| File name: | 02583427_2 |
| Full analysis: | https://app.any.run/tasks/f4c2f76e-5b9e-476e-be46-b06bd87e64ec |
| Verdict: | Malicious activity |
| Analysis date: | July 23, 2021, 02:32:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
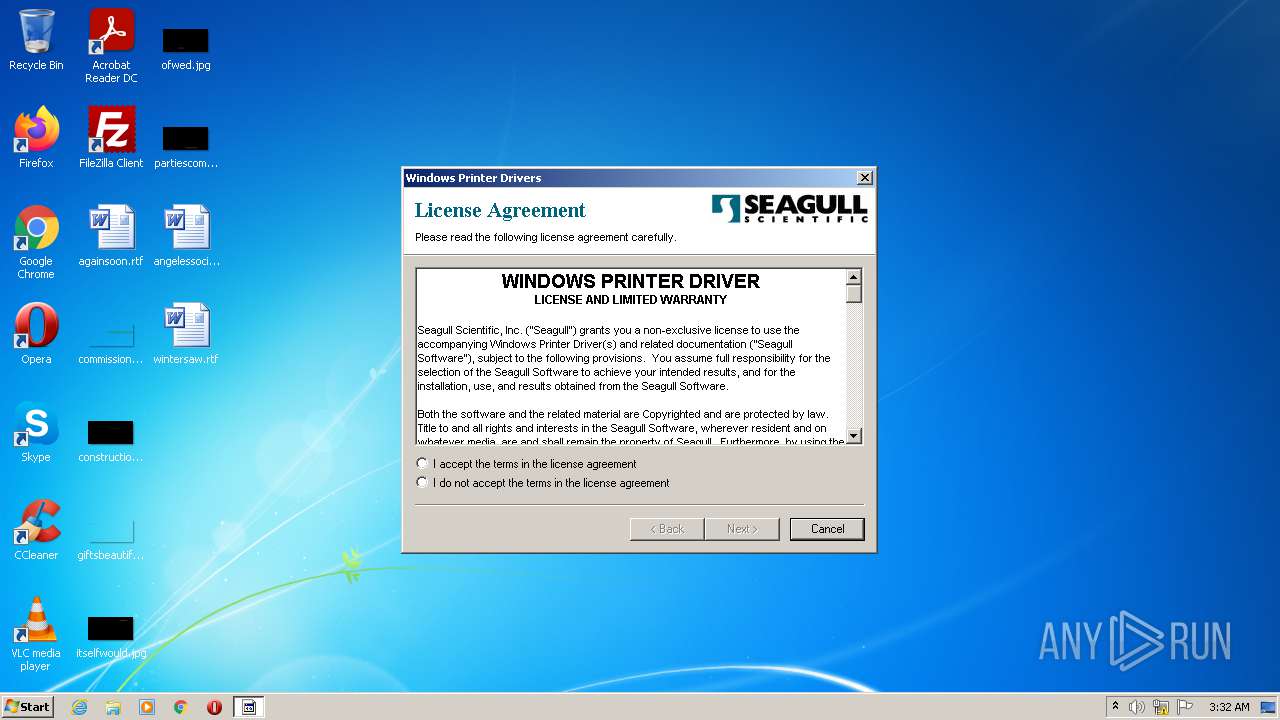
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | ECDDE080A535670684AB18EEB489F075 |
| SHA1: | 2891245FD3FB63BBF3703EF9536267B1BACB5D80 |
| SHA256: | 000ACD41B642E4E8239166E78156C4FE2A7C08A54C5D9BCA10DBE2AE1022AC52 |
| SSDEEP: | 393216:ol4kjQq9F2FZsTMF+rmQ/kRIhi5ulLH50vSodH9OYV:A4kaZof/kruz0vSouYV |
MALICIOUS
Drops executable file immediately after starts
- 02583427_2.exe (PID: 3996)
Application was dropped or rewritten from another process
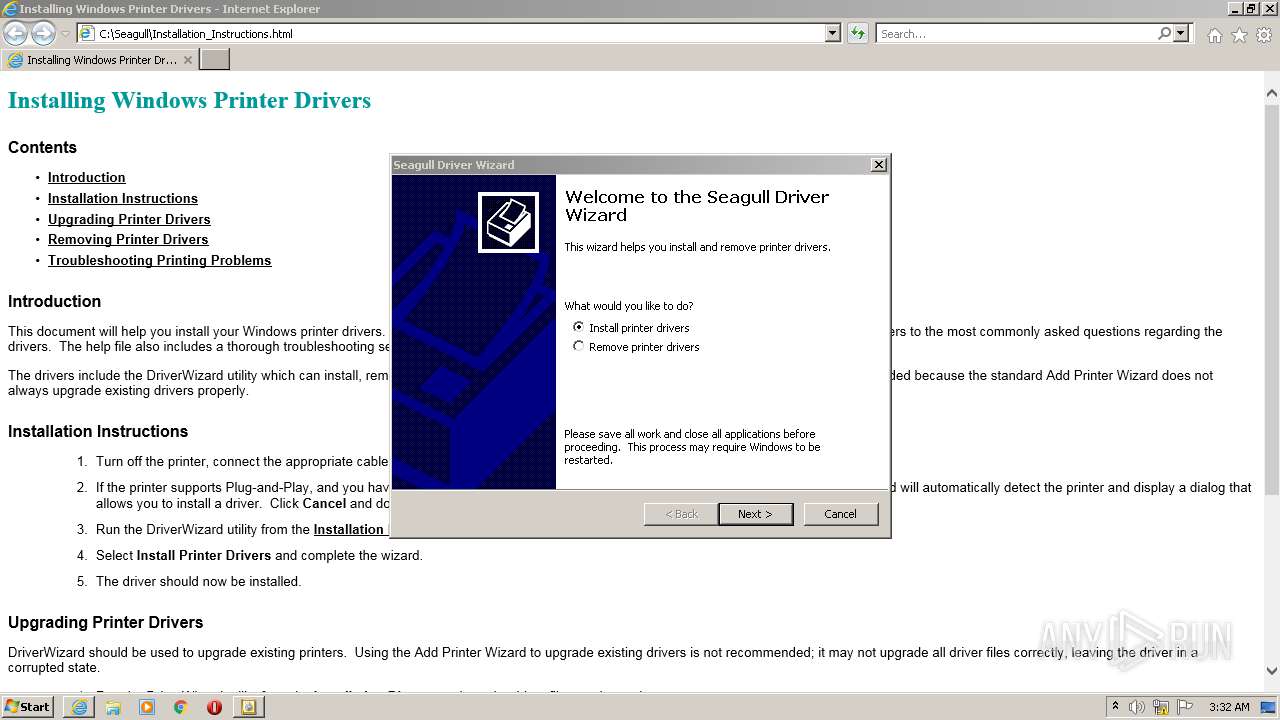
- __ExtractWizard.exe (PID: 4060)
- DriverWizard.exe (PID: 2992)
- DriverWizard.exe (PID: 1596)
Loads dropped or rewritten executable
- spoolsv.exe (PID: 2184)
- DriverWizard.exe (PID: 1596)
- regsvr32.exe (PID: 1516)
Registers / Runs the DLL via REGSVR32.EXE
- spoolsv.exe (PID: 2184)
Changes the autorun value in the registry
- spoolsv.exe (PID: 2184)
SUSPICIOUS
Checks supported languages
- 02583427_2.exe (PID: 3996)
- __ExtractWizard.exe (PID: 4060)
- DriverWizard.exe (PID: 1596)
Reads the computer name
- 02583427_2.exe (PID: 3996)
- DriverWizard.exe (PID: 1596)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3592)
Starts Internet Explorer
- 02583427_2.exe (PID: 3996)
Drops a file that was compiled in debug mode
- 02583427_2.exe (PID: 3996)
- spoolsv.exe (PID: 2184)
- DriverWizard.exe (PID: 1596)
Executable content was dropped or overwritten
- DriverWizard.exe (PID: 1596)
- spoolsv.exe (PID: 2184)
- 02583427_2.exe (PID: 3996)
Executed via COM
- rundll32.exe (PID: 2340)
Executed as Windows Service
- spoolsv.exe (PID: 2184)
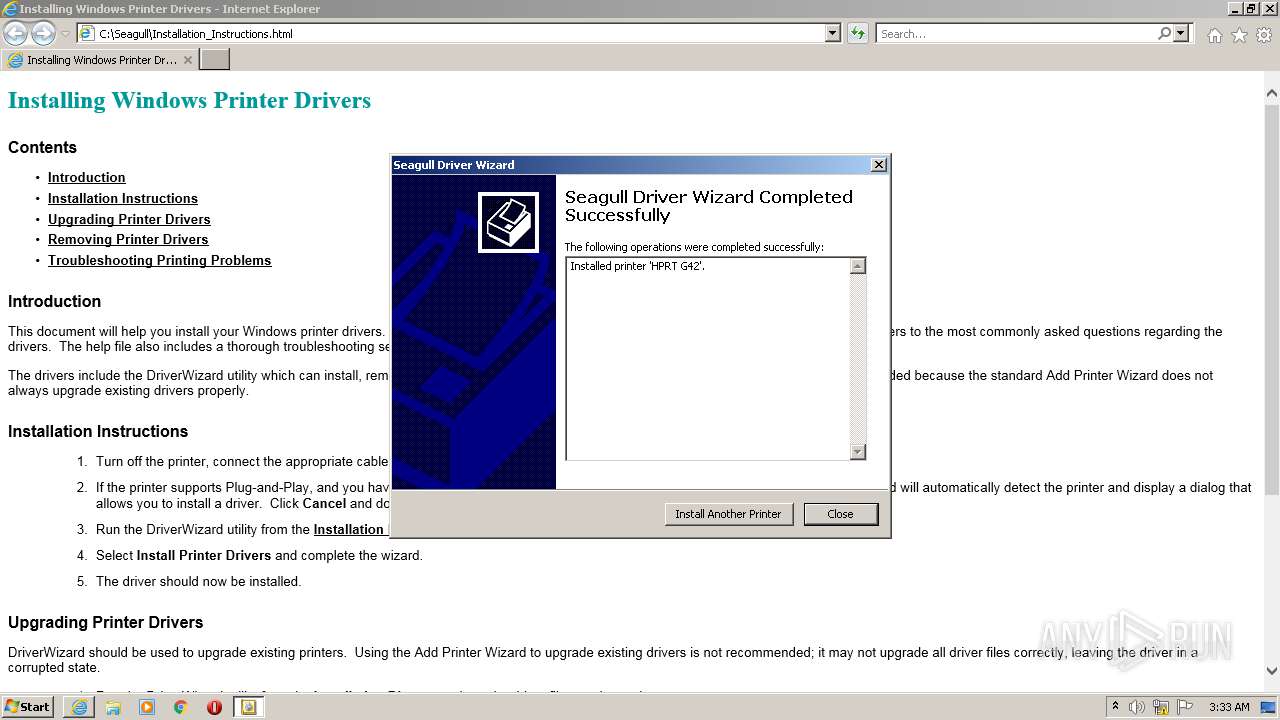
Creates files in the Windows directory
- DriverWizard.exe (PID: 1596)
- spoolsv.exe (PID: 2184)
Drops a file with too old compile date
- spoolsv.exe (PID: 2184)
Uses NETSH.EXE for network configuration
- spoolsv.exe (PID: 2184)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1516)
Creates files in the program directory
- spoolsv.exe (PID: 2184)
Reads Environment values
- netsh.exe (PID: 1820)
INFO
Checks supported languages
- iexplore.exe (PID: 968)
- iexplore.exe (PID: 3592)
- iexplore.exe (PID: 4092)
- rundll32.exe (PID: 2340)
- spoolsv.exe (PID: 2184)
- regsvr32.exe (PID: 1516)
- netsh.exe (PID: 1820)
Application launched itself
- iexplore.exe (PID: 968)
- iexplore.exe (PID: 3592)
Reads the computer name
- iexplore.exe (PID: 968)
- iexplore.exe (PID: 3592)
- iexplore.exe (PID: 4092)
- spoolsv.exe (PID: 2184)
- netsh.exe (PID: 1820)
Changes internet zones settings
- iexplore.exe (PID: 968)
Reads internet explorer settings
- iexplore.exe (PID: 3592)
Checks Windows Trust Settings
- iexplore.exe (PID: 968)
Dropped object may contain Bitcoin addresses
- spoolsv.exe (PID: 2184)
Reads settings of System Certificates
- iexplore.exe (PID: 968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0xb3a1 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 41984 |
| CodeSize: | 84992 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2015:06:23 02:55:41+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Jun-2015 00:55:41 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 23-Jun-2015 00:55:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00014B03 | 0x00014C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62044 |
.rdata | 0x00016000 | 0x000030F2 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.52444 |
.data | 0x0001A000 | 0x00005908 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29875 |
.rsrc | 0x00020000 | 0x00005DC4 | 0x00005E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.62687 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93543 | 482 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.30673 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.23159 | 7336 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.16906 | 3240 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.4328 | 872 | Latin 1 / Western European | UNKNOWN | RT_ICON |
12 | 3.8933 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
13 | 4.58672 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
14 | 4.64602 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.73738 | 76 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
103 | 3.34115 | 308 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
50
Monitored processes
11
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
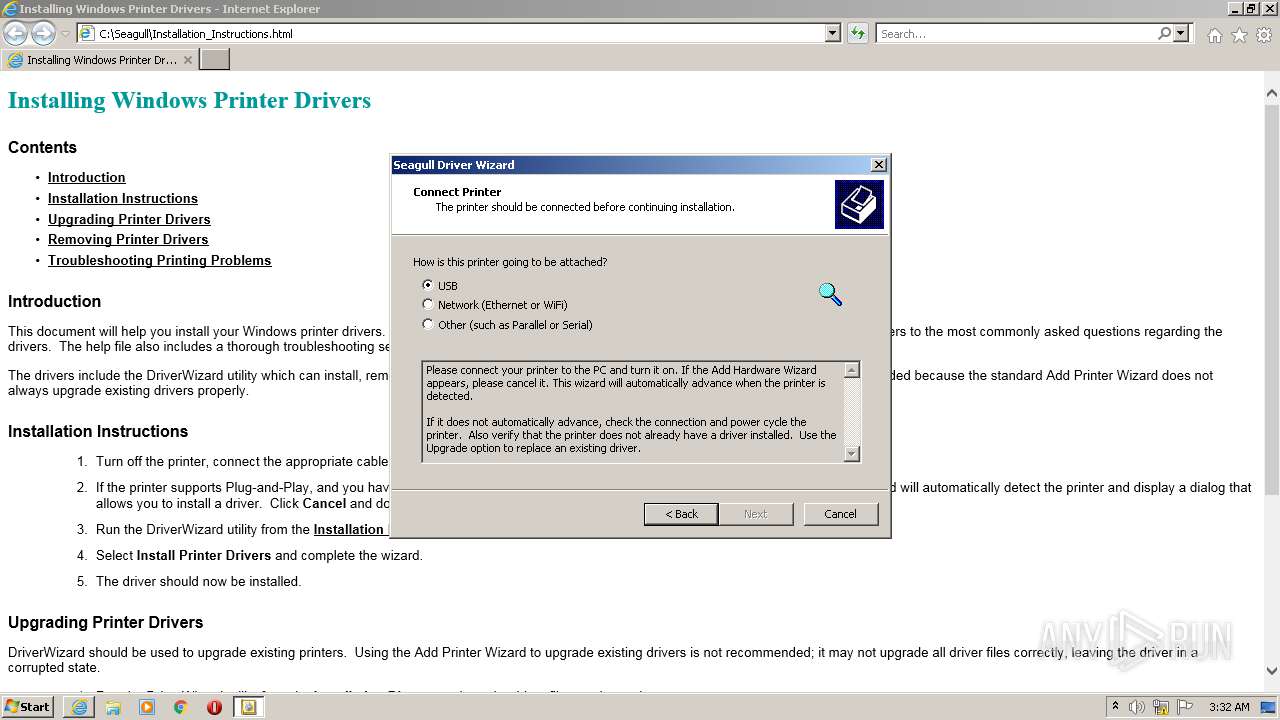
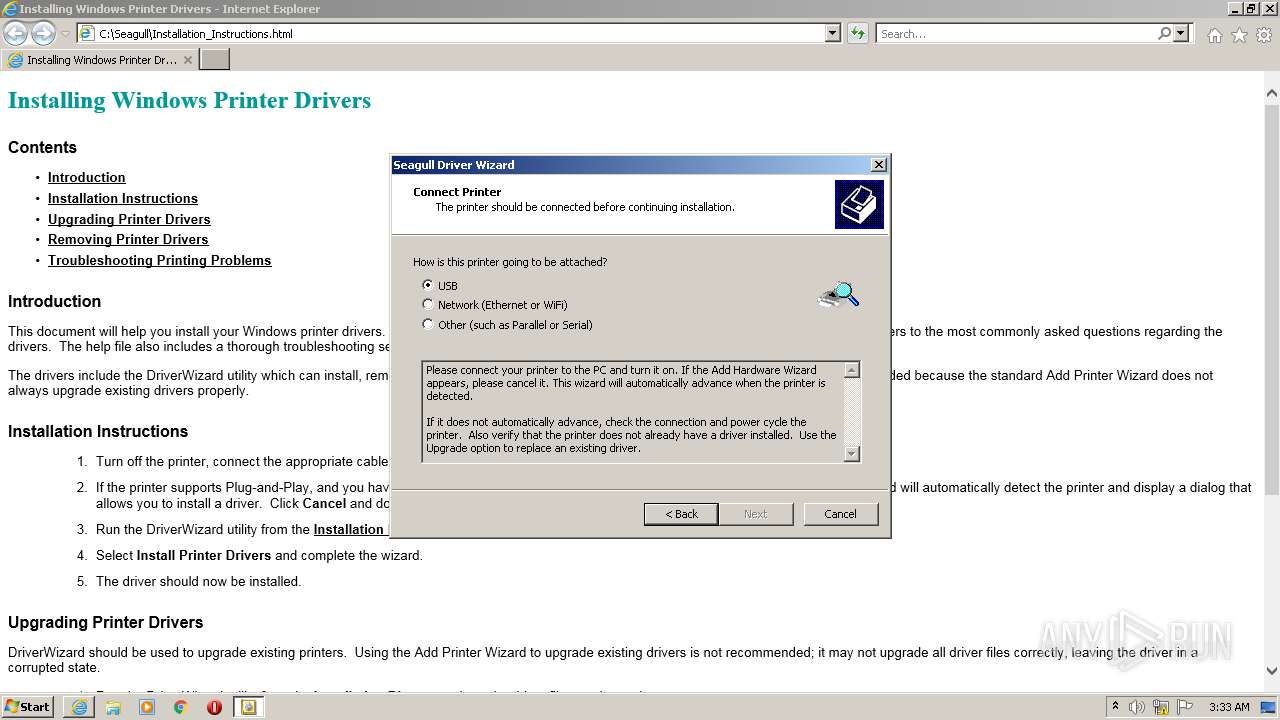
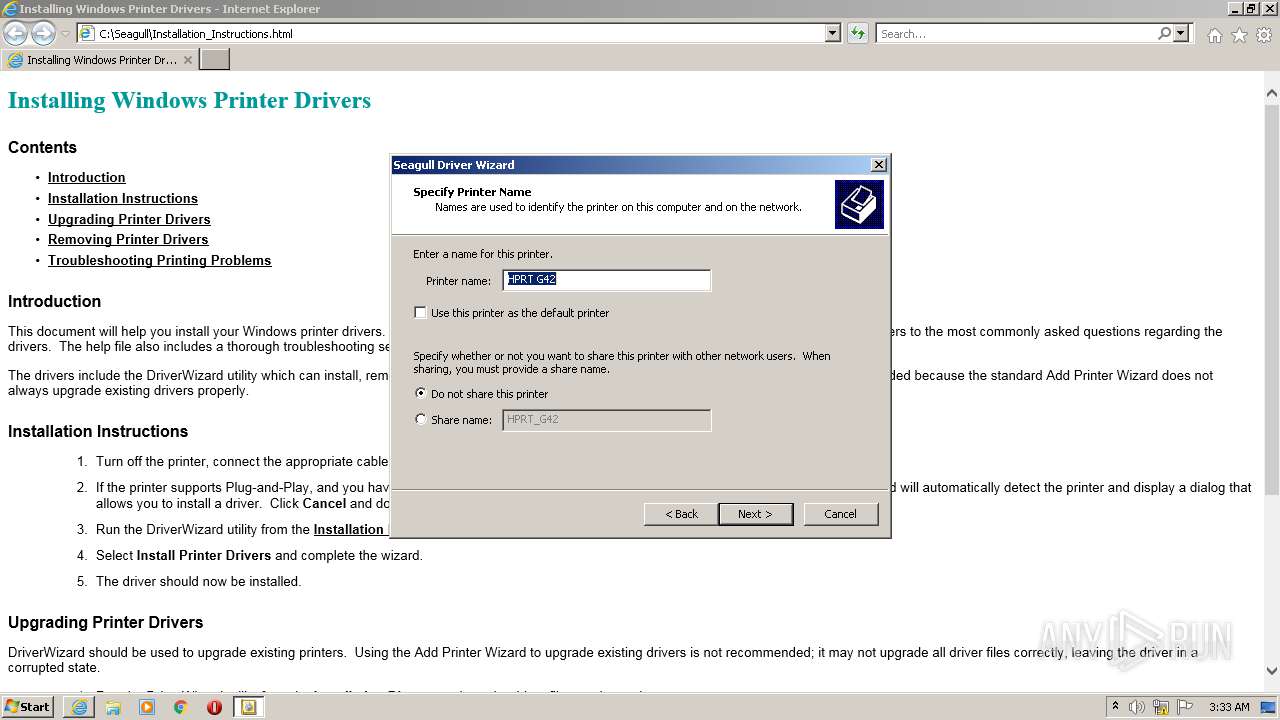
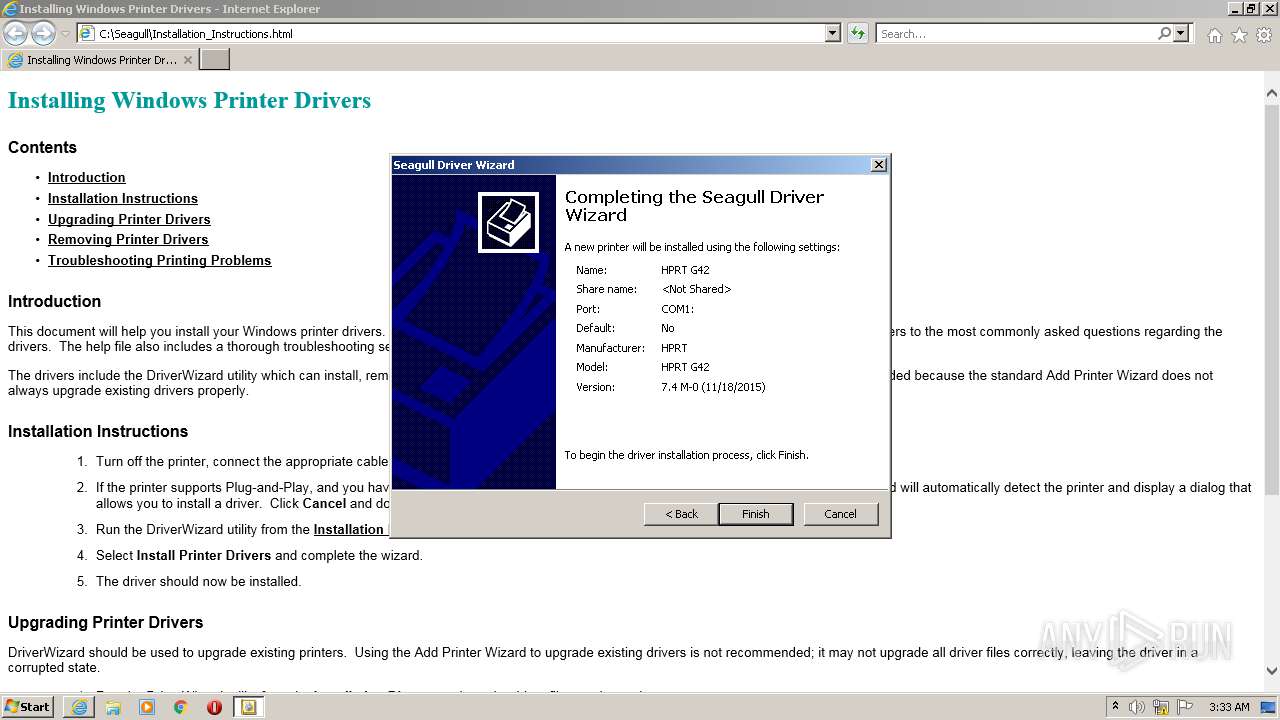
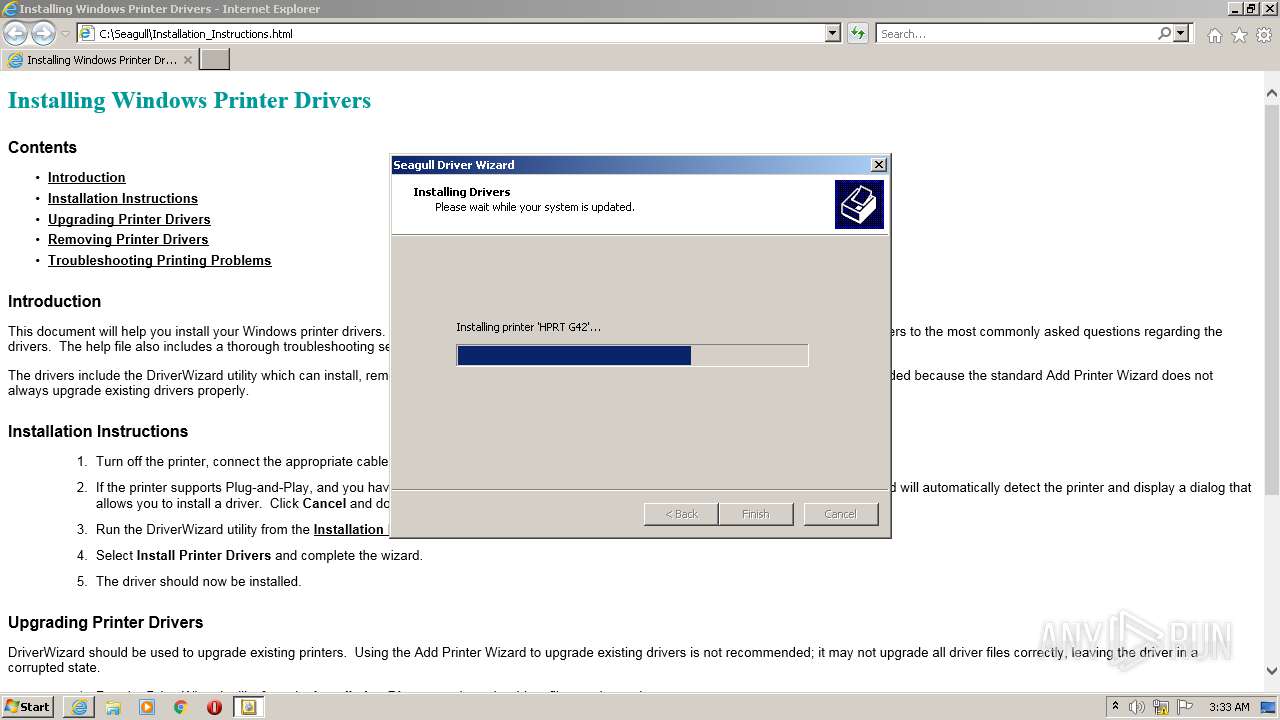
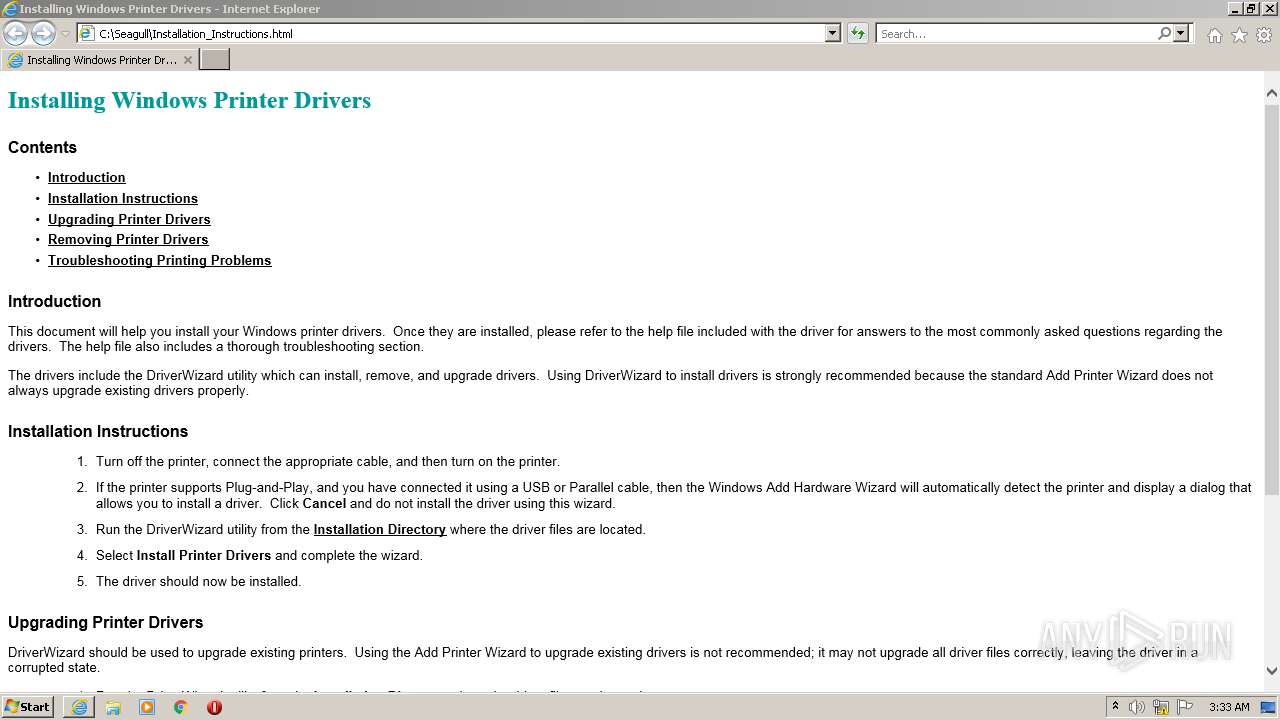
| 968 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Seagull\Installation_Instructions.html | C:\Program Files\Internet Explorer\iexplore.exe | 02583427_2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1516 | regsvr32.exe /s /c DriverAutomationLibrary.dll | C:\Windows\System32\regsvr32.exe | — | spoolsv.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
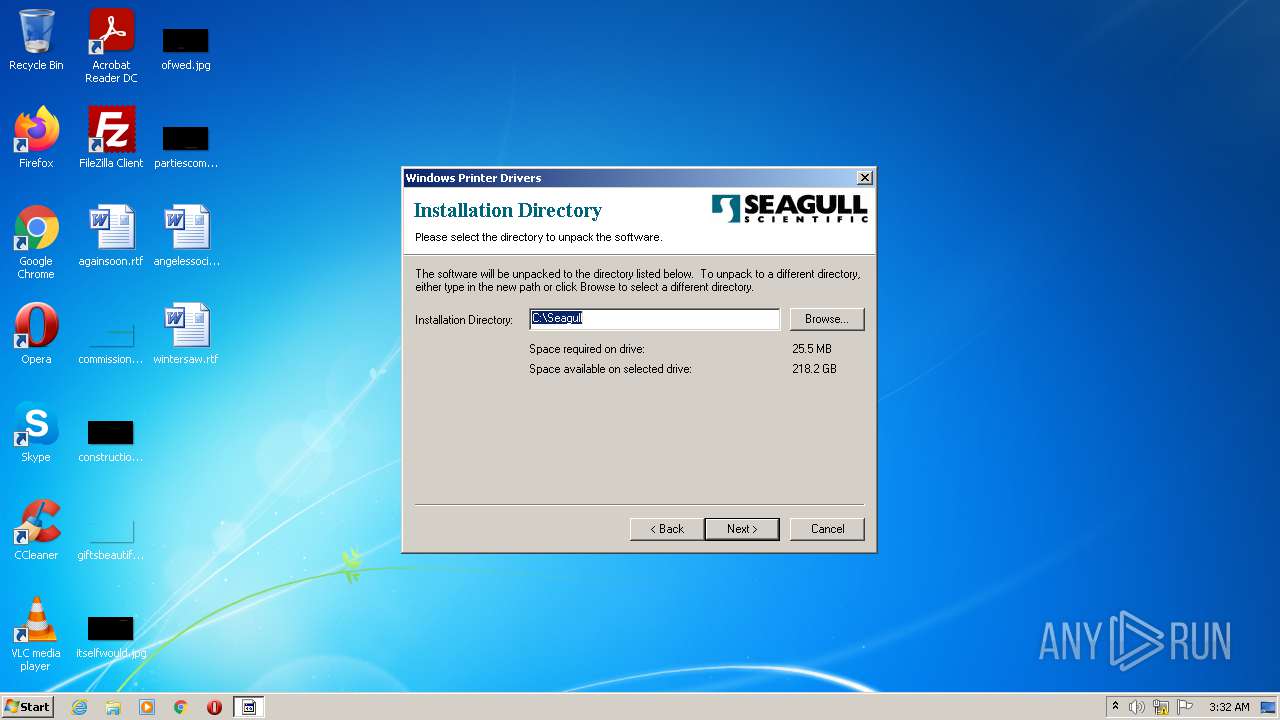
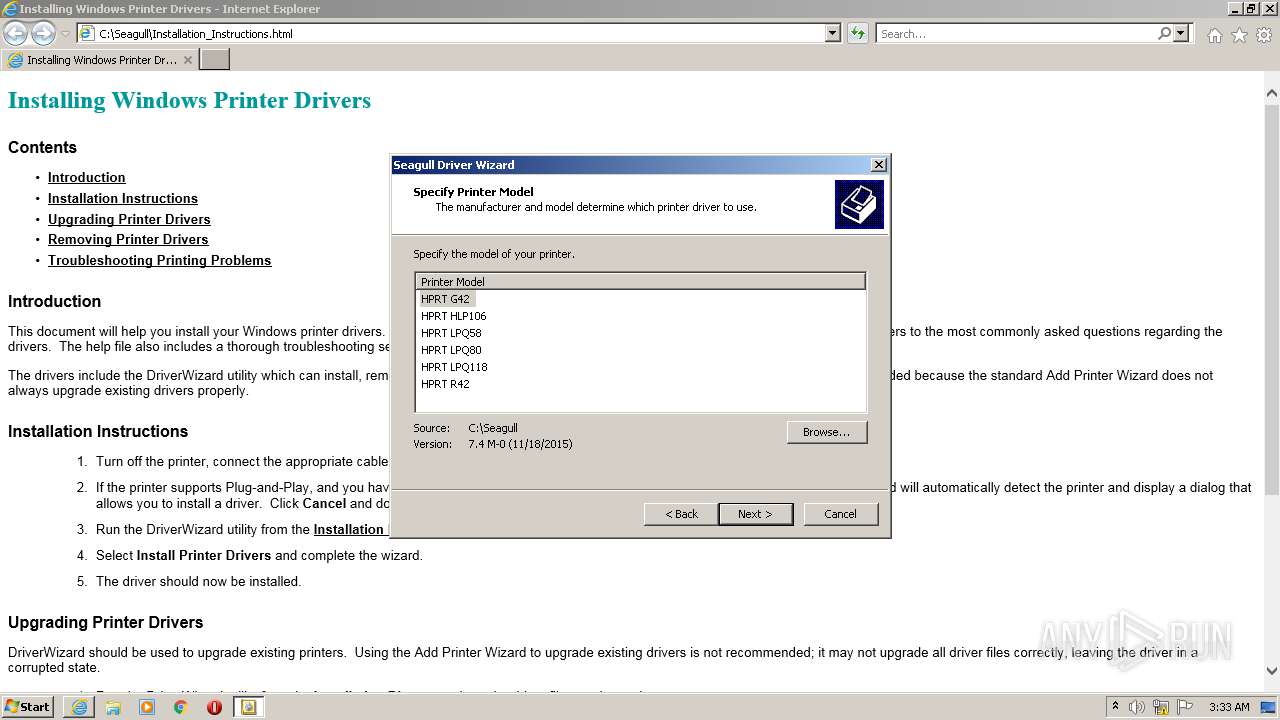
| 1596 | "C:\Seagull\DriverWizard.exe" | C:\Seagull\DriverWizard.exe | 02583427_2.exe | ||||||||||||
User: admin Company: Seagull Scientific, Inc. Integrity Level: HIGH Description: Driver Wizard Exit code: 0 Version: 7.4 Modules
| |||||||||||||||
| 1820 | netsh firewall add portopening tcp 6160 "Seagull Driver Networking" | C:\Windows\System32\netsh.exe | — | spoolsv.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2340 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2992 | "C:\Seagull\DriverWizard.exe" | C:\Seagull\DriverWizard.exe | — | 02583427_2.exe | |||||||||||
User: admin Company: Seagull Scientific, Inc. Integrity Level: MEDIUM Description: Driver Wizard Exit code: 3221226540 Version: 7.4 Modules
| |||||||||||||||
| 3592 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:968 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3996 | "C:\Users\admin\AppData\Local\Temp\02583427_2.exe" | C:\Users\admin\AppData\Local\Temp\02583427_2.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4060 | __ExtractWizard.exe | C:\Users\admin\AppData\Local\Temp\DP_E04D.tmp\__ExtractWizard.exe | — | 02583427_2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
11 595
Read events
10 765
Write events
830
Delete events
0
Modification events
| (PID) Process: | (3996) 02583427_2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3996) 02583427_2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3996) 02583427_2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3996) 02583427_2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 173732800 | |||
| (PID) Process: | (968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30900075 | |||
| (PID) Process: | (968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 473892722 | |||
| (PID) Process: | (968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30900075 | |||
| (PID) Process: | (968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
19
Suspicious files
11
Text files
15
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | 02583427_2.exe | C:\Seagull\hprt.cat | cat | |
MD5:— | SHA256:— | |||
| 3996 | 02583427_2.exe | C:\Seagull\DriverWizard.ddz | compressed | |
MD5:— | SHA256:— | |||
| 3996 | 02583427_2.exe | C:\Seagull\hr#tsc-e.d64 | executable | |
MD5:— | SHA256:— | |||
| 3996 | 02583427_2.exe | C:\Seagull\HPRT.inf | ini | |
MD5:— | SHA256:— | |||
| 3996 | 02583427_2.exe | C:\Seagull\hr#base.ddz | compressed | |
MD5:— | SHA256:— | |||
| 3996 | 02583427_2.exe | C:\Seagull\DriverWizard.exe | executable | |
MD5:— | SHA256:— | |||
| 3996 | 02583427_2.exe | C:\Seagull\hr#tsc.ddz | compressed | |
MD5:— | SHA256:— | |||
| 3996 | 02583427_2.exe | C:\Seagull\hr#tsc-e.dll | executable | |
MD5:— | SHA256:— | |||
| 3996 | 02583427_2.exe | C:\Seagull\hr#tsc-u.dll | executable | |
MD5:— | SHA256:— | |||
| 3996 | 02583427_2.exe | C:\Seagull\hr#tsc-u.d64 | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
13
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
968 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?df5f6fd114544e36 | US | compressed | 4.70 Kb | whitelisted |
968 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
968 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c0065abcee5d4c65 | US | compressed | 4.70 Kb | whitelisted |
968 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
968 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 20.73.194.208:443 | — | — | US | whitelisted |
1360 | svchost.exe | 20.73.194.208:443 | — | — | US | whitelisted |
968 | iexplore.exe | 13.107.4.50:80 | ctldl.windowsupdate.com | Microsoft Corporation | US | whitelisted |
968 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
968 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |