| File name: | DeepLSetup.exe |
| Full analysis: | https://app.any.run/tasks/200372e6-8645-4927-99d5-74a289f9c1f0 |
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2024, 11:29:31 |
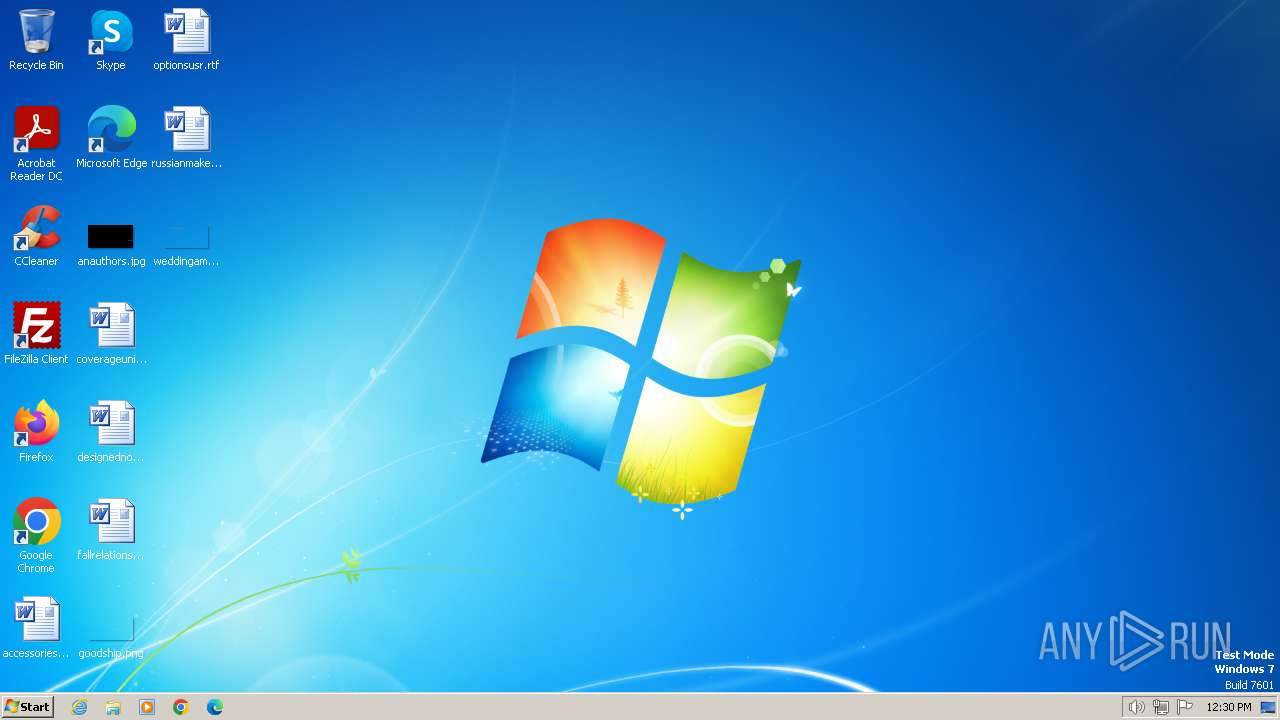
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 90D0A198EBD84AB18ED372DAB02B5862 |
| SHA1: | D4F39B9A647AE6AD7C981C7ACB4A6FF06025094D |
| SHA256: | 0037C9895723FB712B57B144CBB429F319AB5A3C1E4C44A3FFEFA351486BCDAF |
| SSDEEP: | 98304:kmed/dwLBjOlLvjSlRPqiblcNl5EYypBEsBKq:giPWF |
MALICIOUS
Drops the executable file immediately after the start
- DeepLSetup.exe (PID: 4008)
SUSPICIOUS
Creates file in the systems drive root
- DeepLSetup.exe (PID: 4008)
Reads the Internet Settings
- DeepLSetup.exe (PID: 4008)
INFO
Reads the computer name
- DeepLSetup.exe (PID: 4008)
Checks supported languages
- DeepLSetup.exe (PID: 4008)
Process checks whether UAC notifications are on
- DeepLSetup.exe (PID: 4008)
Reads the machine GUID from the registry
- DeepLSetup.exe (PID: 4008)
Reads Environment values
- DeepLSetup.exe (PID: 4008)
Create files in a temporary directory
- DeepLSetup.exe (PID: 4008)
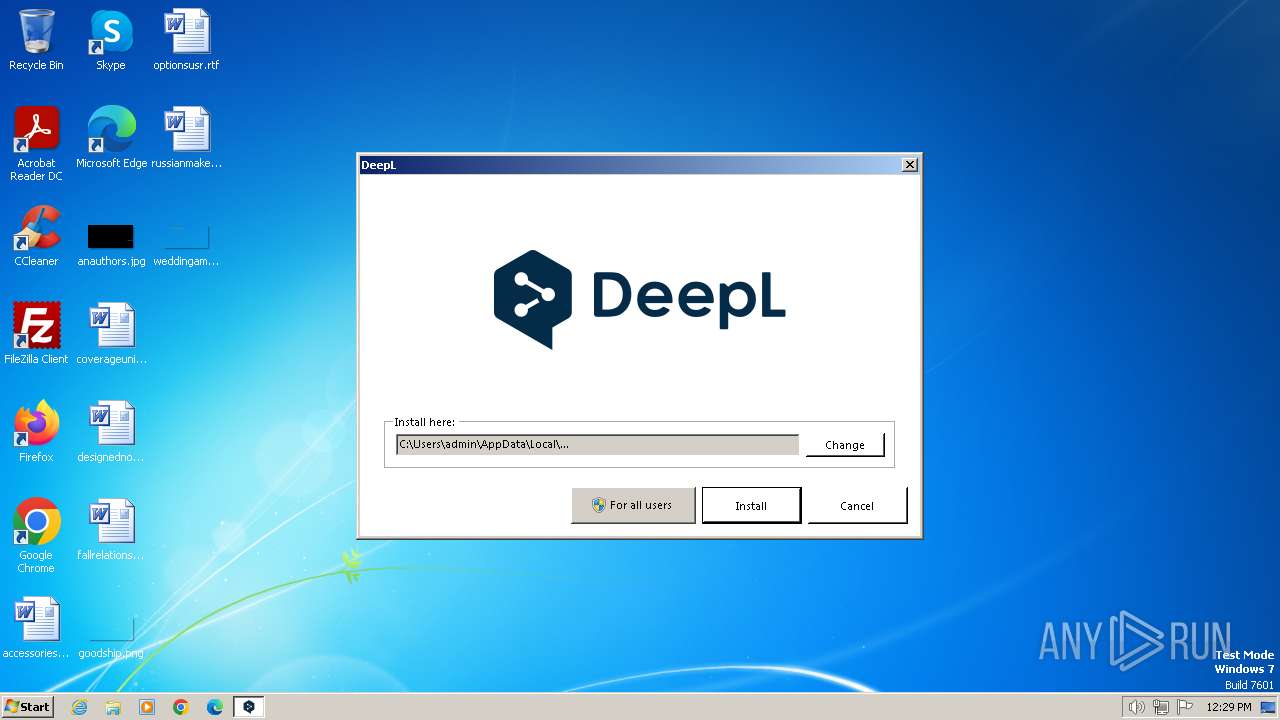
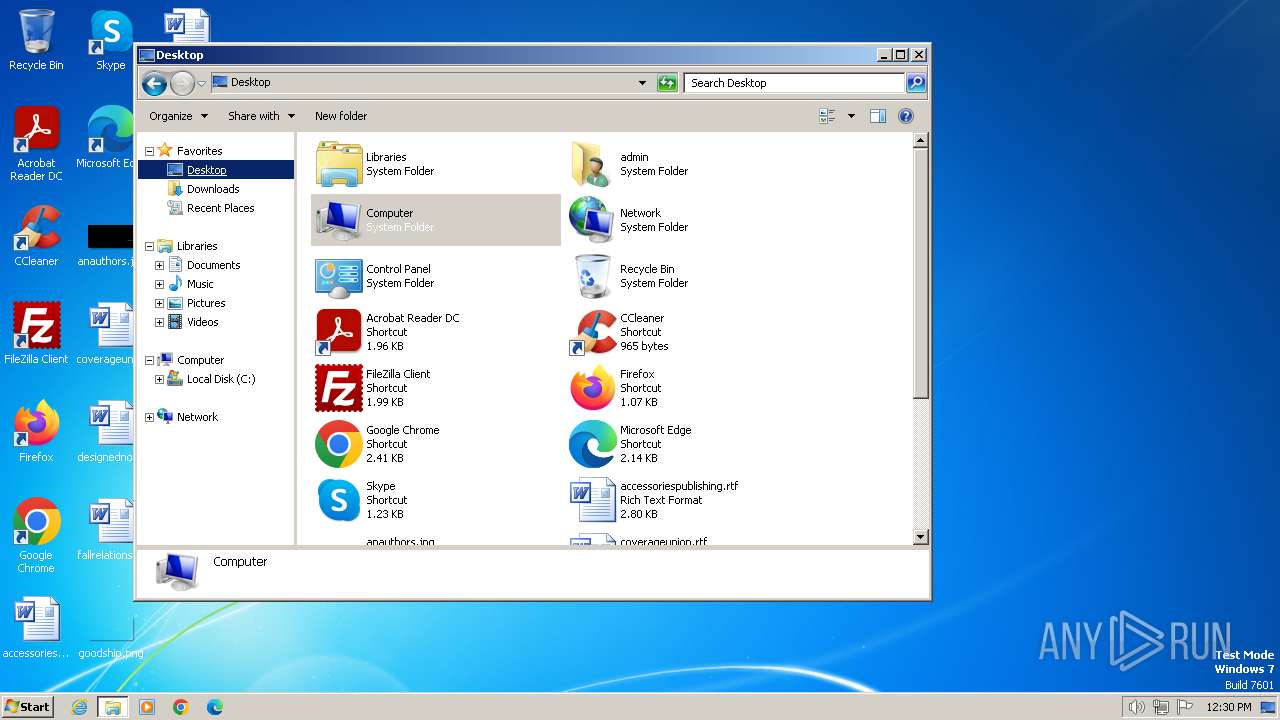
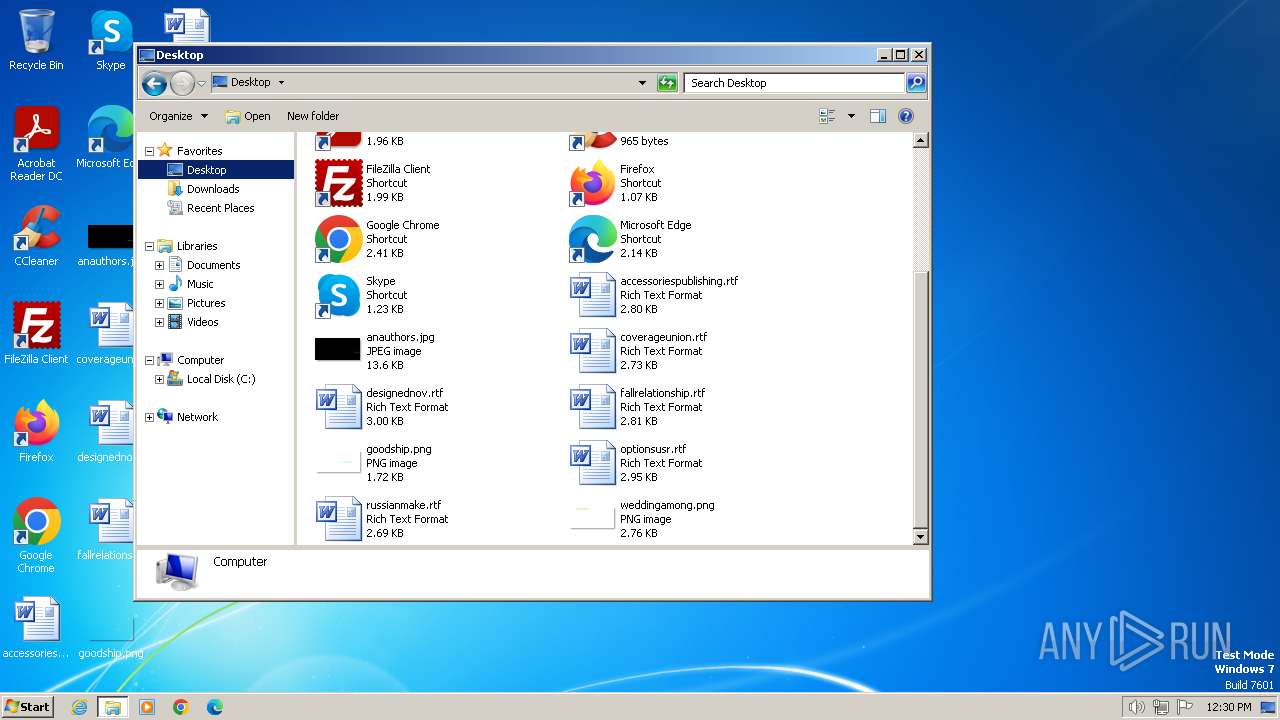
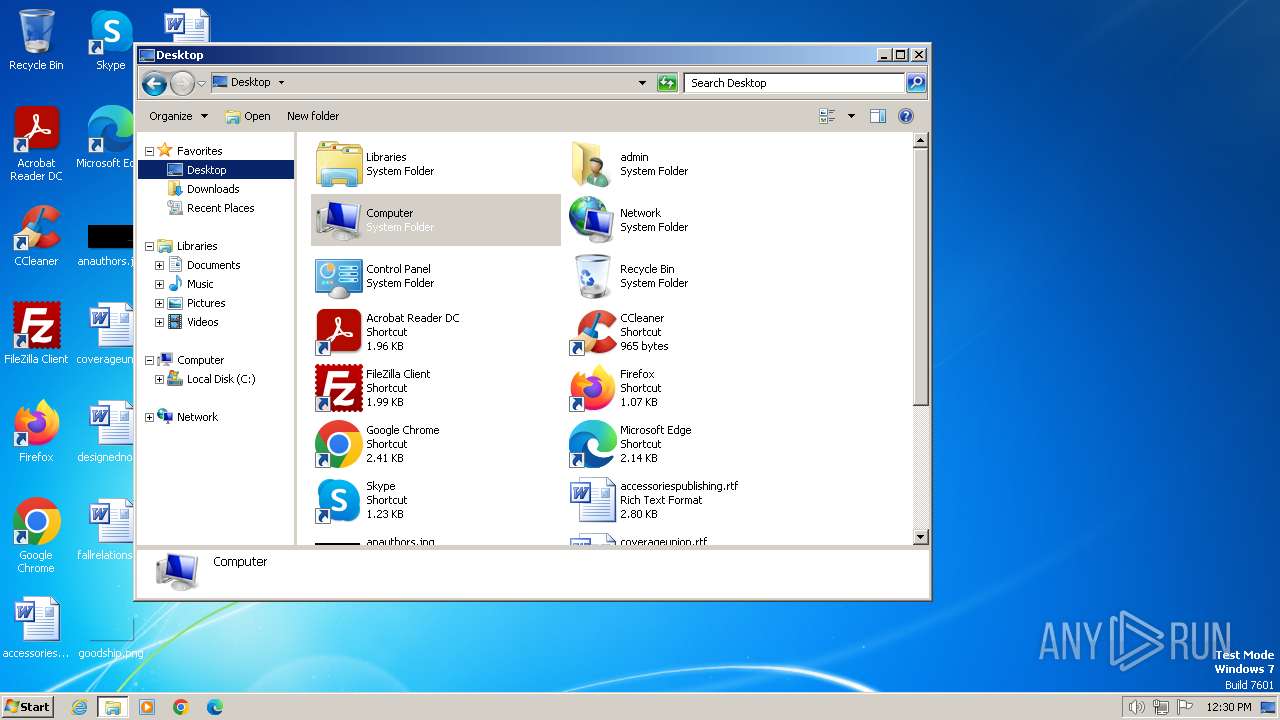
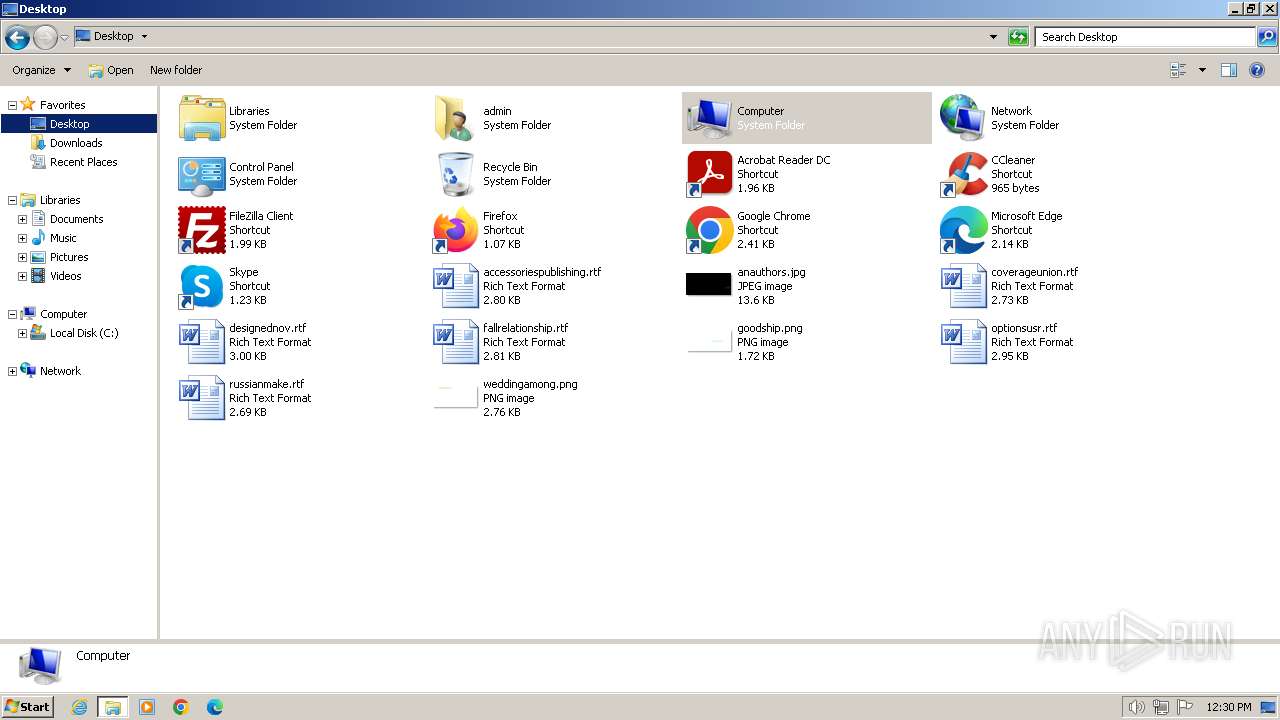
Manual execution by a user
- explorer.exe (PID: 2896)
- explorer.exe (PID: 3072)
Creates files or folders in the user directory
- DeepLSetup.exe (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1988:11:04 23:02:06+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 4291584 |
| InitializedDataSize: | 111616 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x419a9e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Downloads and runs the DeepL app. |
| CompanyName: | DeepLSetup |
| FileDescription: | DeepLSetup |
| FileVersion: | 1.0.0.0 |
| InternalName: | DeepLSetup.exe |
| LegalCopyright: | |
| OriginalFileName: | DeepLSetup.exe |
| ProductName: | DeepL |
| ProductVersion: | 1.0.0-pre+67d1e9668593497f29ca1526a7a37fdc85c23c06 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2896 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3072 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4008 | "C:\Users\admin\AppData\Local\Temp\DeepLSetup.exe" | C:\Users\admin\AppData\Local\Temp\DeepLSetup.exe | explorer.exe | ||||||||||||
User: admin Company: DeepLSetup Integrity Level: MEDIUM Description: DeepLSetup Exit code: 10 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
4 042
Read events
4 028
Write events
14
Delete events
0
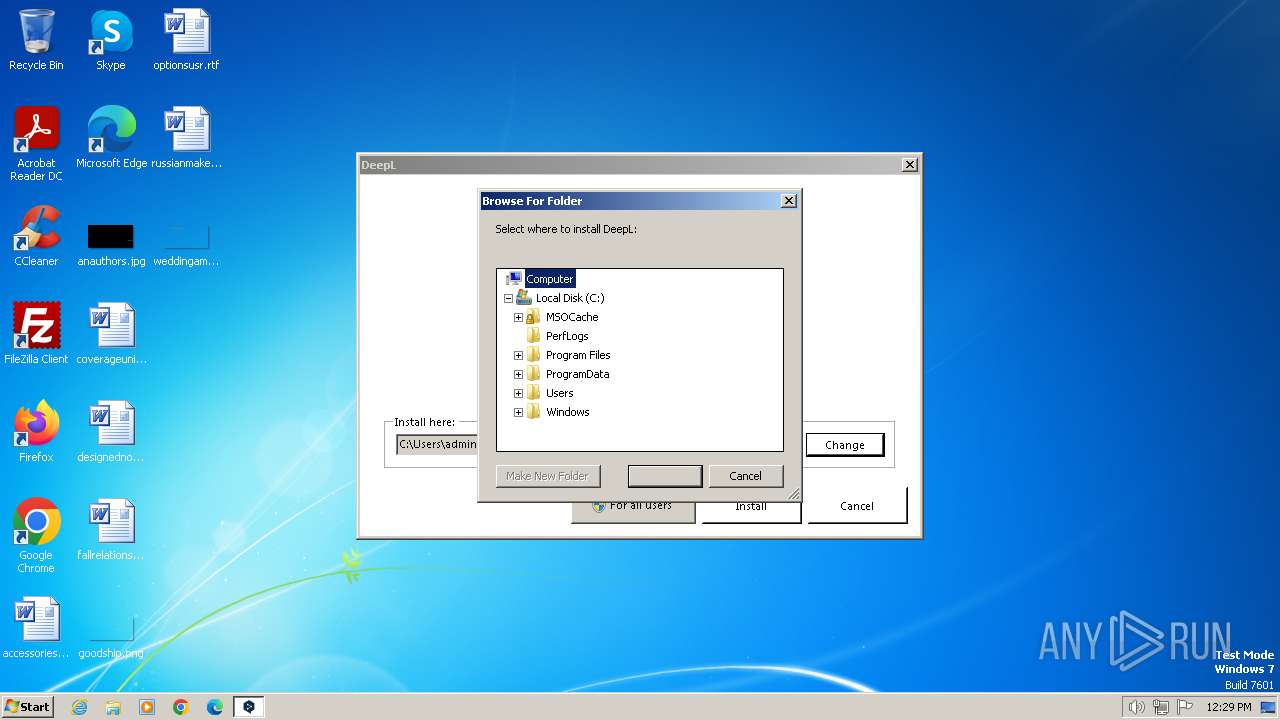
Modification events
| (PID) Process: | (4008) DeepLSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (4008) DeepLSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (4008) DeepLSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepLSetup_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4008) DeepLSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepLSetup_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4008) DeepLSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepLSetup_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4008) DeepLSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepLSetup_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4008) DeepLSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepLSetup_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4008) DeepLSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepLSetup_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (4008) DeepLSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepLSetup_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4008) DeepLSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DeepLSetup_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
7
Unknown types
1
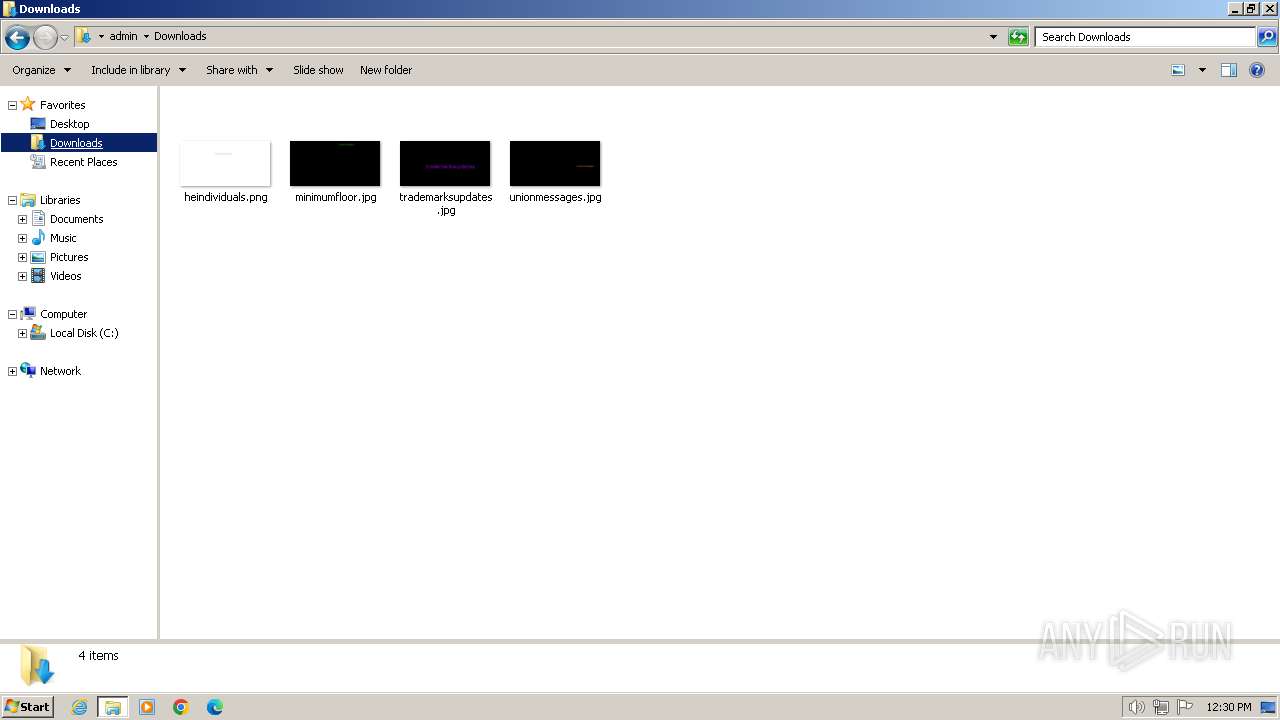
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
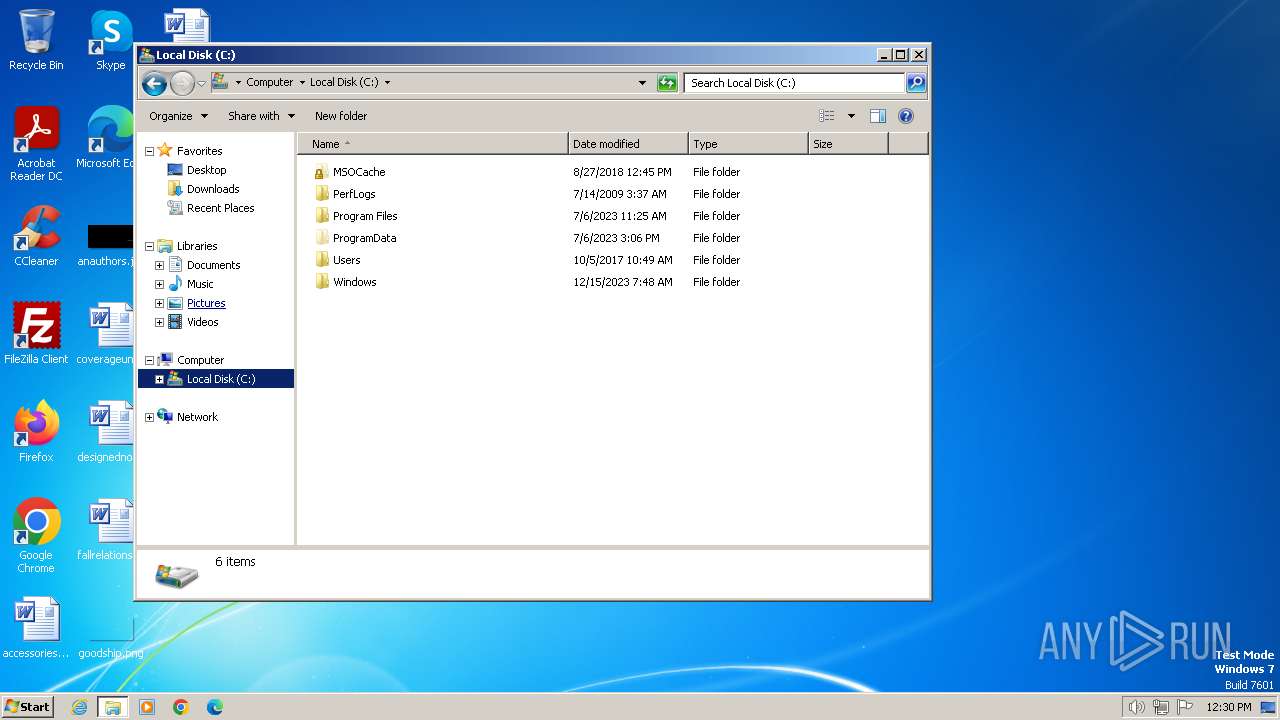
| 4008 | DeepLSetup.exe | C:\Users\admin\AppData\Local\0install.net\implementations\psdg3l02.t2h | binary | |
MD5:— | SHA256:— | |||
| 4008 | DeepLSetup.exe | C:\Users\admin\AppData\Roaming\0install.net\injector\implementation-dirs | — | |
MD5:— | SHA256:— | |||
| 4008 | DeepLSetup.exe | C:\Users\admin\AppData\Roaming\0install.net\injector\temp.o1b54u1o.qf3.global | text | |
MD5:— | SHA256:— | |||
| 4008 | DeepLSetup.exe | C:\Users\admin\AppData\Roaming\0install.net\injector\global | text | |
MD5:— | SHA256:— | |||
| 4008 | DeepLSetup.exe | C:\Users\admin\AppData\Roaming\0install.net\temp.r0dxjofw.rdz.catalog-sources | text | |
MD5:— | SHA256:— | |||
| 4008 | DeepLSetup.exe | C:\Users\admin\AppData\Roaming\0install.net\catalog-sources | text | |
MD5:— | SHA256:— | |||
| 4008 | DeepLSetup.exe | C:\Users\admin\AppData\Roaming\0install.net\injector\temp.swrwtx2b.4vj.trustdb.xml | xml | |
MD5:— | SHA256:— | |||
| 4008 | DeepLSetup.exe | C:\Users\admin\AppData\Roaming\0install.net\injector\trustdb.xml | xml | |
MD5:— | SHA256:— | |||
| 4008 | DeepLSetup.exe | C:\Users\admin\AppData\Local\Temp\DeepLSetup admin Log.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
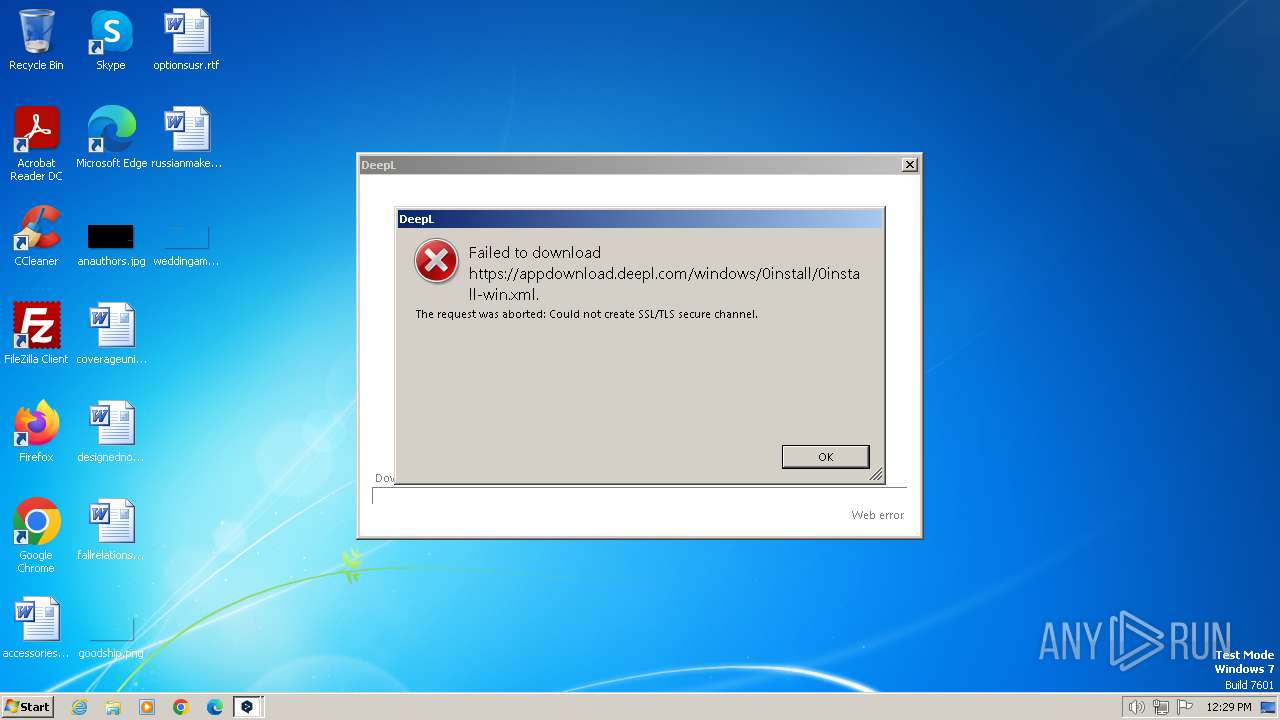
4008 | DeepLSetup.exe | 172.64.151.134:443 | appdownload.deepl.com | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
appdownload.deepl.com |
| unknown |