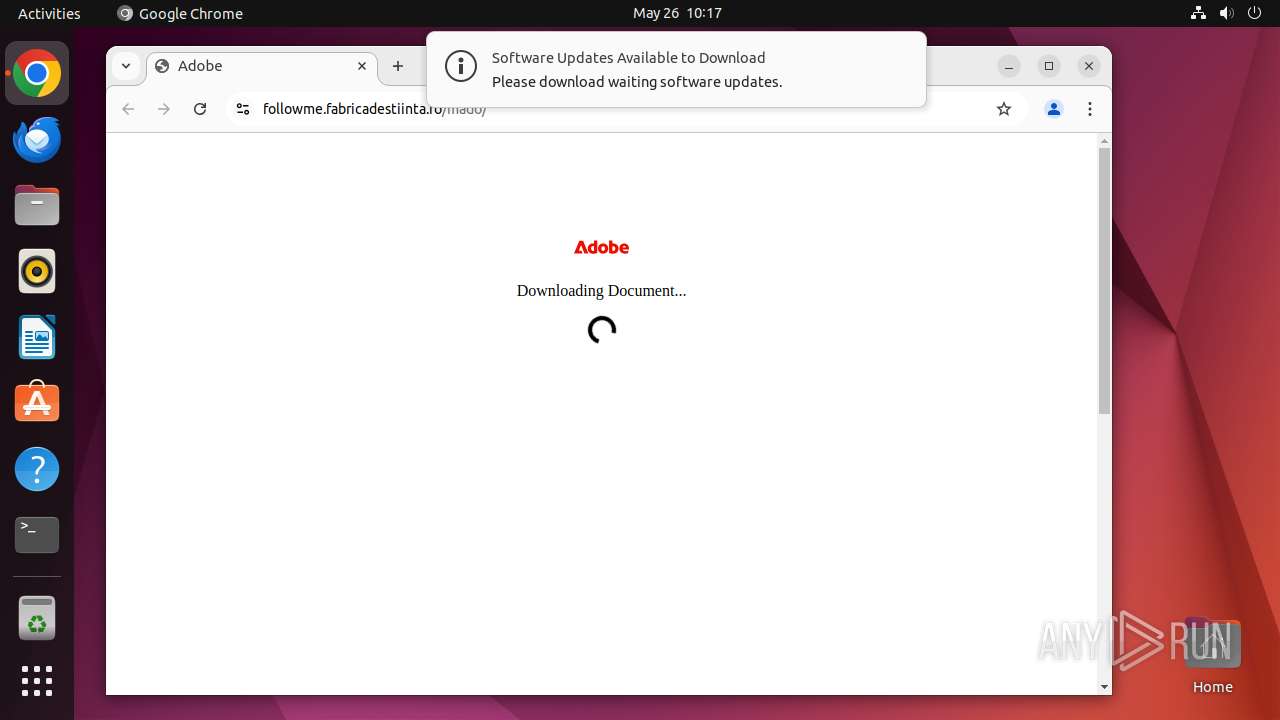
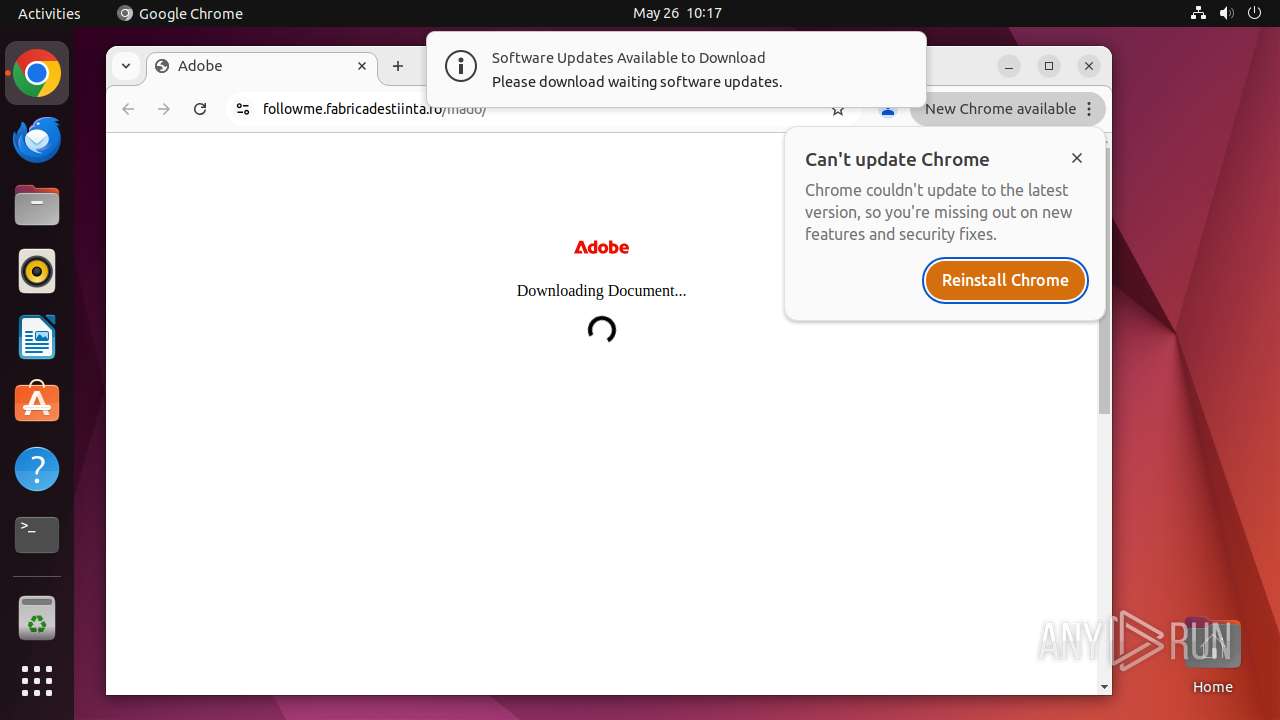
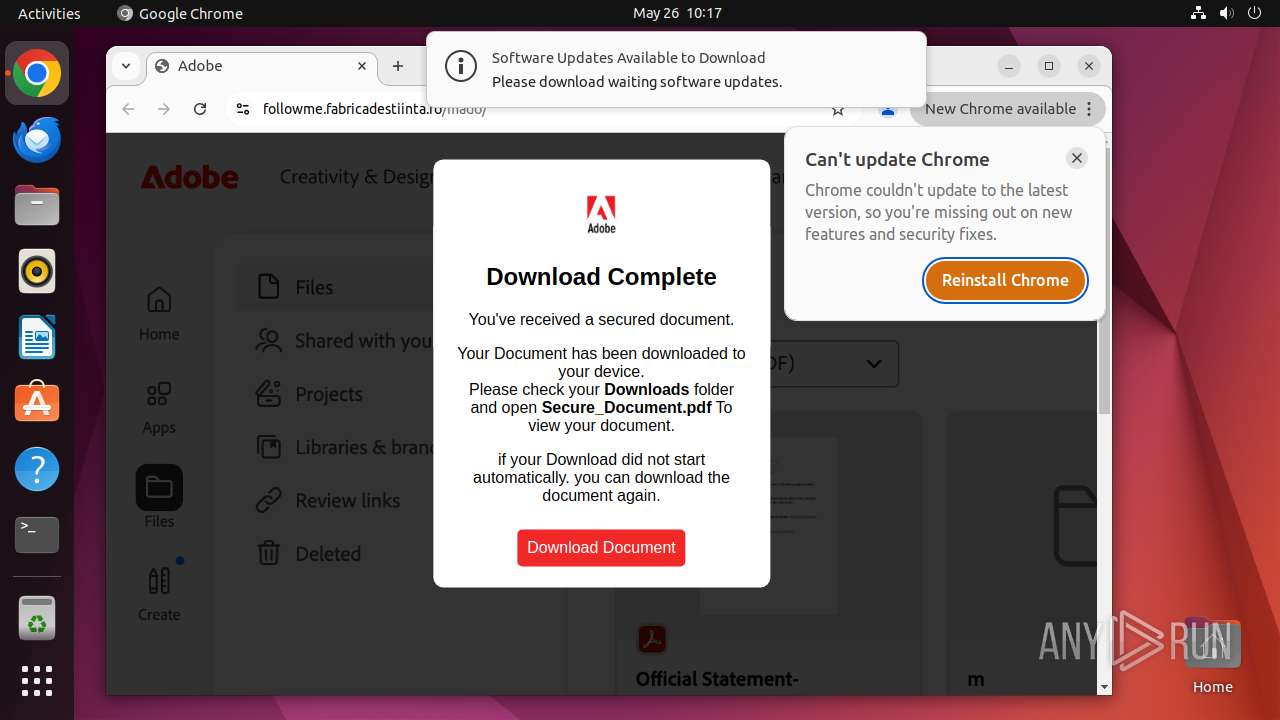
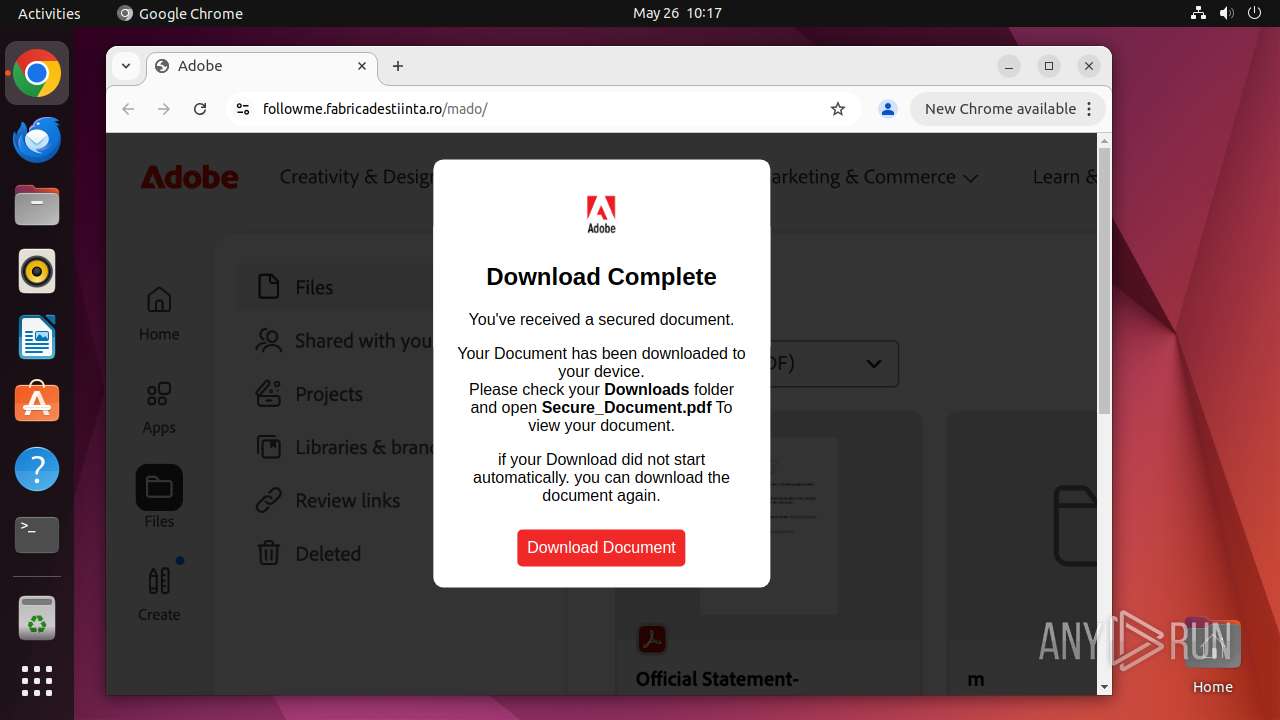
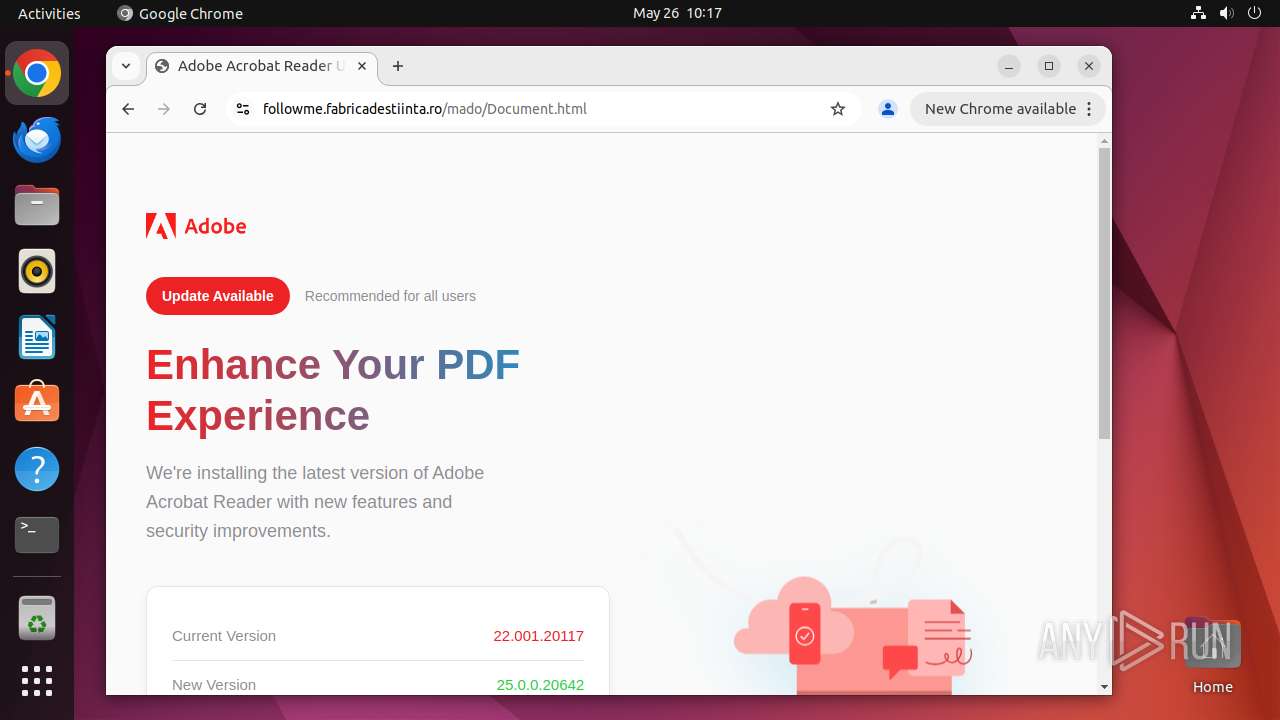
| URL: | http://followme.fabricadestiinta.ro/mado |
| Full analysis: | https://app.any.run/tasks/9bcf195b-b96a-4618-b627-87470129a289 |
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2025, 09:17:06 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MD5: | 3A88E3E548C76EF594F59A2B9390D721 |
| SHA1: | 93F309B382297E7DF870E3022B664D1A4B1DF600 |
| SHA256: | 0005DF214B7D8025E63012B0B5316A8661AEBDDF9254DB6F8A8F85F4ACAE7903 |
| SSDEEP: | 3:N1KYhStQxj+oK:CYhLiX |
MALICIOUS
PHISHING has been detected (SURICATA)
- systemd-resolved (PID: 445)
SUSPICIOUS
Executes commands using command-line interpreter
- sudo (PID: 41020)
- chrome (PID: 41021)
Checks for external IP
- systemd-resolved (PID: 445)
- chrome (PID: 41067)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- chrome (PID: 41067)
INFO
Checks timezone
- chrome (PID: 41021)
Attempting to use instant messaging service
- systemd-resolved (PID: 445)
- chrome (PID: 41067)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
214
Monitored processes
84
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 445 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | ||||||||||||
User: systemd-resolve Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41019 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome http://followme\.fabricadestiinta\.ro/mado " | /usr/bin/dash | — | IntiFjKCklFyPMJr | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41020 | sudo -iu user google-chrome http://followme.fabricadestiinta.ro/mado | /usr/bin/sudo | — | dash | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41021 | /usr/bin/google-chrome http://followme.fabricadestiinta.ro/mado | /opt/google/chrome/chrome | — | sudo | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41022 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41023 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41024 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41025 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41026 | cat | /usr/bin/cat | — | chrome | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41027 | cat | /usr/bin/cat | — | chrome | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
Executable files
0
Suspicious files
79
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 41021 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 41021 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 41021 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 41021 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 41021 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 41021 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 41064 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 41162 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 41021 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
| 41021 | chrome | /home/user/.config/google-chrome/Default/DawnGraphiteCache/data_3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
30
DNS requests
36
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.17:80 | — | Canonical Group Limited | GB | unknown |
— | — | 91.189.91.98:80 | — | Canonical Group Limited | US | unknown |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.48:80 | — | Canonical Group Limited | US | unknown |
— | — | 195.181.170.18:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 185.125.188.57:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
41067 | chrome | 142.250.184.234:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
41067 | chrome | 142.250.185.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
followme.fabricadestiinta.ro |
| unknown |
accounts.google.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
brandlogos.net |
| unknown |
ipinfo.io |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
41067 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
445 | systemd-resolved | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
445 | systemd-resolved | Misc activity | SUSPICIOUS [ANY.RUN] Possible sending an external IP address to Telegram |
41067 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
41067 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
41067 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
41067 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
41067 | chrome | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
41067 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
41067 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |