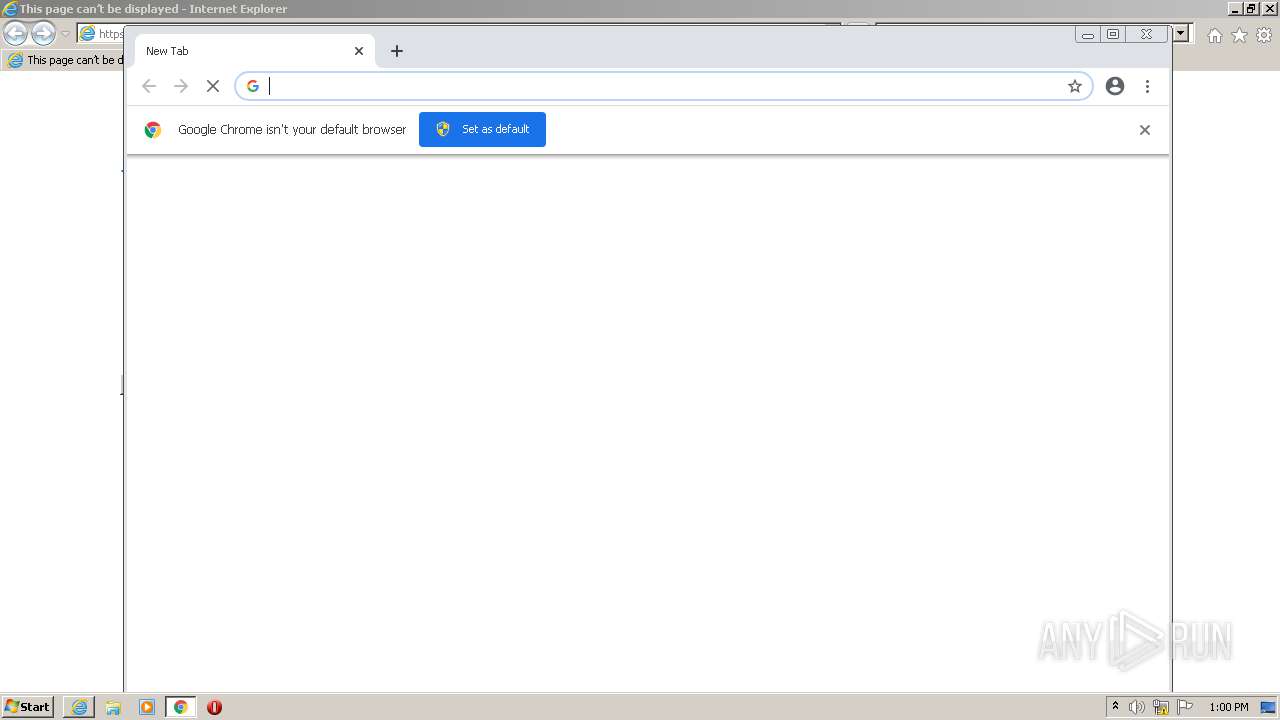
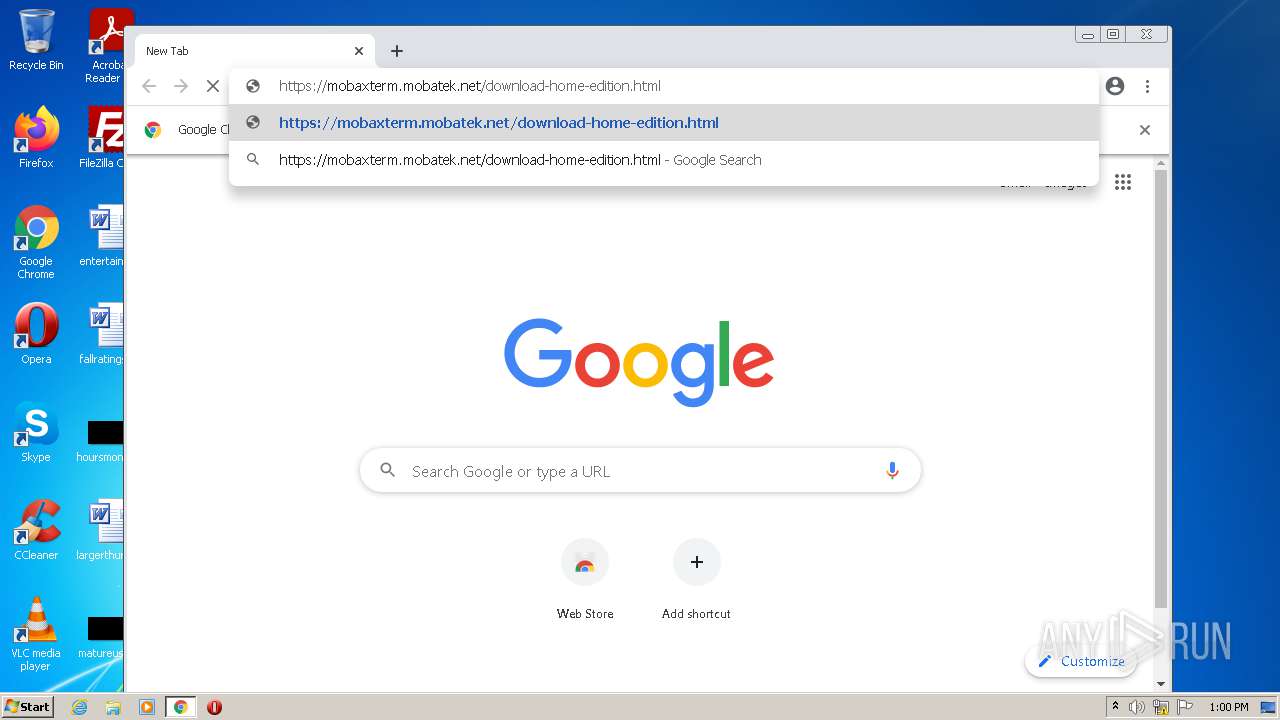
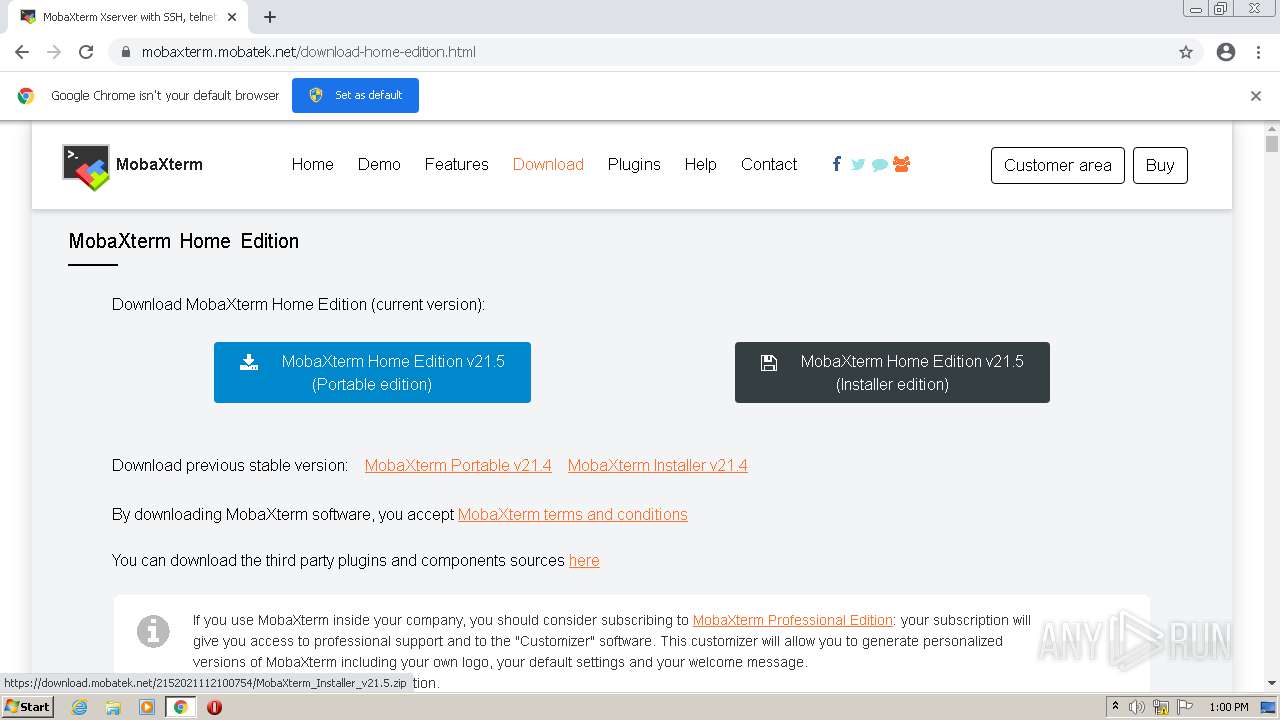
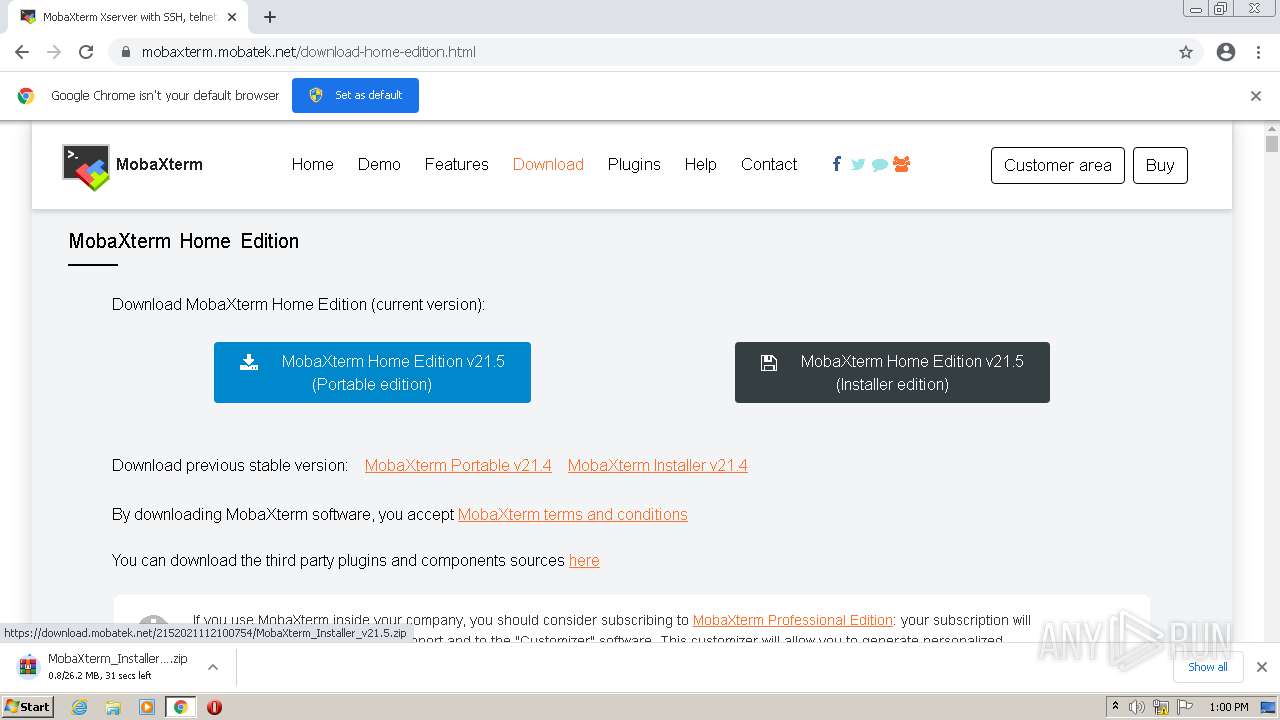
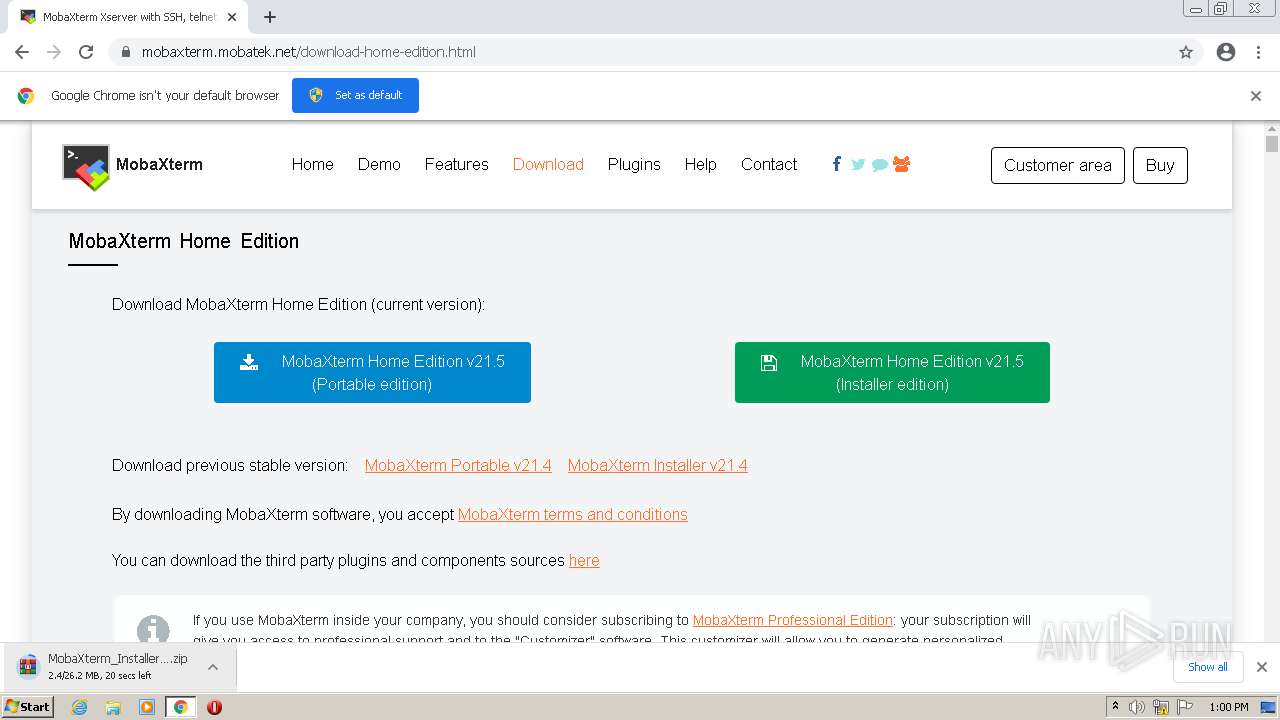
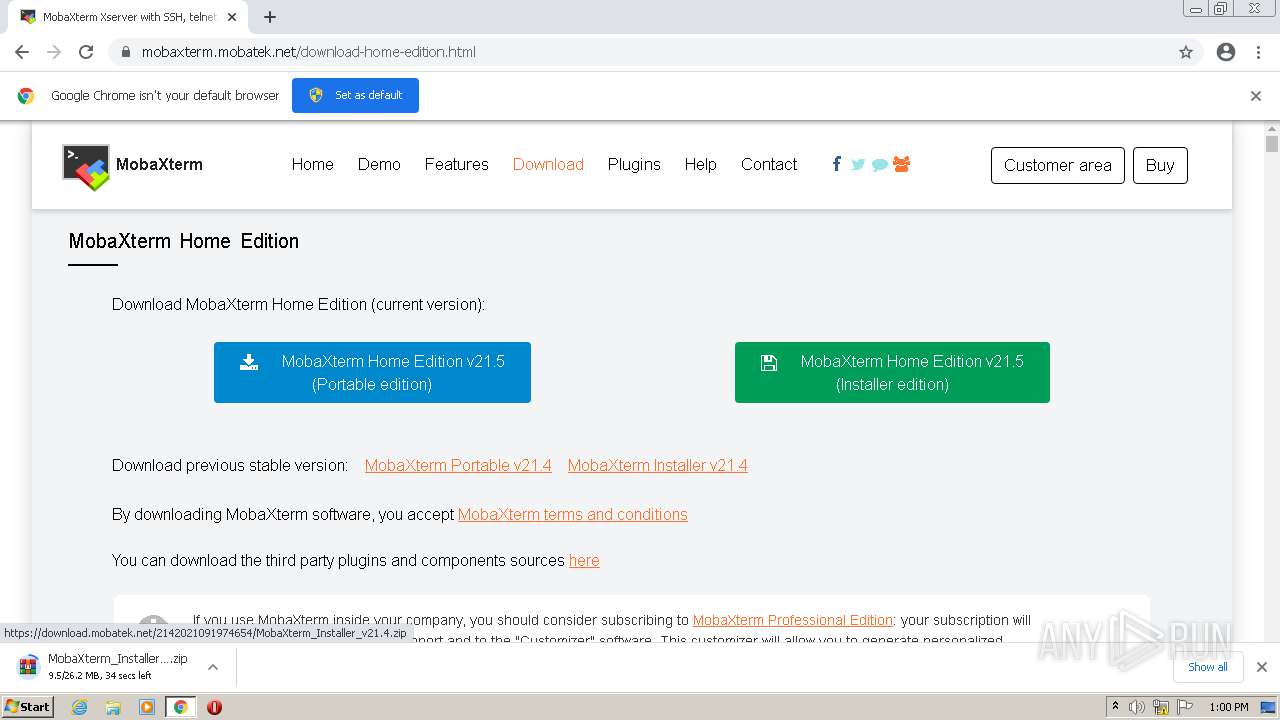
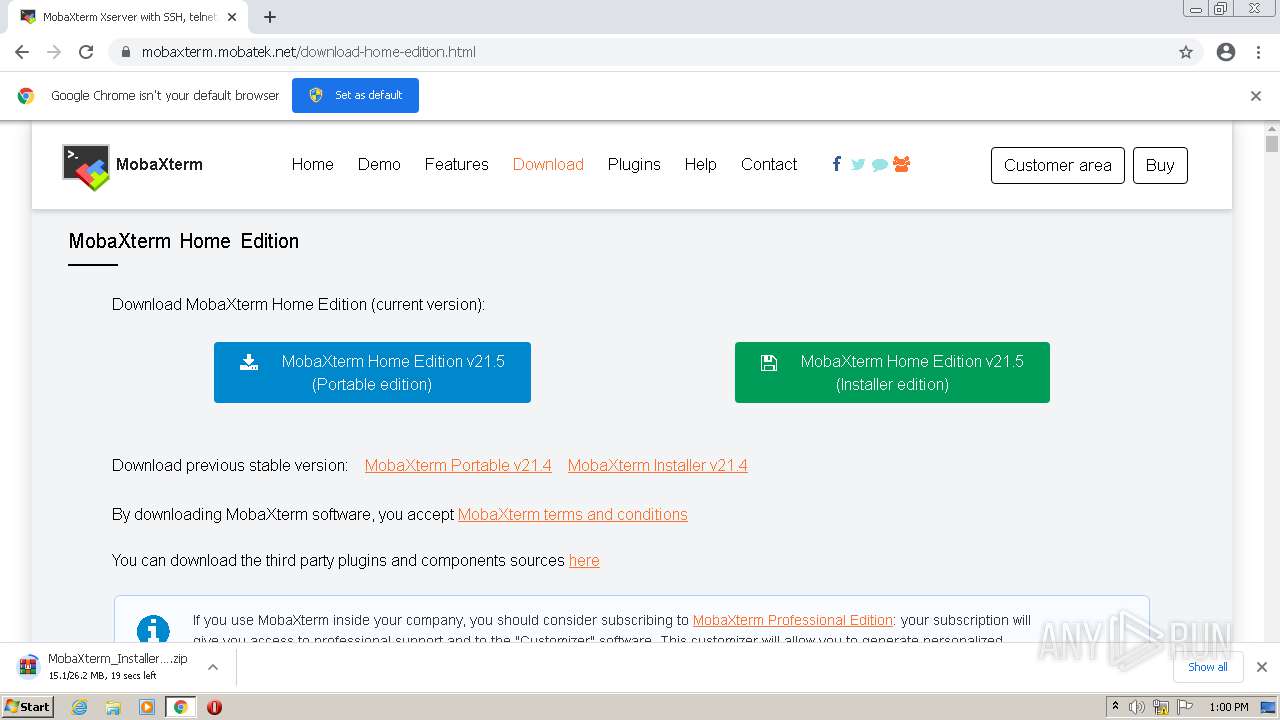
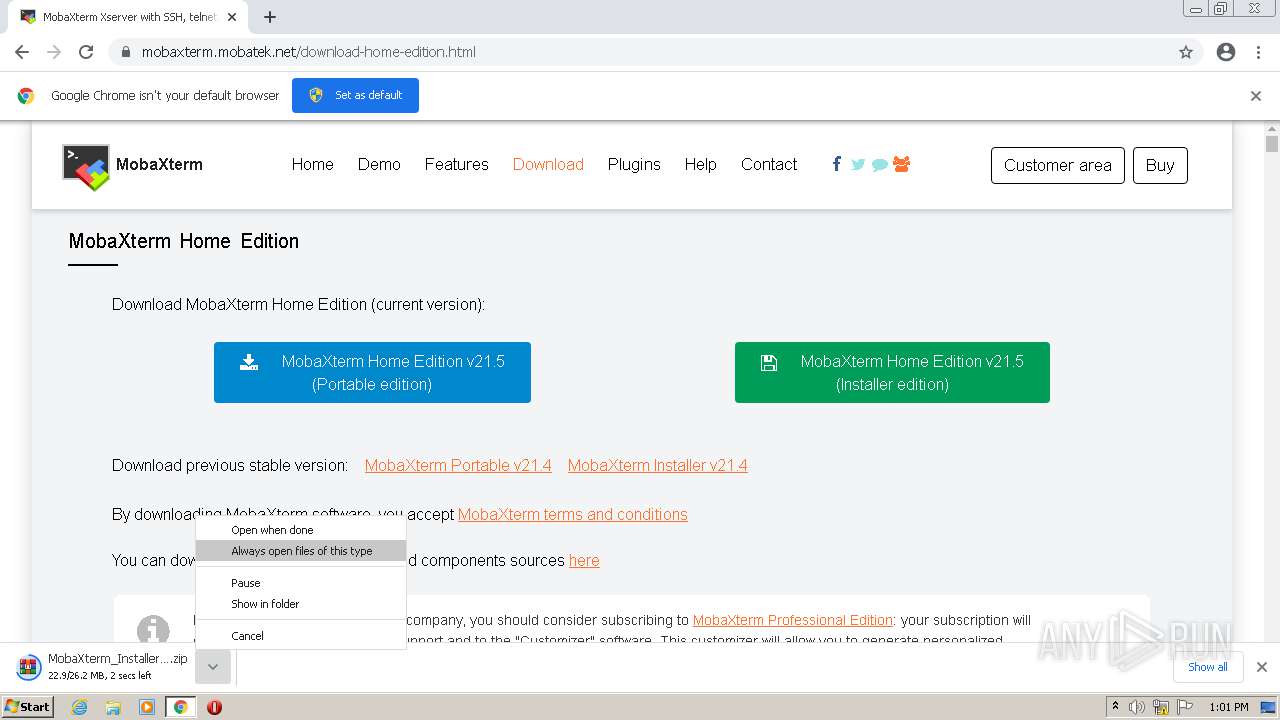
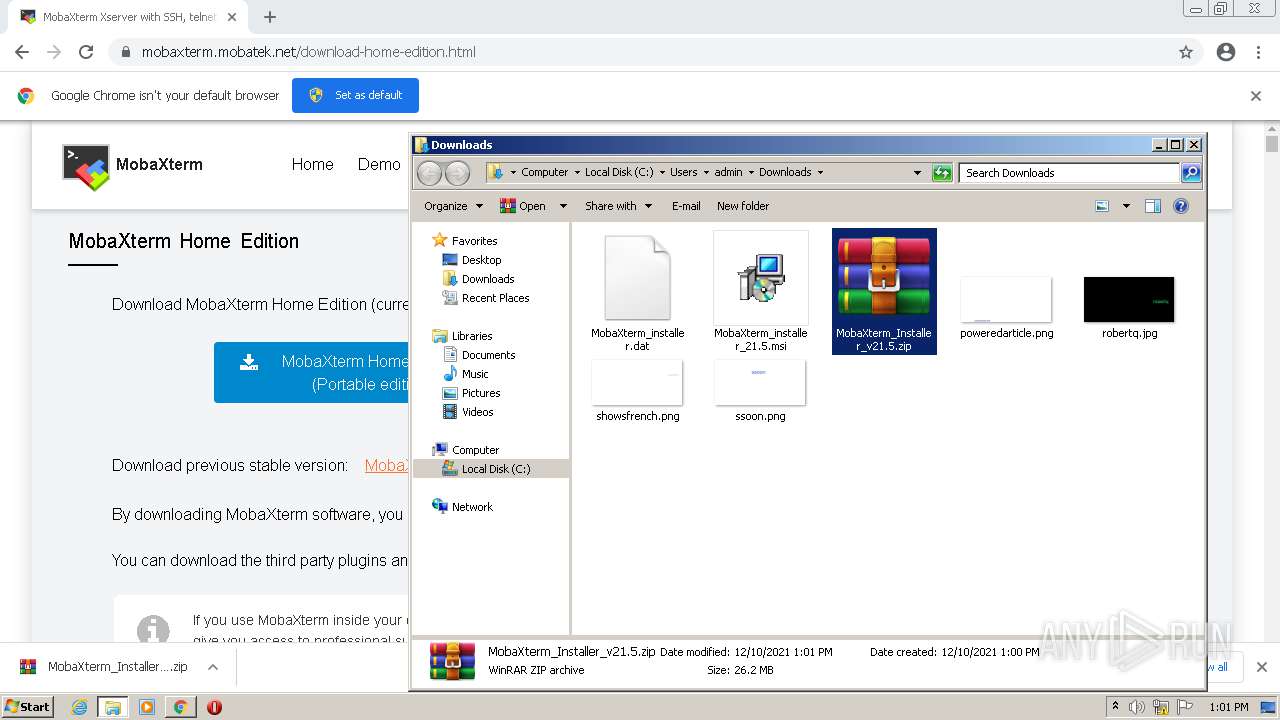
| URL: | https://mobaxterm.mobatek.net/download-home-edition.html |
| Full analysis: | https://app.any.run/tasks/1dd174b8-d1fd-45f4-b161-8d4b27439918 |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2021, 12:59:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D03FC74B722F06E72C8F97701DC7B5CC |
| SHA1: | 229D67E2EEE0AB422ADF08809C843CB5F5887DAC |
| SHA256: | 00070960181E09522F5C78D3971D85168ACB5C07E3428CB5605D76BA14A2A39B |
| SSDEEP: | 3:N8lgHcsaKJNK99BM90n:2QV6BM90n |
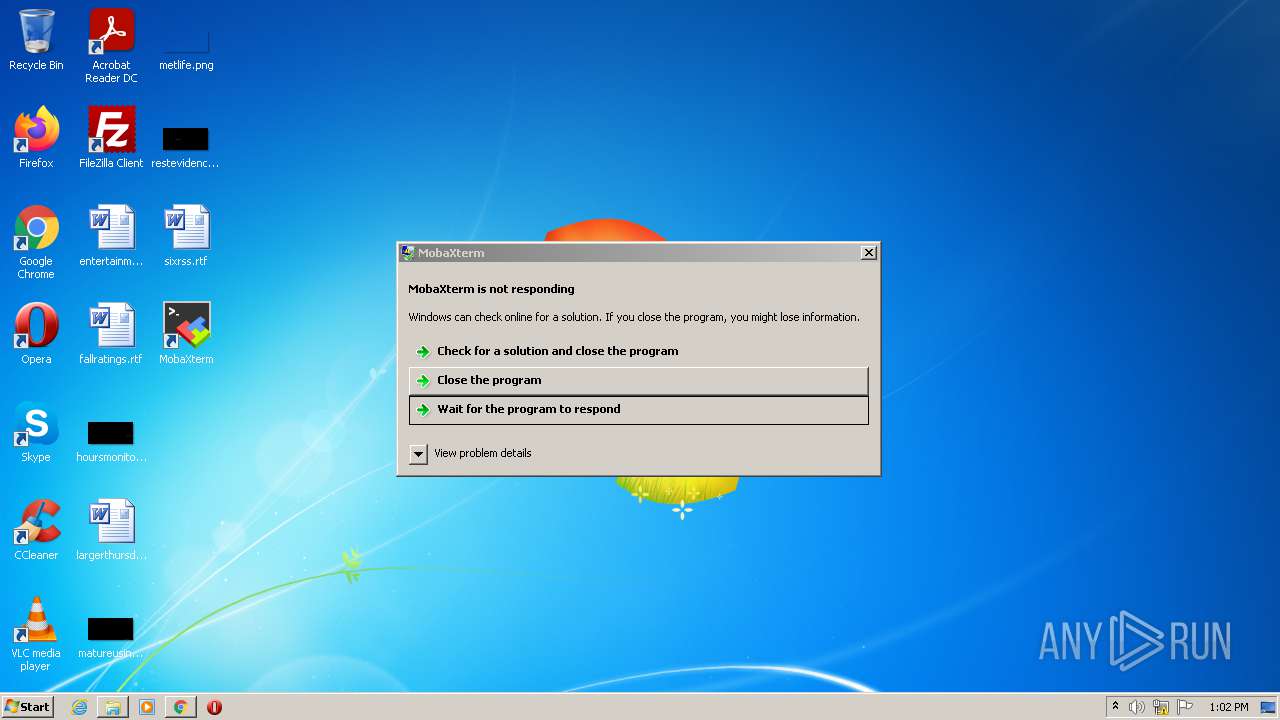
MALICIOUS
Application was dropped or rewritten from another process
- MobaXterm.exe (PID: 3784)
- MobaXterm.exe (PID: 2932)
Detects Cygwin installation
- MobaXterm.exe (PID: 3784)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3176)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2380)
Checks supported languages
- WinRAR.exe (PID: 2540)
- MobaXterm.exe (PID: 2932)
- MobaXterm.exe (PID: 3784)
Reads the computer name
- WinRAR.exe (PID: 2540)
- MobaXterm.exe (PID: 2932)
- MobaXterm.exe (PID: 3784)
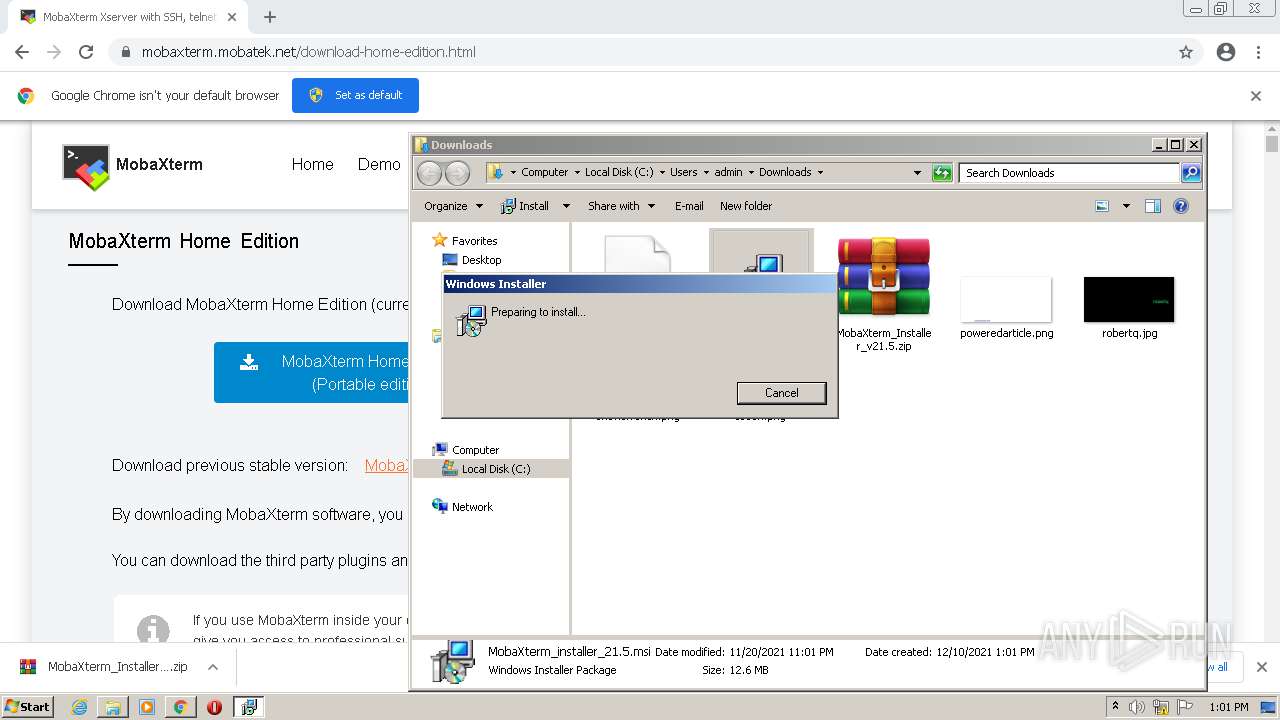
Executed as Windows Service
- msiexec.exe (PID: 1408)
- vssvc.exe (PID: 3880)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3996)
- msiexec.exe (PID: 1408)
Drops a file with too old compile date
- msiexec.exe (PID: 3996)
- msiexec.exe (PID: 1408)
- MobaXterm.exe (PID: 2932)
- MobaXterm.exe (PID: 3784)
Reads the Windows organization settings
- msiexec.exe (PID: 3996)
- msiexec.exe (PID: 1408)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3996)
- msiexec.exe (PID: 1408)
- MobaXterm.exe (PID: 2932)
- MobaXterm.exe (PID: 3784)
Application launched itself
- msiexec.exe (PID: 1408)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 3996)
- msiexec.exe (PID: 1408)
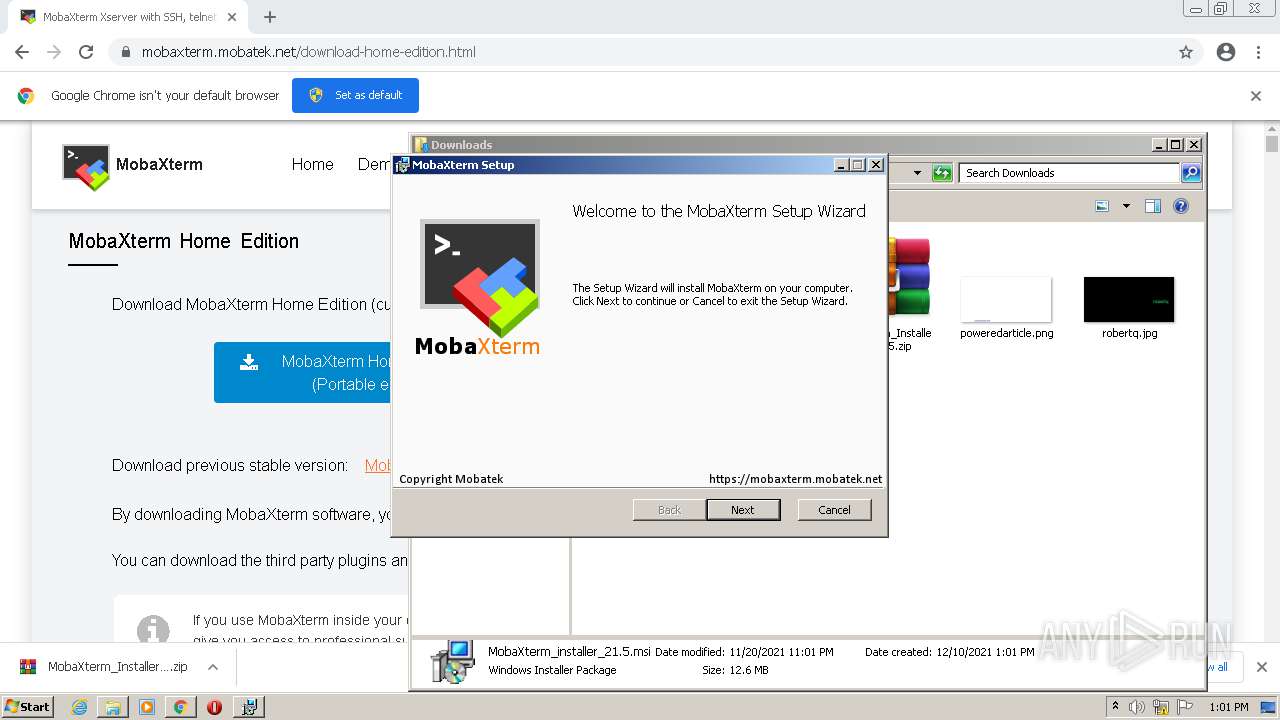
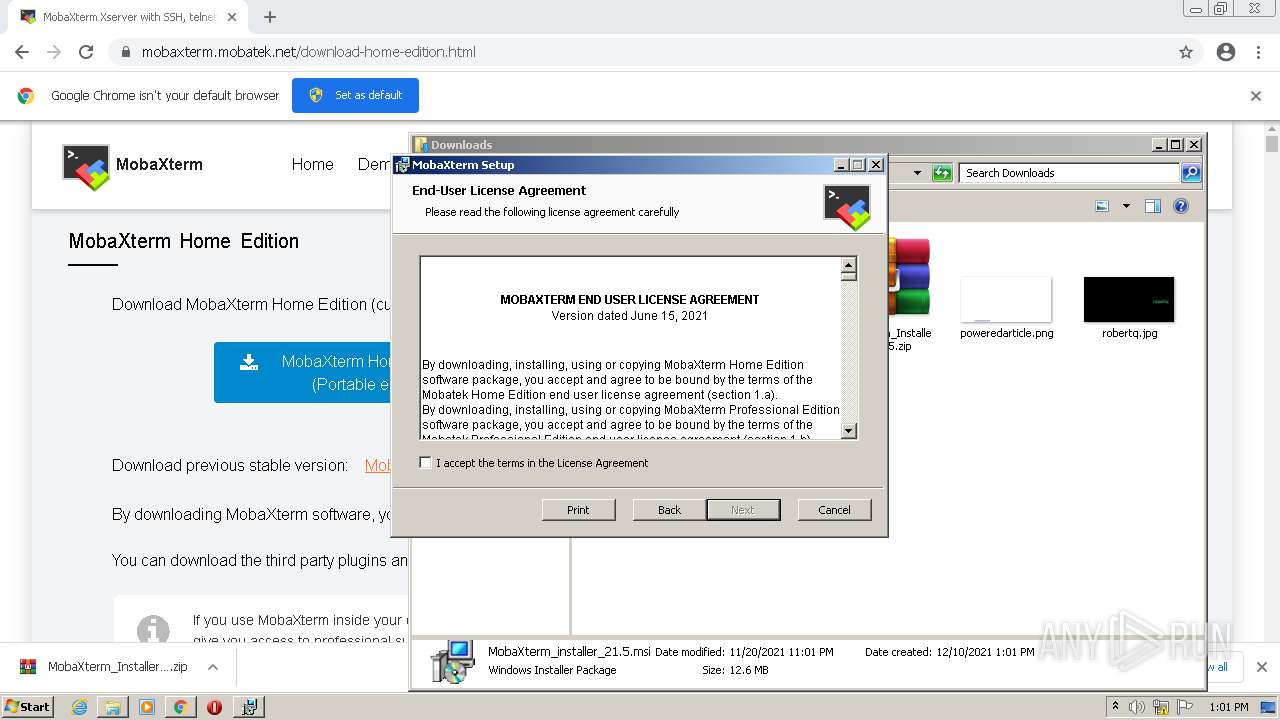
Creates files in the program directory
- msiexec.exe (PID: 1408)
- MsiExec.exe (PID: 580)
Creates a directory in Program Files
- msiexec.exe (PID: 1408)
Drops a file with a compile date too recent
- msiexec.exe (PID: 1408)
- MobaXterm.exe (PID: 3784)
Reads Environment values
- vssvc.exe (PID: 3880)
- MobaXterm.exe (PID: 3784)
Creates a software uninstall entry
- msiexec.exe (PID: 1408)
Searches for installed software
- msiexec.exe (PID: 1408)
Changes default file association
- msiexec.exe (PID: 1408)
Reads mouse settings
- MobaXterm.exe (PID: 3784)
Creates files in the user directory
- MobaXterm.exe (PID: 3784)
INFO
Checks supported languages
- iexplore.exe (PID: 3176)
- chrome.exe (PID: 2380)
- iexplore.exe (PID: 2792)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 996)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 3424)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 2184)
- chrome.exe (PID: 2344)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 1324)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 740)
- chrome.exe (PID: 3372)
- chrome.exe (PID: 1324)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 3332)
- msiexec.exe (PID: 1408)
- MsiExec.exe (PID: 1548)
- vssvc.exe (PID: 3880)
- msiexec.exe (PID: 3996)
- chrome.exe (PID: 3708)
- chrome.exe (PID: 2908)
- MsiExec.exe (PID: 3160)
- MsiExec.exe (PID: 580)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 828)
Reads settings of System Certificates
- iexplore.exe (PID: 2792)
- iexplore.exe (PID: 3176)
- chrome.exe (PID: 996)
- msiexec.exe (PID: 3996)
- msiexec.exe (PID: 1408)
Application launched itself
- iexplore.exe (PID: 2792)
- chrome.exe (PID: 2380)
Checks Windows Trust Settings
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 2792)
- msiexec.exe (PID: 3996)
- msiexec.exe (PID: 1408)
Reads internet explorer settings
- iexplore.exe (PID: 3176)
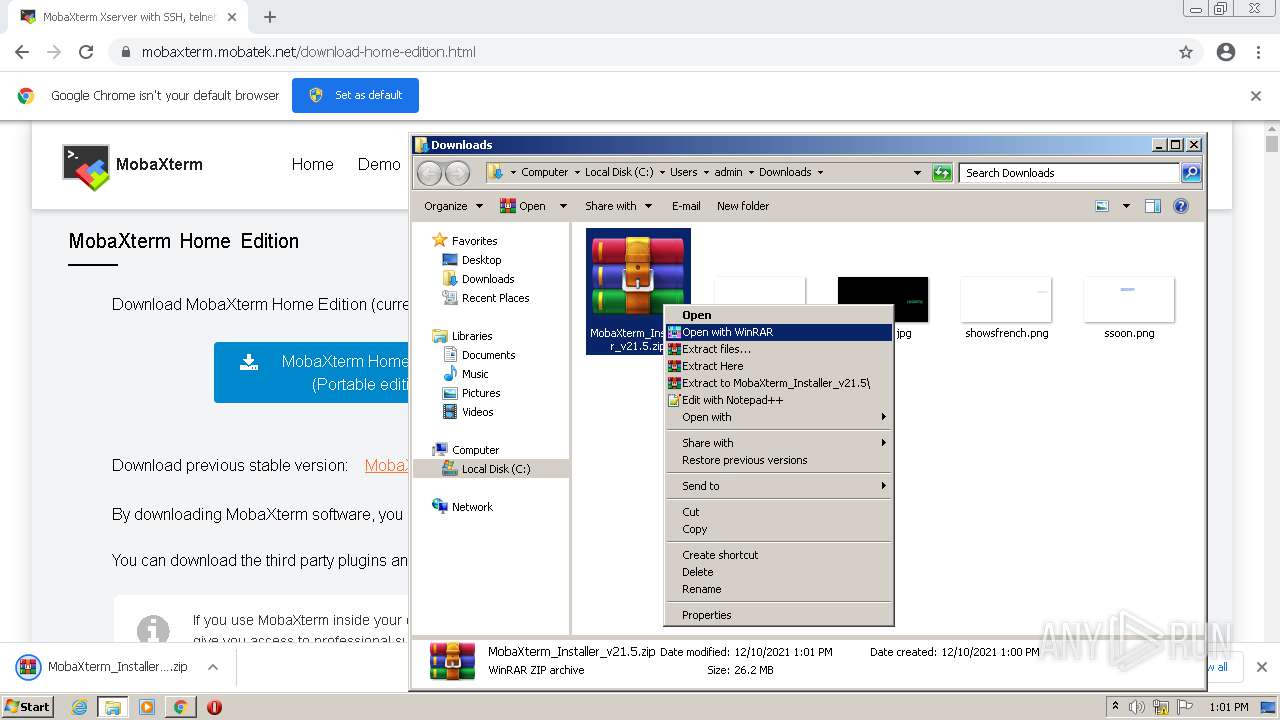
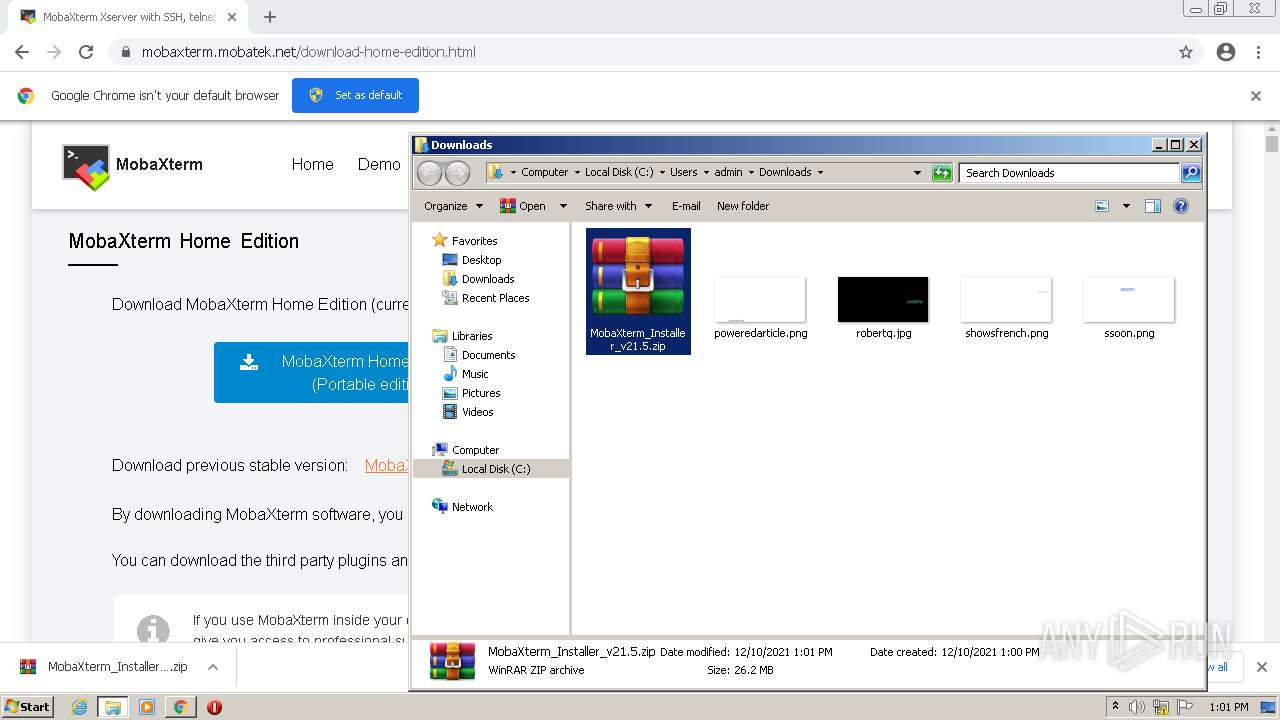
Manual execution by user
- chrome.exe (PID: 2380)
- msiexec.exe (PID: 3996)
- WinRAR.exe (PID: 2540)
- MobaXterm.exe (PID: 3784)
Reads the computer name
- iexplore.exe (PID: 2792)
- iexplore.exe (PID: 3176)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 996)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 740)
- chrome.exe (PID: 1324)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 3372)
- msiexec.exe (PID: 1408)
- MsiExec.exe (PID: 1548)
- vssvc.exe (PID: 3880)
- msiexec.exe (PID: 3996)
- chrome.exe (PID: 2908)
- MsiExec.exe (PID: 3160)
- MsiExec.exe (PID: 580)
Reads the hosts file
- chrome.exe (PID: 2380)
- chrome.exe (PID: 996)
Changes internet zones settings
- iexplore.exe (PID: 2792)
Reads the date of Windows installation
- iexplore.exe (PID: 2792)
- chrome.exe (PID: 1324)
Dropped object may contain Bitcoin addresses
- MobaXterm.exe (PID: 3784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
35
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | C:\Windows\system32\MsiExec.exe -Embedding A0705F006EC253B5315C36DEDCB20F5E E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1556 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=932 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1044,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1348 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3180 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1716 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1408 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1548 | C:\Windows\system32\MsiExec.exe -Embedding 0089F4B7223424ADD4748EA324D9DF7D C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1884 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2920 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
33 074
Read events
32 456
Write events
596
Delete events
22
Modification events
| (PID) Process: | (2792) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2792) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2792) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30928325 | |||
| (PID) Process: | (2792) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2792) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30928325 | |||
| (PID) Process: | (2792) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2792) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2792) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2792) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2792) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
250
Suspicious files
399
Text files
985
Unknown types
160
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61B34F61-94C.pma | — | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_5F5269AC0D922158A5B542020448A2D3 | binary | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_5F5269AC0D922158A5B542020448A2D3 | der | |
MD5:— | SHA256:— | |||
| 996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4bdcf2cf-f778-412e-8d1a-9f8a9b38a422.tmp | text | |
MD5:— | SHA256:— | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1439fa.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
40
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 9.69 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 43.4 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 9.70 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 5.63 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 358 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 88.5 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 20.9 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 9.69 Kb | whitelisted |
3176 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEAXk3DuUOKs7hZfLpqGYUOM%3D | US | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3176 | iexplore.exe | 46.105.198.129:443 | mobaxterm.mobatek.net | OVH SAS | FR | unknown |
3176 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2792 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2792 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3176 | iexplore.exe | 104.18.31.182:80 | ocsp.usertrust.com | Cloudflare Inc | US | unknown |
2792 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
996 | chrome.exe | 142.250.184.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
996 | chrome.exe | 142.250.186.68:443 | www.google.com | Google Inc. | US | whitelisted |
996 | chrome.exe | 142.250.186.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
996 | chrome.exe | 142.250.185.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mobaxterm.mobatek.net |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |