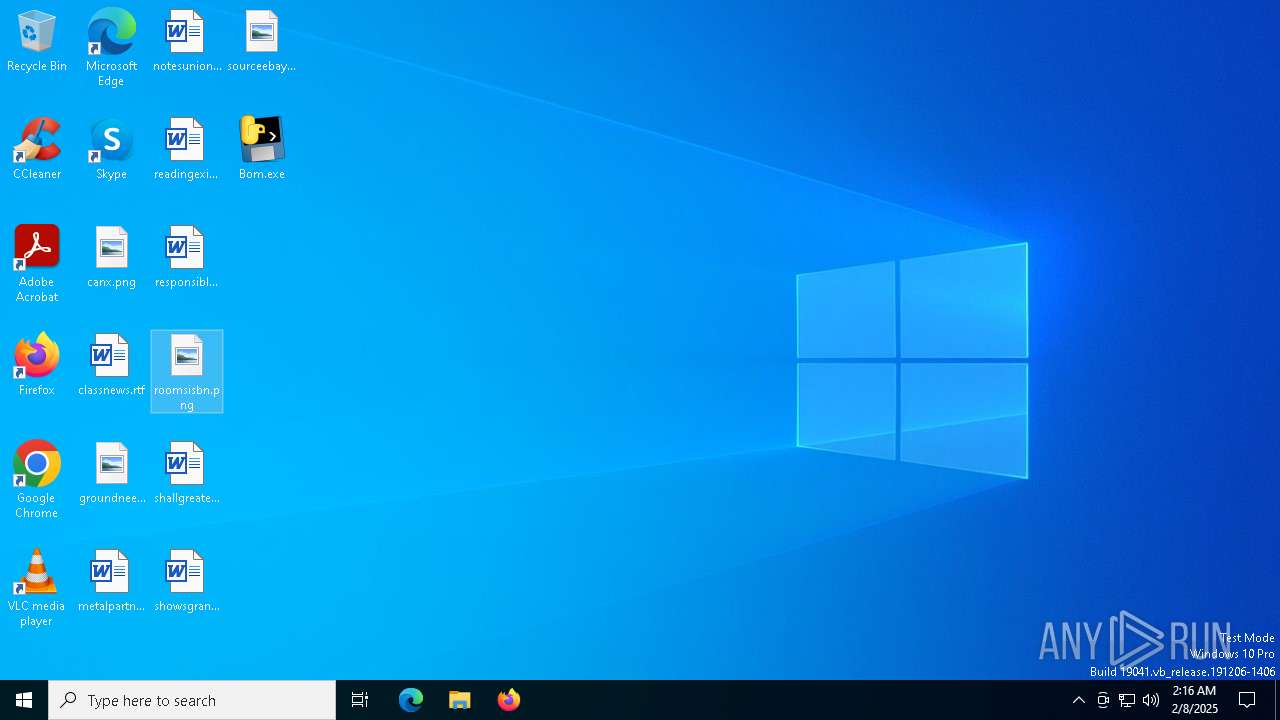
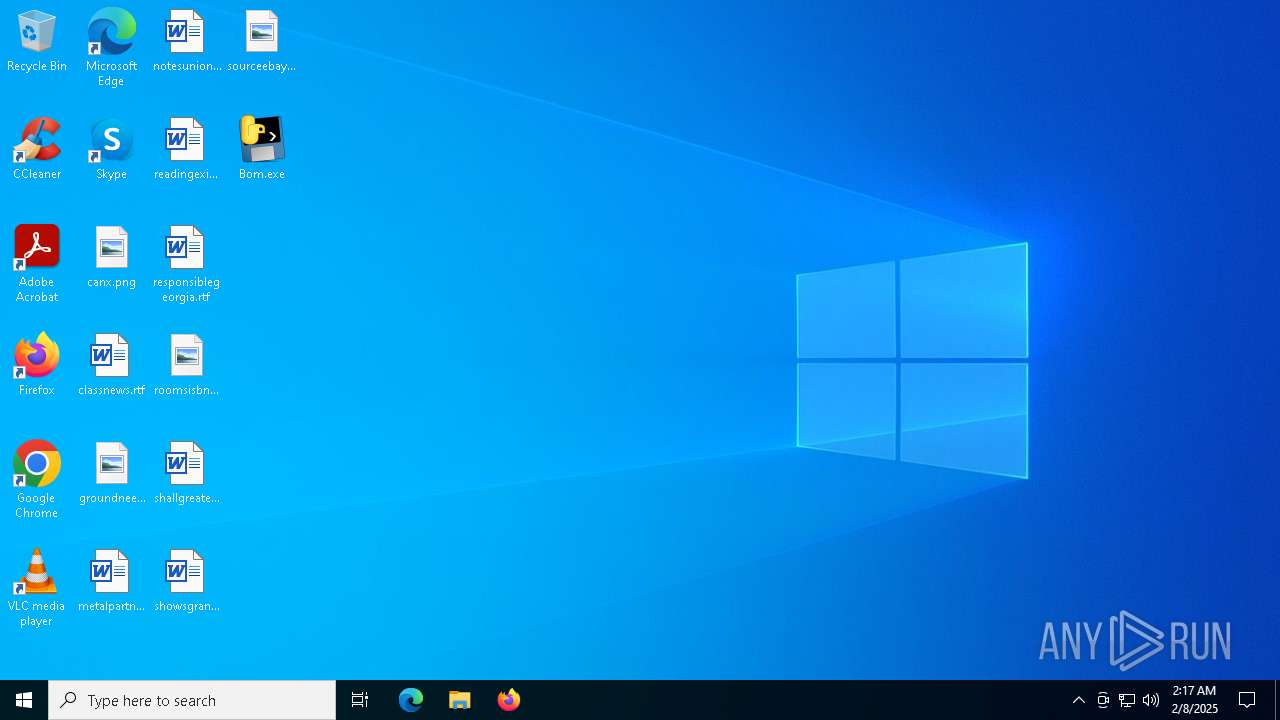
| File name: | Bom.exe |
| Full analysis: | https://app.any.run/tasks/0658ca7b-e099-41b2-a9fa-a87c5c7d943d |
| Verdict: | Malicious activity |
| Analysis date: | February 08, 2025, 02:16:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 5913340721C212C106DD1A1D3D1B720E |
| SHA1: | D4C63B899DF75164D6CA8B6EEFCD6EEEA0B79728 |
| SHA256: | 003B23471195D227493BFFE0573DFAE38B751950CE9F5BD11F048D672D942003 |
| SSDEEP: | 98304:ccd2vTuoYjH/2xumzy72m/4jvTNECbIdD1VUGF2IG4KRC1w2uaskVRCPZovL2dy7:lDGckQBObOHEEP2eHwG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops python dynamic module
- Bom.exe (PID: 6276)
- Bom.exe (PID: 6940)
The process drops C-runtime libraries
- Bom.exe (PID: 6276)
- Bom.exe (PID: 6940)
Process drops legitimate windows executable
- Bom.exe (PID: 6276)
- Bom.exe (PID: 6940)
Executable content was dropped or overwritten
- Bom.exe (PID: 6276)
- Bom.exe (PID: 6940)
Application launched itself
- Bom.exe (PID: 6276)
- Bom.exe (PID: 6940)
Loads Python modules
- Bom.exe (PID: 6376)
- Bom.exe (PID: 7004)
INFO
Checks supported languages
- Bom.exe (PID: 6276)
- Bom.exe (PID: 6376)
- Bom.exe (PID: 6940)
- Bom.exe (PID: 7004)
Reads the computer name
- Bom.exe (PID: 6276)
- Bom.exe (PID: 6940)
Create files in a temporary directory
- Bom.exe (PID: 6276)
- Bom.exe (PID: 6940)
The sample compiled with english language support
- Bom.exe (PID: 6276)
- Bom.exe (PID: 6940)
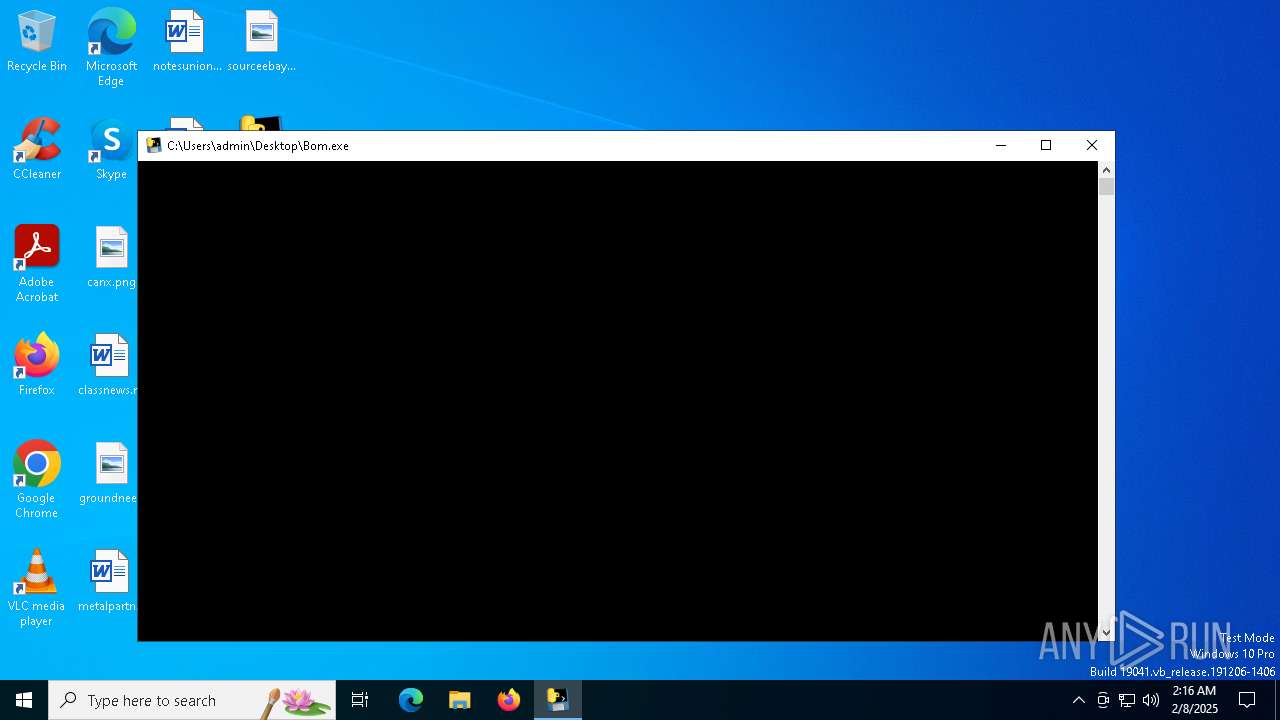
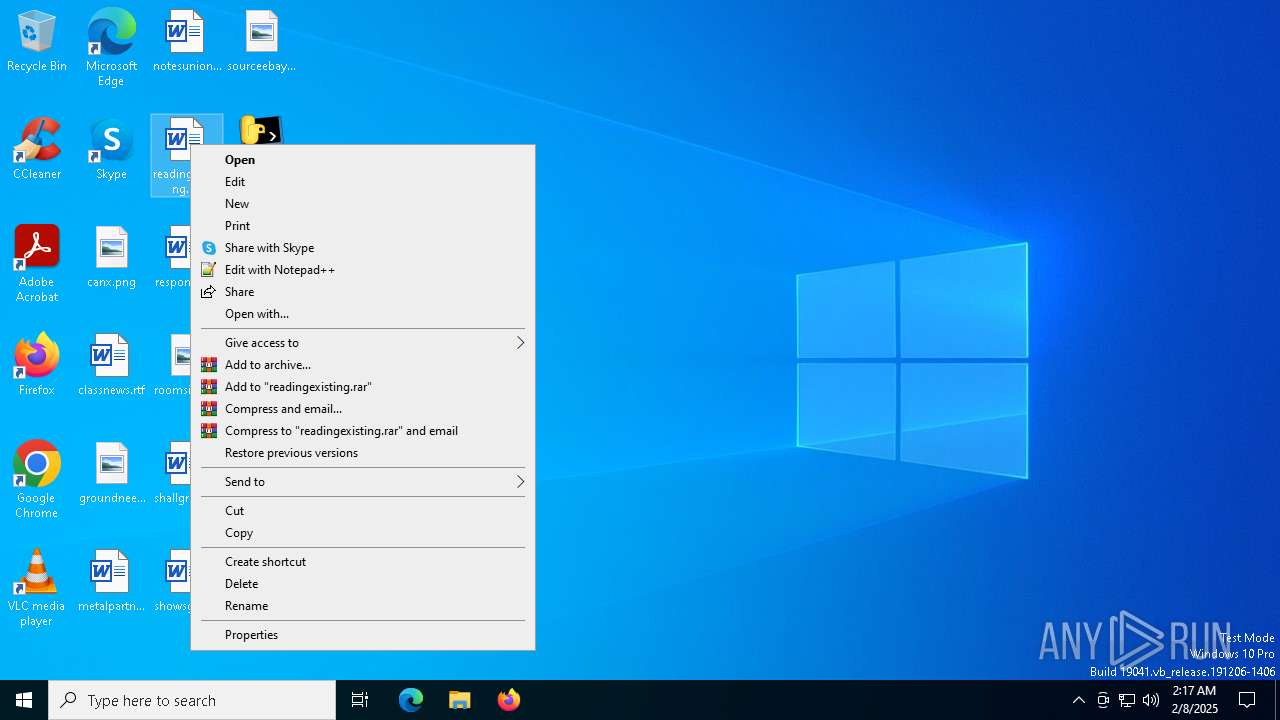
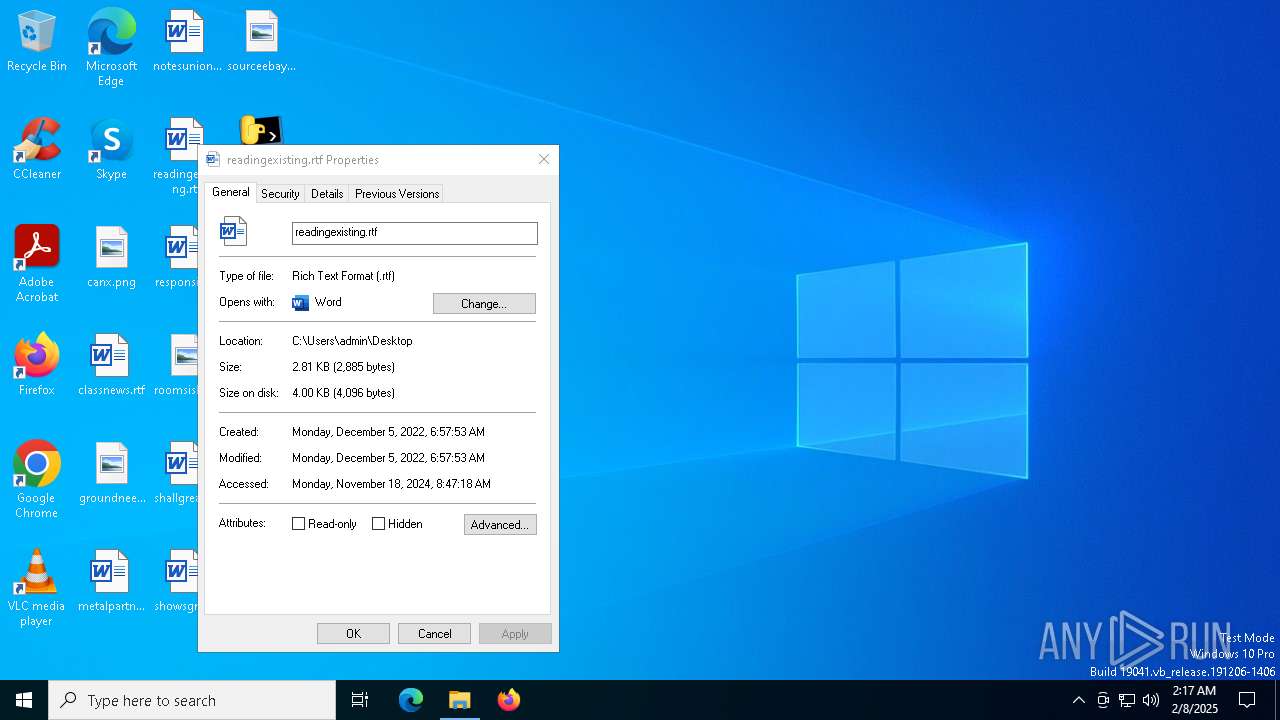
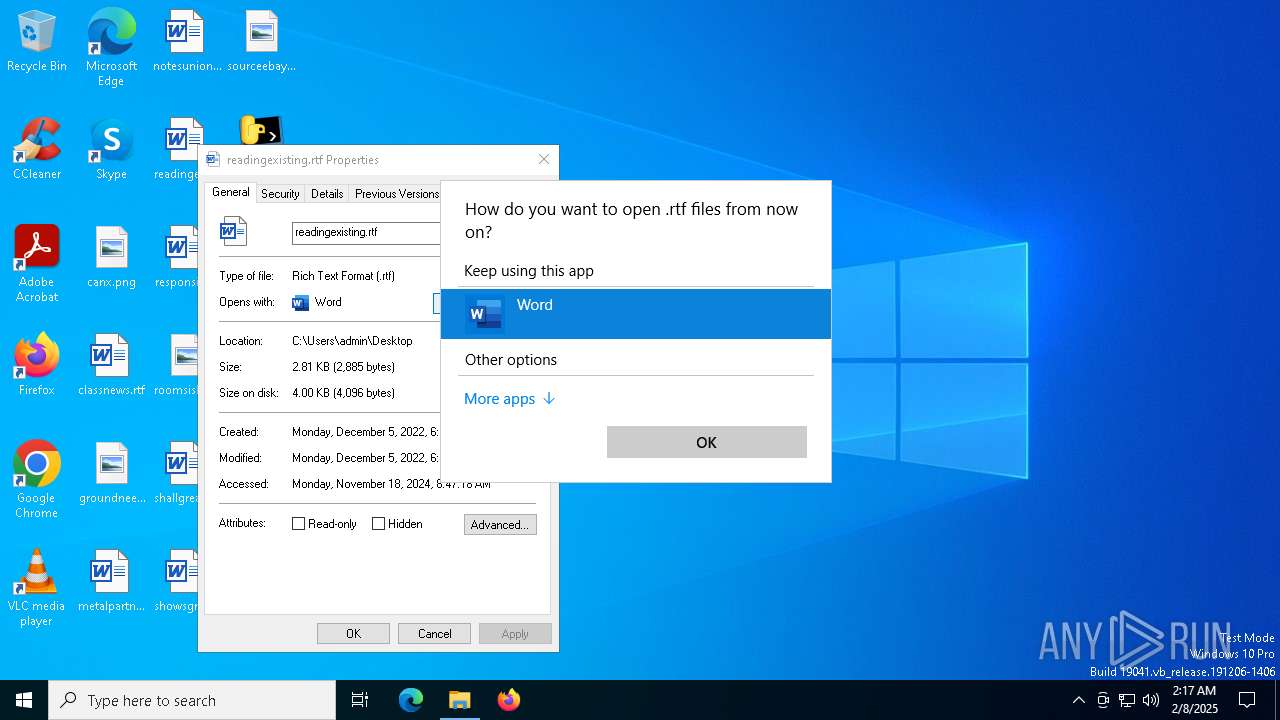
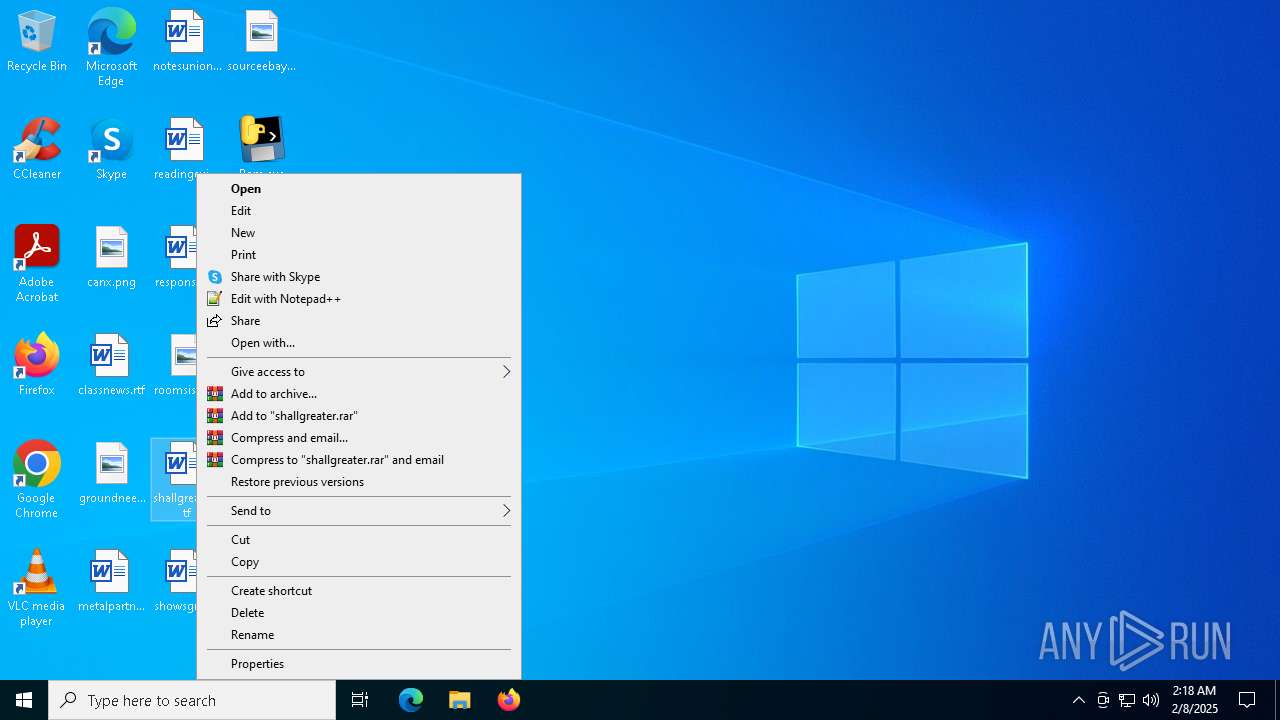
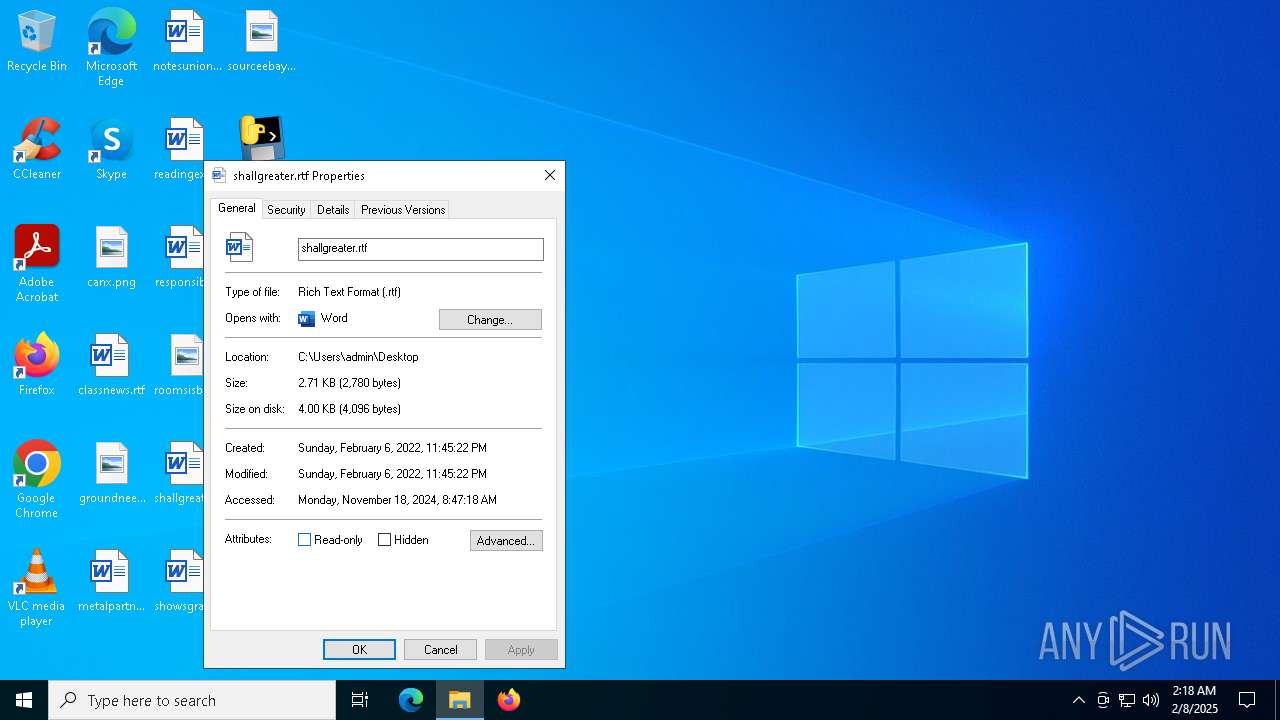
Manual execution by a user
- Bom.exe (PID: 6940)
- WINWORD.EXE (PID: 3840)
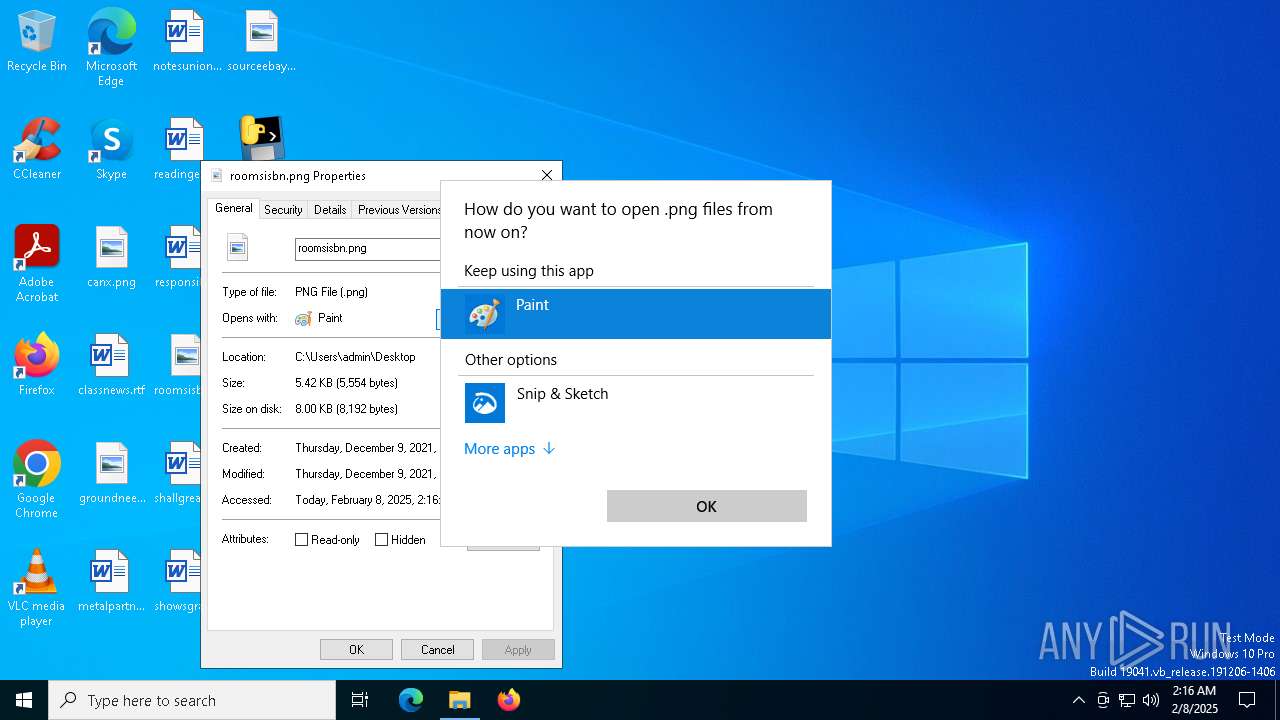
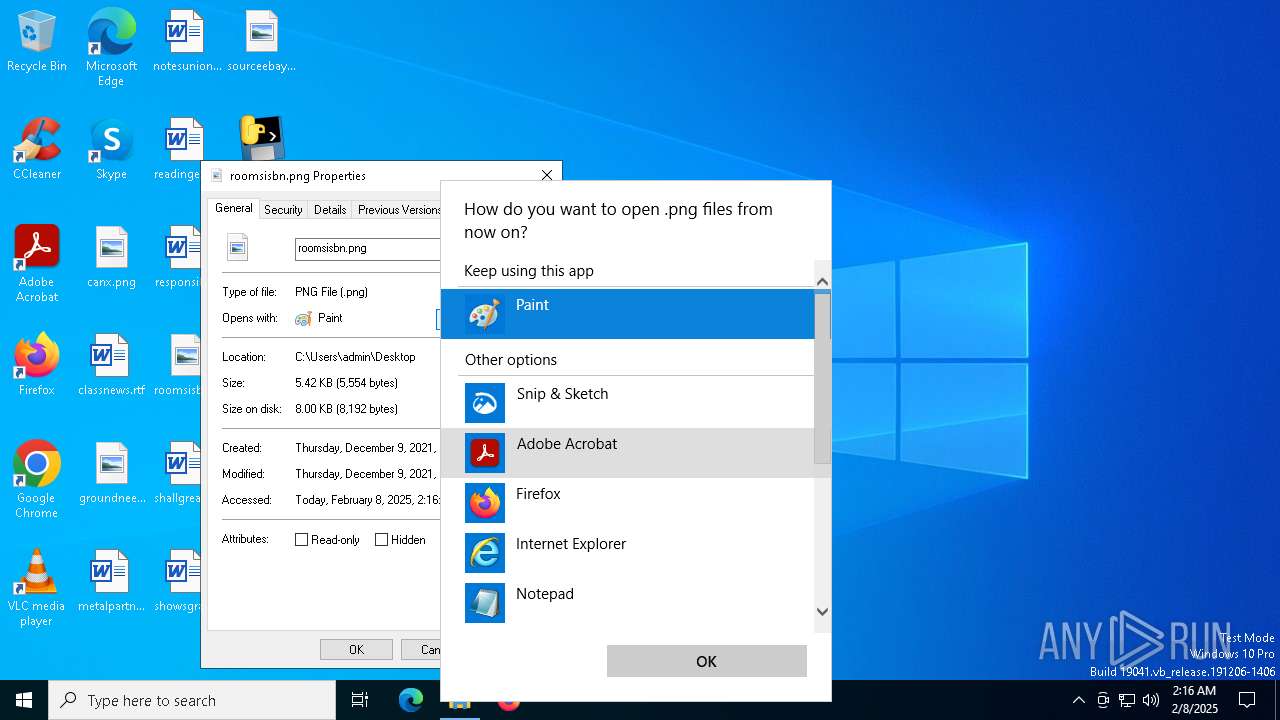
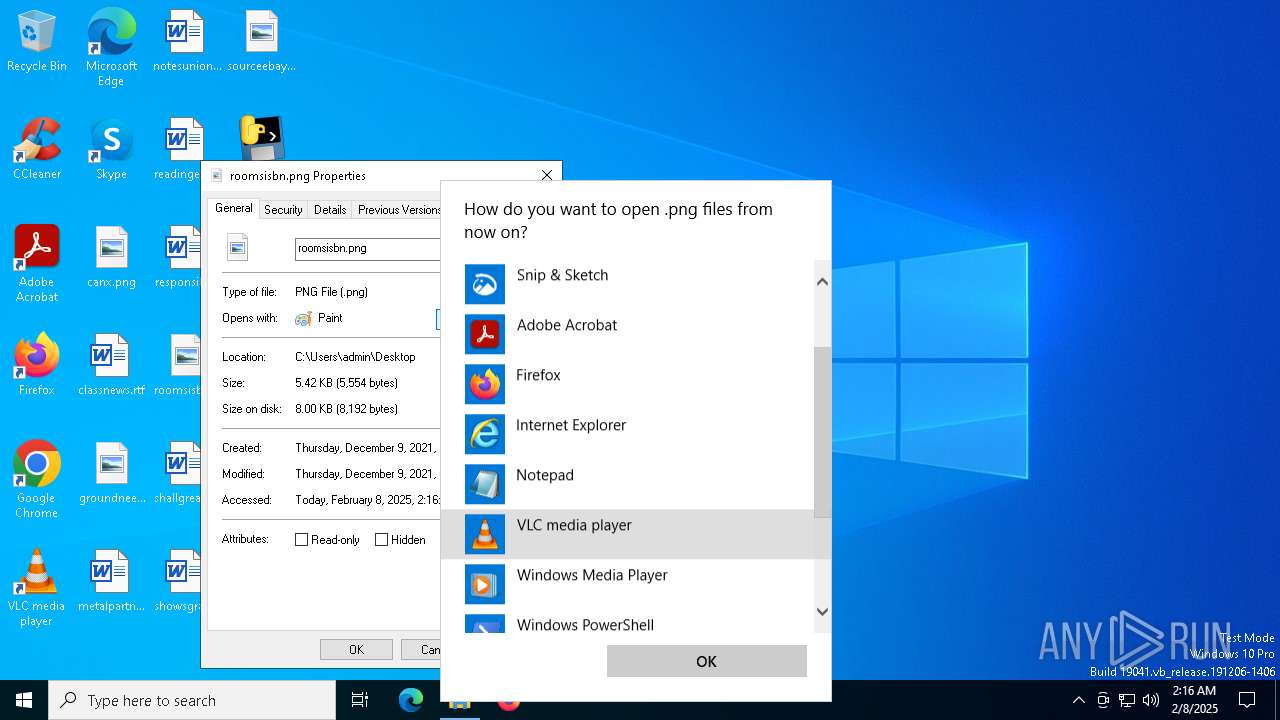
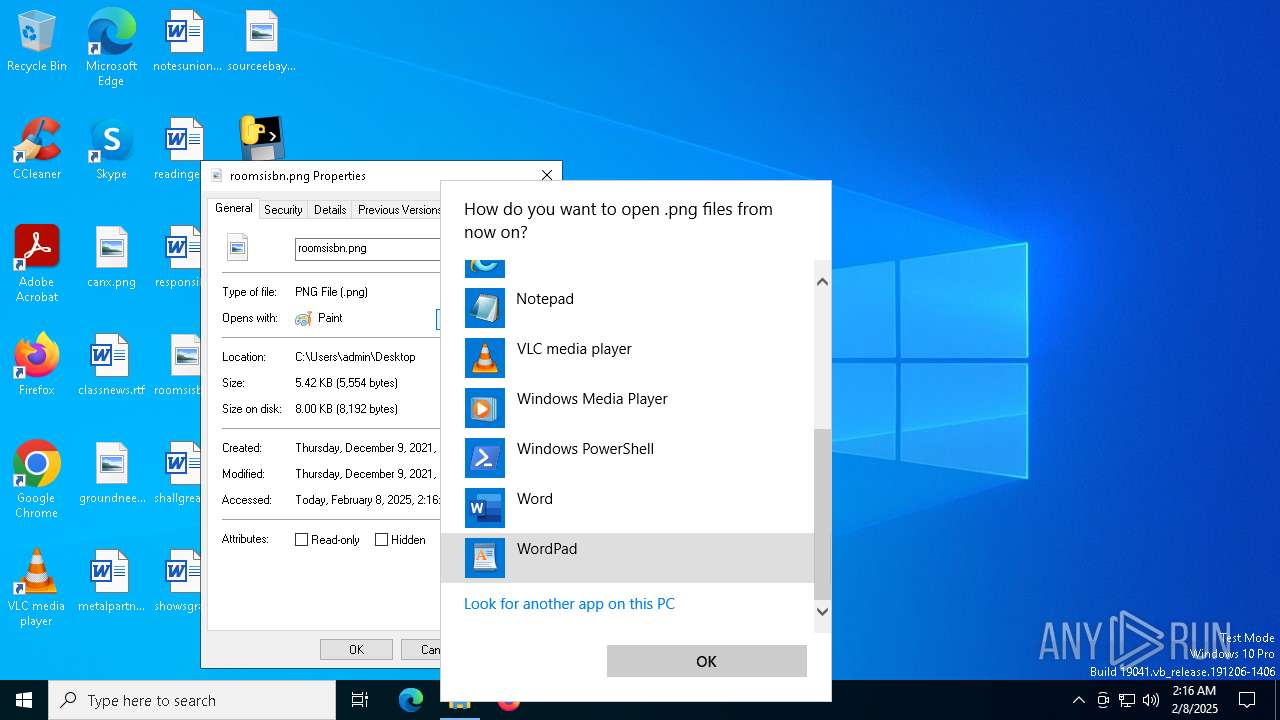
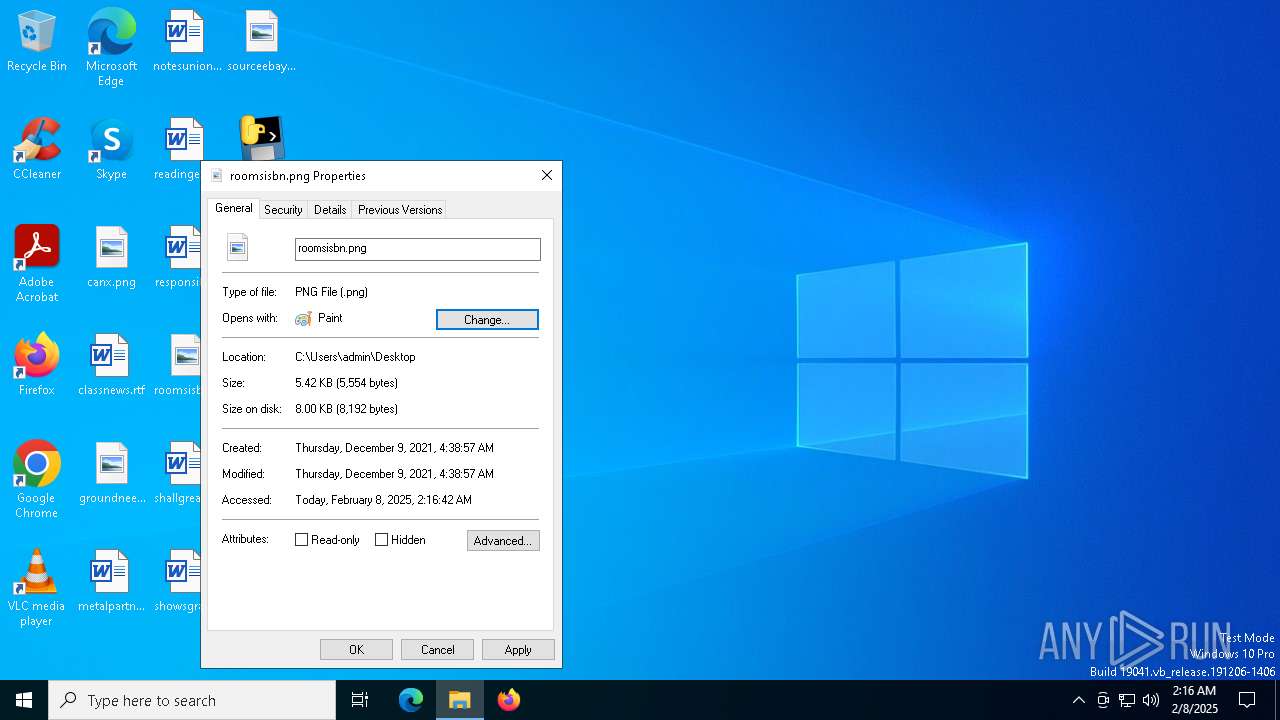
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 6300)
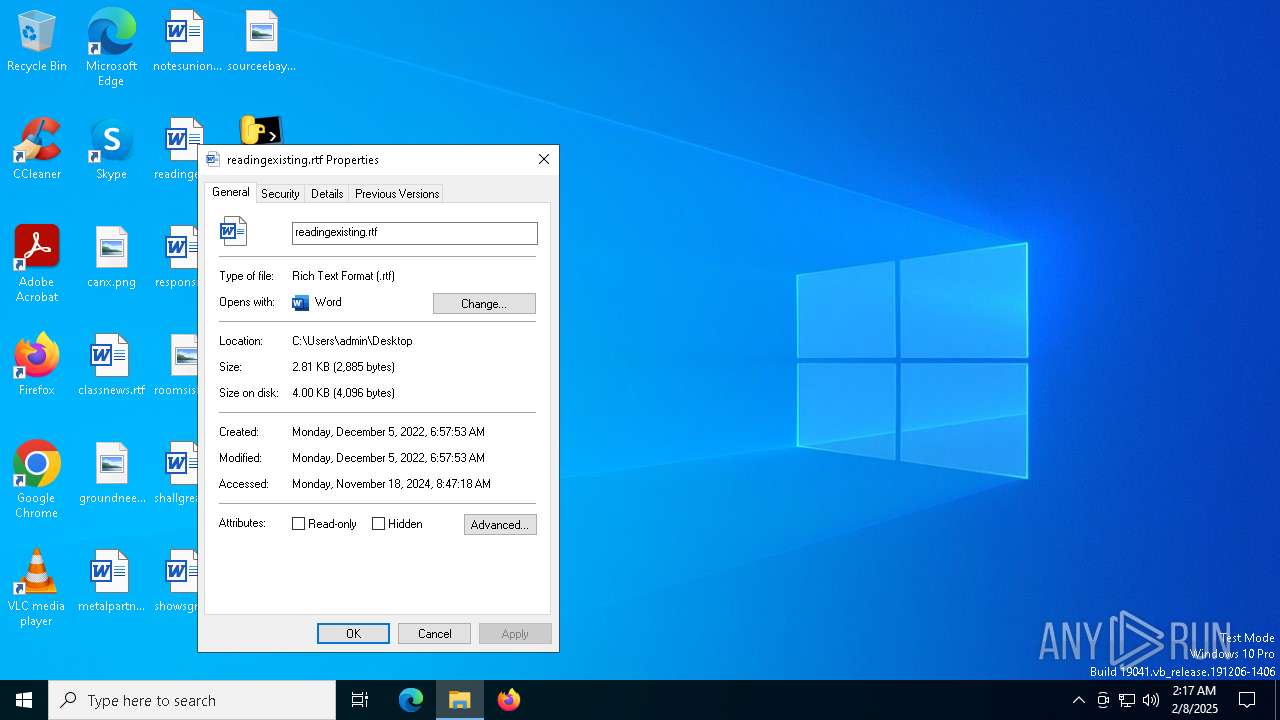
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 6300)
- OpenWith.exe (PID: 5316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:02:08 02:14:12+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 176640 |
| InitializedDataSize: | 152576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc380 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
143
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3840 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\responsiblegeorgia.rtf" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 5316 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6276 | "C:\Users\admin\Desktop\Bom.exe" | C:\Users\admin\Desktop\Bom.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 6284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Bom.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6300 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6376 | "C:\Users\admin\Desktop\Bom.exe" | C:\Users\admin\Desktop\Bom.exe | — | Bom.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 6380 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "80CC671F-77B1-4887-B629-63C6B91BBB9C" "B3F2FD65-0AED-4C77-9E33-CA4476369A99" "3840" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Exit code: 0 Version: 0.12.2.0 Modules
| |||||||||||||||
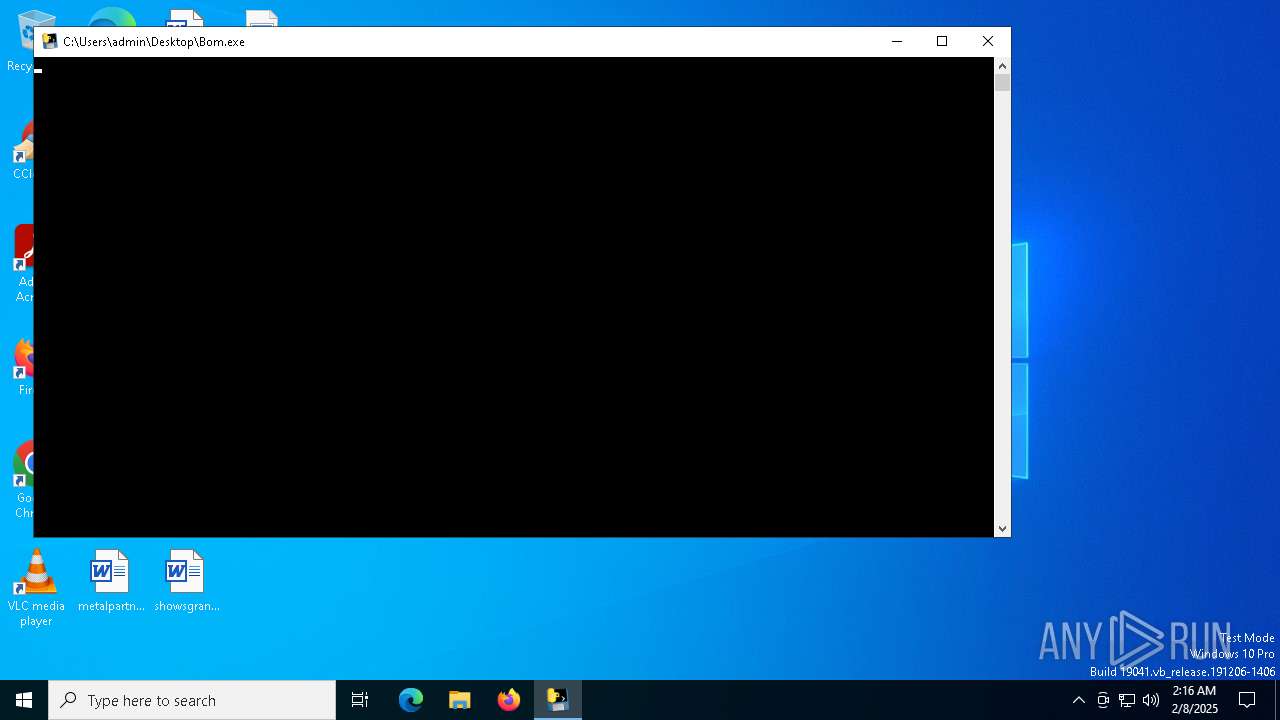
| 6940 | "C:\Users\admin\Desktop\Bom.exe" | C:\Users\admin\Desktop\Bom.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 6952 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Bom.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7004 | "C:\Users\admin\Desktop\Bom.exe" | C:\Users\admin\Desktop\Bom.exe | — | Bom.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
Total events
8 908
Read events
8 633
Write events
251
Delete events
24
Modification events
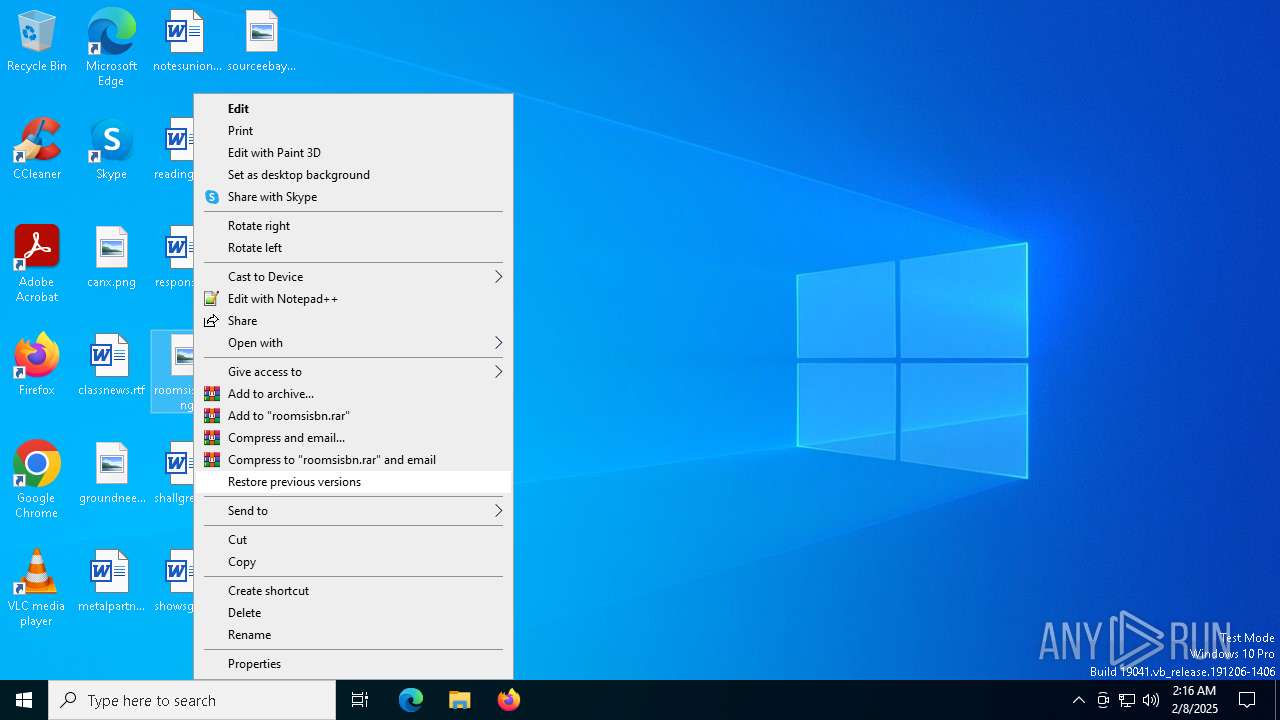
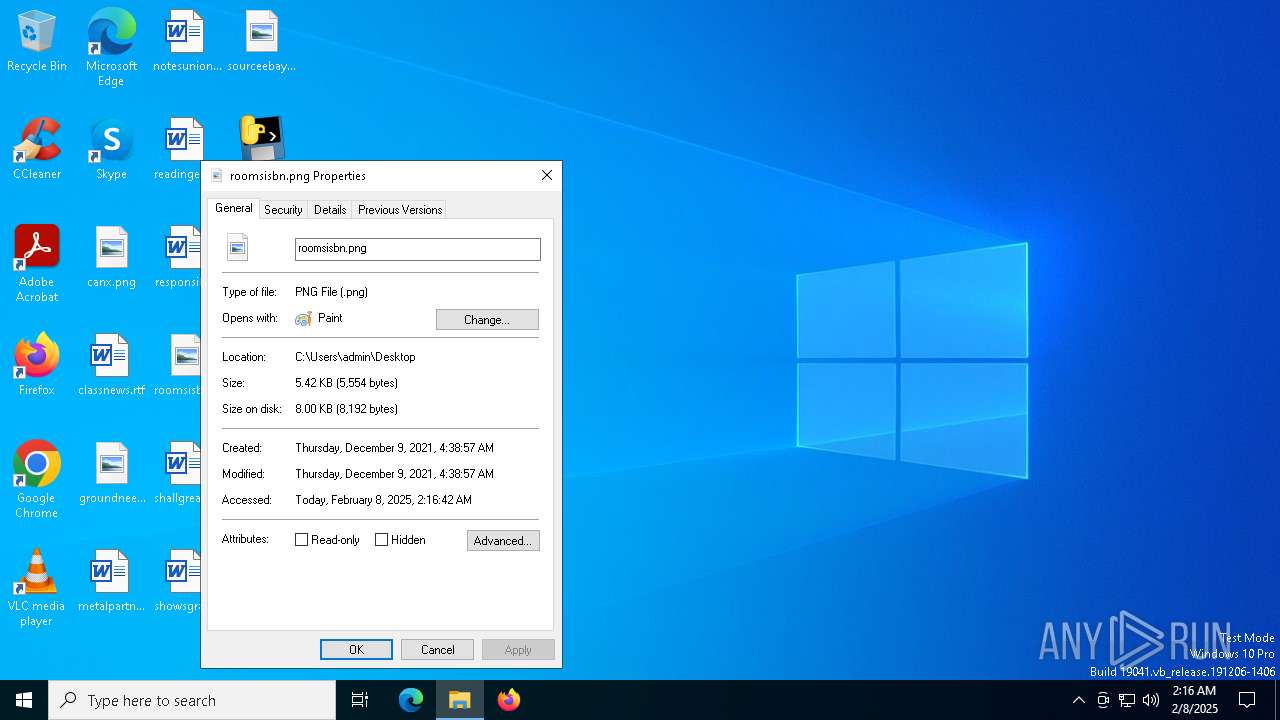
| (PID) Process: | (6300) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.png\OpenWithProgids |
| Operation: | write | Name: | pngfile |
Value: | |||
| (PID) Process: | (5316) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rtf\OpenWithProgids |
| Operation: | write | Name: | Word.RTF.8 |
Value: | |||
| (PID) Process: | (3840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\3840 |
| Operation: | write | Name: | 0 |
Value: 0B0E107ABFEB65E7B5344DB29EDFC8E23A671A230046A6E4D99EF9B9DEED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511801ED2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (3840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | tr-tr |
Value: 1 | |||
| (PID) Process: | (3840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (3840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (3840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (3840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (3840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (3840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
Executable files
107
Suspicious files
30
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6276 | Bom.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:8805DE8AEAD10A48193B54F882A7763A | SHA256:22B0D0412C274A04D11D7FD3F6545EFF245E6F032E21B86D920C2844DD1007C6 | |||
| 6276 | Bom.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\_socket.pyd | executable | |
MD5:B77017BAA2004833EF3847A3A3141280 | SHA256:A19E3C7C03EF1B5625790B1C9C42594909311AB6DF540FBF43C6AA93300AB166 | |||
| 6276 | Bom.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:8142799F92638D67267278D2FCAB85E0 | SHA256:F36025FD0715EC893C112F06472072C565385B8C5FA675CCE5B4A9158BFB87E9 | |||
| 6276 | Bom.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:1754ECB52A0C9FB6F11C43476975BE9E | SHA256:631A106755F13A78032D7C17CD19C5185FE89D93FDA2AC108C4F53E27DCDECDB | |||
| 6276 | Bom.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\api-ms-win-core-fibers-l1-1-0.dll | executable | |
MD5:B4C1A9EF2CF923A81969FAF2F74E5C18 | SHA256:938A52984E7E9FFEEF350A794907639D453E346D5BDC0AEC8C1360D040CC672A | |||
| 6276 | Bom.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:75C8A3C1DFE2096F1A2C6BA51DE7196F | SHA256:3D95961590FE6DA5C569BCB0A54651488E70DD7B15C257E1B9FAF8A3CC0E63E4 | |||
| 6276 | Bom.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:31B55653D51DE75F30BE2EEA85AEAD0F | SHA256:1CE185AFEEA0A30A12B496D95DF395C18BD0E99570C0AC3126758476D4B6AEA0 | |||
| 6276 | Bom.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\_decimal.pyd | executable | |
MD5:C88282908BA54510EDA3887C488198EB | SHA256:980A63F2B39CF16910F44384398E25F24482346A482ADDB00DE42555B17D4278 | |||
| 6276 | Bom.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\_bz2.pyd | executable | |
MD5:AA1083BDE6D21CABFC630A18F51B1926 | SHA256:00B8CA9A338D2B47285C9E56D6D893DB2A999B47216756F18439997FB80A56E3 | |||
| 6276 | Bom.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\VCRUNTIME140.dll | executable | |
MD5:BE8DBE2DC77EBE7F88F910C61AEC691A | SHA256:4D292623516F65C80482081E62D5DADB759DC16E851DE5DB24C3CBB57B87DB83 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
45
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.38.73.129:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.38.73.129:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6476 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3840 | WINWORD.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3840 | WINWORD.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.21.65.132:443 | — | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2144 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.21.65.154:443 | — | Akamai International B.V. | NL | unknown |
5064 | SearchApp.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|