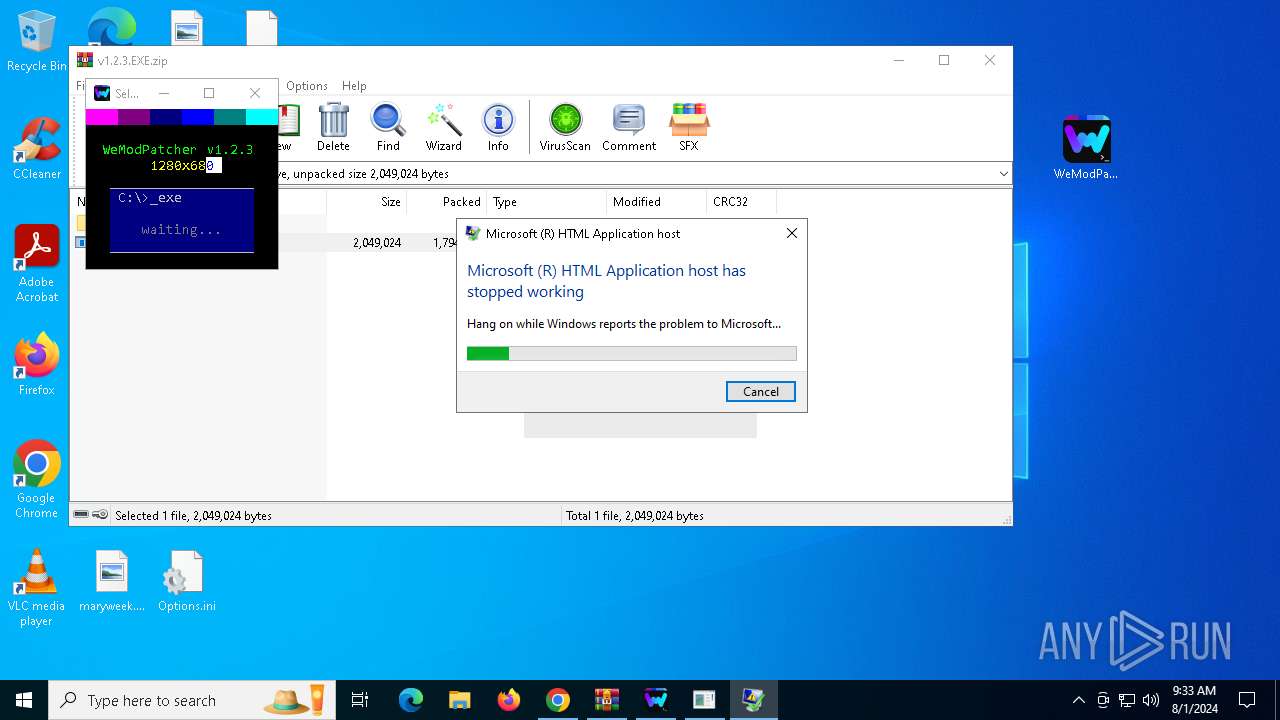
Executes application which crashes
- mshta.exe (PID: 6328)
- mshta.exe (PID: 1536)
- mshta.exe (PID: 7748)
- mshta.exe (PID: 6300)
INFO
Application launched itself
- chrome.exe (PID: 6364)
Drops the executable file immediately after the start
- chrome.exe (PID: 7148)
- chrome.exe (PID: 6364)
- WinRAR.exe (PID: 8004)
- chrome.exe (PID: 7292)
Executable content was dropped or overwritten
- chrome.exe (PID: 7148)
- WinRAR.exe (PID: 8004)
- chrome.exe (PID: 7292)
Checks supported languages
- TextInputHost.exe (PID: 7560)
- curl.exe (PID: 7204)
- chcp.com (PID: 6052)
- mode.com (PID: 5976)
- chcp.com (PID: 7984)
- WeModPatcher.exe (PID: 8088)
- chcp.com (PID: 5240)
- chcp.com (PID: 904)
- chcp.com (PID: 7716)
- chcp.com (PID: 7996)
- chcp.com (PID: 3864)
Reads the computer name
- TextInputHost.exe (PID: 7560)
- curl.exe (PID: 7204)
The process uses the downloaded file
- chrome.exe (PID: 7792)
- WinRAR.exe (PID: 8004)
- chrome.exe (PID: 6364)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6364)
Manual execution by a user
- WeModPatcher.exe (PID: 8088)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7780)
Reads Internet Explorer settings
- mshta.exe (PID: 7748)
- mshta.exe (PID: 6328)
- mshta.exe (PID: 1536)
- mshta.exe (PID: 6300)
Checks proxy server information
- WerFault.exe (PID: 1716)
- mshta.exe (PID: 7748)
- mshta.exe (PID: 6328)
- mshta.exe (PID: 1536)
- WerFault.exe (PID: 1164)
- WerFault.exe (PID: 4704)
- WerFault.exe (PID: 1344)
- mshta.exe (PID: 6300)
Reads the software policy settings
- WerFault.exe (PID: 1716)
- WerFault.exe (PID: 1164)
- WerFault.exe (PID: 4704)
- WerFault.exe (PID: 1344)
Create files in a temporary directory
- WeModPatcher.exe (PID: 8088)
Creates files or folders in the user directory
- WerFault.exe (PID: 1716)
- WerFault.exe (PID: 1164)
- WerFault.exe (PID: 4704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
222
Monitored processes
81
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | chcp 850 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "(Get-Culture).Name" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | C:\WINDOWS\system32\WerFault.exe -u -p 6328 -s 1980 | C:\Windows\System32\WerFault.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | C:\WINDOWS\system32\WerFault.exe -u -p 6300 -s 1968 | C:\Windows\System32\WerFault.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1536 | powershell -Command "Write-Host -B 13 -F 13 '....' -NoNewline; Write-Host -B 5 -F 5 '....' -NoNewline; Write-Host -B 1 -F 1 '....' -NoNewline; Write-Host -B 9 -F 9 '....' -NoNewline; Write-Host -B 3 -F 3 '....' -NoNewline; Write-Host -B 11 -F 11 '...' `n`n -NoNewline; Write-Host -B 0 -F 10 ' WeModPatcher v1.2.3'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1536 | mshta.exe "C:\Users\admin\Desktop\Launcher.hta" | C:\Windows\System32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 3221225477 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1716 | C:\WINDOWS\system32\WerFault.exe -u -p 7748 -s 1960 | C:\Windows\System32\WerFault.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4768 --field-trial-handle=1844,i,6745890159475442950,3684945364591758052,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2088 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "(Get-Culture).DisplayName" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2340 | C:\WINDOWS\system32\cmd.exe /c mshta.exe "C:\Users\admin\Desktop\Launcher.hta" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225477 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
108 045
Read events
107 945
Write events
94
Delete events
6
Modification events
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
3
Suspicious files
113
Text files
85
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe5bf6.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe5bf6.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:723783C35EAEEE1492EDB30847AE6750 | SHA256:C29323F784CF873BF34992E7A2B4630B19641BF42980109E31D5AF2D487DF6F8 | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
63
DNS requests
37
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5484 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5484 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5372 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6904 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
768 | lsass.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
7388 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p2zbkxfgkqyr6ljey2oe3bnzoy_2023.11.29.1201/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.11.29.1201_all_acqy67ncydhwie54b6ghdtndubgq.crx3 | unknown | — | — | whitelisted |
7388 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p2zbkxfgkqyr6ljey2oe3bnzoy_2023.11.29.1201/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.11.29.1201_all_acqy67ncydhwie54b6ghdtndubgq.crx3 | unknown | — | — | whitelisted |
7388 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p2zbkxfgkqyr6ljey2oe3bnzoy_2023.11.29.1201/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.11.29.1201_all_acqy67ncydhwie54b6ghdtndubgq.crx3 | unknown | — | — | whitelisted |
7388 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kct3f2b256c6ad54mamrbriypm_3037/jflookgnkcckhobaglndicnbbgbonegd_3037_all_acsnwcofavbntb2tnme2h7xagkka.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4056 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4936 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6636 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
6364 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6636 | chrome.exe | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | unknown |
6636 | chrome.exe | 185.199.110.133:443 | objects.githubusercontent.com | FASTLY | US | unknown |
6364 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| shared |
accounts.google.com |
| whitelisted |
objects.githubusercontent.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |