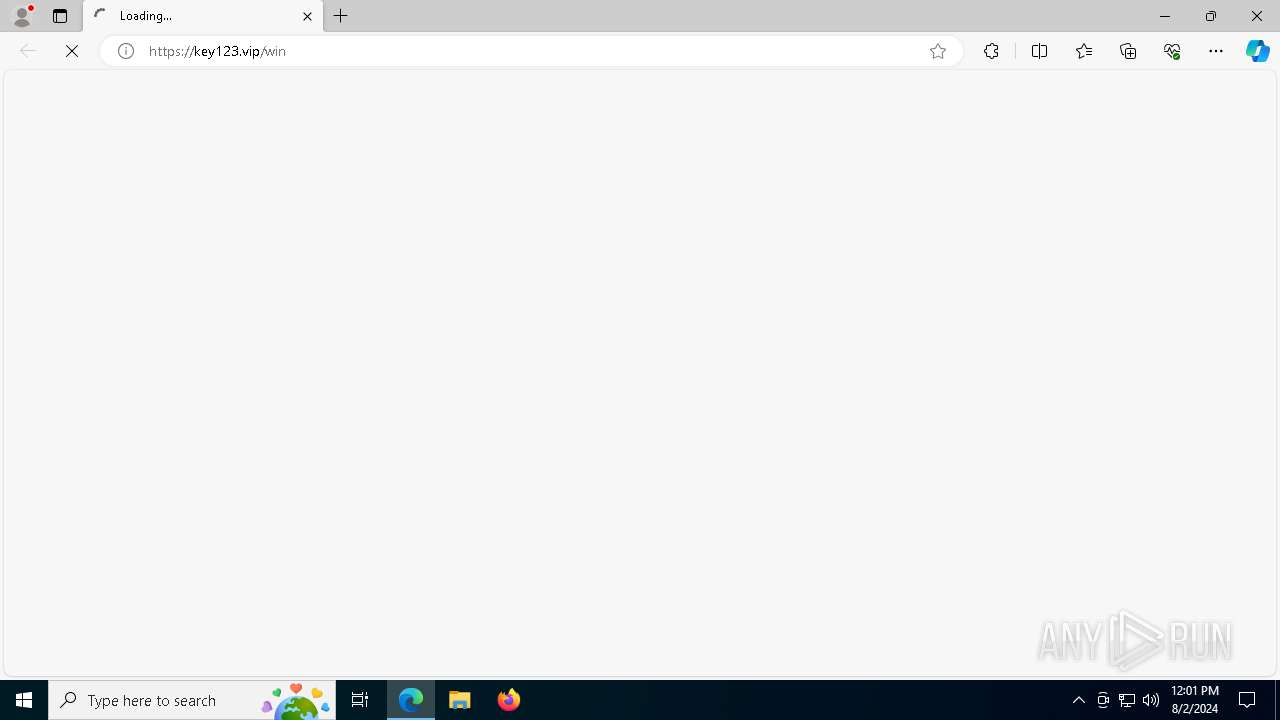
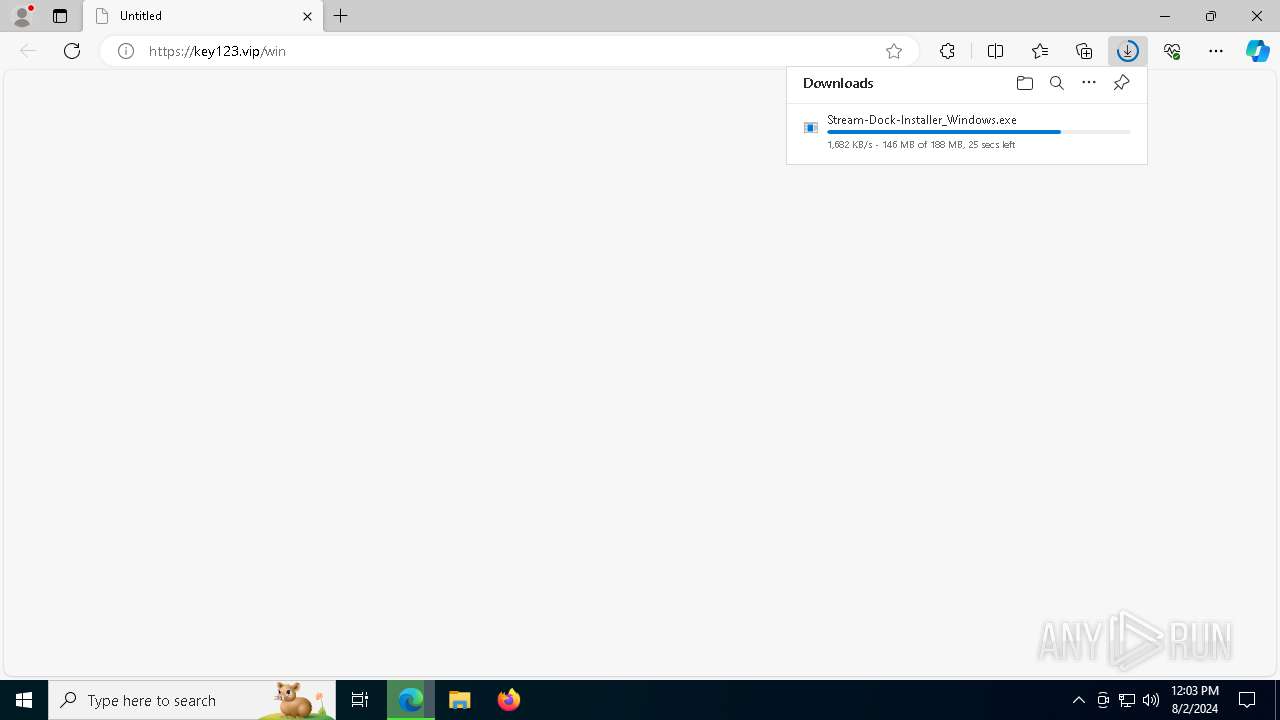
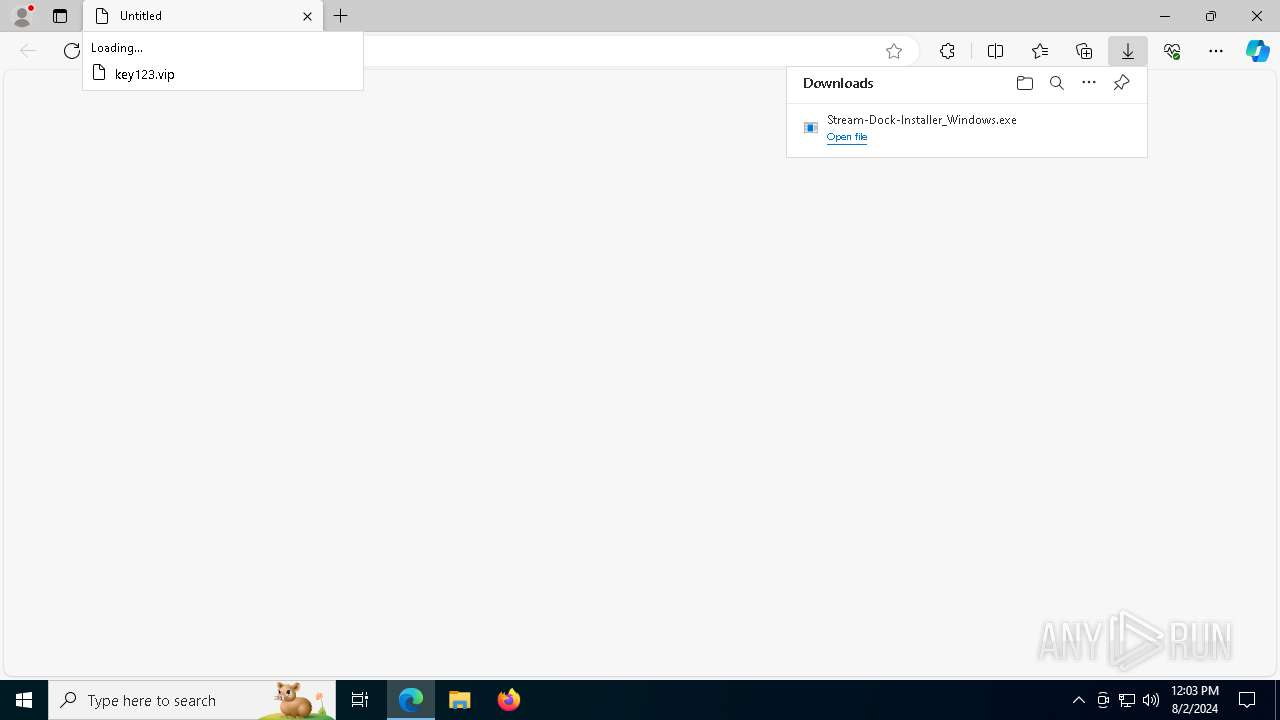
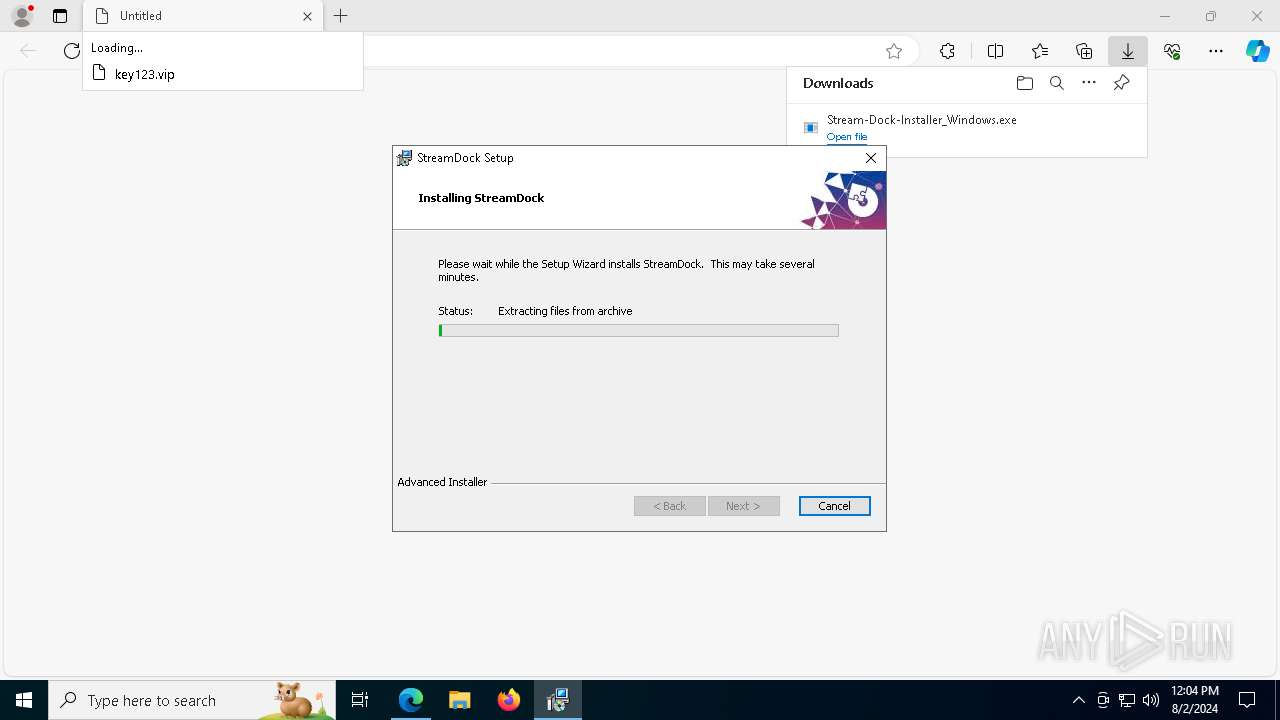
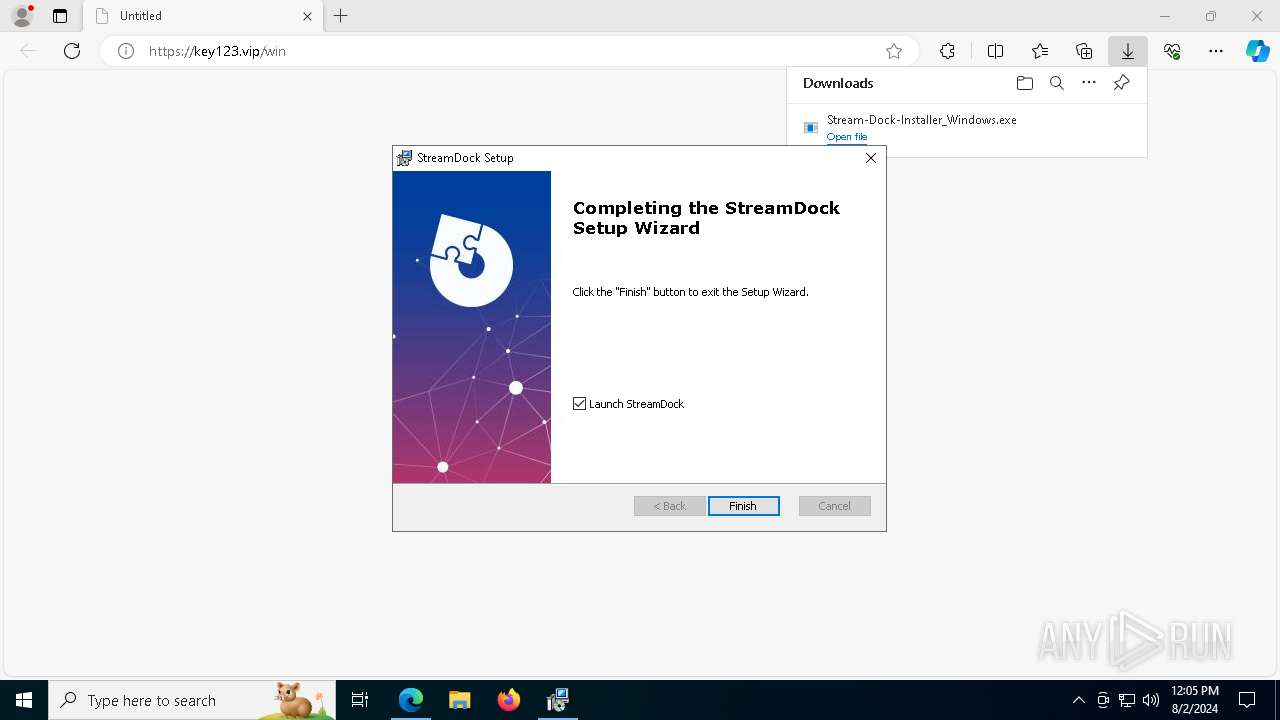
| URL: | https://key123.vip/win |
| Full analysis: | https://app.any.run/tasks/daa4f2d6-ee4e-449d-aaff-50e5b1b198b2 |
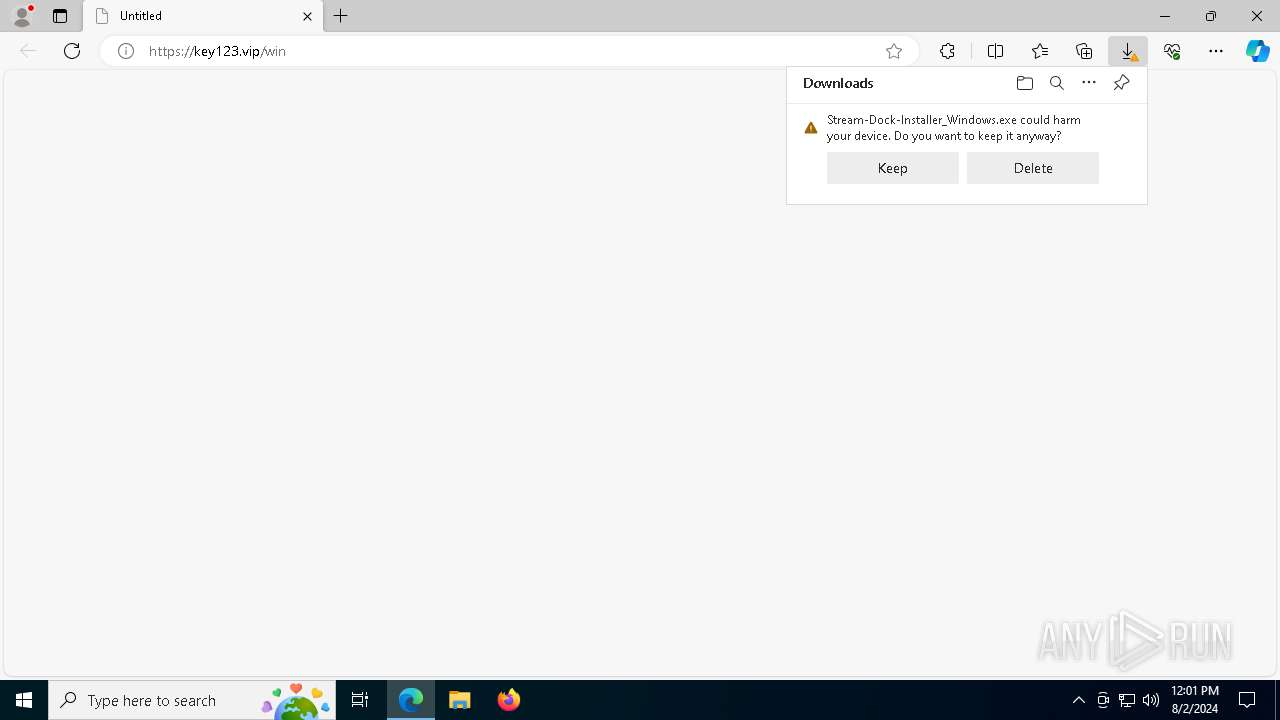
| Verdict: | Malicious activity |
| Analysis date: | August 02, 2024, 12:01:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | E707762B5232C64AFF9E3CBABE4BFEF8 |
| SHA1: | 905F632A127B90B876FB776E3DC93808A645B493 |
| SHA256: | 00B337CEA95DC88F281CBABA1DF869C93E7A687C224F2CF5B014AAA447D6BB85 |
| SSDEEP: | 3:N8FiTeK:2ITeK |
MALICIOUS
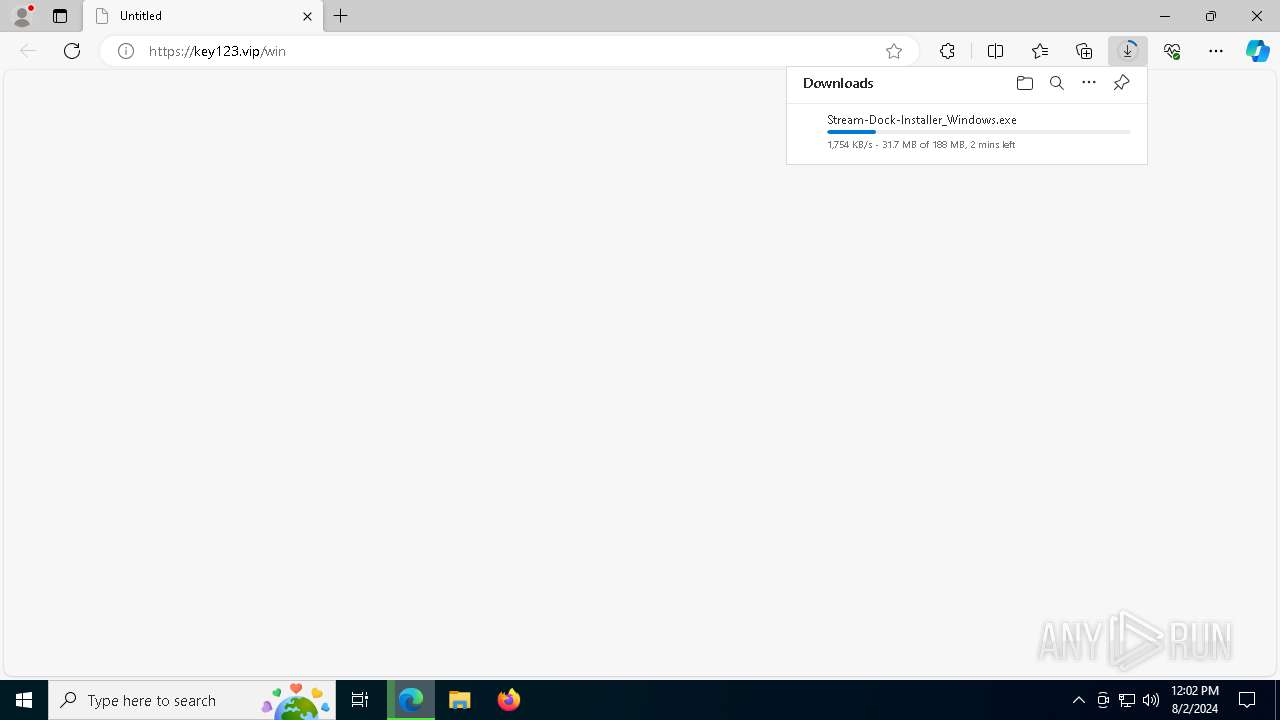
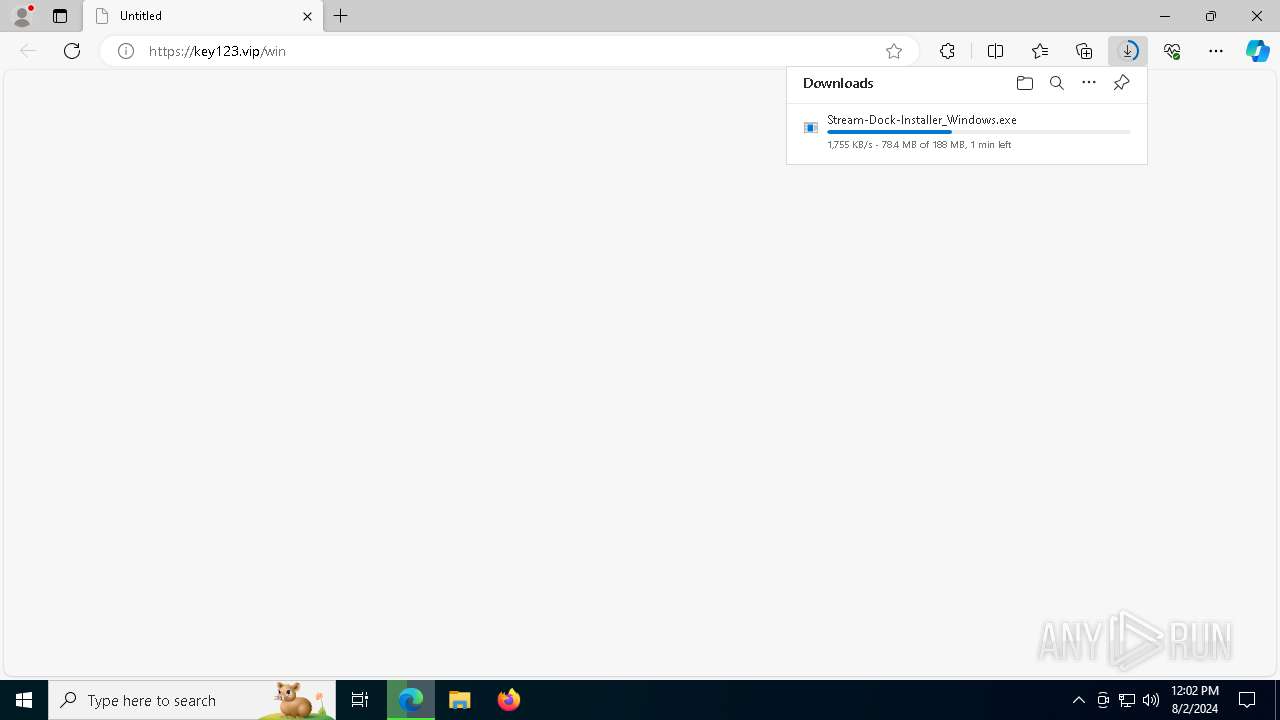
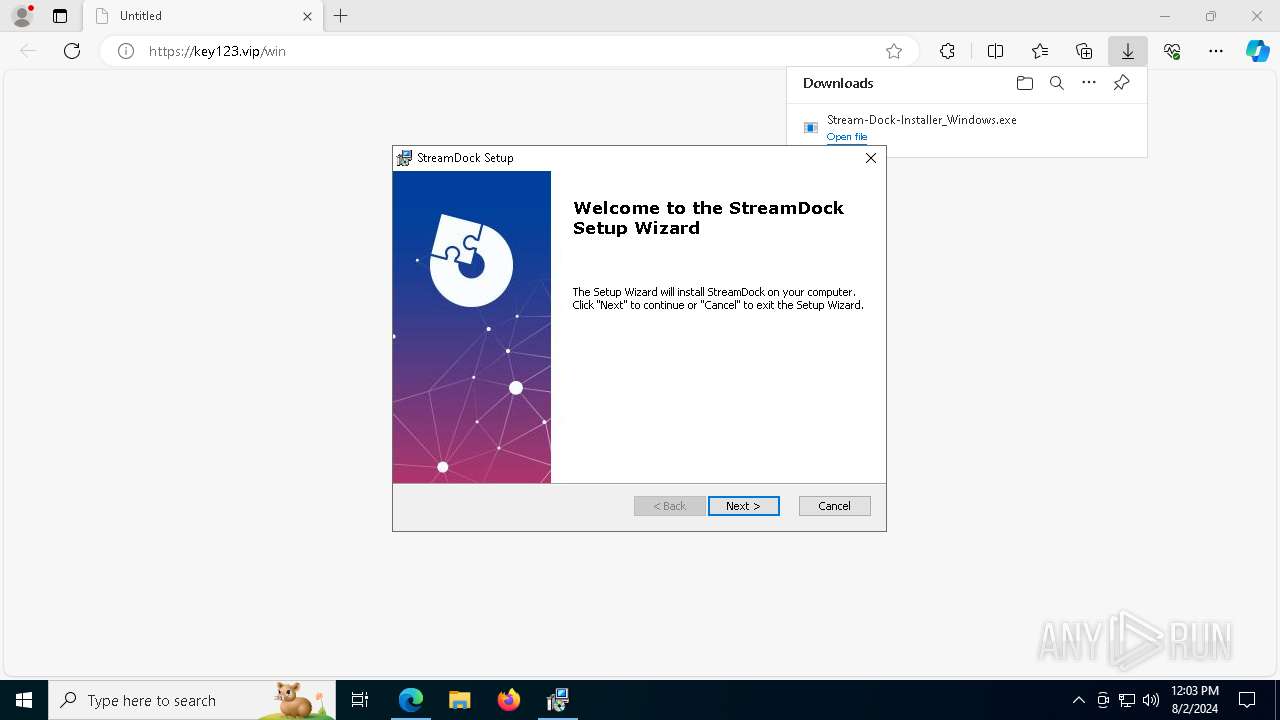
Drops the executable file immediately after the start
- Stream-Dock-Installer_Windows.exe (PID: 7560)
- msiexec.exe (PID: 6236)
- StreamDock.exe (PID: 4004)
Loads dropped or rewritten executable
- svchost.exe (PID: 4060)
- backgroundTaskHost.exe (PID: 5180)
- svchost.exe (PID: 236)
- MusNotificationUx.exe (PID: 2228)
- svchost.exe (PID: 1120)
- svchost.exe (PID: 5284)
- RuntimeBroker.exe (PID: 7200)
- SrTasks.exe (PID: 2536)
- svchost.exe (PID: 7720)
- msedge.exe (PID: 6456)
- svchost.exe (PID: 2208)
- WmiPrvSE.exe (PID: 7936)
- MusNotifyIcon.exe (PID: 5172)
- WaaSMedicAgent.exe (PID: 2224)
- msiexec.exe (PID: 6236)
- backgroundTaskHost.exe (PID: 1568)
- backgroundTaskHost.exe (PID: 8132)
- RUXIMICS.exe (PID: 6200)
- conhost.exe (PID: 6452)
- RuntimeBroker.exe (PID: 4644)
- svchost.exe (PID: 7704)
- conhost.exe (PID: 2508)
- backgroundTaskHost.exe (PID: 236)
- VSSVC.exe (PID: 6724)
- consent.exe (PID: 4784)
- SIHClient.exe (PID: 7888)
- backgroundTaskHost.exe (PID: 1020)
- svchost.exe (PID: 2304)
- RuntimeBroker.exe (PID: 236)
- StreamDock.exe (PID: 4004)
- backgroundTaskHost.exe (PID: 3900)
- svchost.exe (PID: 4324)
- conhost.exe (PID: 7232)
- audiodg.exe (PID: 7652)
- SplashScreen.exe (PID: 7444)
- svchost.exe (PID: 872)
- svchost.exe (PID: 4644)
- WerFault.exe (PID: 3076)
- WerFault.exe (PID: 2608)
Changes the autorun value in the registry
- msiexec.exe (PID: 6236)
SUSPICIOUS
Executable content was dropped or overwritten
- Stream-Dock-Installer_Windows.exe (PID: 7560)
- StreamDock.exe (PID: 4004)
Reads the Windows owner or organization settings
- Stream-Dock-Installer_Windows.exe (PID: 7560)
- msiexec.exe (PID: 6236)
The process drops C-runtime libraries
- msiexec.exe (PID: 6236)
- StreamDock.exe (PID: 4004)
Executes as Windows Service
- VSSVC.exe (PID: 6724)
Process drops legitimate windows executable
- msiexec.exe (PID: 6236)
- StreamDock.exe (PID: 4004)
Reads security settings of Internet Explorer
- Stream-Dock-Installer_Windows.exe (PID: 7560)
Executing commands from a ".bat" file
- Stream-Dock-Installer_Windows.exe (PID: 7560)
- cmd.exe (PID: 7228)
Reads the date of Windows installation
- Stream-Dock-Installer_Windows.exe (PID: 7560)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7228)
- Stream-Dock-Installer_Windows.exe (PID: 7560)
Application launched itself
- cmd.exe (PID: 7228)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 7228)
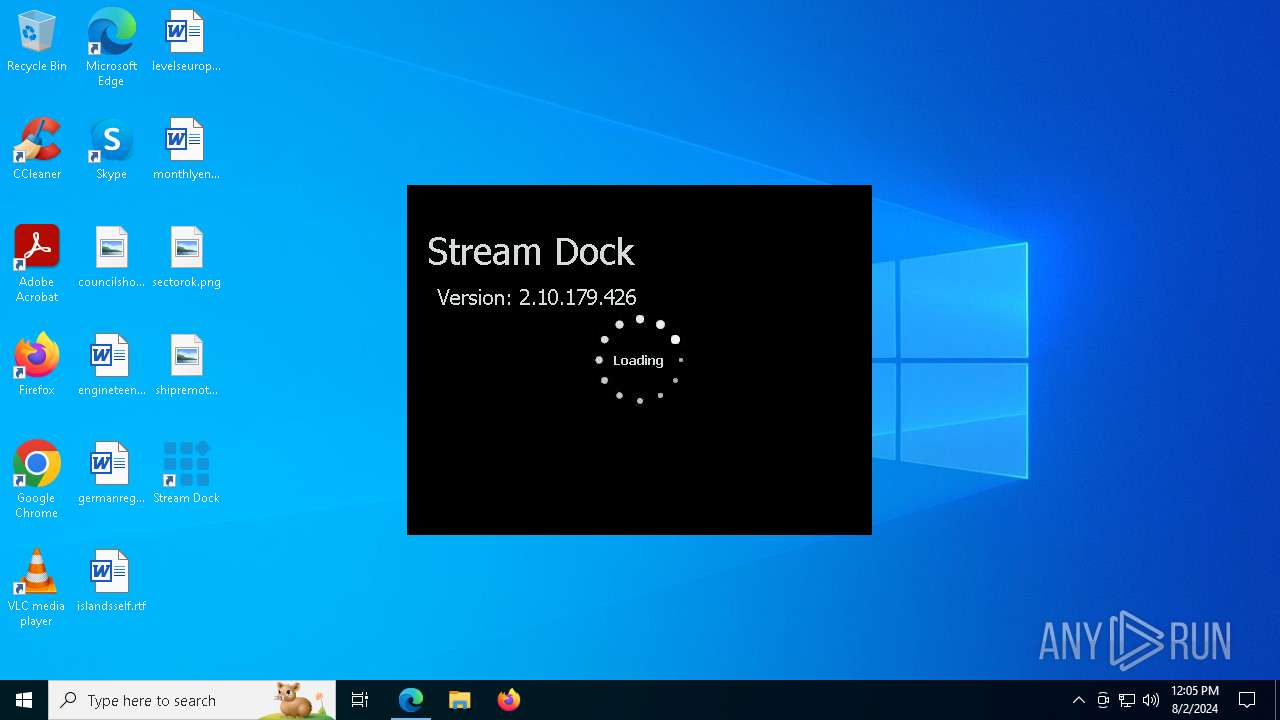
Executes application which crashes
- StreamDock.exe (PID: 4004)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 6456)
Executable content was dropped or overwritten
- msedge.exe (PID: 6456)
- msiexec.exe (PID: 7712)
- msiexec.exe (PID: 6236)
Application launched itself
- msedge.exe (PID: 6456)
Reads Environment values
- identity_helper.exe (PID: 2080)
- Stream-Dock-Installer_Windows.exe (PID: 7560)
- msiexec.exe (PID: 6624)
- msiexec.exe (PID: 6080)
- StreamDock.exe (PID: 4004)
Creates files in the program directory
- RUXIMICS.exe (PID: 6200)
- MusNotifyIcon.exe (PID: 5172)
- MusNotificationUx.exe (PID: 2228)
- svchost.exe (PID: 1120)
- svchost.exe (PID: 872)
Reads the time zone
- MusNotificationUx.exe (PID: 2228)
- MusNotifyIcon.exe (PID: 5172)
- WmiPrvSE.exe (PID: 7936)
Checks proxy server information
- backgroundTaskHost.exe (PID: 3900)
- backgroundTaskHost.exe (PID: 1020)
- backgroundTaskHost.exe (PID: 5180)
- StreamDock.exe (PID: 4004)
- WerFault.exe (PID: 3076)
Reads the software policy settings
- WaaSMedicAgent.exe (PID: 2224)
- backgroundTaskHost.exe (PID: 3900)
- backgroundTaskHost.exe (PID: 5180)
- backgroundTaskHost.exe (PID: 1020)
- SIHClient.exe (PID: 7888)
- consent.exe (PID: 4784)
- WerFault.exe (PID: 3076)
Checks supported languages
- RUXIMICS.exe (PID: 6200)
- Stream-Dock-Installer_Windows.exe (PID: 7560)
- msiexec.exe (PID: 6236)
- msiexec.exe (PID: 6304)
- msiexec.exe (PID: 6080)
- msiexec.exe (PID: 6624)
- identity_helper.exe (PID: 2080)
- StreamDock.exe (PID: 4004)
- SplashScreen.exe (PID: 7444)
Reads security settings of Internet Explorer
- backgroundTaskHost.exe (PID: 1020)
- backgroundTaskHost.exe (PID: 3900)
- RuntimeBroker.exe (PID: 236)
- backgroundTaskHost.exe (PID: 236)
- backgroundTaskHost.exe (PID: 1568)
- backgroundTaskHost.exe (PID: 5180)
- backgroundTaskHost.exe (PID: 8132)
- svchost.exe (PID: 2304)
Create files in a temporary directory
- svchost.exe (PID: 7720)
- Stream-Dock-Installer_Windows.exe (PID: 7560)
Creates files or folders in the user directory
- backgroundTaskHost.exe (PID: 1020)
- backgroundTaskHost.exe (PID: 8132)
- Stream-Dock-Installer_Windows.exe (PID: 7560)
- StreamDock.exe (PID: 4004)
- WerFault.exe (PID: 3076)
The process uses the downloaded file
- msedge.exe (PID: 7444)
- msedge.exe (PID: 6456)
- consent.exe (PID: 4784)
Reads the computer name
- Stream-Dock-Installer_Windows.exe (PID: 7560)
- msiexec.exe (PID: 6236)
- msiexec.exe (PID: 6304)
- msiexec.exe (PID: 6080)
- msiexec.exe (PID: 6624)
- identity_helper.exe (PID: 2080)
- StreamDock.exe (PID: 4004)
- SplashScreen.exe (PID: 7444)
Drops the executable file immediately after the start
- msiexec.exe (PID: 7712)
- msedge.exe (PID: 6456)
Loads dropped or rewritten executable
- msedge.exe (PID: 7360)
- msedge.exe (PID: 8060)
- msedge.exe (PID: 6232)
- msedge.exe (PID: 6608)
- msedge.exe (PID: 8008)
- msedge.exe (PID: 4104)
- msedge.exe (PID: 6824)
- msedge.exe (PID: 1116)
- msedge.exe (PID: 6244)
- msedge.exe (PID: 7312)
- msedge.exe (PID: 6720)
- msedge.exe (PID: 5552)
- msedge.exe (PID: 6172)
- msedge.exe (PID: 7164)
- msedge.exe (PID: 6316)
- msedge.exe (PID: 2396)
- msedge.exe (PID: 7444)
- msedge.exe (PID: 7072)
- msedge.exe (PID: 5328)
- msedge.exe (PID: 3176)
- identity_helper.exe (PID: 2080)
- msedge.exe (PID: 7660)
- msedge.exe (PID: 6236)
- msedge.exe (PID: 6860)
- msedge.exe (PID: 3076)
- msedge.exe (PID: 7320)
- msedge.exe (PID: 7156)
- msedge.exe (PID: 6264)
- msedge.exe (PID: 7048)
- msedge.exe (PID: 4772)
- msedge.exe (PID: 2456)
- msedge.exe (PID: 7312)
- msedge.exe (PID: 7340)
- msedge.exe (PID: 6216)
- msedge.exe (PID: 6816)
Manual execution by a user
- StreamDock.exe (PID: 4004)
Creates a software uninstall entry
- msiexec.exe (PID: 6236)
Process checks computer location settings
- Stream-Dock-Installer_Windows.exe (PID: 7560)
Reads the machine GUID from the registry
- StreamDock.exe (PID: 4004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
198
Monitored processes
86
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\WINDOWS\system32\BackgroundTaskHost.exe" -ServerName:BackgroundTaskHost.WebAccountProvider | C:\Windows\System32\backgroundTaskHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Background Task Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s wuauserv | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | C:\WINDOWS\System32\svchost.exe -k WerSvcGroup | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | "C:\WINDOWS\system32\backgroundTaskHost.exe" -ServerName:App.AppXmtcan0h2tfbfy7k9kn8hbxb6dmzz1zh0.mca | C:\Windows\System32\backgroundTaskHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Background Task Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5252 --field-trial-handle=2336,i,4838505630376553962,9660974600401083143,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1120 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s DsmSvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\WINDOWS\system32\BackgroundTaskHost.exe" -ServerName:BackgroundTaskHost.WebAccountProvider | C:\Windows\System32\backgroundTaskHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Background Task Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2080 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5684 --field-trial-handle=2336,i,4838505630376553962,9660974600401083143,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2136 | C:\WINDOWS\system32\cmd.exe /S /D /c" del "C:\Users\admin\AppData\Local\Temp\EXE8C71.tmp.bat" " | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
87 763
Read events
86 435
Write events
1 236
Delete events
92
Modification events
| (PID) Process: | (6456) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6456) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6456) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6456) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6456) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6456) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6456) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6456) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6456) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6456) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
162
Suspicious files
1 022
Text files
1 361
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe536b.TMP | — | |
MD5:— | SHA256:— | |||
| 6456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe536b.TMP | — | |
MD5:— | SHA256:— | |||
| 6456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe537b.TMP | — | |
MD5:— | SHA256:— | |||
| 6456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe537b.TMP | — | |
MD5:— | SHA256:— | |||
| 6456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe537b.TMP | — | |
MD5:— | SHA256:— | |||
| 6456 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
77
DNS requests
66
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1020 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4008 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7720 | svchost.exe | HEAD | 200 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/820a23ba-bd71-40b7-8cae-4903ba074f95?P1=1723190649&P2=404&P3=2&P4=J82cILyXRLNUeDmKU79y%2fyf2OV4VD63YxayloDuK9P%2f6YA%2b1LF7DtWFOUJ4mzbkI2XpcezMI%2b%2f%2fpt5VRUNf%2bJA%3d%3d | unknown | — | — | whitelisted |
5180 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7720 | svchost.exe | GET | 206 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/820a23ba-bd71-40b7-8cae-4903ba074f95?P1=1723190649&P2=404&P3=2&P4=J82cILyXRLNUeDmKU79y%2fyf2OV4VD63YxayloDuK9P%2f6YA%2b1LF7DtWFOUJ4mzbkI2XpcezMI%2b%2f%2fpt5VRUNf%2bJA%3d%3d | unknown | — | — | whitelisted |
7720 | svchost.exe | GET | 206 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/820a23ba-bd71-40b7-8cae-4903ba074f95?P1=1723190649&P2=404&P3=2&P4=J82cILyXRLNUeDmKU79y%2fyf2OV4VD63YxayloDuK9P%2f6YA%2b1LF7DtWFOUJ4mzbkI2XpcezMI%2b%2f%2fpt5VRUNf%2bJA%3d%3d | unknown | — | — | whitelisted |
7720 | svchost.exe | GET | 206 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/820a23ba-bd71-40b7-8cae-4903ba074f95?P1=1723190649&P2=404&P3=2&P4=J82cILyXRLNUeDmKU79y%2fyf2OV4VD63YxayloDuK9P%2f6YA%2b1LF7DtWFOUJ4mzbkI2XpcezMI%2b%2f%2fpt5VRUNf%2bJA%3d%3d | unknown | — | — | whitelisted |
7720 | svchost.exe | GET | 206 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/820a23ba-bd71-40b7-8cae-4903ba074f95?P1=1723190649&P2=404&P3=2&P4=J82cILyXRLNUeDmKU79y%2fyf2OV4VD63YxayloDuK9P%2f6YA%2b1LF7DtWFOUJ4mzbkI2XpcezMI%2b%2f%2fpt5VRUNf%2bJA%3d%3d | unknown | — | — | whitelisted |
7720 | svchost.exe | GET | 206 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/820a23ba-bd71-40b7-8cae-4903ba074f95?P1=1723190649&P2=404&P3=2&P4=J82cILyXRLNUeDmKU79y%2fyf2OV4VD63YxayloDuK9P%2f6YA%2b1LF7DtWFOUJ4mzbkI2XpcezMI%2b%2f%2fpt5VRUNf%2bJA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3140 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
692 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6824 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6456 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6824 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6824 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6824 | msedge.exe | 23.32.238.91:443 | bzib.nelreports.net | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
key123.vip |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
cdn1.key123.vip |
| unknown |
update.googleapis.com |
| whitelisted |