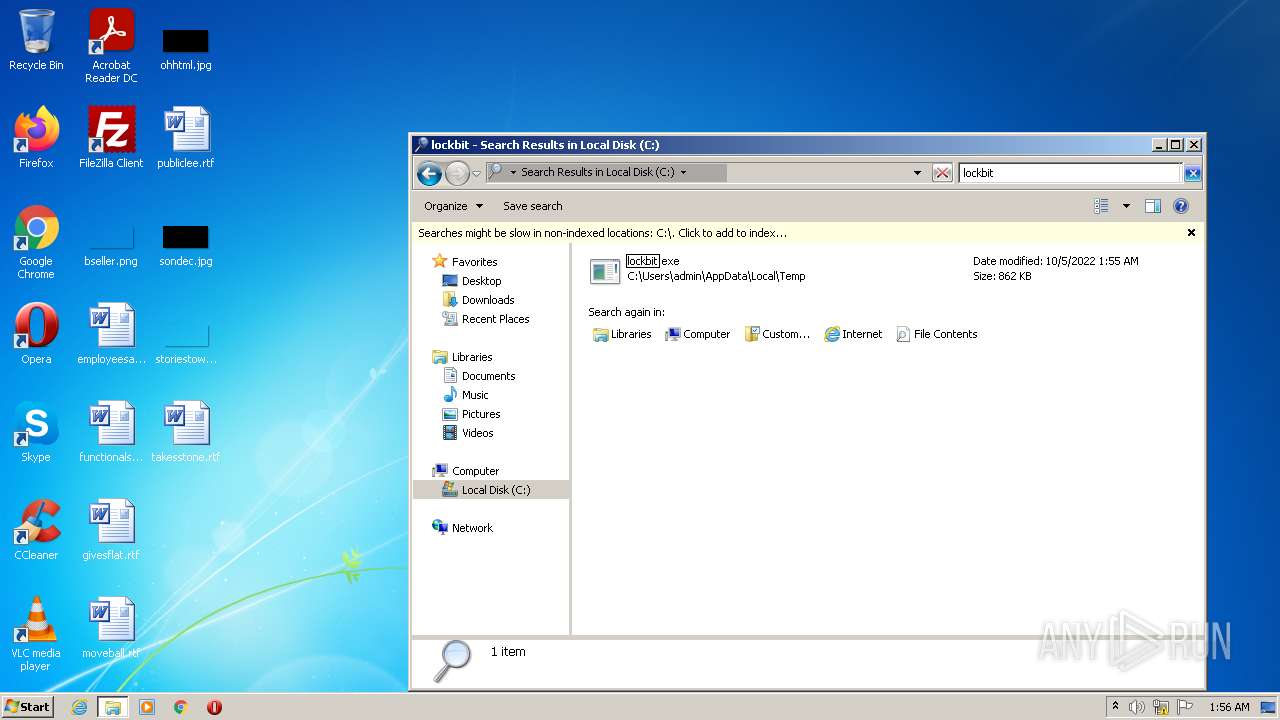
| File name: | lockbit |
| Full analysis: | https://app.any.run/tasks/d3c537cf-67af-4f8f-99d7-ac4291f29028 |
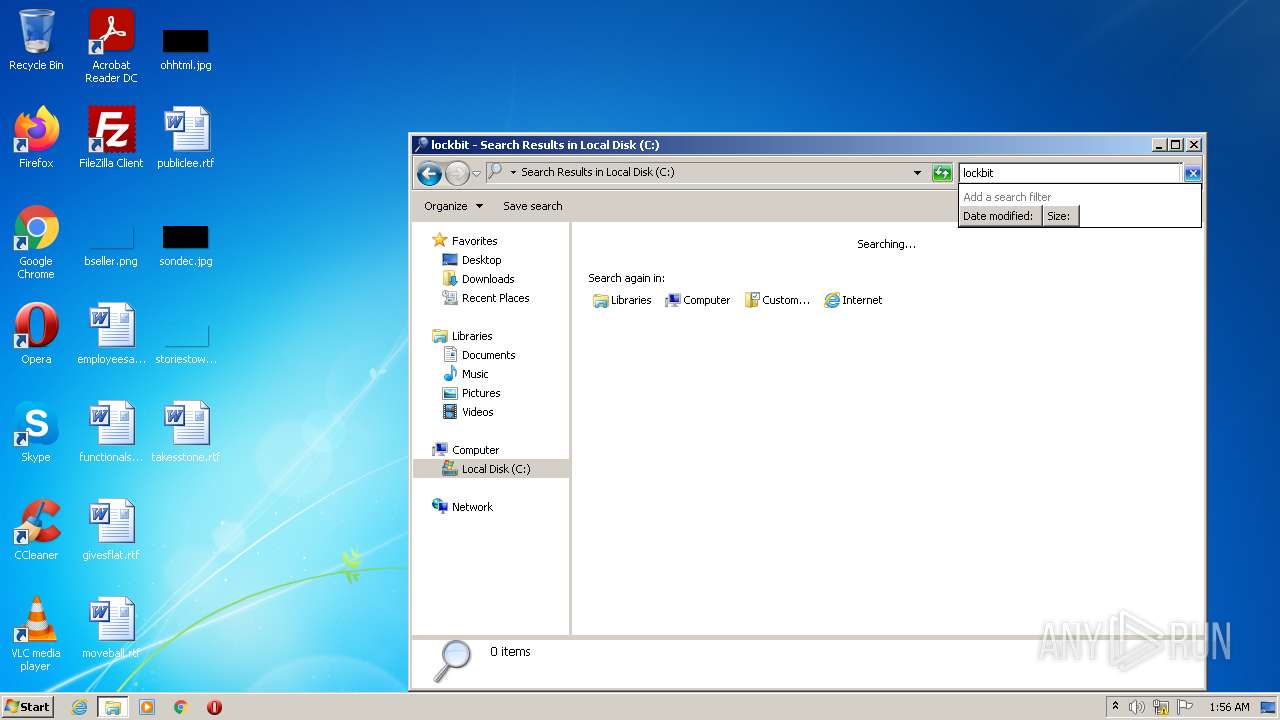
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 00:55:12 |
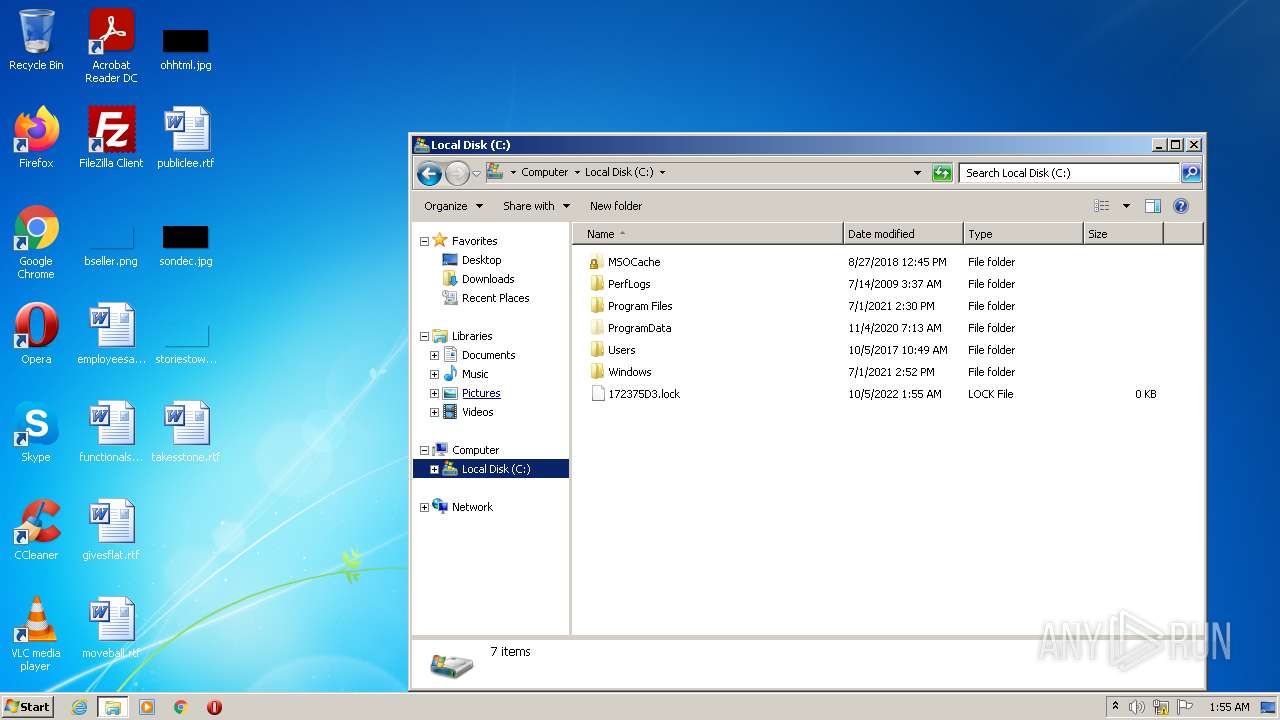
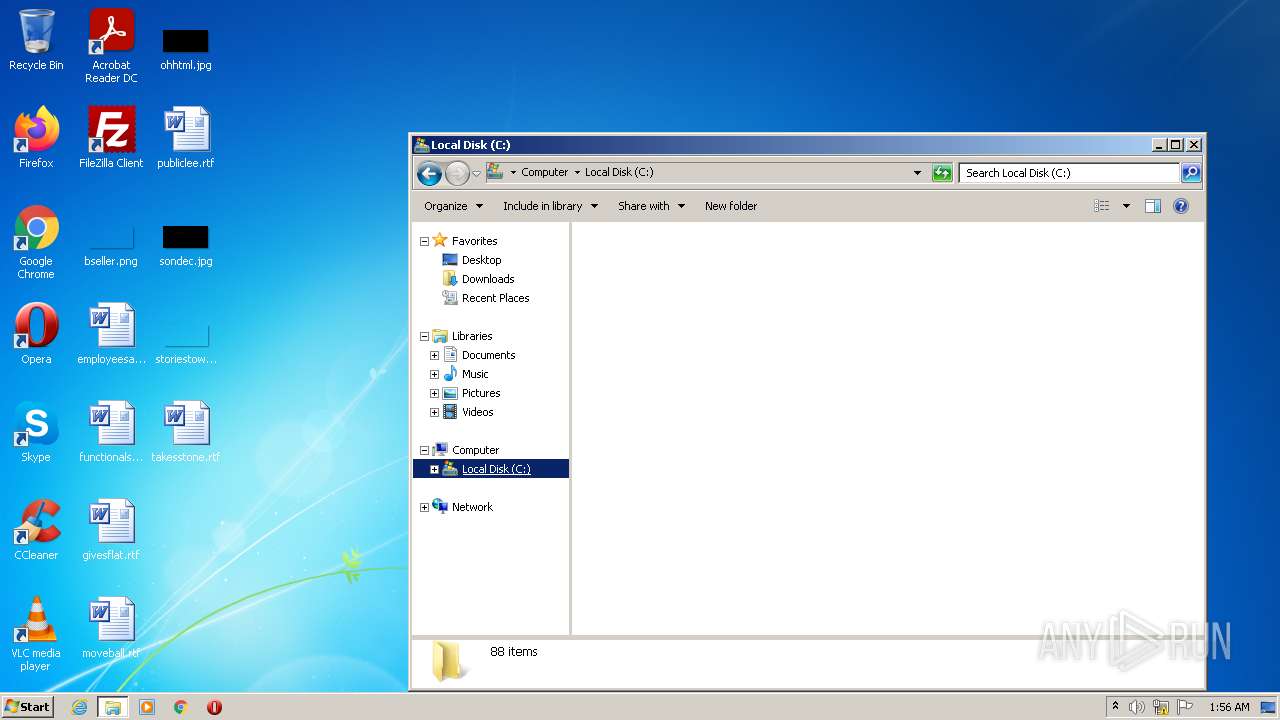
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 96DE05212B30EC85D4CF03386C1B84AF |
| SHA1: | DBE5243C6EA5CC4CFB3EDF042BD94A59CF9A0E64 |
| SHA256: | 00260C390FFAB5734208A7199DF0E4229A76261C3F5B7264C4515ACB8EB9C2F8 |
| SSDEEP: | 24576:DxAf2NuubB6RWspgjuwu7pl4Ha+UmxJH+Q9F:dAfSrWW4g+7Ht+UmxJe6 |
MALICIOUS
Changes the autorun value in the registry
- lockbit.exe (PID: 2736)
Drops executable file immediately after starts
- lockbit.exe (PID: 2736)
Deletes shadow copies
- cmd.exe (PID: 2412)
- cmd.exe (PID: 3964)
- cmd.exe (PID: 3504)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 1152)
- cmd.exe (PID: 3492)
- cmd.exe (PID: 2412)
SUSPICIOUS
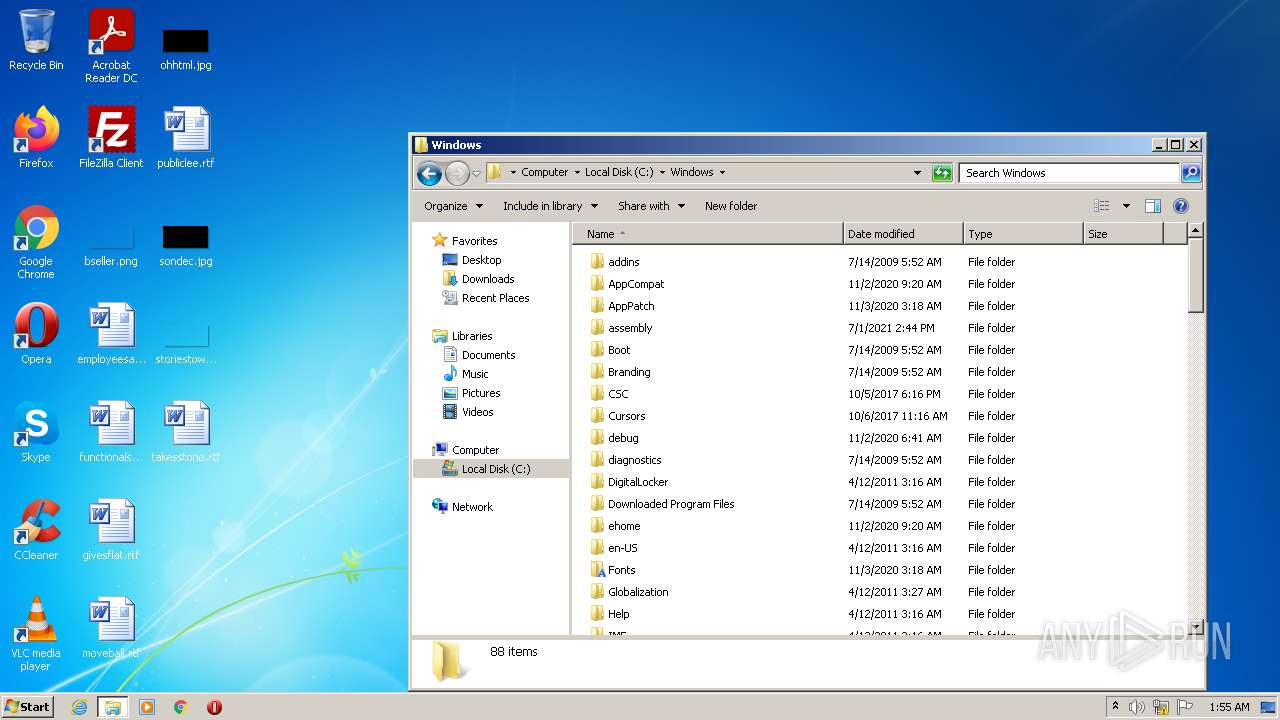
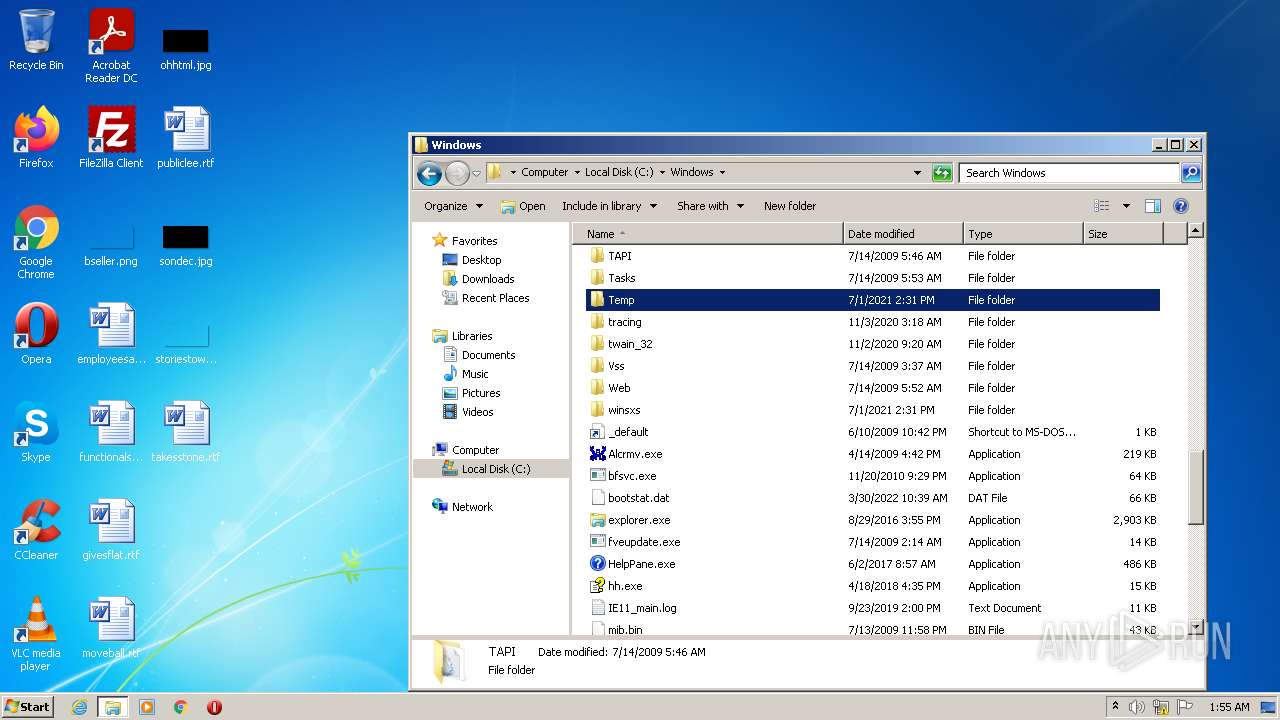
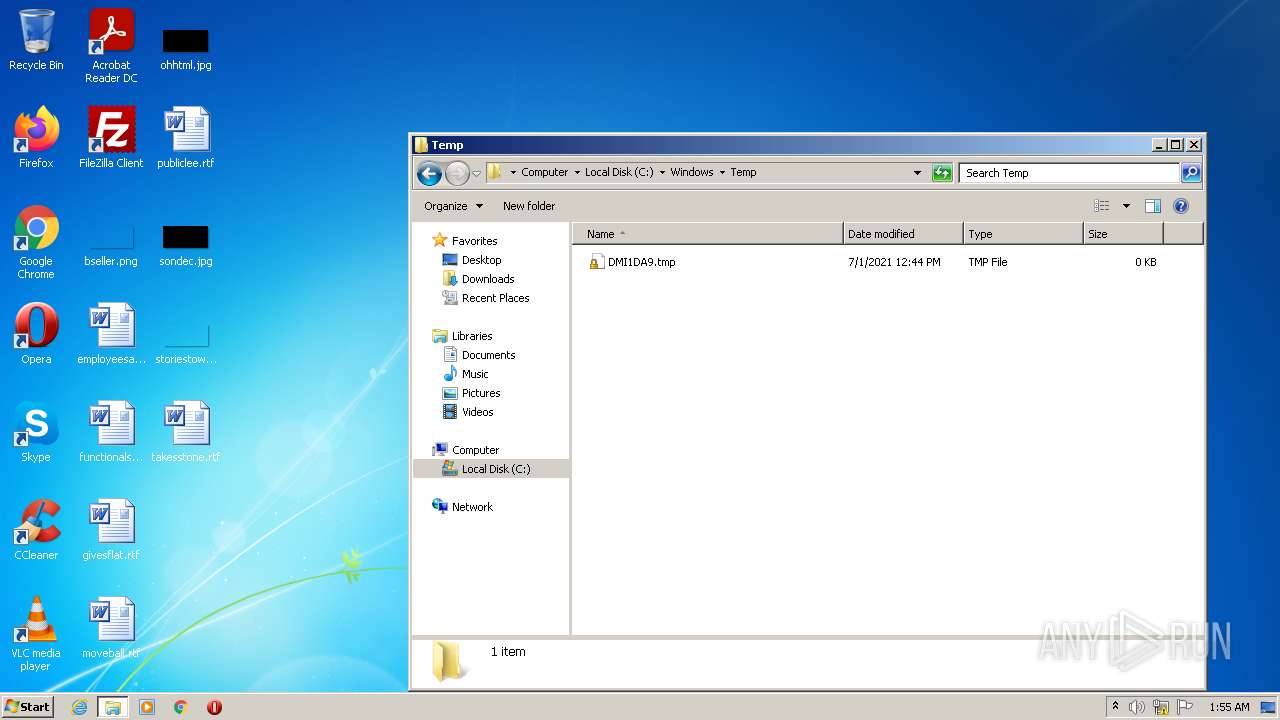
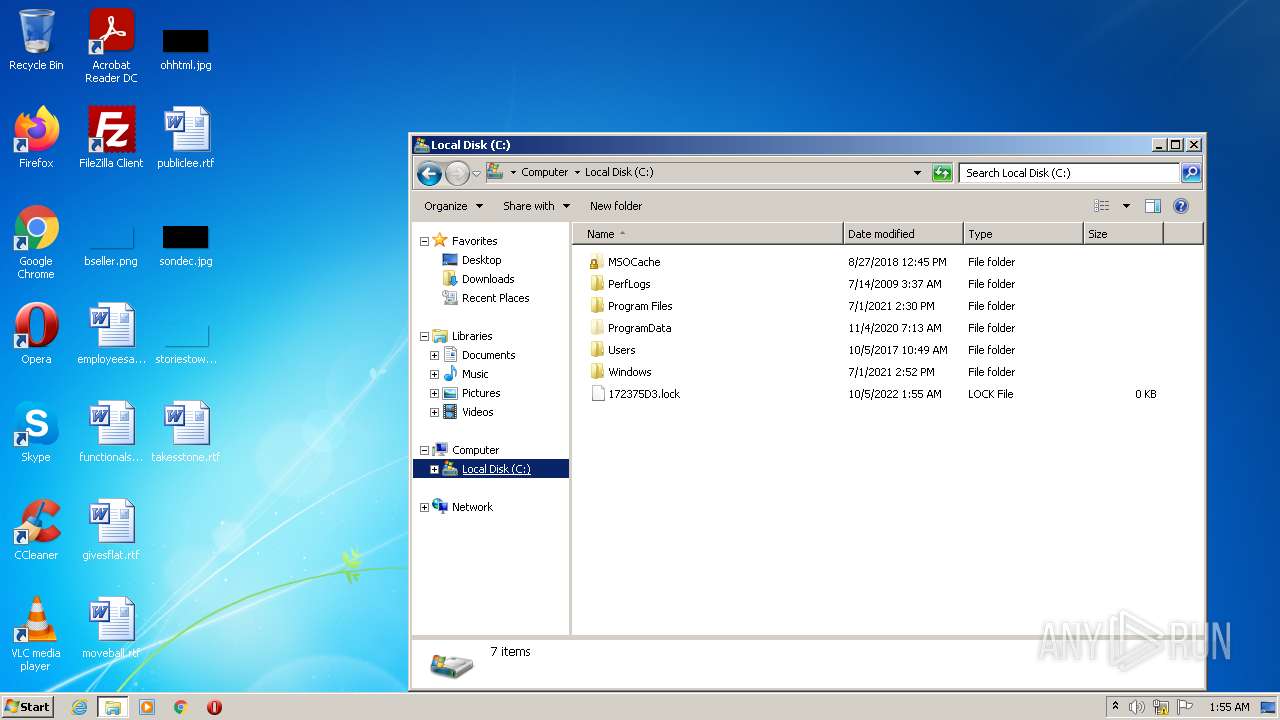
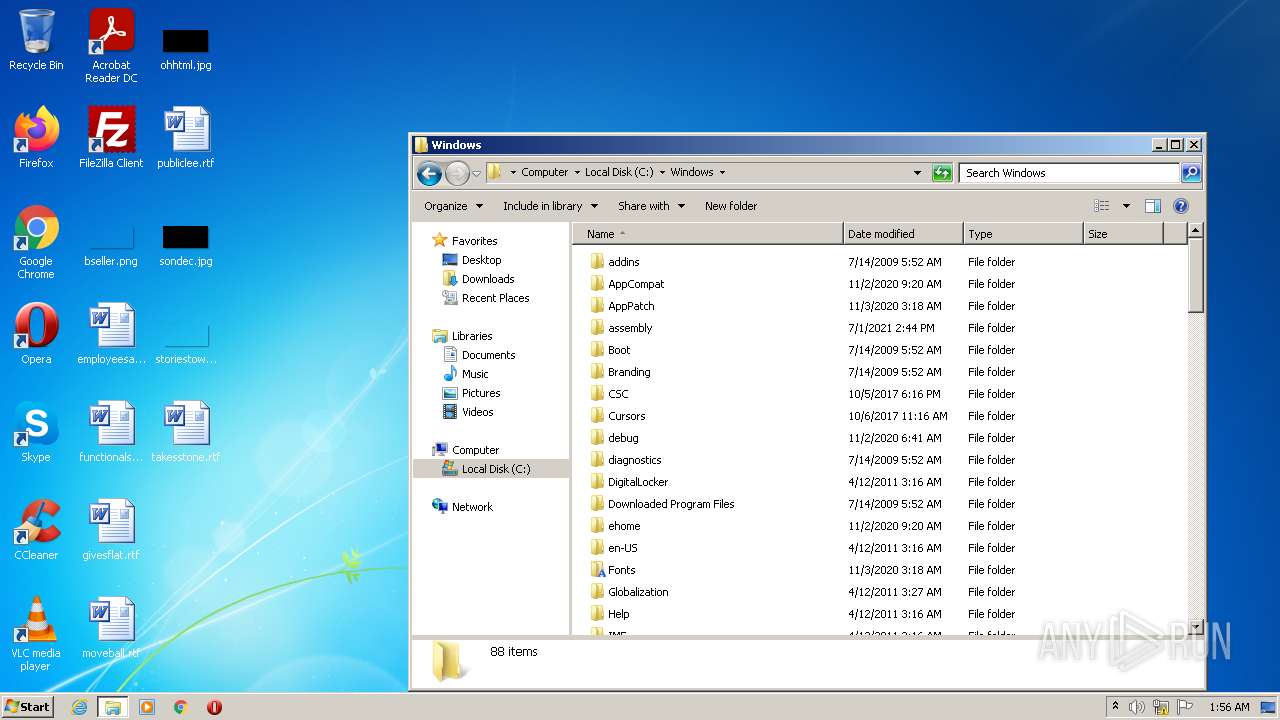
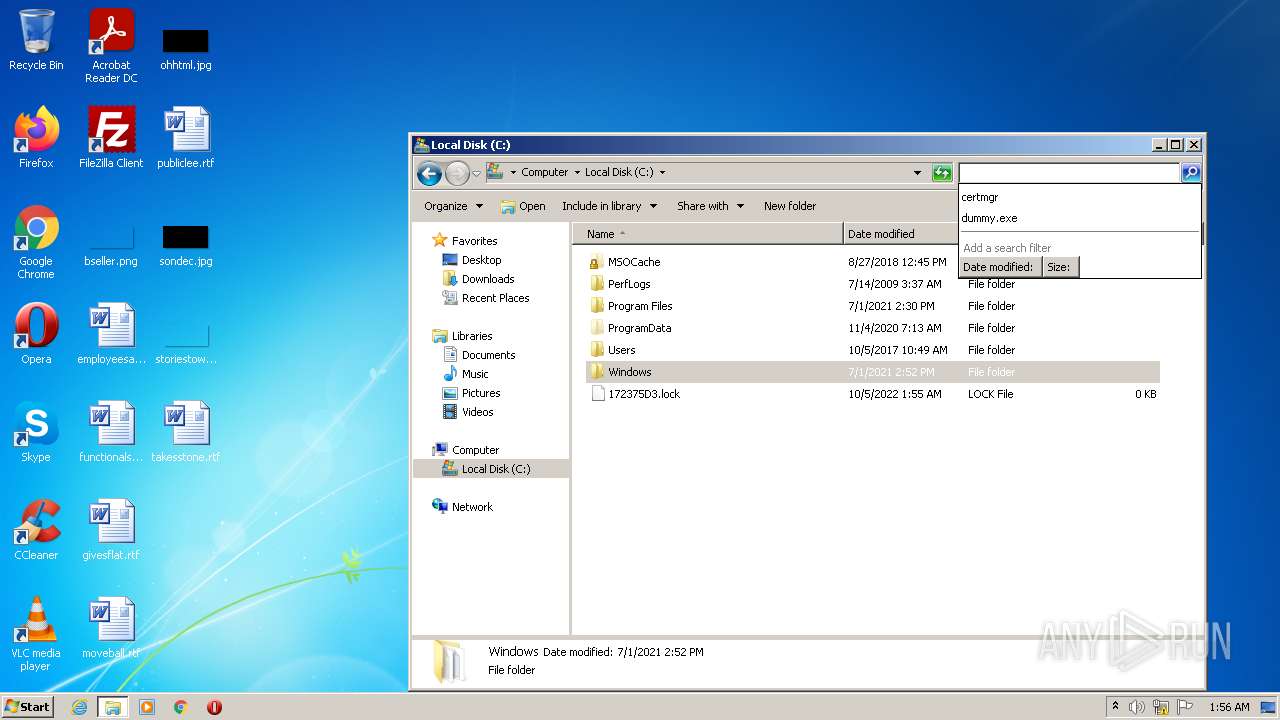
Creates files in the Windows directory
- lockbit.exe (PID: 2736)
Executed via COM
- DllHost.exe (PID: 3568)
- DllHost.exe (PID: 2096)
- DllHost.exe (PID: 4036)
- DllHost.exe (PID: 2904)
Checks supported languages
- lockbit.exe (PID: 560)
- lockbit.exe (PID: 2736)
- cmd.exe (PID: 2412)
- lockbit.exe (PID: 3160)
- lockbit.exe (PID: 1332)
Reads the computer name
- lockbit.exe (PID: 560)
- lockbit.exe (PID: 2736)
- lockbit.exe (PID: 3160)
Drops a file with a compile date too recent
- lockbit.exe (PID: 2736)
Starts CMD.EXE for commands execution
- lockbit.exe (PID: 2736)
Executed as Windows Service
- vssvc.exe (PID: 3528)
Uses WEVTUTIL.EXE to clean Windows Eventlog
- cmd.exe (PID: 3328)
- cmd.exe (PID: 3044)
- cmd.exe (PID: 3648)
- cmd.exe (PID: 2744)
- cmd.exe (PID: 3740)
- cmd.exe (PID: 1256)
Creates files in the program directory
- lockbit.exe (PID: 2736)
INFO
Checks supported languages
- DllHost.exe (PID: 3568)
- DllHost.exe (PID: 2096)
- explorer.exe (PID: 2276)
- vssadmin.exe (PID: 3316)
- DllHost.exe (PID: 4036)
- DllHost.exe (PID: 2904)
- vssvc.exe (PID: 3528)
- bcdedit.exe (PID: 1096)
- cmd.exe (PID: 3964)
- vssadmin.exe (PID: 2272)
- cmd.exe (PID: 1152)
- bcdedit.exe (PID: 2668)
- WMIC.exe (PID: 2984)
- cmd.exe (PID: 1340)
- cmd.exe (PID: 2832)
- WMIC.exe (PID: 3656)
- cmd.exe (PID: 3044)
- wevtutil.exe (PID: 2300)
- cmd.exe (PID: 3648)
- wevtutil.exe (PID: 3928)
- cmd.exe (PID: 3328)
- wevtutil.exe (PID: 3908)
- cmd.exe (PID: 3492)
- WMIC.exe (PID: 3720)
- cmd.exe (PID: 2924)
- bcdedit.exe (PID: 1604)
- cmd.exe (PID: 3308)
- cmd.exe (PID: 1256)
- cmd.exe (PID: 3504)
- vssadmin.exe (PID: 2668)
- bcdedit.exe (PID: 2780)
- wevtutil.exe (PID: 3768)
- wevtutil.exe (PID: 2912)
- wevtutil.exe (PID: 3904)
- cmd.exe (PID: 3740)
- cmd.exe (PID: 2744)
- bcdedit.exe (PID: 3336)
- bcdedit.exe (PID: 2572)
Reads the computer name
- DllHost.exe (PID: 2096)
- DllHost.exe (PID: 3568)
- explorer.exe (PID: 2276)
- DllHost.exe (PID: 4036)
- DllHost.exe (PID: 2904)
- vssadmin.exe (PID: 3316)
- vssadmin.exe (PID: 2272)
- vssvc.exe (PID: 3528)
- wevtutil.exe (PID: 3908)
- WMIC.exe (PID: 3656)
- WMIC.exe (PID: 2984)
- wevtutil.exe (PID: 3928)
- WMIC.exe (PID: 3720)
- wevtutil.exe (PID: 2300)
- vssadmin.exe (PID: 2668)
- wevtutil.exe (PID: 3768)
- wevtutil.exe (PID: 3904)
- wevtutil.exe (PID: 2912)
Manual execution by user
- explorer.exe (PID: 2276)
- lockbit.exe (PID: 3160)
Dropped object may contain Bitcoin addresses
- lockbit.exe (PID: 2736)
Dropped object may contain TOR URL's
- lockbit.exe (PID: 2736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2021-Jul-09 14:54:27 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 216 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 2 |
| TimeDateStamp: | 2021-Jul-09 14:54:27 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 823283 | 823296 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59832 |
.data | 827392 | 93460 | 58880 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.77639 |
Total processes
107
Monitored processes
43
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Users\admin\AppData\Local\Temp\lockbit.exe" | C:\Users\admin\AppData\Local\Temp\lockbit.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1096 | bcdedit /set {default} recoveryenabled No | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1152 | /c bcdedit /set {default} recoveryenabled No | C:\Windows\system32\cmd.exe | — | lockbit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1256 | /c wevtutil cl security | C:\Windows\system32\cmd.exe | — | lockbit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1332 | "C:\Users\admin\AppData\Local\Temp\lockbit.exe" | C:\Users\admin\AppData\Local\Temp\lockbit.exe | — | DllHost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1340 | /c wmic SHADOWCOPY /nointeractive | C:\Windows\system32\cmd.exe | — | lockbit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 44124 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1604 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2096 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | vssadmin Delete Shadows /All /Quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2276 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 733
Read events
5 696
Write events
37
Delete events
0
Modification events
| (PID) Process: | (2096) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ICM\Calibration |
| Operation: | write | Name: | DisplayCalibrator |
Value: C:\Users\admin\AppData\Local\Temp\lockbit.exe | |||
| (PID) Process: | (3568) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3568) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3568) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3568) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2736) lockbit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | {AD2359D3-E3E3-40C5-BF5C-BFBC1DD0BDA} |
Value: "C:\Users\admin\AppData\Local\Temp\lockbit.exe" | |||
| (PID) Process: | (2736) lockbit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.lockbit\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: C:\windows\system32\172375.ico | |||
| (PID) Process: | (2736) lockbit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 101 | |||
| (PID) Process: | (2736) lockbit.exe | Key: | HKEY_CURRENT_USER\Software\172375D3E3B45C |
| Operation: | write | Name: | Private |
Value: 0DDB15CE38A80E5D800A56AE009F2931230460BA56CDB681C12EE0DFDA617703D075DB32D9E4B60BC10CC265DE58649B993CD9DE9C2048B4D8AA6731BE2B297EAE7DDF0DB53E7059C8E7121775B7774C0F1CCD85DE075FF30E29E76F3ABA4BCF9BBAFED4758878384B0F9C17CAB05072 | |||
| (PID) Process: | (2736) lockbit.exe | Key: | HKEY_CURRENT_USER\Software\172375D3E3B45C |
| Operation: | write | Name: | Public |
Value: A41164347761DF6688B88D49912AB7C1F61B42AF54754C84381BF178FEC6F20D | |||
Executable files
0
Suspicious files
6 099
Text files
1 391
Unknown types
175
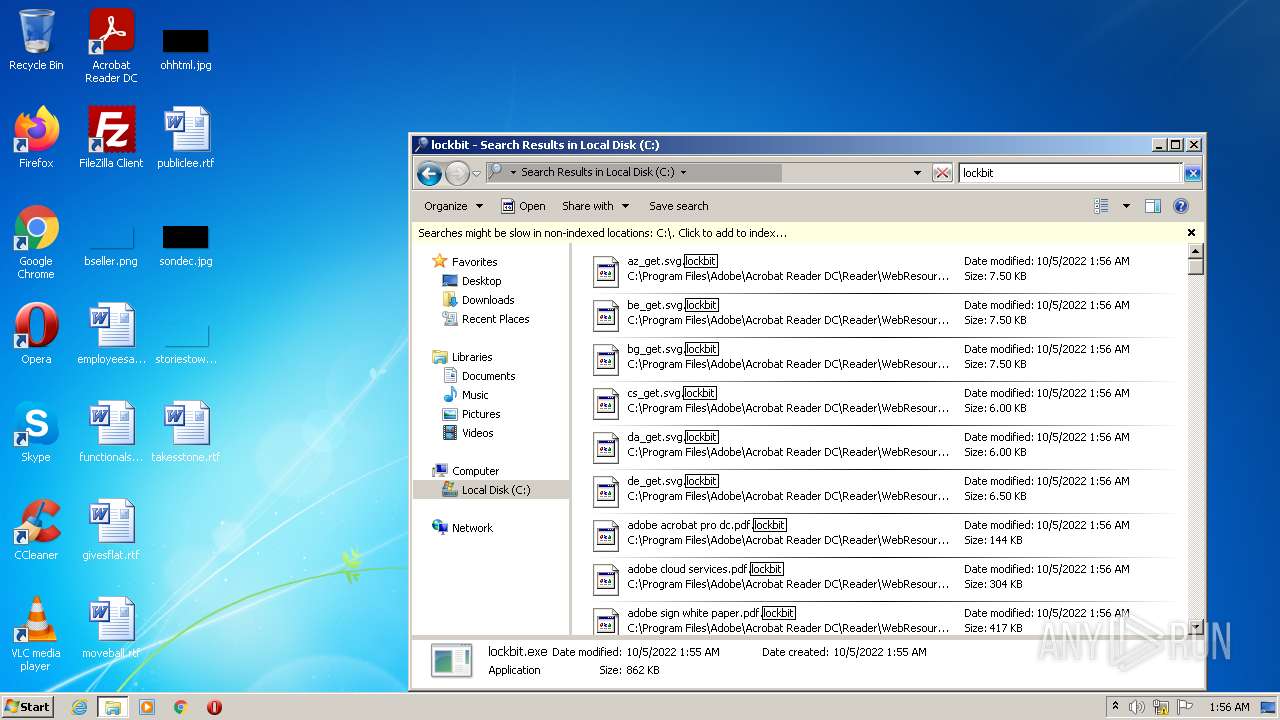
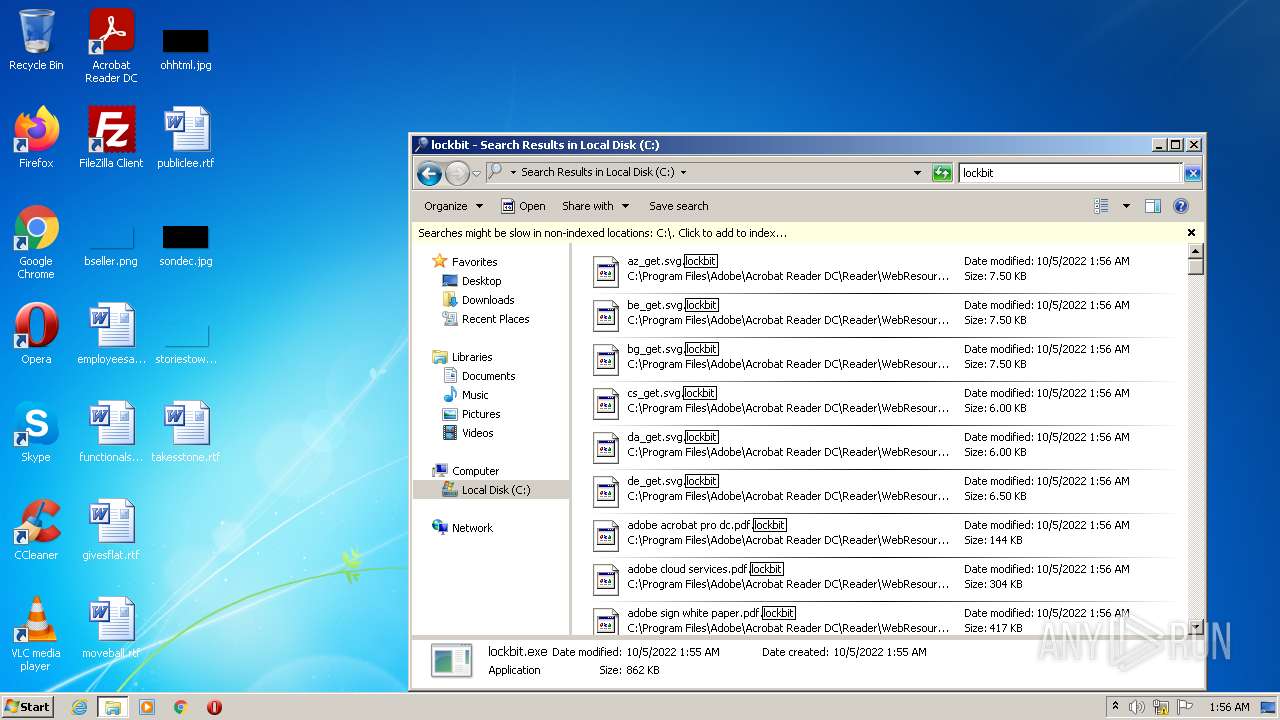
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2736 | lockbit.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\certificates_r.aapp.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2736 | lockbit.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\accessibility_r_rhp.aapp.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2736 | lockbit.exe | C:\program files\adobe\acrobat reader dc\reader\1494870c-9912-c184-4cc9-b401-a53f4d8de290.pdf | binary | |
MD5:— | SHA256:— | |||
| 2736 | lockbit.exe | C:\program files\adobe\acrobat reader dc\reader\acroapp\enu\actions_r_rhp.aapp | binary | |
MD5:— | SHA256:— | |||
| 2736 | lockbit.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\actions_r_rhp.aapp.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2736 | lockbit.exe | C:\program files\adobe\acrobat reader dc\reader\acroapp\enu\appcenter_r.aapp | binary | |
MD5:— | SHA256:— | |||
| 2736 | lockbit.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\collectsignatures.aapp.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2736 | lockbit.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\combine_r_rhp.aapp.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2736 | lockbit.exe | C:\program files\adobe\acrobat reader dc\reader\Restore-My-Files.txt | text | |
MD5:— | SHA256:— | |||
| 2736 | lockbit.exe | C:\program files\adobe\acrobat reader dc\reader\acroapp\enu\accessibility_r_rhp.aapp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.1:135 | — | — | — | unknown |
— | — | 192.168.100.1:445 | — | — | — | unknown |
— | — | 192.168.100.2:445 | — | — | — | whitelisted |
— | — | 192.168.100.2:135 | — | — | — | whitelisted |